近期准备参加CTF 一头雾水 开始练练手
https://2018game.picoctf.com/ 这个网站挺适合新手的(据说面向高中生?? 惭愧惭愧)
前面几个比较简单 就从
Resources - Points: 50 - (Solves: 26288)这个开始
Resources - Points: 50 - (Solves: 26288)
Solve:
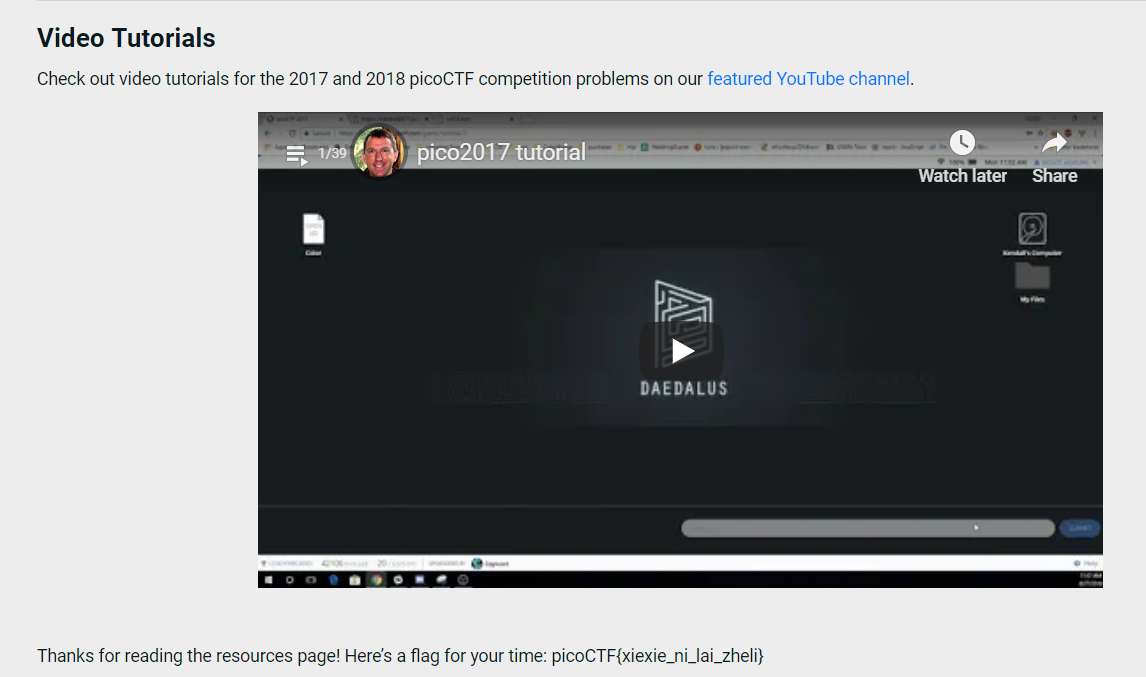
We put together a bunch of resources to help you out on our website! If you go over there, you might even find a flag! https://picoctf.com/resources (link)
点开这个网站,看完视频就可以拿到旗子了。
Reversing Warmup 1 - Points: 50 - (Solves: 16506)
Solve:
Throughout your journey you will have to run many programs. Can you navigate to /problems/reversing-warmup-1_1_b416a2d0694c871d8728d8268d84ac5c on the shell server and run this program to retreive the flag?
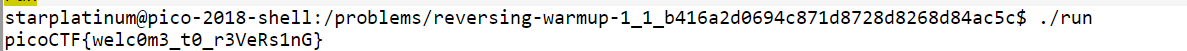
这个一开始看我很懵,还点击下载了那个run文件。查了一波发现是要登录这个网站给的shell,执行那个文件夹下的run。
打开shell,用自己的用户名密码登录(登录该网站的用户名密码)
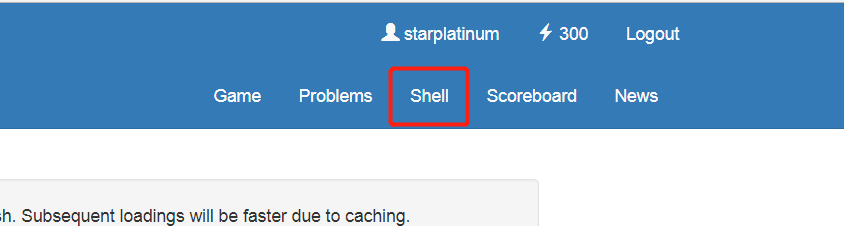
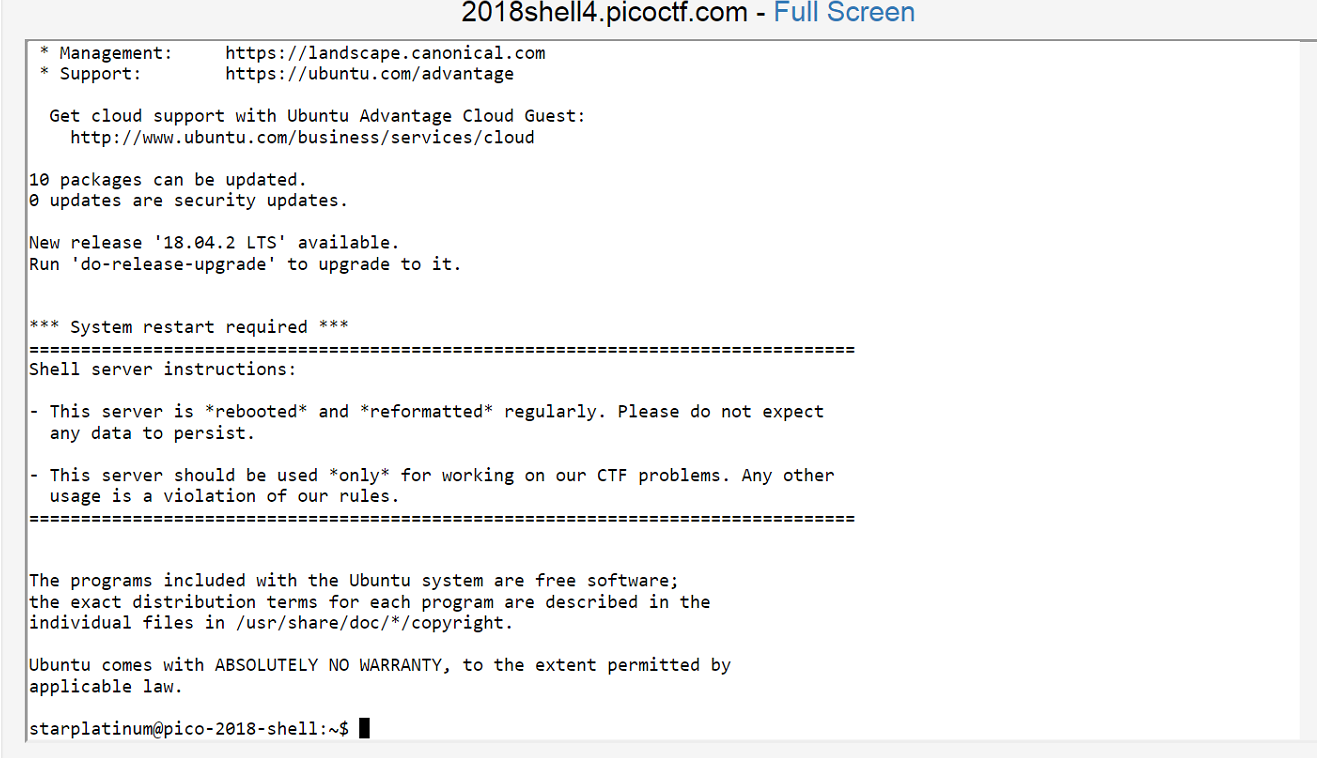
接着进入题目给的文件夹,运行run文件,获得旗子
Reversing Warmup 2 - Points: 50 - (Solves: 19109)
Solve:
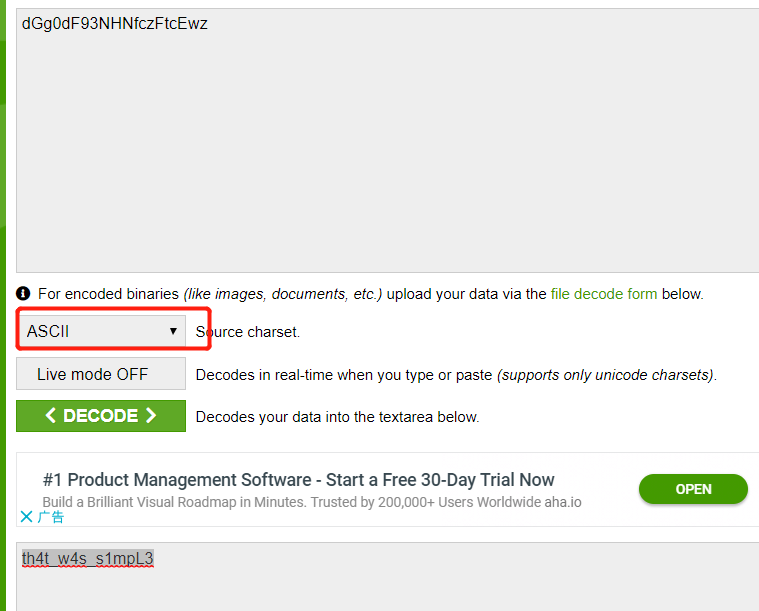
Can you decode the following string dGg0dF93NHNfczFtcEwz from base64 format to ASCII?
网上搜索一个解码的网站,比如https://www.base64decode.org/
复制字符串进去,选择解码为ASCII即可
Crypto Warmup 1 - Points: 75 - (Solves: 13281)
Solve:
Crpyto can often be done by hand, here's a message you got from a friend, llkjmlmpadkkc with the key of thisisalilkey. Can you use this table to solve it?.
下载表格之后如下:
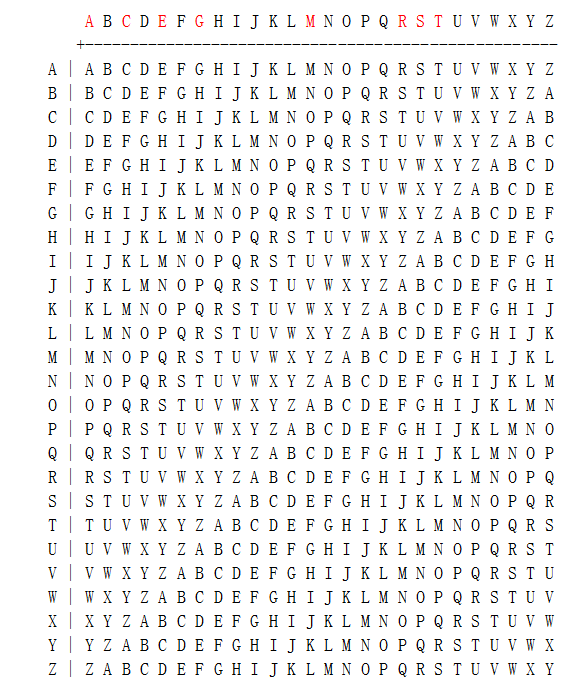
llkjmlmpadkkc
thisisalilkey
开始以为是l行t列的 然后找出来是ESSBUDMAIOUOA,不对
查了别人的答案后发现是,t行找到l列,往上看它的列标为S,h行找到l列,它的列标为E,一次类推,找出来的字母是SECRETMESSAGE
旗子picoCTF{SECRETMESSAGE}
grep 1 - Points: 75 - (Solves: 20527)
solve:
Can you find the flag in file? This would be really obnoxious to look through by hand, see if you can find a faster way. You can also find the file in /problems/grep-1_4_0431431e36a950543a85426d0299343e on the shell server.
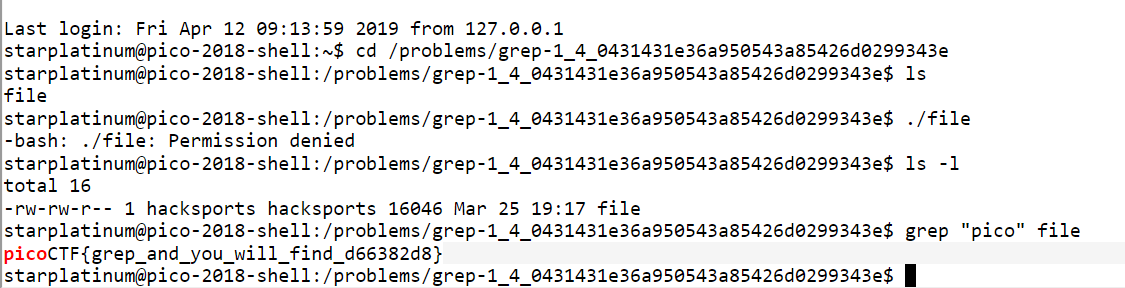
考察grep的用法。
net cat - Points: 75 - (Solves: 18315)
solve:
Using netcat (nc) will be a necessity throughout your adventure. Can you connect to 2018shell.picoctf.com at port 10854 to get the flag?

考察netcat的用法
HEEEEEEERE'S Johnny! - Points: 100 - (Solves: 7649)
solve:
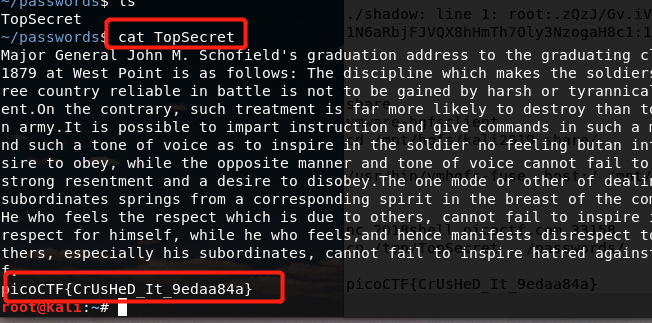
Okay, so we found some important looking files on a linux computer. Maybe they can be used to get a password to the process. Connect with nc 2018shell.picoctf.com 40157. Files can be found here: passwd shadow.
这道题考察用户密码shadow加密、以及用john the ripper破解的知识
用网站自带的shell 登录nc 2018shell.picoctf.com 40157,发现需要用户密码。
回到题目,发现提供了passwd、 shadow两个文件,就是登录所需的用户和密码。
在Linux上下载,运行:
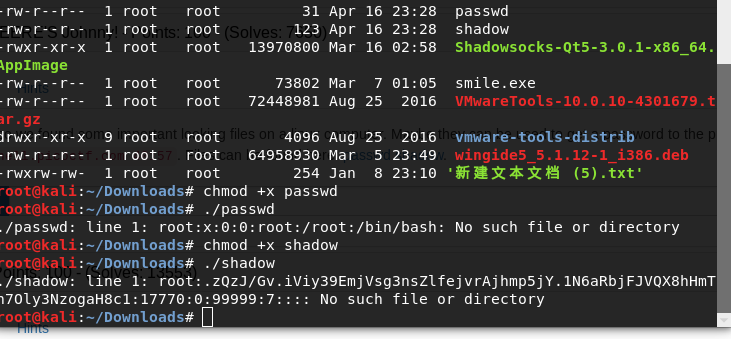
发现用户名是root,但是密码已经被加密过。
这时候需要一个叫john的软件破解。
教程说明见 http://www.linuxidc.com/Linux/2011-09/42617.htm
按着这个安装好软件。
将CTF网站上下载的passwd和shadow文件放到run文件夹下,然后用unshadow将它俩传到passfile
然后解密这个passfile
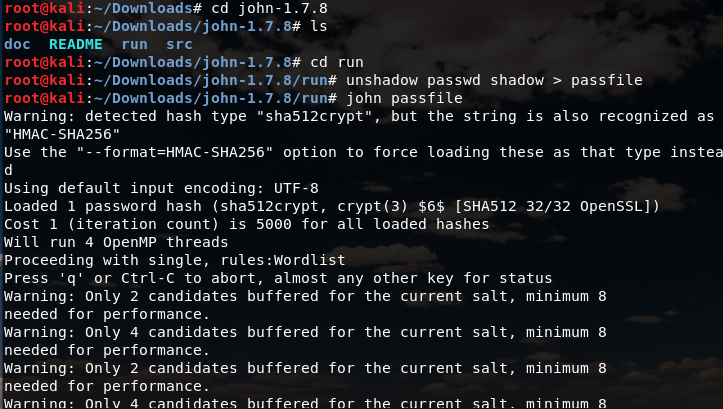
可以看到破解出来了

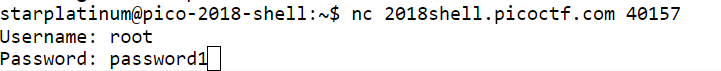
用户名:root
密码:password1
因情况而定,我看到有个博主的密码是hellokitty
登录后获得旗子
strings - Points: 100 - (Solves: 13611)
solve:
Can you find the flag in this file without actually running it? You can also find the file in /problems/strings_2_b7404a3aee308619cb2ba79677989960 on the shell server.
考察strings的用法

列出strings文件中所有ASCII文本并以此作为输入,用grep命令搜索包含pico的字段。
pipe - Points: 110 - (Solves: 12617)
solve:
During your adventure, you will likely encounter a situation where you need to process data that you receive over the network rather than through a file. Can you find a way to save the output from this program and search for the flag? Connect with 2018shell.picoctf.com 48696.
考察管道的用法
如果直接nc 2018shell.picoctf.com 48696 进去是一个死循环,一直跳信息。
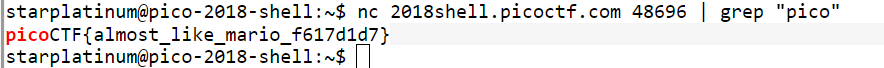
把|前面的输出当做|后面的输入。
Inspect Me - Points: 125 - (Solves: 16343)
solve:Inpect this code! http://2018shell.picoctf.com:35349 (link)
打开这个网址,查看源码:

发现了第一部分的flag,然后点开.css和.js
.css

.js
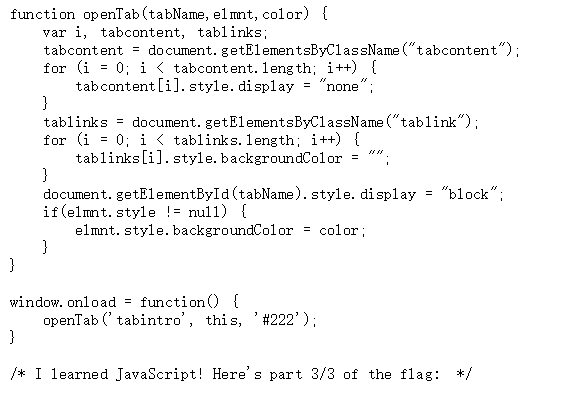
拼出来的flag:picoCTF{ur_4_real_1nspect0r_g4dget_098df0d0}
grep 2 - Points: 125 - (Solves: 11676)
solve:
This one is a little bit harder. Can you find the flag in /problems/grep-2_4_06c2058761f24267033e7ca6ff9d9144/files on the shell server? Remember, grep is your friend.
考察grep命令
在files文件夹下查找包含"pico"字段的信息
在files/files2/file8文件里有旗子的信息
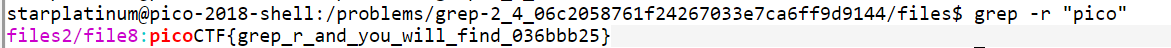
grep还是很方便的,一个个找太耗时
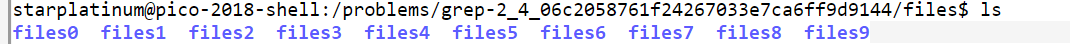
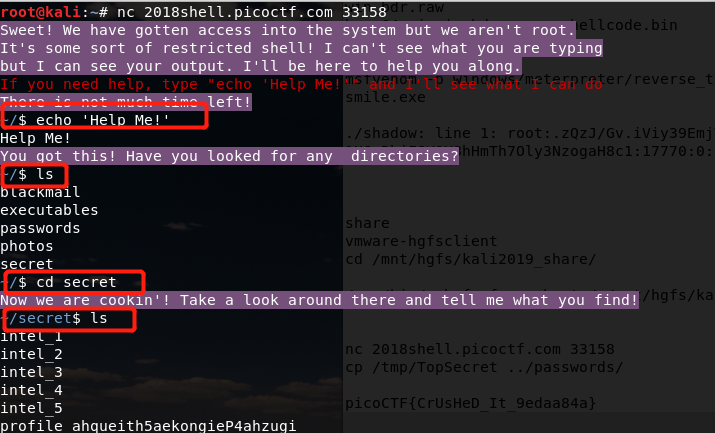
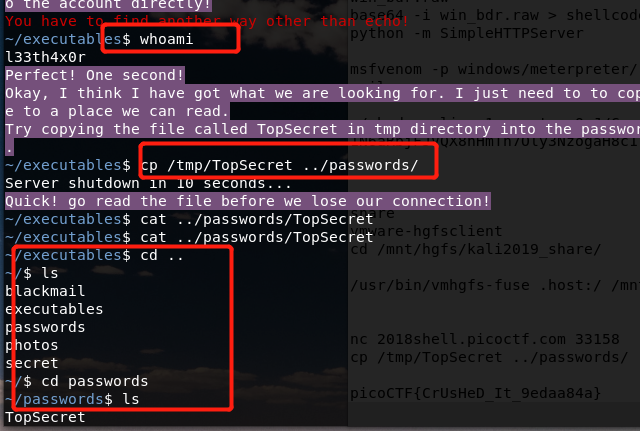
Aca-Shell-A - Points: 150 - (Solves: 9643)
solve:
It's never a bad idea to brush up on those linux skills or even learn some new ones before you set off on this adventure! Connect with nc 2018shell.picoctf.com 33158.
这个题不难。。就是要拼手速 跟着提示敲

Client Side is Still Bad - Points: 150 - (Solves: 14377)
solve:
I forgot my password again, but this time there doesn't seem to be a reset, can you help me? http://2018shell.picoctf.com:53990 (link)
点开链接之后发现是这样的:
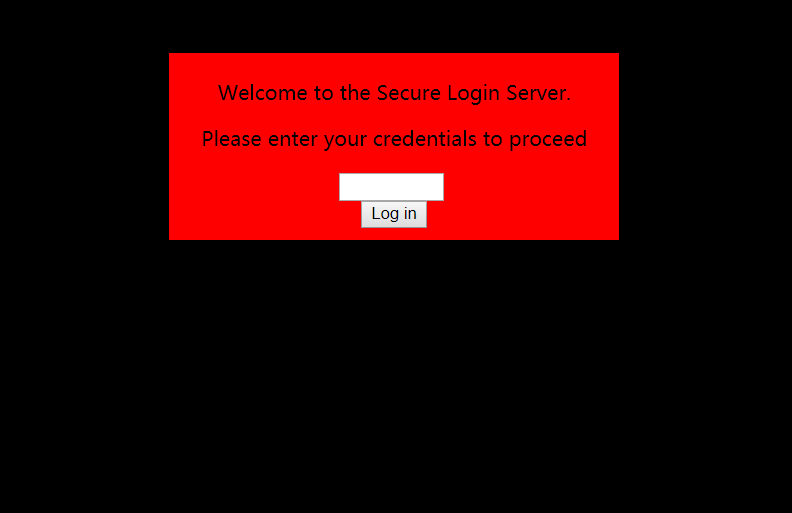
先看一下源码:
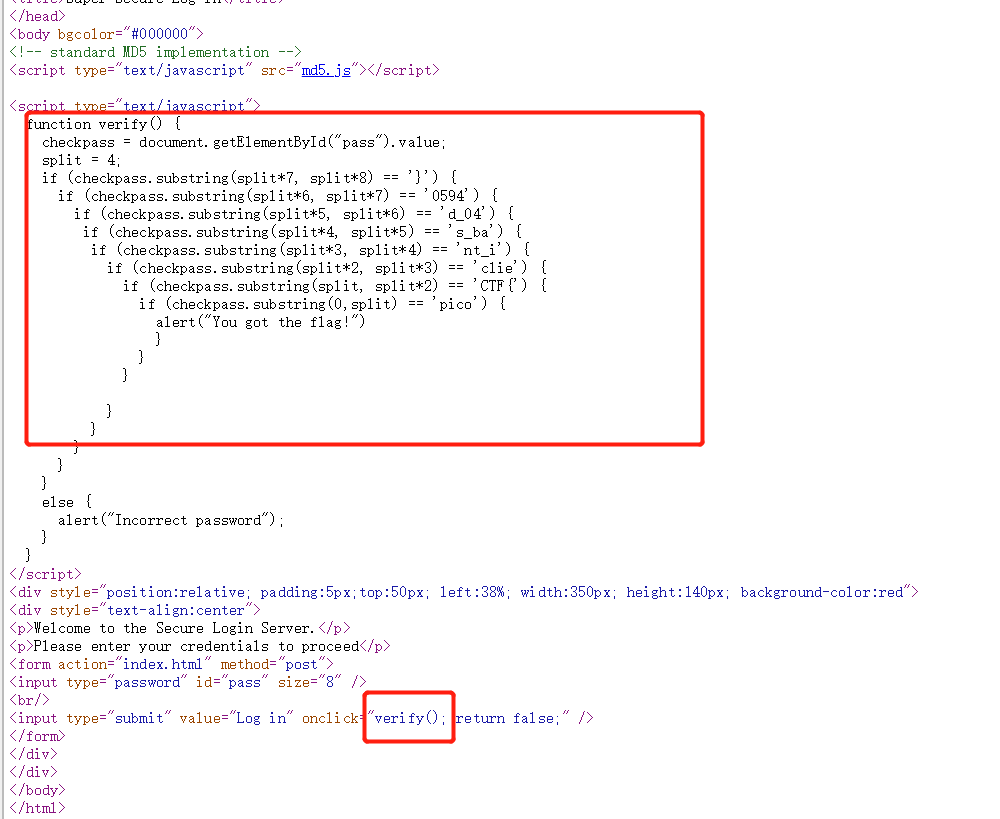
emmm,这直接给给了flag,倒着写上去就是了!
Desrouleaux - Points: 150 - (Solves: 5271)
solve:
Our network administrator is having some trouble handling the tickets for all of of our incidents. Can you help him out by answering all the questions? Connect with nc 2018shell.picoctf.com 63299. incidents.json
查看这个json文件,nc链接之后一共有三个问题。三个问题好像都是随机的。。。下面是第三个问题
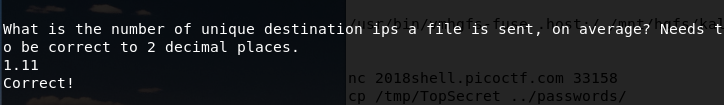
有9种文件,总共发送十次,有一个文件是发送了两次,所以10/9.。
Logon - Points: 150 - (Solves: 9109)
solve:
I made a website so now you can log on to! I don't seem to have the admin password. See if you can't get to the flag. http://2018shell.picoctf.com:62746 (link)
这个题涉及cookie
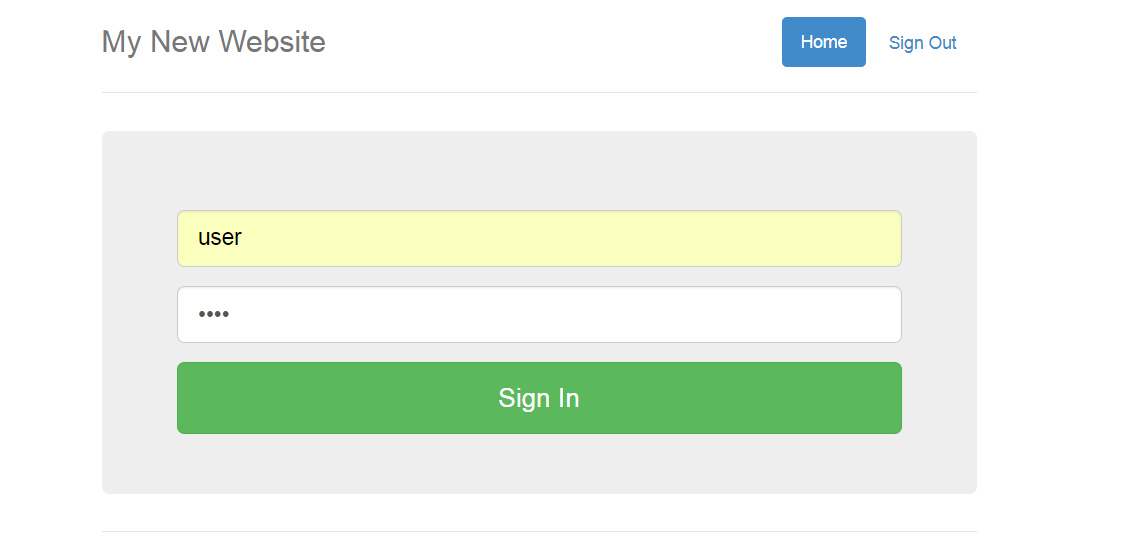
随便用一个账号密码登录(除了账号admin)
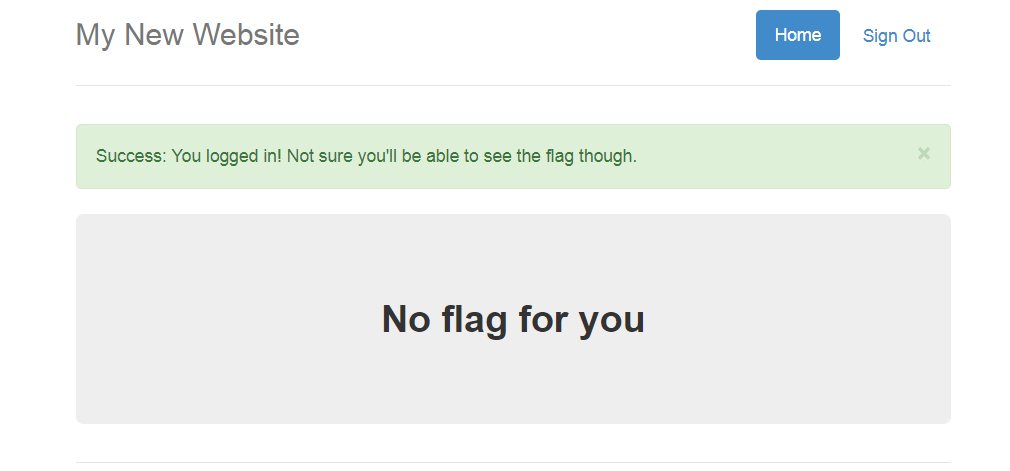
没有获得旗子。查看cookie(谷歌浏览器用editthiscookie插件)
发现admin字段是False,将它改为True,刷新页面。

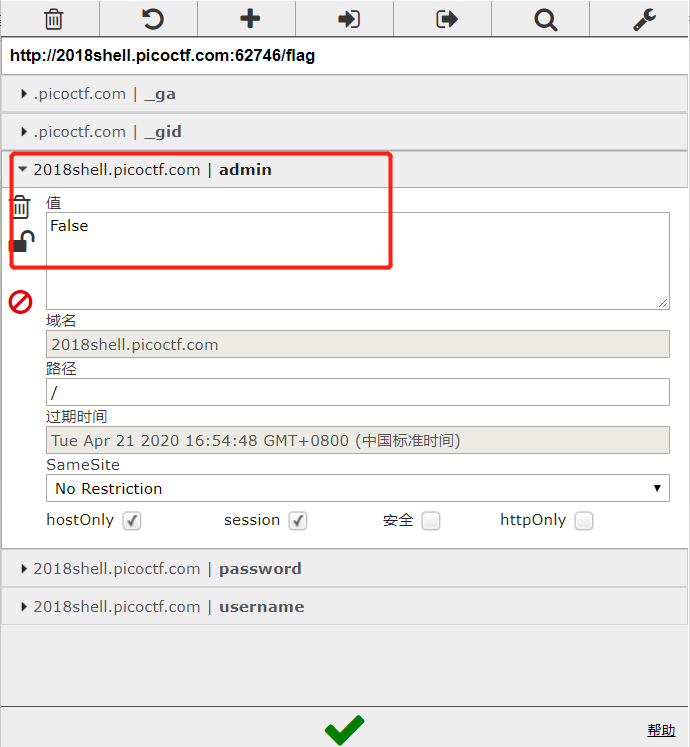
Reading Between the Eyes - Points: 150 - (Solves: 6784)
solve:
Stego-Saurus hid a message for you in this image, can you retreive it?
下载图片,是一张二哈的照片Hhh
在kali Linux上面解码的。首先安装一个工具:
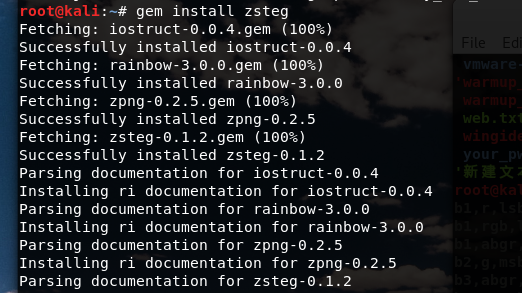
然后用zsteg解码:
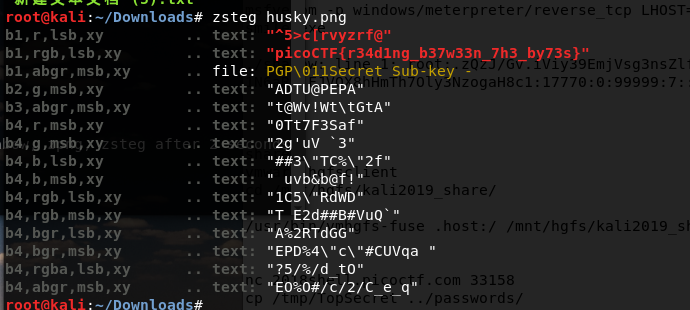
flag就出来了。。
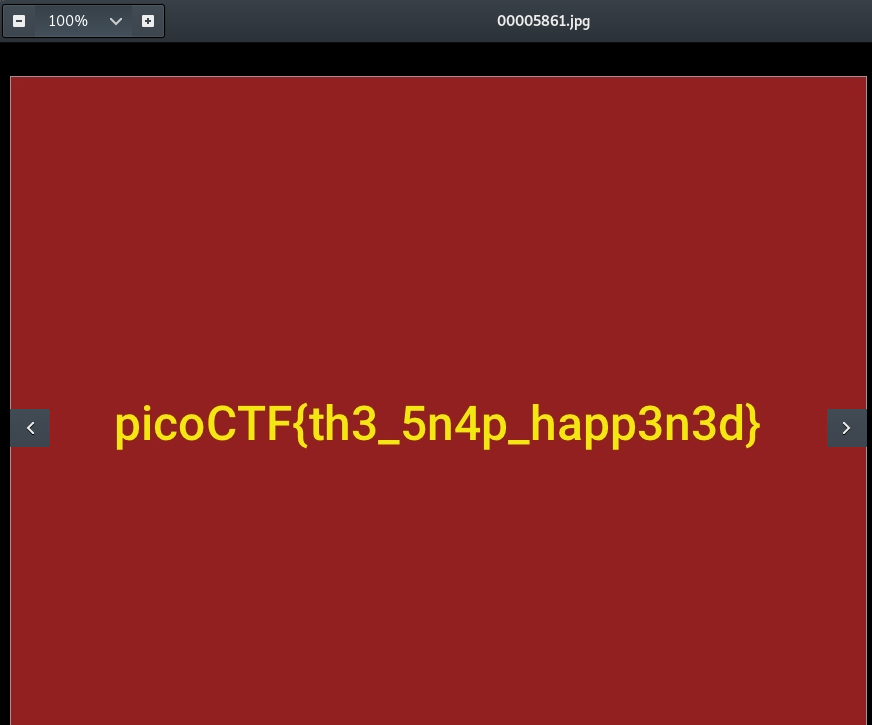
Recovering From the Snap - Points: 150 - (Solves: 5380)
solve:
There used to be a bunch of animals here, what did Dr. Xernon do to them?
先用file命令查看文件信息
该命令用来识别文件类型,也可用来辨别一些文件的编码格式。它是通过查看文件的头部信息来获取文件类型,而不是像Windows通过扩展名来确定文件类型的。
执行权限 :All User
指令所在路径:/usr/bin/file

用foremost命令还原文件。
https://mp.weixin.qq.com/s/R_GoqwrFS82_T4exiXH8cw
这里有一些简单的介绍
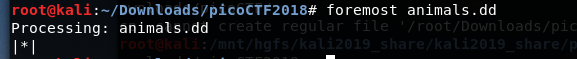
接着会解压出一个output文件夹,里面有几张图片
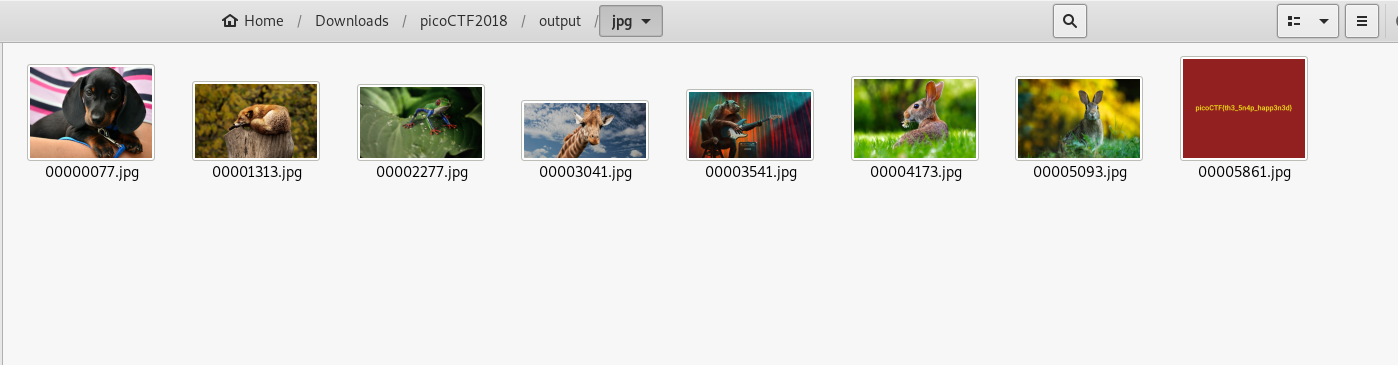
flag隐藏其中
admin panel - Points: 150 - (Solves: 8475)
solve:
We captured some traffic logging into the admin panel, can you find the password?
下载文件,是一个.pcap文件,可以用wireshark分析。
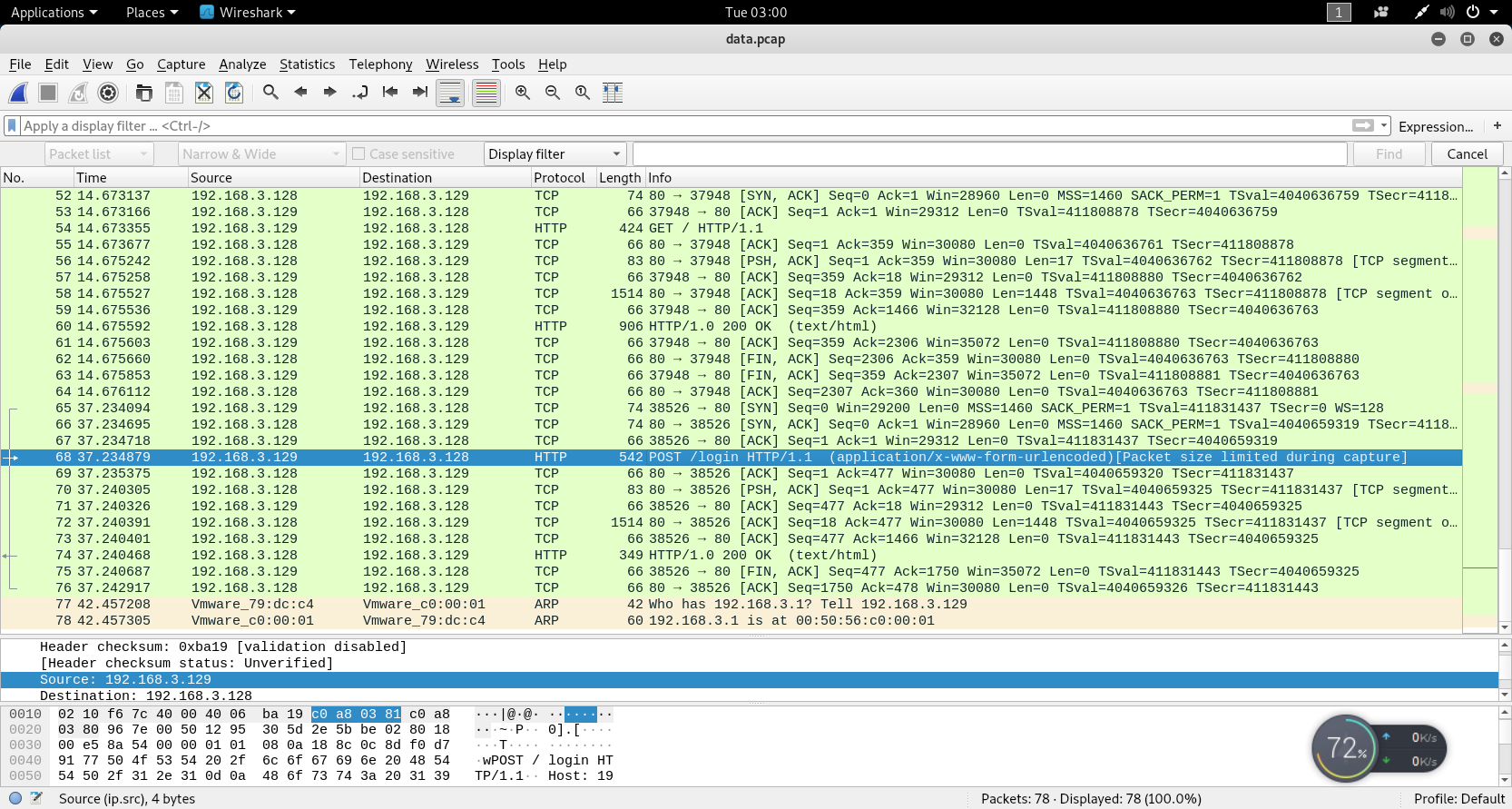
题目说到admin、password等,就主要看看HTTP包的,选一下带有admin、login字段的查看。。右键Follow->TCP Stream
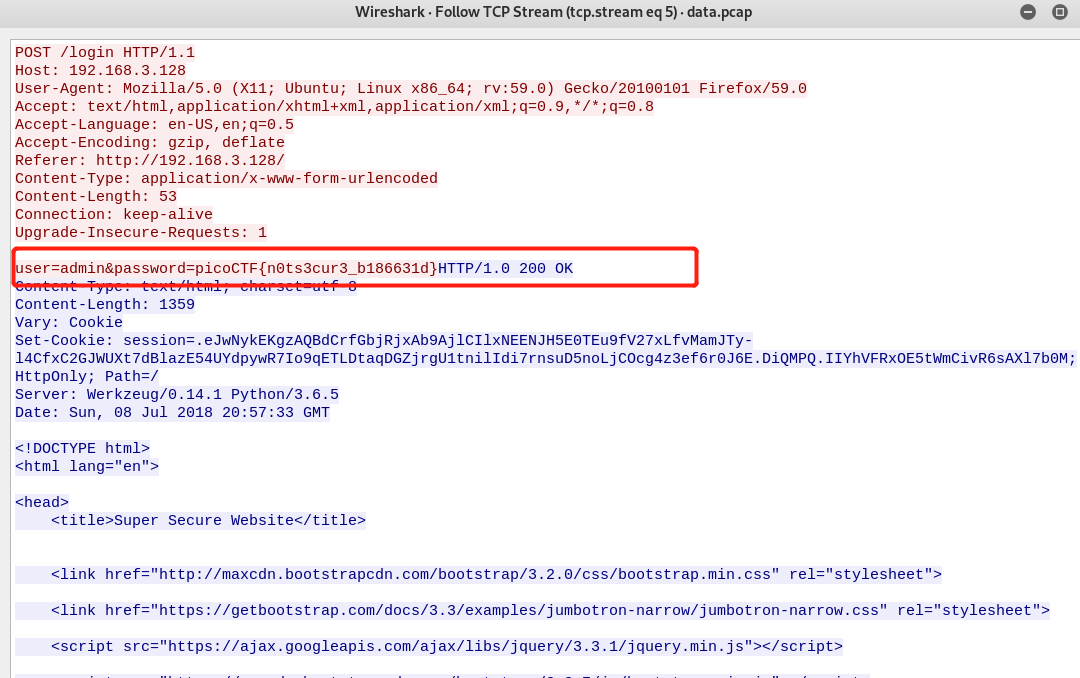
可以看到flag。。
可能第一个没找对,可以试着多找几个
HTTP协议都是明文,所以还有一种更简单粗暴的方法:
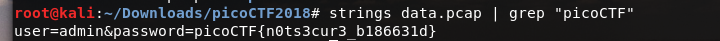
直接strings命令就可以输出了。。
assembly-0 - Points: 150 - (Solves: 4949)
solve:
What does asm0(0xaa,0xf2) return? Submit the flag as a hexadecimal value (starting with '0x'). NOTE: Your submission for this question will NOT be in the normal flag format. Source located in the directory at /problems/assembly-0_2_485b2d48345b19addbeb06a36aabdc74.
网站上给的提示是汇编语言。。。
https://www.youtube.com/watch?v=sLsgSC6ViS8&t=314s
跟着这个up主做的,但是看不到汇编代码。。
先这样吧。。
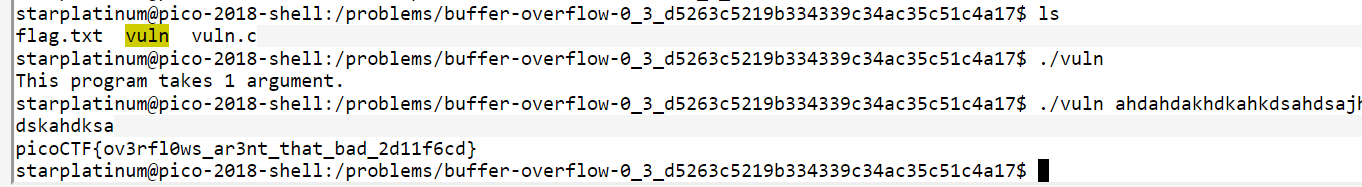
buffer overflow 0 - Points: 150 - (Solves: 6054)
solve:
Let's start off simple, can you overflow the right buffer in this program to get the flag? You can also find it in /problems/buffer-overflow-0_3_d5263c5219b334339c34ac35c51c4a17 on the shell server. Source.
下载这个program和source。vuln.c和vuln。
看一下这个vunl.c的代码
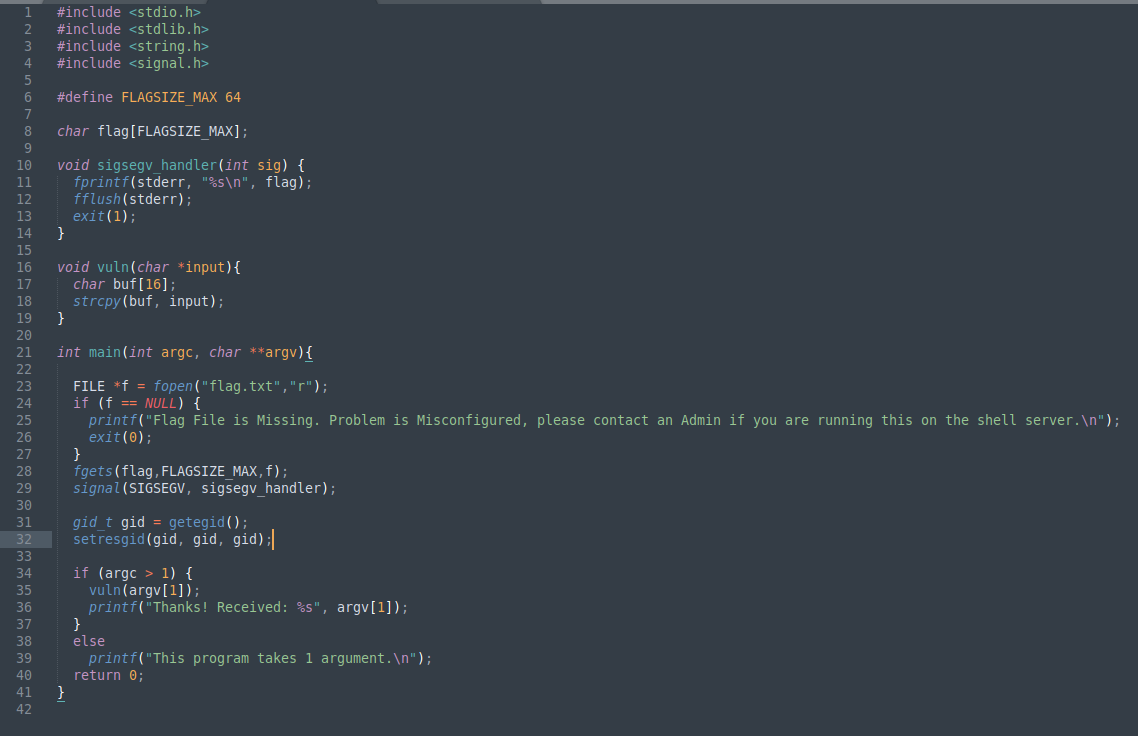
看一个Up主的说明是,运行这个vuln.c,要输入一个参数,这buf是16字节,但是方法里没有明确限制位数,当输入位数超过16时,就会输出flag。。。
https://www.youtube.com/watch?v=sLsgSC6ViS8&t=699s
登录网站给的shell:
caesar cipher 1 - Points: 150 - (Solves: 9356)
solve:
This is one of the older ciphers in the books, can you decrypt the message? You can find the ciphertext in /problems/caesar-cipher-1_3_160978e2a142244574bd048623dba1ed on the shell server.
下载这个message,是一个已经用恺撒密码加密的flag。
点开Hint那个连接,介绍的是偏移3个位置。所以我们试试偏移3解码的值。
用在线的解码网址就可以解了
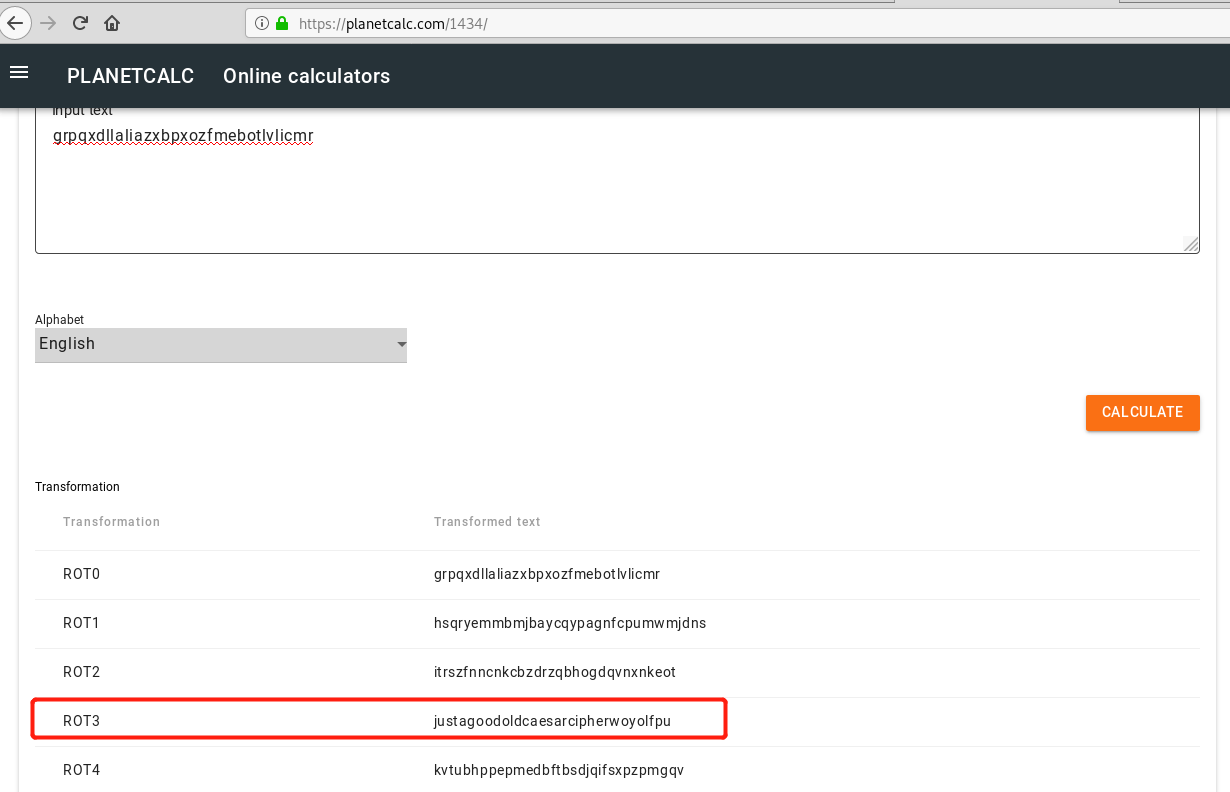
看样子挺像的,输入进去就是它了!
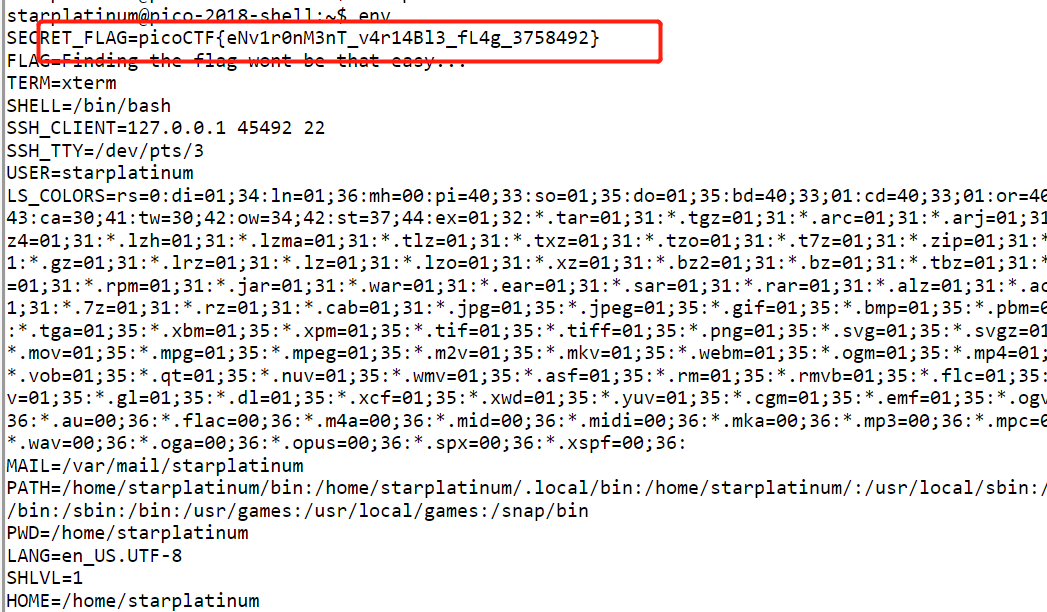
environ - Points: 150 - (Solves: 8101)
solve:
Sometimes you have to configure environment variables before executing a program. Can you find the flag we've hidden in an environment variable on the shell server?
用自带的shell输入env就可以了:
hertz - Points: 150 - (Solves: 5835)
solve:
Here's another simple cipher for you where we made a bunch of substitutions. Can you decrypt it? Connect with nc 2018shell.picoctf.com 14928.
连接之后这一串。。完全整蒙了
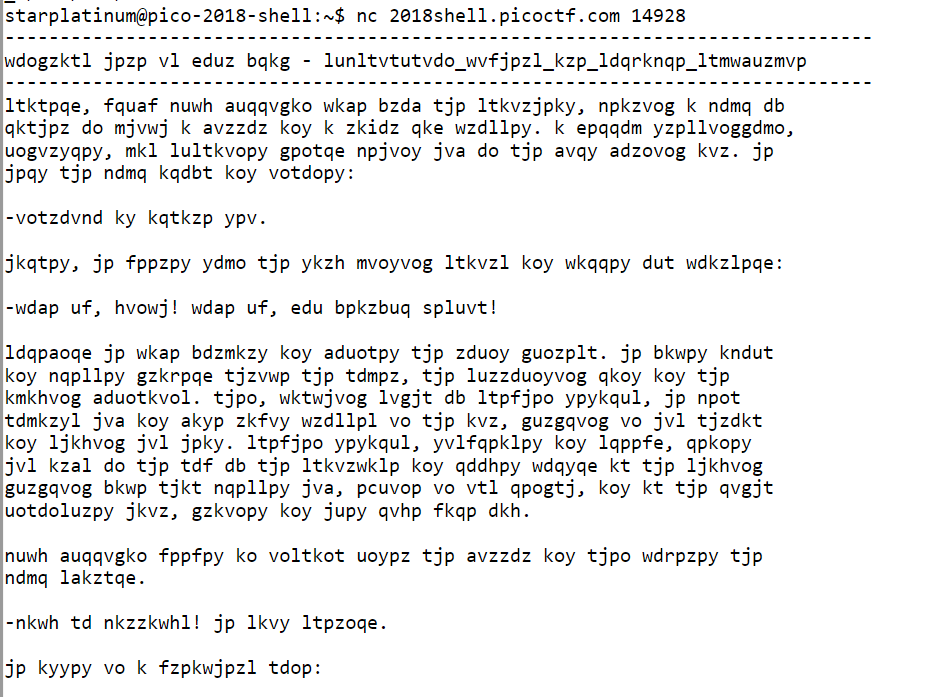
在网上查了一下,有个up主教的用quipquip这个网站,把那一大段贴进去。。可能要贴多次,因为每次nc出来的密文都不一样,所以有时候解里面没看到flag。 下面贴的是成功的

picoCTF{substitution_ciphers_are_solvable_stwcmurwie}
hex editor - Points: 150 - (Solves: 7876)
solve:
This cat has a secret to teach you. You can also find the file in /problems/hex-editor_3_086632ac634f394afd301fb6a8dbadc6 on the shell server.
这个cat下下来是一只猫hhh,根据hint xdd,hexedit,bvi,查了下,前两个查到了是十六进制编辑器。
直接在终端 xxd cat.jpg 拖到最下方:
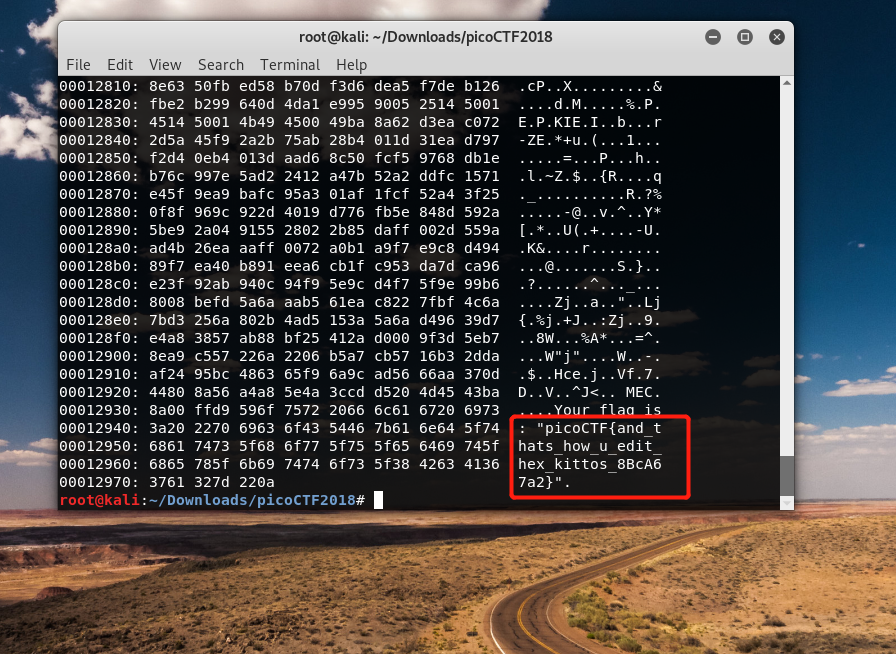
输入这个flag就好啦
ssh-keyz - Points: 150 - (Solves: 7067)
solve:
As nice as it is to use our webshell, sometimes its helpful to connect directly to our machine. To do so, please add your own public key to ~/.ssh/authorized_keys, using the webshell. The flag is in the ssh banner which will be displayed when you login remotely with ssh to with your username.
考察ssh-keygen
跟着hint的视频做了一遍(https://www.youtube.com/watch?v=3CN65ccfllU&list=PLJ_vkrXdcgH-lYlRV8O-kef2zWvoy79yP&index=4)
其实这个题不产生id_rsa.pub 也可以 直接
ssh 到网站的shell 就行了
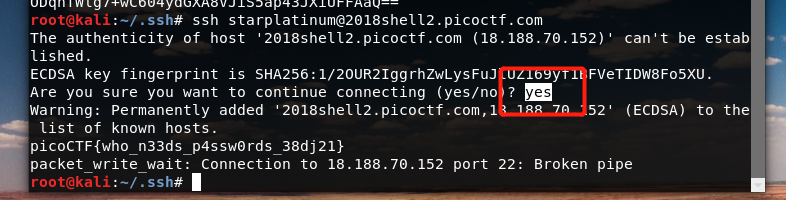
这里要输入yes!!!!如果直接回车 会弹出host key verification failed...
就因为这个问题。。折腾了好久