0x001 Win下检测
https://github.com/robertdavidgraham/rdpscan
C:\Users\K8team\Desktop\rdpscan-master\vs10\Release 的目录
2019/06/02 02:11 <DIR> .
2019/06/02 02:11 <DIR> ..
2019/06/02 01:55 2,582,016 libcrypto-1_1.dll
2019/06/02 01:57 619,520 libssl-1_1.dll
2019/06/02 02:04 172,032 rdpscan.exe
3 个文件 3,373,568 字节
2 个目录 2,462,433,280 可用字节
C:\Users\K8team\Desktop\rdpscan-master\vs10\Release>rdpscan 192.168.1.101-192.168.1.105
192.168.1.101 - VULNERABLE - CVE-2019-0708
192.168.1.102 - VULNERABLE - CVE-2019-0708
C:\Users\K8team\Desktop\rdpscan-master\vs10\Release>rdpscan 192.168.1.101-192.168.1.105
192.168.1.102 - SAFE - CredSSP/NLA required
192.168.1.101 - VULNERABLE - CVE-2019-0708

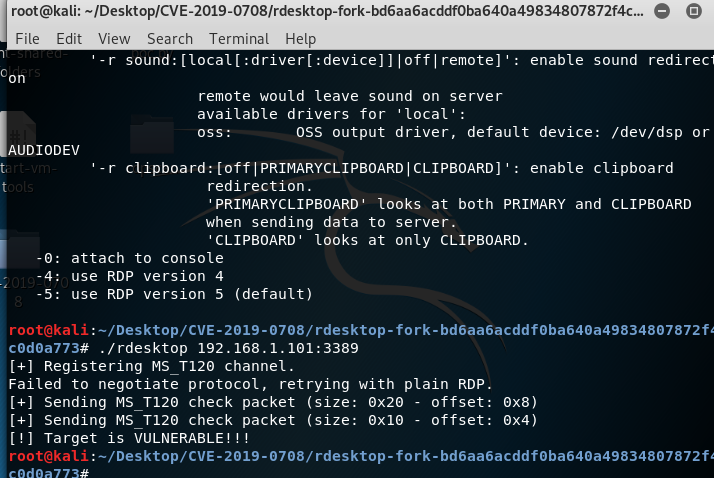
0x002 Linux下检测
https://github.com/SugiB3o/Check-vuln-CVE-2019-0708 root@kali:~/Desktop# ./rdesktop 192.168.1.101:3389 ERROR: Failed to open keymap en-us [+] Registering MS_T120 channel. Failed to negotiate protocol, retrying with plain RDP. [+] Sending MS_T120 check packet (size: 0x20 - offset: 0x8) [+] Sending MS_T120 check packet (size: 0x10 - offset: 0x4) [!] Target is VULNERABLE!!!
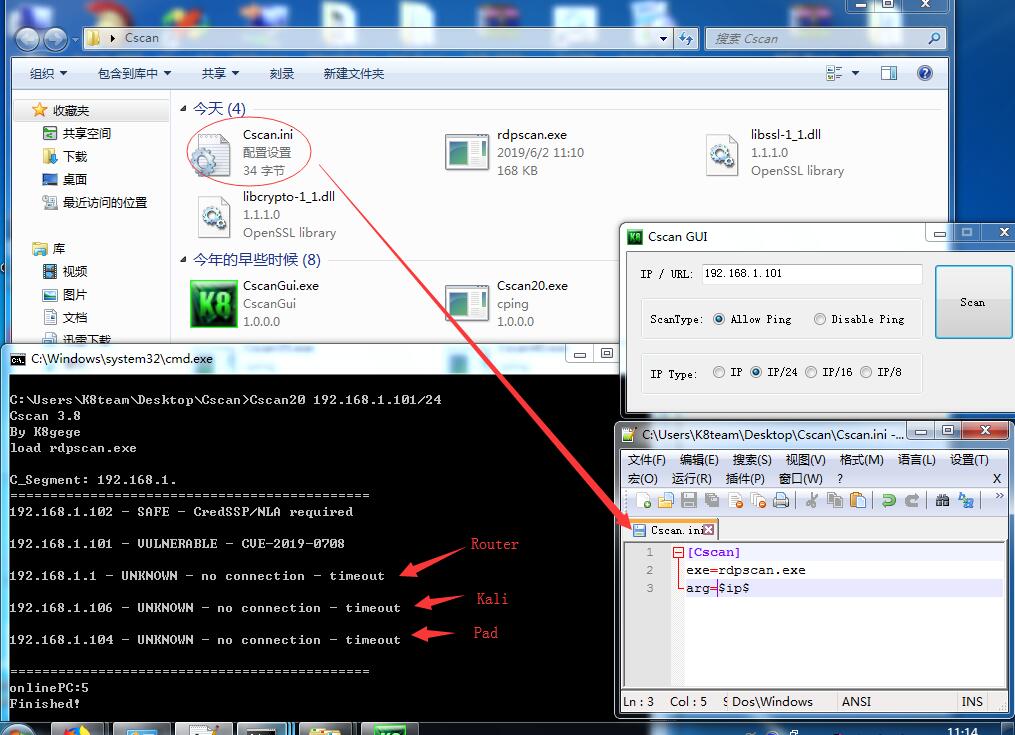
0x003 Cscan批量检测
将rdpscan.exe以及dll文件拷贝至Cscan目录,新建Cscan.ini文件,内容如下
[Cscan] exe=rdpscan.exe arg=$ip$
批量扫描
Cscan.exe 192.168.1.101/24 (扫单个C段,多个C段或B段请参考Cscan说明)
本地可使用GUI(仅.net 2.0,请根据自身或目标电脑.net版本选择Cscan版本)
0x004 Bin下载
Win下编译可能比较麻烦这里提供编译好的成品
分别是Win7 x86的exe,当然64系统下也可以用
Kali 2019 x64的可执行文件,其它版本自行编译