一、实验拓扑: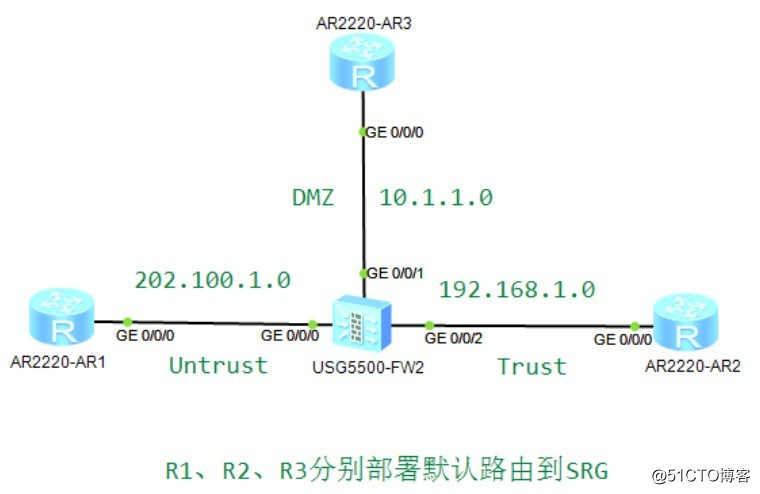
二、实验要求:
1、内网:连接R2接口G0/0/2是三层接口,其它接口都是二层接口;R1、R2、R3部署默认路由到USG;
2、USG上创建VLAN 10、202,并将G0/0/0划分到VLAN 202,G0/0/1划分到VLAN 10;
3、部署Policy 0:允许Trust到Untrust的ICMP流量出去;部署Policy 1:允许DMZ到Untrust Outbound的ICMP流量出去;
4、R3 Ping R1;R2 Ping R1是否可通?
三、命令部署:
1、路由器接口地址、默认路由略
[R1]ip route-static 0.0.0.0 0.0.0.0 202.100.1.10
[R2]ip route-static 0.0.0.0 0.0.0.0 192.168.1.10
[R3]ip route-static 0.0.0.0 0.0.0.0 10.1.1.10
2、USG配置:
(1)接口配置:
[SRG]int g0/0/0
[SRG-GigabitEthernet0/0/0]portswitch
[SRG-GigabitEthernet0/0/0]port access vlan 202
[SRG]int g0/0/1
[SRG-GigabitEthernet0/0/1]portswitch
[SRG-GigabitEthernet0/0/1]port access vlan 10
[SRG]int g0/0/2
[SRG-GigabitEthernet0/0/2]ip add 192.168.1.10 24
查看:
[SRG-GigabitEthernet0/0/0]display this //默认输完portswitch,就是access口
portswitch
port link-type access
[SRG]display ip int bri //已经没有G0/0/0、G0/0/1接口显示了
创建VLAN:
[SRG]vlan 10
[SRG-vlan-10]vlan 202
配置VLAN地址:
[SRG]int vlanif 202
[SRG-Vlanif202]ip add 202.100.1.10 24
[SRG]int Vlanif 10
[SRG-Vlanif10]ip add 10.1.1.10 24
查看:
[SRG]display ip interface brief //增加了VLAN 地址
把原来的接口解出来:
[SRG]firewall zone untrust
[SRG-zone-untrust]undo add int g0/0/0
[SRG]firewall zone dmz
[SRG-zone-dmz]undo add int g0/0/1
划分VLAN到不通区域:
[SRG]firewall zone untrust
[SRG-zone-untrust]add int g0/0/0
[SRG]firewall zone dmz
[SRG-zone-dmz]add int Vlanif 10
测试:
[SRG]ping 202.100.1.1 //可通
[SRG]ping 10.1.1.3 //可通
(2)部署Policy 1:允许DMZ到Untrust Outbound的ICMP流量出去
[SRG]ip service-set aaa type object
[SRG-object-service-set-aaa]service protocol icmp
[SRG]policy interzone dmz untrust outbound
[SRG-policy-interzone-dmz-untrust-outbound]policy 1
[SRG-policy-interzone-dmz-untrust-outbound-1]policy source 10.1.1.0 mask 24
[SRG-policy-interzone-dmz-untrust-outbound-1]policy destination 202.100.1.0 mask 24
[SRG-policy-interzone-dmz-untrust-outbound-1]policy service service-set aaa
[SRG-policy-interzone-dmz-untrust-outbound-1]action permit
(3)部署Policy 0:允许Trust到Untrust的ICMP流量出去
[SRG]policy interzone trust untrust outbound
[SRG-policy-interzone-trust-untrust-outbound]policy 0
[SRG-policy-interzone-trust-untrust-outbound-0]policy source 192.168.1.0 mask 24
[SRG-policy-interzone-trust-untrust-outbound-0]policy destination 202.100.1.0 mask 24
[SRG-policy-interzone-trust-untrust-outbound-0]policy service service-set aaa
[SRG-policy-interzone-trust-untrust-outbound-0]action permit
测试:
[R2]ping 202.100.1.1
Reply from 202.100.1.1: bytes=56 Sequence=1 ttl=254 time=50 ms
Reply from 202.100.1.1: bytes=56 Sequence=2 ttl=254 time=50 ms
Reply from 202.100.1.1: bytes=56 Sequence=3 ttl=254 time=50 ms
Reply from 202.100.1.1: bytes=56 Sequence=4 ttl=254 time=50 ms
Reply from 202.100.1.1: bytes=56 Sequence=5 ttl=254 time=40 ms
实现效果受影响。