作者信息:苗浩15515026488微信同号
本文摘抄自《华为ICT大赛-网络赛道学习空间(中国区)》,如有侵权,请及时联系作者删除文章
一、项目背景
比赛模拟了某大型公司企业网通过广域网连接数据中心的场景。
考虑到网络冗余和流量负载均衡的需求,企业网部署MSTP、防火墙双机热备用于承载web业务和Internet访问业务。同时,为了满足员工的无线办公需求,工程师需要部署WLAN设备于企业网内,用于访问Internet。
在使用丰富的网络资源建设企业网络和数据中心网络的时代大背景下,工程师们证面临严峻的安全问题,NGFW可以部署于企业网络和数据中心网络出口有利于降低安全风险,以帮助实现安全且高效的网络管理。
该企业的私有云部署在总部数据中心机房,企业的各类业务系统都部署在其私有云上,其中企业的OA系统所在的web服务器部署在总部的数据中心,企业各分支需要通过MPLS VPN访问远端数据中心的Web-Server,并且出于安全因素,Web-Server的私网地址不通告到广域网,而是通过一个外部公网地址100.1.1.1提供访问,Web-Client到Web-Server的流量需要在防火墙FW3上做目的地址转换,转换成Web-Server私有地址实现访问。
为实现数据中心租户位于不用子网的业务虚拟机互通,这里业务虚拟机为VM1和VM2,需要在数据中心部署GRE隧道,以打通VM1和VM2的三层通道。
广域网为企业的内网和远端总部数据中心提供链接,提供在广域网上部署MPLS VPN实现企业的互联网专线功能,以确保在广域网上的业务隔离的效果。
二、网络赛道
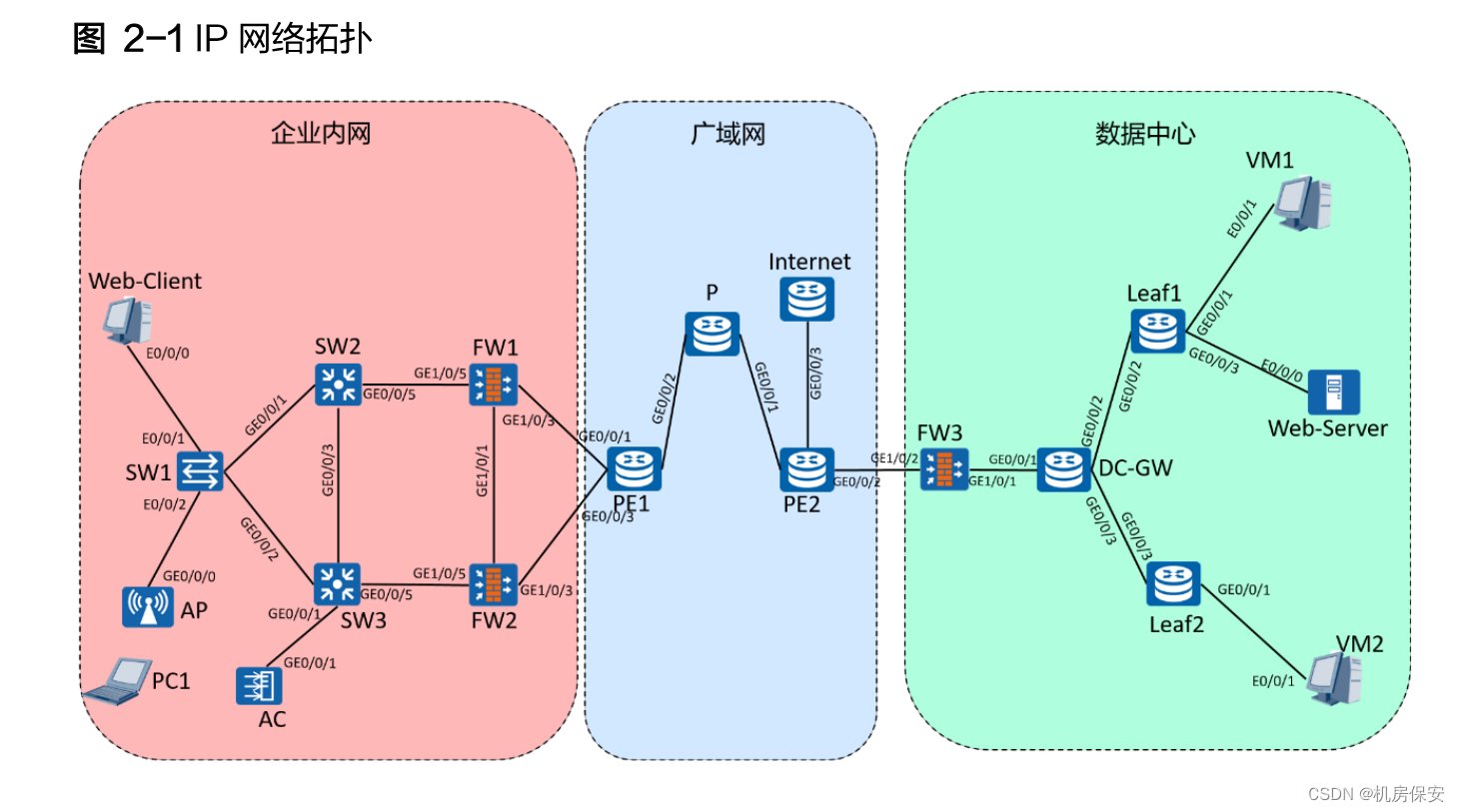
实验环境使用如下设备:
- 2台S5700(SW2、SW3)
- 1台S3700(SW1)
- 3台防火墙USG6000V(FW1-FW3)
- 7台路由器Router(PE1、PE2、P、Internet、Leaf1、Leaf2)
- 1台AC6605(AC)
- 1台AP6050(AP)
- 1台WLAN终端(PC)
- 1台Web服务器(Web-Server)
- 1台Web客户端(Web-Client)
- 2台虚拟机(VM1、VM2)

 2.1 比赛任务
2.1 比赛任务
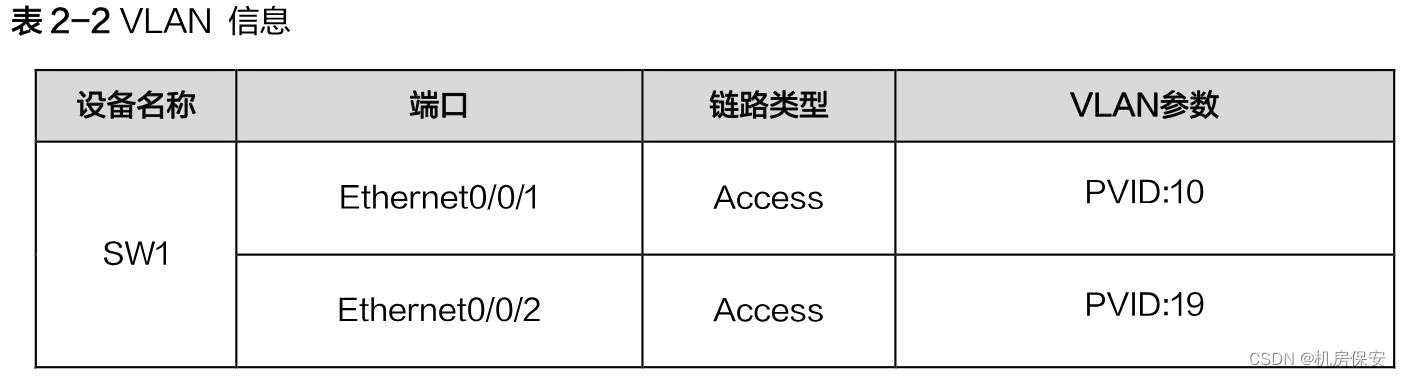
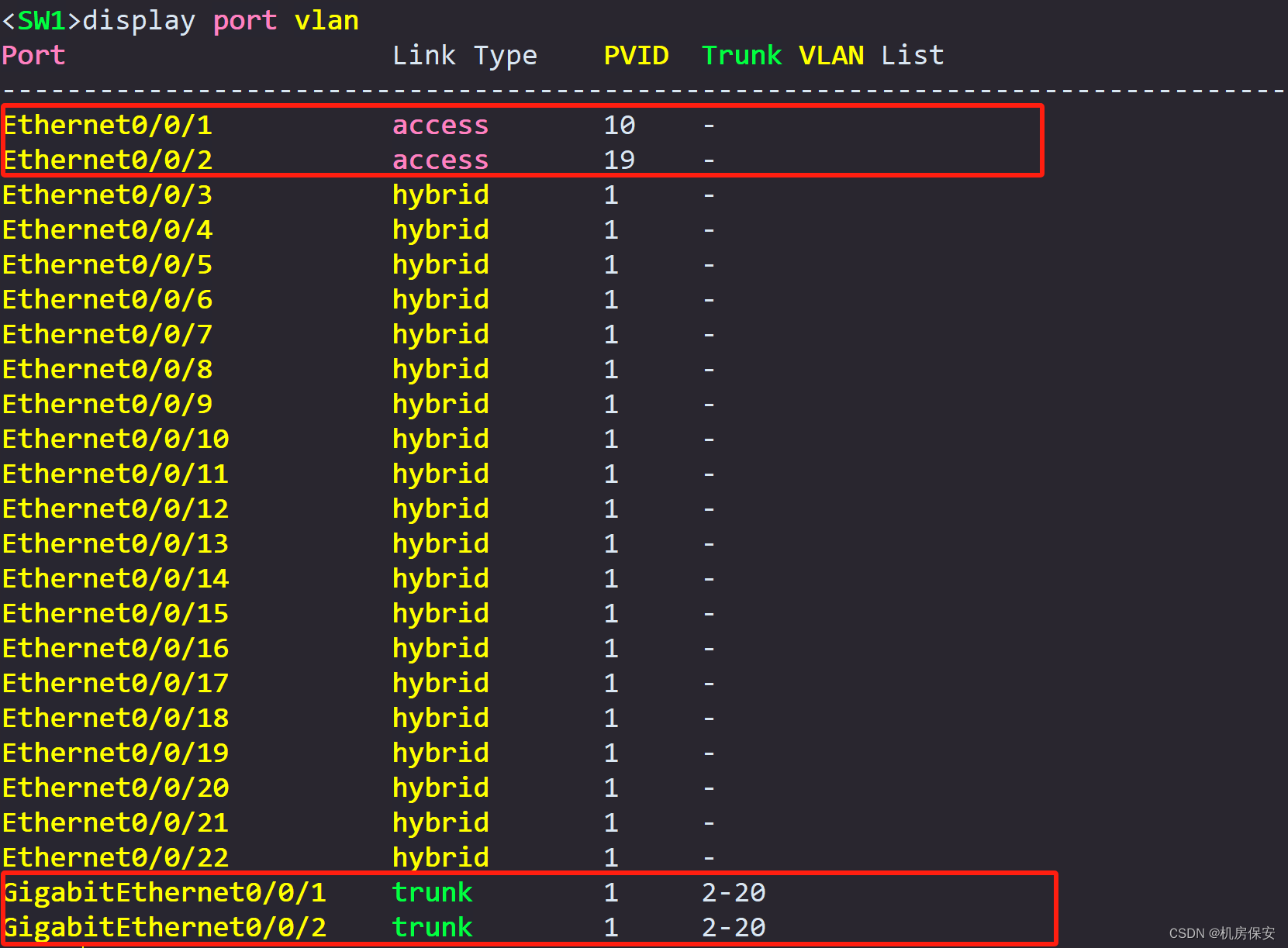
任务1:VLAN
根据2-2规划,配置网络设备名称,在SW1、SW2、SW3上配置VLAN链路类型和VLAN参数、在PE1、FW1和FW2上配置子接口和子接口ID。


任务2:IP地址
根据图2-1和表2-3配置网络设备名称和接口IP地址。
配置过程:
任务1/2:设备命名/VLAN/IP地址
#SW1
<Huawei>system-view
[Huawei]sysname SW1
[SW1]vlan batch 2 to 20
[SW1]interface Ethernet0/0/1
[SW1-Ethernet0/0/1]port link-type access
[SW1-Ethernet0/0/1]port default vlan 10
[SW1]interface Ethernet0/0/2
[SW1-Ethernet0/0/2]port link-type access
[SW1-Ethernet0/0/2]port default vlan 19
[SW1]port-group group-member GigabitEthernet 0/0/1 GigabitEthernet 0/0/2
[SW1-port-group]port link-type trunk
[SW1-port-group]undo port trunk allow-pass vlan 1
[SW1-port-group]port trunk allow-pass vlan 2 to 20
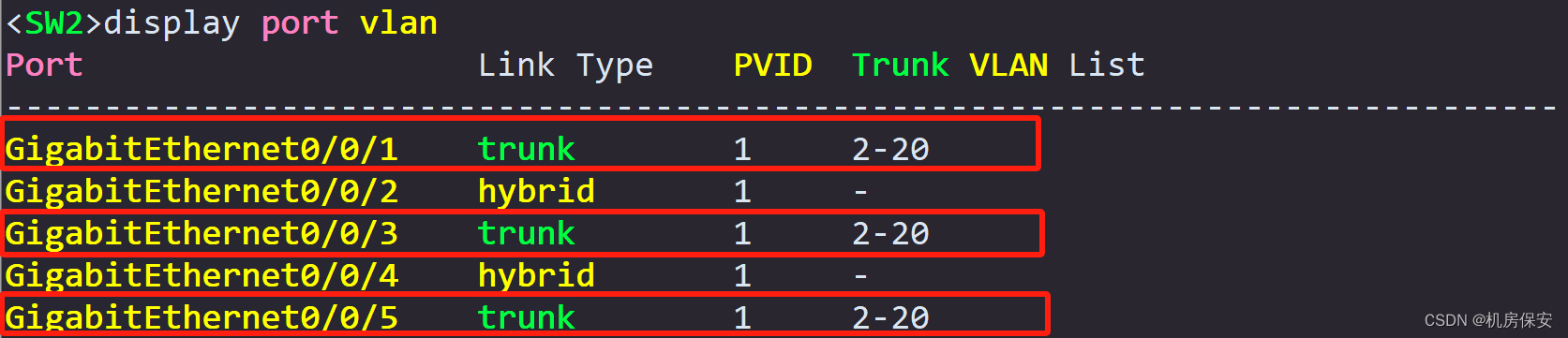
#SW2
<Huawei>system-view
[Huawei]sysname SW2
[SW2]vlan batch 2 to 20
[SW2]port-group group-member GigabitEthernet 0/0/1 GigabitEthernet 0/0/3 GigabitEthernet 0/0/5
[SW2-port-group]port link-type trunk
[SW2-port-group]undo port trunk allow-pass vlan 1
[SW2-port-group]port trunk allow-pass vlan 2 to 20
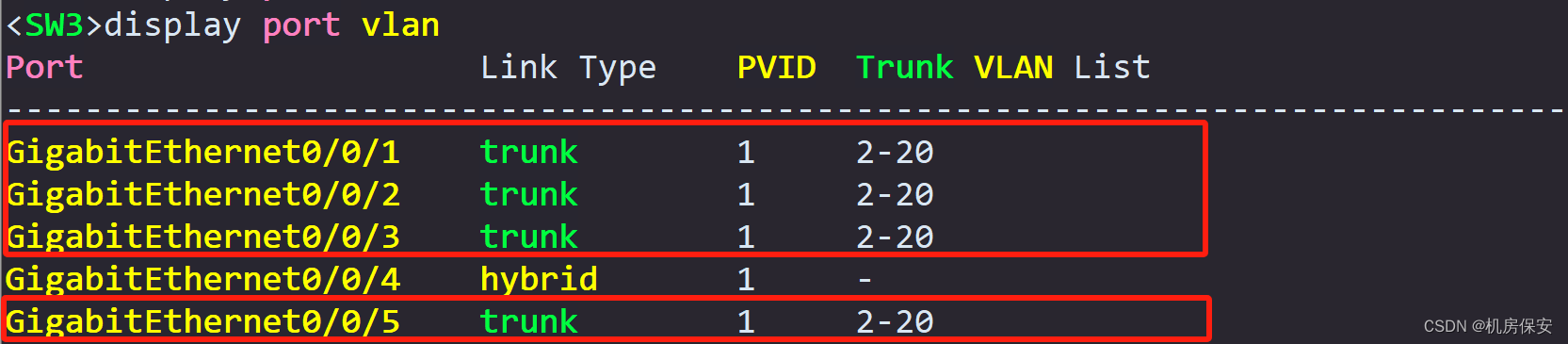
#SW3
<Huawei>system-view
[Huawei]sysname SW3
[SW3]vlan batch 2 to 20
[SW3]port-group group-member GigabitEthernet 0/0/1 to GigabitEthernet 0/0/3 GigabitEthernet 0/0/5
[SW3-port-group]port link-type trunk
[SW3-port-group]undo port trunk allow-pass vlan 1
[SW3-port-group]port trunk allow-pass vlan 2 to 20
#FW1
<USG6000V1>system-view
[USG6000V1]sysname FW1
[FW1]interface GigabitEthernet 1/0/5.1
[FW1-GigabitEthernet1/0/5.1]vlan-type dot1q 10
[FW1-GigabitEthernet1/0/5.1]ip address 192.168.1.2 24
[FW1]interface GigabitEthernet 1/0/5.2
[FW1-GigabitEthernet1/0/5.2]vlan-type dot1q 20
[FW1-GigabitEthernet1/0/5.2]ip address 192.168.2.2 24
[FW1]interface GigabitEthernet 1/0/3.1
[FW1-GigabitEthernet1/0/3.1]vlan-type dot1q 1
[FW1-GigabitEthernet1/0/3.1]ip address 10.2.2.1 30
[FW1]interface GigabitEthernet 1/0/1
[FW1-GigabitEthernet1/0/1]ip address 15.1.1.1 24
[FW1]interface GigabitEthernet 1/0/3
[FW1-GigabitEthernet1/0/3]ip address 10.2.1.1 30
#FW2
<USG6000V1>system-view
[USG6000V1]sysname FW2
[FW2]interface GigabitEthernet 1/0/5.1
[FW2-GigabitEthernet1/0/5.1]vlan-type dot1q 10
[FW2-GigabitEthernet1/0/5.1]ip address 192.168.1.3 24
[FW2]interface GigabitEthernet 1/0/5.2
[FW2-GigabitEthernet1/0/5.2]vlan-type dot1q 20
[FW2-GigabitEthernet1/0/5.2]ip address 192.168.2.3 24
[FW2]interface GigabitEthernet 1/0/3.1
[FW2-GigabitEthernet1/0/3.1]vlan-type dot1q 1
[FW2-GigabitEthernet1/0/3.1]ip address 10.3.2.1 30
[FW2]interface GigabitEthernet 1/0/1
[FW2-GigabitEthernet1/0/1]ip address 15.1.1.2 24
[FW2]interface GigabitEthernet 1/0/3
[FW2-GigabitEthernet1/0/3]ip address 10.3.1.1 30
#PE1
<Huawei>system-view
[Huawei]sysname PE1
[PE1]interface GigabitEthernet 0/0/1.1
[PE1-GigabitEthernet0/0/1.1]dot1q termination vid 1
[PE1-GigabitEthernet0/0/1.1]arp broadcast enable
[PE1-GigabitEthernet0/0/1.1]ip address 10.2.2.2 30
[PE1]interface GigabitEthernet 0/0/3.1
[PE1-GigabitEthernet0/0/3.1]dot1q termination vid 1
[PE1-GigabitEthernet0/0/3.1]arp broadcast enable
[PE1-GigabitEthernet0/0/3.1]ip address 10.3.2.2 30
[PE1]interface LoopBack 0
[PE1-LoopBack0]ip address 1.1.1.1 32
[PE1]interface GigabitEthernet0/0/1
[PE1-GigabitEthernet0/0/1]ip address 10.2.1.2 30
[PE1]interface GigabitEthernet0/0/2
[PE1-GigabitEthernet0/0/2]ip address 20.1.1.1 30
[PE1]interface GigabitEthernet0/0/3
[PE1-GigabitEthernet0/0/3]ip address 10.3.1.2 30
#AC1
<AC6605>system-view
[AC6605]sysname AC
[AC]vlan batch 19 20
[AC]interface GigabitEthernet 0/0/1
[AC-GigabitEthernet0/0/1]port link-type trunk
[AC-GigabitEthernet0/0/1]undo port trunk allow-pass vlan 1
[AC-GigabitEthernet0/0/1]port trunk allow-pass vlan 19 20
#FW3
<USG6000V1>system-view
[USG6000V1]sysname FW3
[FW3]interface GigabitEthernet 1/0/1
[FW3-GigabitEthernet1/0/1]ip address 30.1.1.1 30
[FW3]interface GigabitEthernet 1/0/2
[FW3-GigabitEthernet1/0/2]ip address 20.1.3.2 30
#P
<Huawei>system-view
[Huawei]sysname P
[P]interface LoopBack 0
[P-LoopBack0]ip address 2.2.2.2 32
[P]interface GigabitEthernet0/0/1
[P-GigabitEthernet0/0/1]ip address 20.1.2.1 30
[P]interface GigabitEthernet0/0/2
[P-GigabitEthernet0/0/2]ip address 20.1.1.2 30
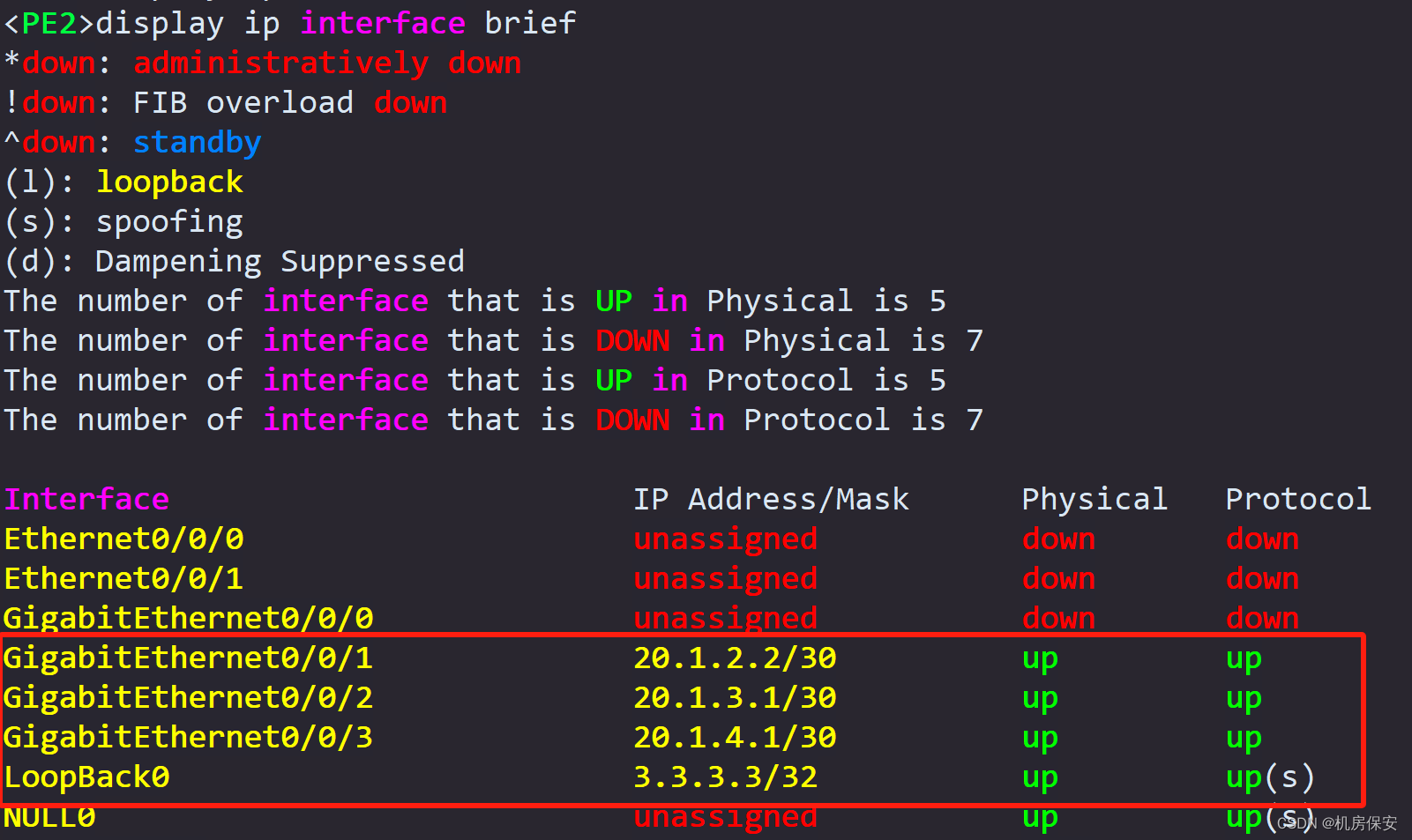
#PE2
<Huawei>system-view
[Huawei]sysname PE2
[PE2]interface LoopBack 0
[PE2-LoopBack0]ip address 3.3.3.3 32
[PE2]interface GigabitEthernet0/0/1
[PE2-GigabitEthernet0/0/1]ip address 20.1.2.2 30
[PE2]interface GigabitEthernet0/0/2
[PE2-GigabitEthernet0/0/2]ip address 20.1.3.1 30
[PE2]interface GigabitEthernet0/0/3
[PE2-GigabitEthernet0/0/3]ip address 20.1.4.1 30
#Internet
<Huawei>system-view
[Huawei]sysname Internet
[Internet]interface LoopBack 0
[Internet-LoopBack0]ip address 16.16.16.16 32
[Internet]interface GigabitEthernet0/0/3
[Internet-GigabitEthernet0/0/3]ip address 20.1.4.2 30
#DC-GW
<Huawei>system-view
[Huawei]sysname DC-GW
[DC-GW]interface LoopBack 0
[DC-GW-LoopBack0]ip address 11.11.11.11 32
[DC-GW]interface GigabitEthernet0/0/1
[DC-GW-GigabitEthernet0/0/1]ip address 30.1.1.2 30
[DC-GW]interface GigabitEthernet0/0/2
[DC-GW-GigabitEthernet0/0/2]ip address 30.1.2.1 30
[DC-GW]interface GigabitEthernet0/0/3
[DC-GW-GigabitEthernet0/0/3]ip address 30.1.3.1 30
#Leaf1
<Huawei>system-view
[Huawei]sysname Leaf1
[Leaf1]interface LoopBack 0
[Leaf1-LoopBack0]ip address 12.12.12.12 32
[Leaf1]interface GigabitEthernet0/0/1
[Leaf1-GigabitEthernet0/0/1]ip address 172.16.3.254 24
[Leaf1]interface GigabitEthernet0/0/2
[Leaf1-GigabitEthernet0/0/2]ip address 30.1.2.2 30
[Leaf1]interface GigabitEthernet0/0/3
[Leaf1-GigabitEthernet0/0/3]ip address 172.16.1.254 24
#Leaf2
<Huawei>system-view
[Huawei]sysname Leaf2
[Leaf2]interface LoopBack 0
[Leaf2-LoopBack0]ip address 13.13.13.13 32
[Leaf2]interface GigabitEthernet0/0/1
[Leaf2-GigabitEthernet0/0/1]ip address 172.16.2.254 24
[Leaf2]interface GigabitEthernet0/0/3
[Leaf2-GigabitEthernet0/0/3]ip address 30.1.3.2 30验证:







任务3:MSTP配置
为了实现二层网络的防环功能和流量负载均衡的目的,需要在SW1、SW2、SW3上配置 MSTP功能
- 配置region名称为RG1。
- 将VLAN2到VLAN10映射到生成树实例instance 1,将VLAN11到VLAN20映射到生成树实例instance 2。
- 配置SW2为instance 1的根桥,instance 2的备份根桥;配置SW3为instance 2的根桥,instance 1的备份根桥。
- 配置SW2的GE 0/0/1口为STP根保护,关闭GE0/0/5的STP功能;配置SW3的GE0/0/2口为STP根保护,配置GE0/0/1口为STP边缘端口,关闭GE0/0/5口的STP功能。
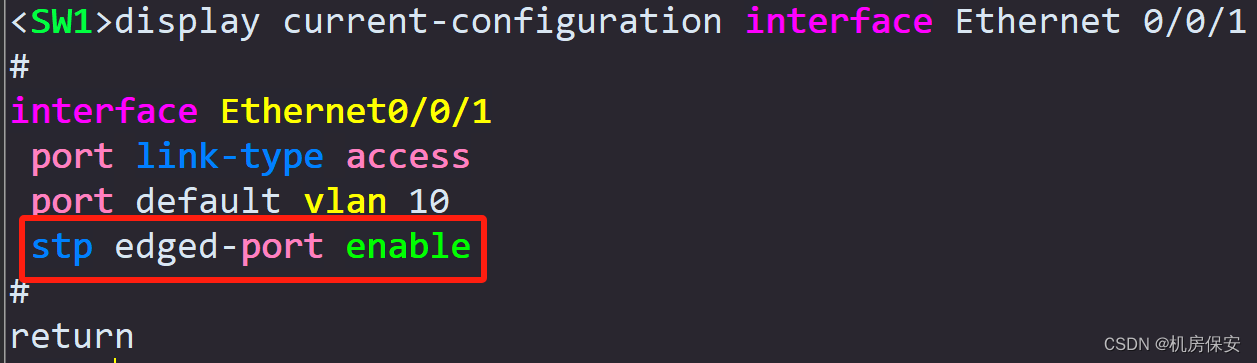
- 配置SW1的E0/0/1和E0/0/2口为STP边缘端口。
配置过程:
任务3:MSTP
#SW2
[SW2]stp region-configuration
[SW2-mst-region]region-name RG1
[SW2-mst-region]instance 1 vlan 2 to 10
[SW2-mst-region]instance 2 vlan 11 to 20
[SW2-mst-region]active region-configuration
[SW2]stp instance 1 root primary
[SW2]stp instance 2 root secondary
[SW2]interface GigabitEthernet 0/0/1
[SW2-GigabitEthernet0/0/1]stp root-protection
[SW2]interface GigabitEthernet 0/0/5
[SW2-GigabitEthernet0/0/5]stp disable
#SW3
[SW3]stp region-configuration
[SW3-mst-region]region-name RG1
[SW3-mst-region]instance 1 vlan 2 to 10
[SW3-mst-region]instance 2 vlan 11 to 20
[SW3-mst-region]active region-configuration
[SW3]stp instance 1 root secondary
[SW3]stp instance 2 root primary
[SW3]interface GigabitEthernet 0/0/2
[SW3-GigabitEthernet0/0/2]stp root-protection
[SW3]interface GigabitEthernet 0/0/1
[SW3-GigabitEthernet0/0/1]stp edged-port enable
[SW3]interface GigabitEthernet 0/0/5
[SW3-GigabitEthernet0/0/5]stp disable
#SW1
[SW1]stp region-configuration
[SW1-mst-region]region-name RG1
[SW1-mst-region]instance 1 vlan 2 to 10
[SW1-mst-region]instance 2 vlan 11 to 20
[SW1-mst-region]active region-configuration
[SW1]port-group group-member Ethernet 0/0/1 Ethernet 0/0/2
[SW1-port-group]stp edged-port enable 验证:




任务4:防火墙安全区域配置
为实现网络安全的需求,需要部署防火墙,按要求规划安全区域,并且按照最小权限原则放开必要的端口权限,确保业务的正常通信。
请按照如下表格2-4的数据规划完成防火墙的安全区域配置。
验证:



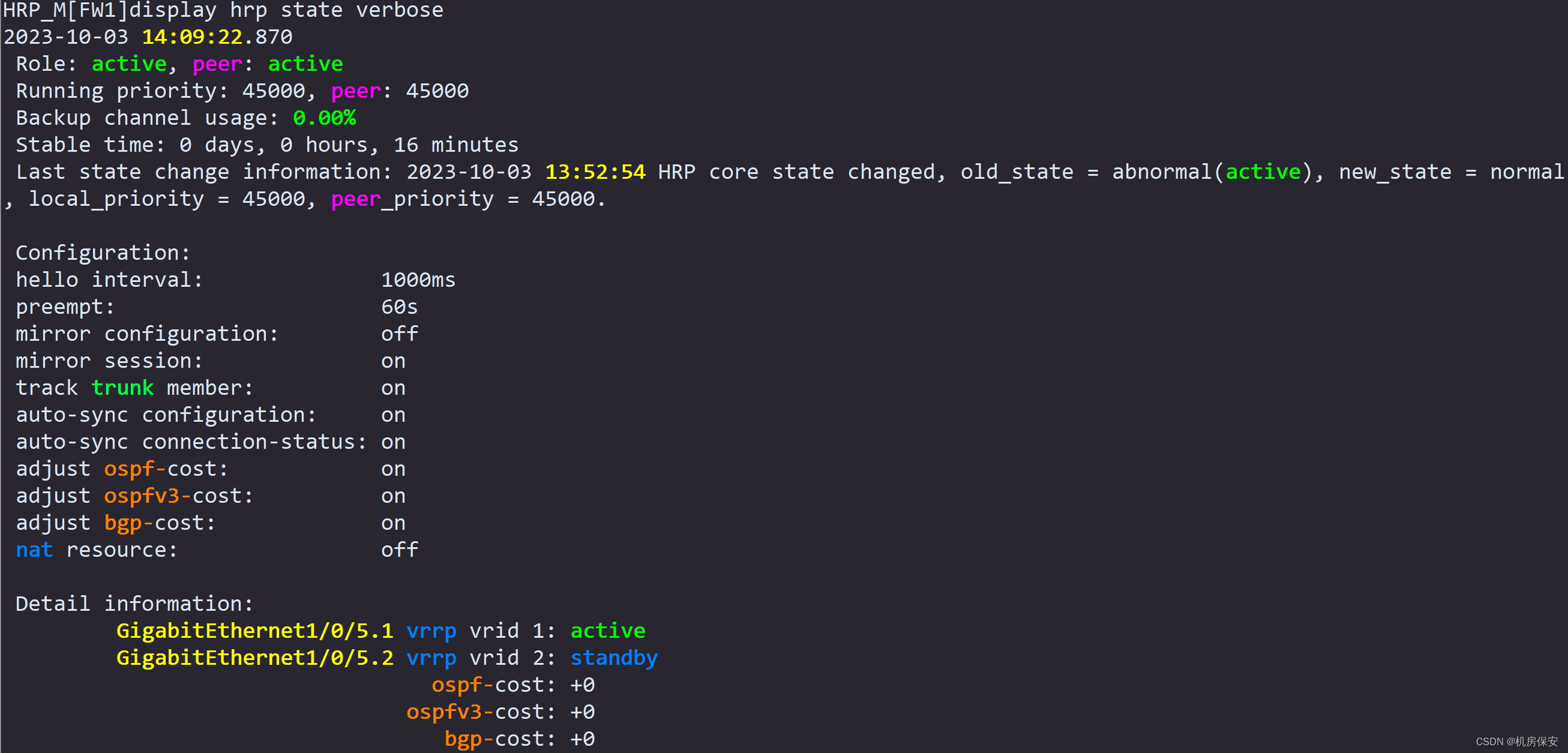
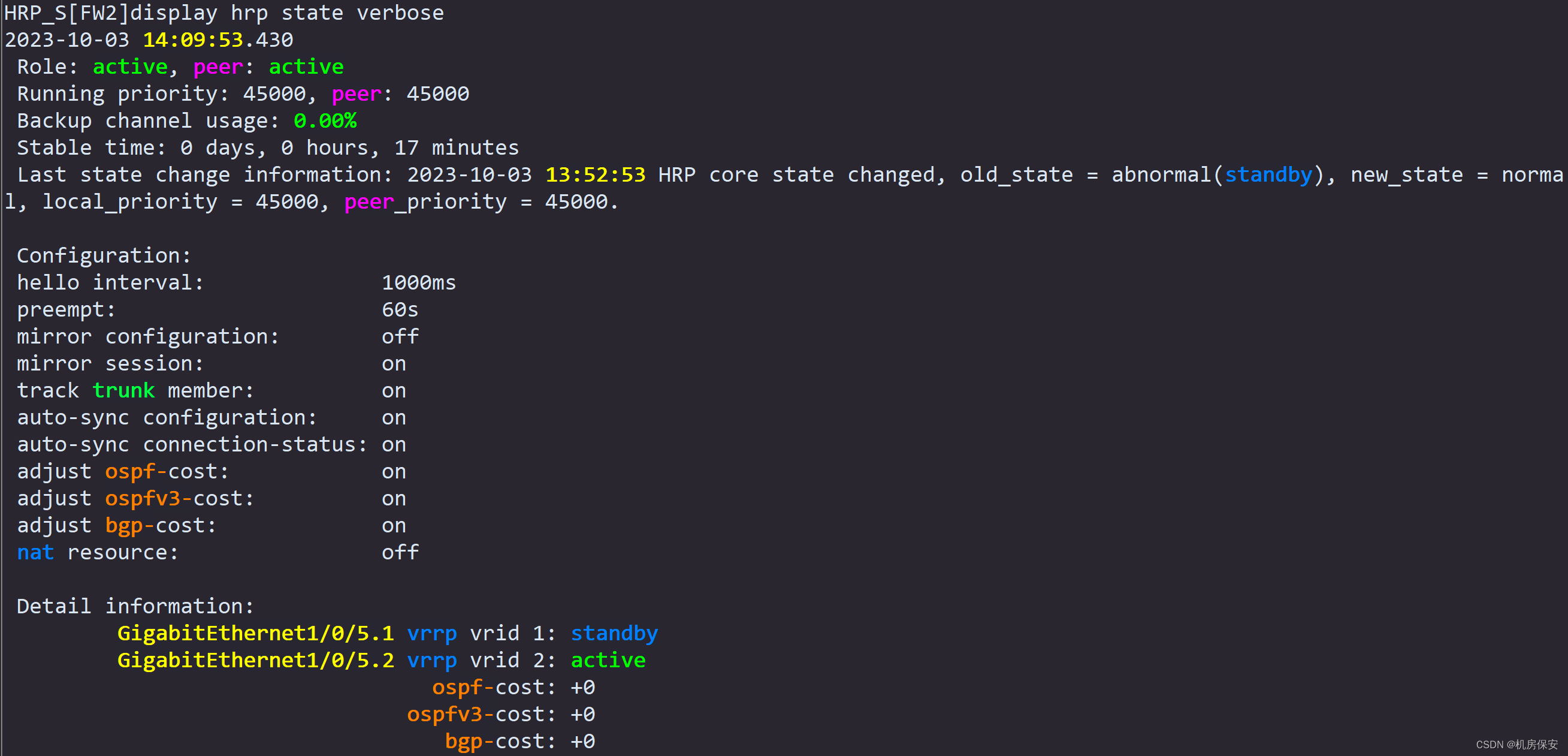
任务5:防火墙VRRP、双机热备和安全策略配置
为了避免防火墙单点故障,且充分利用网络资源,采用负载均衡模式部署防火墙双机热备,以增加网络健壮性。
- 按表2-5的VRRP规划,完成VRRP配置。
- 使能FW1和FW2的hrp功能,配置FW1和FW2的G1/0/1口为HRP接口,并使能session快速备份功能。
- 然后按照需求完成防火墙安全策略配置。
- FW1:创建名称为“web”的安全策略,放通web服务流量;
- FW1:创建名称为“Wireless”的安全策略,放通WLAN流量;
- FW3:创建名称为“web”的安全策略,放通web服务流量;
- 在FW3配置NAT server功能,global地址和端口号分别为100.1.1.1和8080,inside地址和协议分别为172.16.1.1和http。
安全策略禁止全放通,要求所有安全策略按照实际细化配置。
配置过程:
任务4:防火墙安全区域配置
#FW1
[FW1]firewall zone trust
[FW1-zone-trust]add interface GigabitEthernet 1/0/5.1
[FW1-zone-trust]add interface GigabitEthernet 1/0/5.2
[FW1]firewall zone untrust
[FW1-zone-untrust]add interface GigabitEthernet 1/0/3
[FW1-zone-untrust]add interface GigabitEthernet 1/0/3.1
[FW1]firewall zone dmz
[FW1-zone-dmz]add interface GigabitEthernet 1/0/1
#FW2
[FW2]firewall zone trust
[FW2-zone-trust]add interface GigabitEthernet 1/0/5.1
[FW2-zone-trust]add interface GigabitEthernet 1/0/5.2
[FW2]firewall zone untrust
[FW2-zone-untrust]add interface GigabitEthernet 1/0/3
[FW2-zone-untrust]add interface GigabitEthernet 1/0/3.1
[FW2]firewall zone dmz
[FW2-zone-dmz]add interface GigabitEthernet 1/0/1
#FW3
[FW3]firewall zone trust
[FW3-zone-trust]add interface GigabitEthernet 1/0/1
[FW3]firewall zone untrust
[FW3-zone-untrust]add interface GigabitEthernet 1/0/2
任务5:防火墙VRRP、双机热备和安全策略配置
防火墙VRRP
#FW1
[FW1]interface GigabitEthernet 1/0/5.1
[FW1-GigabitEthernet1/0/5.1]vrrp vrid 1 virtual-ip 192.168.1.254 active
[FW1]interface GigabitEthernet 1/0/5.2
[FW1-GigabitEthernet1/0/5.2]vrrp vrid 2 virtual-ip 192.168.2.254 standby
#FW2
[FW2]interface GigabitEthernet 1/0/5.1
[FW2-GigabitEthernet1/0/5.1]vrrp vrid 1 virtual-ip 192.168.1.254 standby
[FW2]interface GigabitEthernet 1/0/5.2
[FW2-GigabitEthernet1/0/5.2]vrrp vrid 2 virtual-ip 192.168.2.254 active
HRP
#FW1
[FW1]hrp interface GigabitEthernet 1/0/1 remote 15.1.1.2
[FW1]hrp enable
HRP_M[FW1]hrp mirror session enable
HRP_M[FW1]hrp auto-sync config static-route (+B)
#FW2
[FW2]hrp interface GigabitEthernet 1/0/1 remote 15.1.1.1
[FW2]hrp enable
HRP_S[FW2]hrp mirror session enable
安全策略
#FW1
HRP_M[FW1]security-policy (+B)
HRP_M[FW1-policy-security]rule name web (+B)
HRP_M[FW1-policy-security-rule-web]source-zone trust (+B)
HRP_M[FW1-policy-security-rule-web]destination-zone untrust (+B)
HRP_M[FW1-policy-security-rule-web]source-address 192.168.1.1 32 (+B)
HRP_M[FW1-policy-security-rule-web]destination-address 172.16.1.1 32 (+B)
HRP_M[FW1-policy-security-rule-web]service http (+B)
HRP_M[FW1-policy-security-rule-web]service https (+B)
HRP_M[FW1-policy-security-rule-web]action permit (+B)
HRP_M[FW1-policy-security]rule name Wireless (+B)
HRP_M[FW1-policy-security-rule-Wireless]source-zone trust (+B)
HRP_M[FW1-policy-security-rule-Wireless]source-zone local (+B)
HRP_M[FW1-policy-security-rule-Wireless]source-zone untrust (+B)
HRP_M[FW1-policy-security-rule-Wireless]destination-zone untrust (+B)
HRP_M[FW1-policy-security-rule-Wireless]destination-zone trust (+B)
HRP_M[FW1-policy-security-rule-Wireless]destination-zone local (+B)
HRP_M[FW1-policy-security-rule-Wireless]source-address 192.168.2.0 24 (+B)
HRP_M[FW1-policy-security-rule-Wireless]action permit (+B)
HRP_M[FW1]int g1/0/5.1 (+B)
HRP_M[FW1-GigabitEthernet1/0/5.1]service-manage ping permit (+B)
HRP_M[FW1]int g1/0/5.2 (+B)
HRP_M[FW1-GigabitEthernet1/0/5.2]service-manage ping permit (+B)
#FW3
[FW3]security-policy
[FW3-policy-security]rule name web
[FW3-policy-security-rule-web]source-zone untrust
[FW3-policy-security-rule-web]destination-zone trust
[FW3-policy-security-rule-web]source-address 192.168.1.1 32
[FW3-policy-security-rule-web]destination-address 172.16.1.1 32
[FW3-policy-security-rule-web]service http
[FW3-policy-security-rule-web]service https
[FW3-policy-security-rule-web]action permit
[FW3-policy-security]rule name BGP
[FW3-policy-security-rule-BGP]source-zone untrust
[FW3-policy-security-rule-BGP]destination-zone local
[FW3-policy-security-rule-BGP]source-address 20.1.3.1 mask 255.255.255.255
[FW3-policy-security-rule-BGP]destination-address 20.1.3.2 mask 255.255.255.255
[FW3-policy-security-rule-BGP]service bgp
[FW3-policy-security-rule-BGP]service tcp
[FW3-policy-security-rule-BGP]action permit
[FW3]security-policy
[FW3-policy-security]rule name OSPF
[FW3-policy-security-rule-OSPF]source-zone trust
[FW3-policy-security-rule-OSPF]destination-zone local
[FW3-policy-security-rule-OSPF]source-address 30.1.1.2
[FW3-policy-security-rule-OSPF]service ospf
[FW3-policy-security-rule-OSPF]action permit
NAT Server
#FW3
[FW3]nat server nat_server zone untrust protocol tcp global 100.1.1.1 8080 inside 172.16.1.1 www验证:


任务6:公网静态路由配置(路由可参考图2-2、图2-3及描述)
- 为了实现将去往Internet的流量和去往数据中心Web-server的流量引流到广域网上,需要在FW1和FW2上配置静态路由实现。PE1的主接口用于接收Internet流量,PE1的子接口用于接收Web-Server流量。在PE1上配置两台指向WLAN客户端的回程静态路由,回程路由需要指向FW1和FW2实现负载分担,用于引导Internet回程流量。
- 因需要发布global地址段到VPN,所以需要在防火墙FW3上配置到Web-Server global地址100.1.1.1的静态黑洞路由,用于引导Web-Server的VPN流量。
- 在FW3上配置一条缺省路由,引导Web-Server从数据中心到企业内网的回程流量。
配置过程:
#FW1
[FW1]ip route-static 0.0.0.0 0.0.0.0 10.2.1.2
[FW1]ip route-static 100.1.1.1 255.255.255.255 10.2.2.2
#FW2
[FW2]ip route-static 0.0.0.0 0.0.0.0 10.3.1.2
#FW3
[FW3]ip route-static 100.1.1.1 32 NULL 0
[FW3]ip route-static 100.1.1.1 255.255.255.255 10.3.2.2
[FW3]ip route-static 0.0.0.0 0.0.0.0 20.1.3.1
#PE1
[PE1]ip route-static 192.168.2.0 24 10.2.1.1
[PE1]ip route-static 192.168.2.0 24 10.3.1.1验证:



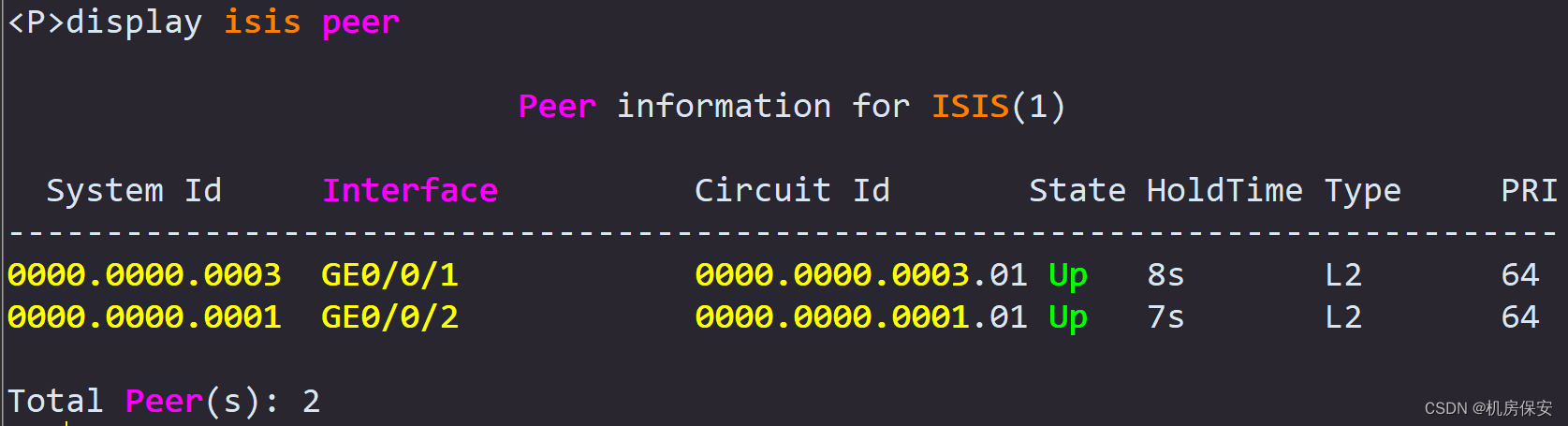
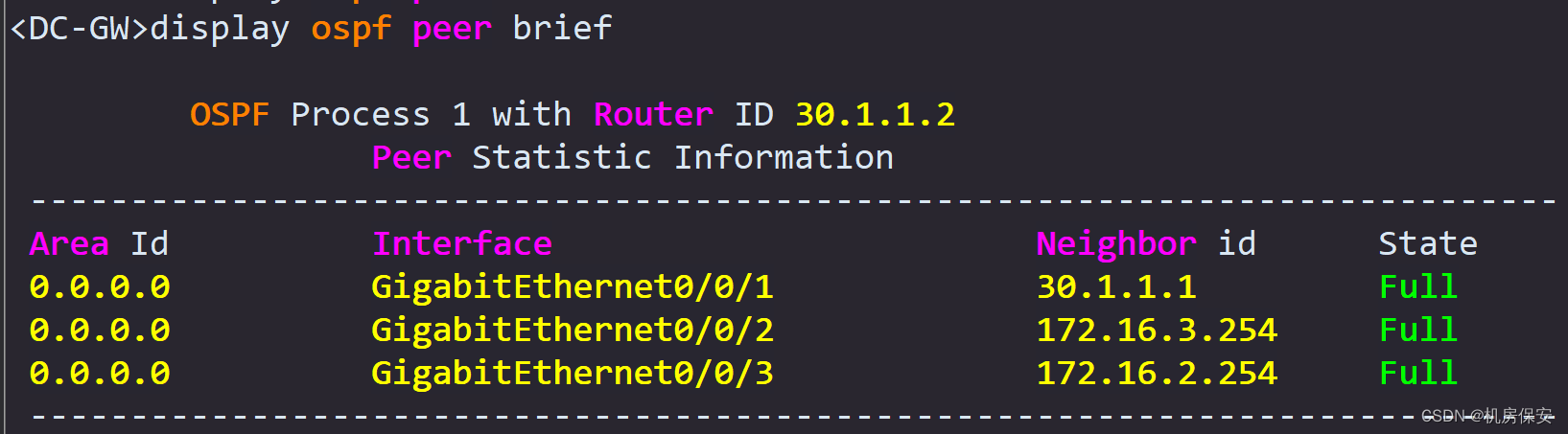
任务7:公网动态路由配置
- 在PE1、P、PE2组成的广域网里部署ISIS路由协议,进程ID为1,ISIS域配置为Level-2层,区域ID号为01,systemid值自行规划。要求PE1的Loopback0和GE0/0/2,P路由器Loopback0、GE0/0/1和GE0/0/2,PE2的Loopback0和GE0/0/1使能ISIS协议。
- 为了提高网络安全性,需要配置对LSP、CSNP、PSNP报文MD5认证功能,认证密码为ICTEXAM。
- DC数据中心部署OSPF,DC内所有路由器均部署在ospf area 0骨干区域,要求FW3的GE1/0/1,DC-GW的loopback0、GE0/0/1、GE0/0/2和GE0/0/3,Leaf1的Loopback0、GE0/0/2和GE0/0/3,Leaf2的loopback0和GE0/0/3所在的地址段发布到OSPF区域。
- FW3往OSPF路由域发布缺省路由引导Web-Server服务器到企业内网的回程流量。要求当FW3与PE2的链路中断后,FW3可以同步停止发布缺省路由,避免产生无效流量。
- PE1的loopback0和P路由器的loopback0配置为IBGP邻居,PE2的loopback0和P路由器的loopback0配置为IBGP邻居,P路由器配置IBGP邻居组,添加PE1和PE2为邻居组成员,P路由器配置为反射器RR,PE1和PE2是P路由器的客户端。PE2的GE0/0/3和Internet路由器的GE0/0/3配置为EBGP邻居。把Internet路由器上的loopback0地址提供EBGP通告给对端路由器PE2,引导流量上行。(路由可参考图2-2及描述)
配置过程:
任务7:公网动态路由配置
ISIS
#PE1
[PE1]isis 1
[PE1-isis-1]network-entity 01.0000.0000.0001.00
[PE1-isis-1]is-level level-2
[PE1-isis-1]domain-authentication-mode md5 ICTEXAM
[PE1]interface LoopBack 0
[PE1-LoopBack0]isis enable 1
[PE1]interface GigabitEthernet0/0/2
[PE1-GigabitEthernet0/0/2]isis enable 1
#P
[P]isis 1
[P-isis-1]network-entity 01.0000.0000.0002.00
[P-isis-1]is-level level-2
[PE1-isis-1]domain-authentication-mode md5 ICTEXAM
[P]interface LoopBack 0
[P-LoopBack0]isis enable 1
[P]interface GigabitEthernet0/0/1
[P-GigabitEthernet0/0/1]isis enable 1
[P]interface GigabitEthernet0/0/2
[P-GigabitEthernet0/0/2]isis enable 1
#PE2
[PE2]isis 1
[PE2-isis-1]network-entity 01.0000.0000.0003.00
[PE2-isis-1]is-level level-2
[PE1-isis-1]domain-authentication-mode md5 ICTEXAM
[PE2]interface LoopBack 0
[PE2-LoopBack0]isis enable 1
[PE2]interface GigabitEthernet0/0/1
[PE2-GigabitEthernet0/0/1]isis enable 1
OSPF
#FW3
[FW3]ospf 1
[FW3-ospf-1]default-route-advertise type 1
[FW3-ospf-1]area 0
[FW3-ospf-1-area-0.0.0.0]network 30.1.1.1 0.0.0.0
#DC-GW
[DC-GW]ospf 1
[DC-GW-ospf-1]area 0
[DC-GW-ospf-1-area-0.0.0.0]network 11.11.11.11 0.0.0.0
[DC-GW-ospf-1-area-0.0.0.0]network 30.1.1.2 0.0.0.0
[DC-GW-ospf-1-area-0.0.0.0]network 30.1.2.1 0.0.0.0
[DC-GW-ospf-1-area-0.0.0.0]network 30.1.3.1 0.0.0.0
#Leaf1
[Leaf1]ospf 1
[Leaf1-ospf-1]area 0
[Leaf1-ospf-1-area-0.0.0.0]network 12.12.12.12 0.0.0.0
[Leaf1-ospf-1-area-0.0.0.0]network 30.1.2.2 0.0.0.0
[Leaf1-ospf-1-area-0.0.0.0]network 172.16.1.254 0.0.0.0
#Leaf2
[Leaf2]ospf 1
[Leaf2-ospf-1]area 0
[Leaf2-ospf-1-area-0.0.0.0]network 30.1.3.2 0.0.0.0
[Leaf2-ospf-1-area-0.0.0.0]network 13.13.13.13 0.0.0.0
BGP
#PE1
[PE1]bgp 100
[PE1-bgp]peer 2.2.2.2 as-number 100
[PE1-bgp]peer 2.2.2.2 connect-interface LoopBack0
#P
[P]bgp 100
[P-bgp]group PE1-PE2 internal
[P-bgp]peer 1.1.1.1 group PE1-PE2
[P-bgp]peer 3.3.3.3 group PE1-PE2
[P-bgp]peer PE1-PE2 connect-interface LoopBack 0
[P-bgp]peer PE1-PE2 reflect-client
#PE2
[PE2]bgp 100
[PE2-bgp]peer 2.2.2.2 as-number 100
[PE2-bgp]peer 2.2.2.2 connect-interface LoopBack 0
[PE2-bgp]peer 20.1.4.2 as-number 200
[PE2-bgp]peer 20.1.3.2 as-number 300
[PE2-bgp]peer 2.2.2.2 next-hop-local
#Internet
[Internet]bgp 200
[Internet-bgp]peer 20.1.4.1 as-number 100
[Internet-bgp]network 16.16.16.16 32
#FW3
[Internet]bgp 300
[Internet-bgp]peer 20.1.3.1 as-number 100
[Internet-bgp]network 100.1.1.1 32验证:


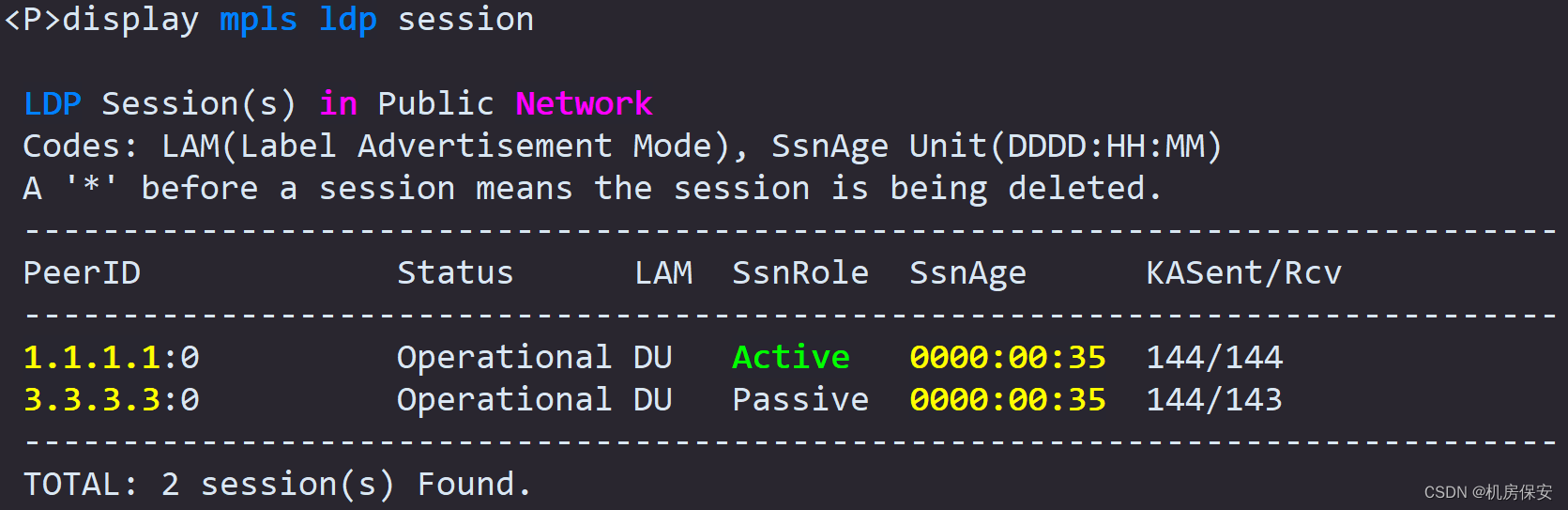
任务8:MPLS VPN(路由可参考图2-3及描述)
- PE1的loopback0和P路由器的Loopback0配置为MP-IBGP邻居,PE2的loopback0和P路由器的loopback0配置MP-IBGP邻居,P路由器配置为VPN反射器vRR,PE1和PE2是P路由器的客户端。为了能将路由顺利传递,需要在P路由器上配置undo policy vpn-target。
- PE1、P、PE2使能MPLS和MPLS LDP,并将各自的loopback0接口地址配置为MPLS LSR ID。PE1的GE0/0/2,P路由器的GE0/0/1和GE0/0/2,PE2的FE0/0/1均使能MPLS和MPLS LDP。
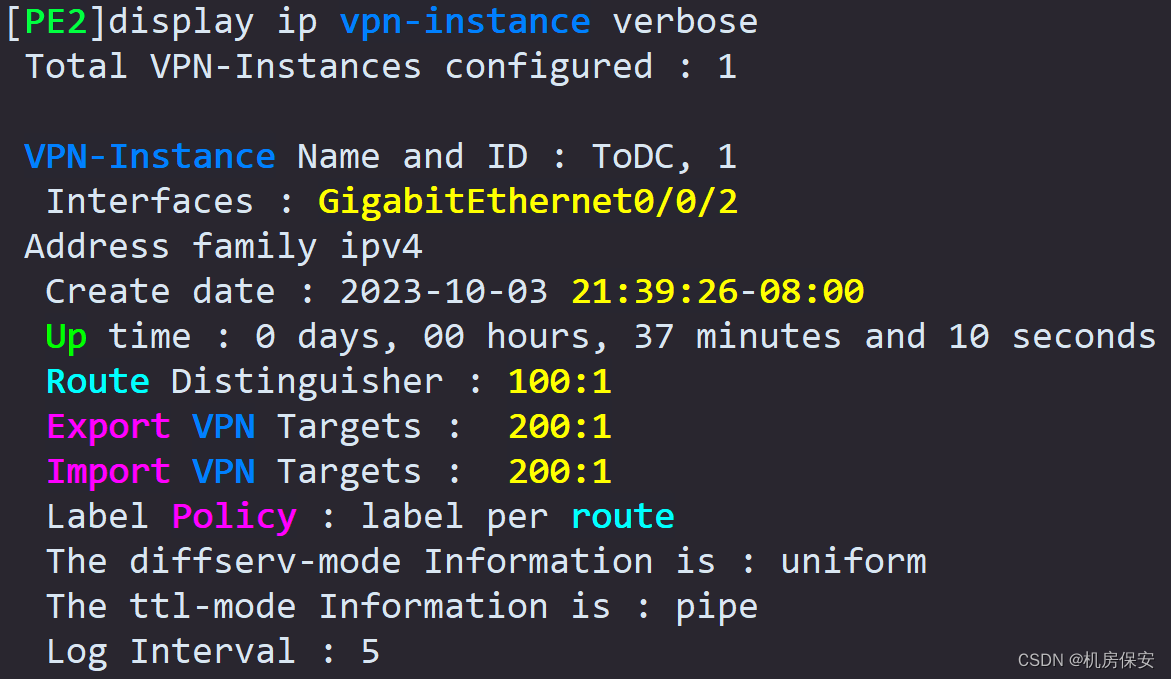
- PE1和PE2配置VPN实例,命名为ToDC,RD值为100:1,Export RT和Import RT均为200:1。把PE1的GE0/0/3.1接口绑定到PE1的VPN实例ToDC,PE2的GE0/0/2绑定到PE2的VPN实例ToDC。
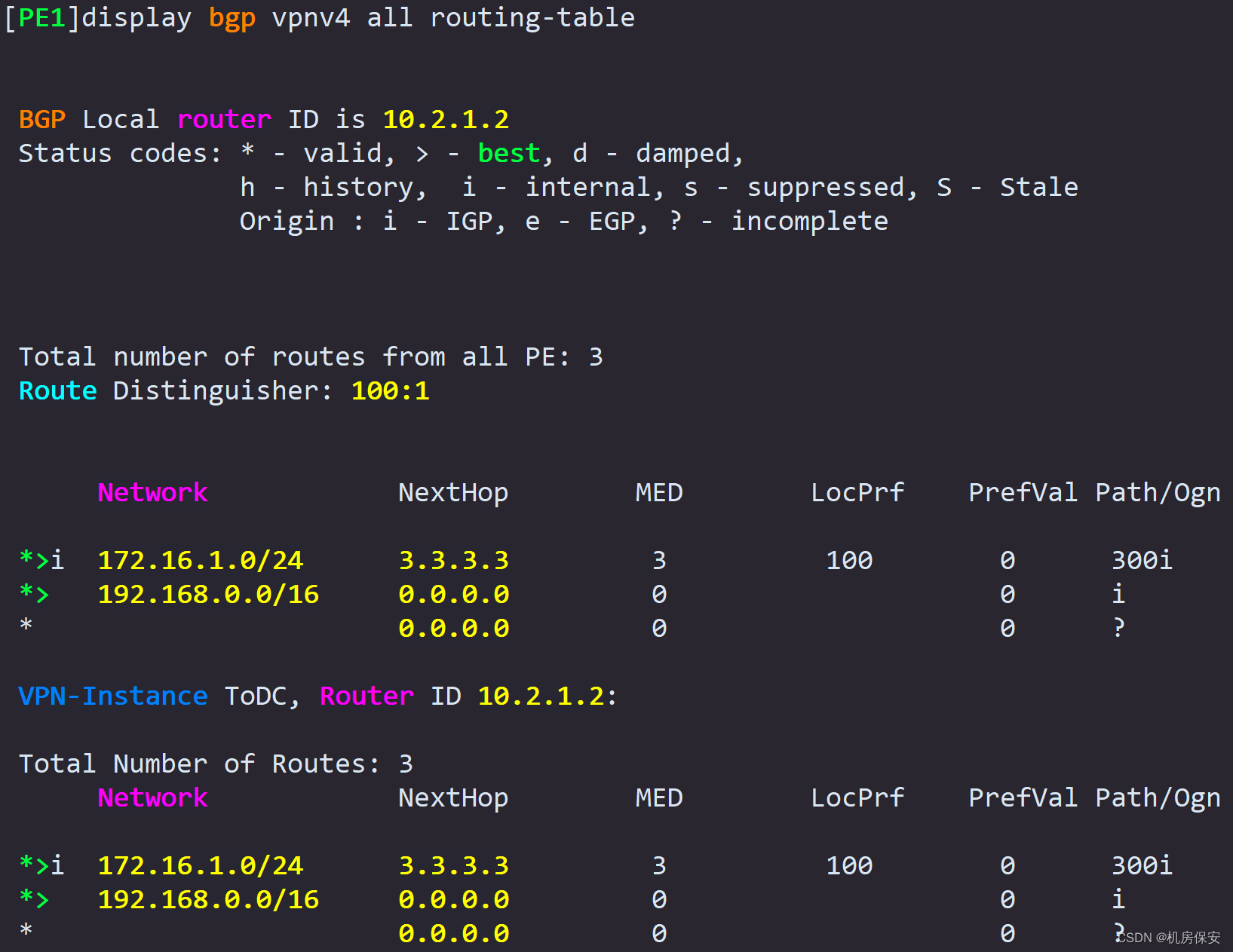
- 在PE1的VPN实例ToDC内配置静态路由,目的网段为Web-Client地址段192.168.0.0/16,吓一跳指向FW1和FW2的GE1/0/3.1,以实现Web-Server回程流量的负载分担。将配置的两条等价静态路由引入到VPN实例ToDC中,让MP-IBGP通告给PE2,引导Web-Server的回程流量。
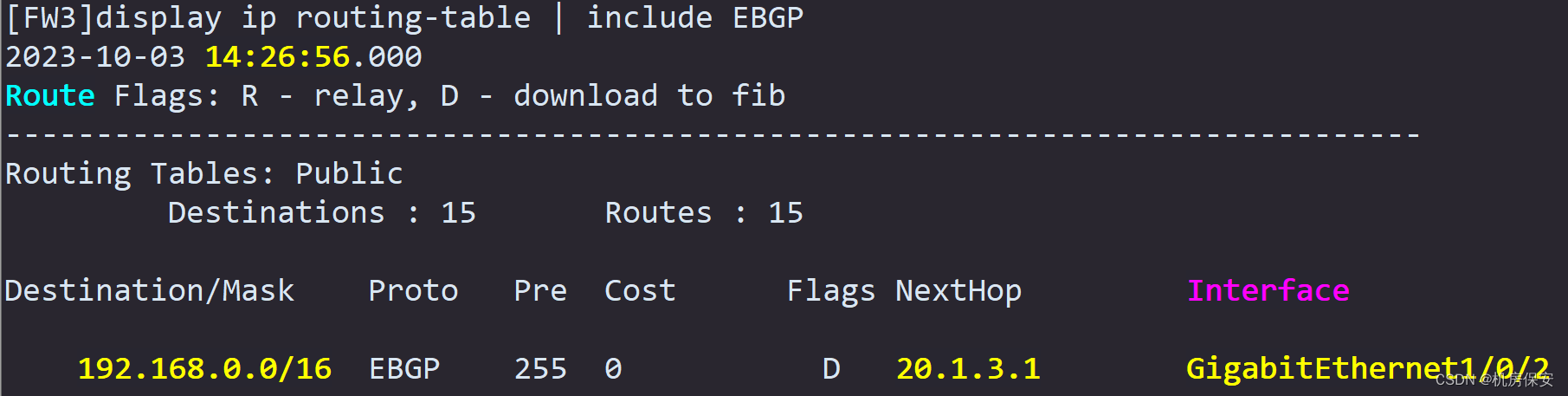
- PE2的VPN实例ToDC上的接口GE0/0/2与FW3的GE1/0/2配置为EBGP邻居,通过EBGP邻居交换Web-Server业务路由。
任务8:MPLS VPN配置
VPN实例
#PE1
[PE1]ip vpn-instance ToDC
[PE1-vpn-instance-ToDC]route-distinguisher 100:1
[PE1-vpn-instance-ToDC-af-ipv4]vpn-target 200:1 both
[PE1]interface GigabitEthernet0/0/3.1
[PE1-GigabitEthernet0/0/3.1]ip binding vpn-instance ToDC
[PE1-GigabitEthernet0/0/3.1]ip address 10.3.2.2 30
[PE1]interface GigabitEthernet0/0/1.1
[PE1-GigabitEthernet0/0/1.1]ip binding vpn-instance ToDC
[PE1-GigabitEthernet0/0/1.1]ip address 10.2.2.2 30
#PE2
[PE2]ip vpn-instance ToDC
[PE2-vpn-instance-ToDC]route-distinguisher 100:1
[PE2-vpn-instance-ToDC-af-ipv4]vpn-target 200:1 both
[PE2]interface GigabitEthernet0/0/2
[PE2-GigabitEthernet0/0/2]ip binding vpn-instance ToDC
[PE2-GigabitEthernet0/0/2]ip address 20.1.3.1 30
MPLS
#PE1
[PE1]mpls lsr-id 1.1.1.1
[PE1]mpls
[PE1]mpls ldp
[PE1]interface GigabitEthernet0/0/2
[PE1-GigabitEthernet0/0/2]mpls
[PE1-GigabitEthernet0/0/2]mpls ldp
#P
[P]mpls lsr-id 2.2.2.2
[P]mpls
[P]mpls ldp
[P]interface GigabitEthernet0/0/1
[P-GigabitEthernet0/0/1]mpls
[P-GigabitEthernet0/0/1]mpls ldp
[P]interface GigabitEthernet0/0/2
[P-GigabitEthernet0/0/2]mpls
[P-GigabitEthernet0/0/2]mpls ldp
#PE2
[PE2]mpls lsr-id 3.3.3.3
[PE2]mpls
[PE2]mpls ldp
[PE2]interface GigabitEthernet0/0/1
[PE2-GigabitEthernet0/0/1]mpls
[PE2-GigabitEthernet0/0/1]mpls ldp
MP-BGP
#PE1
[PE1]bgp 100
[PE1-bgp]ipv4-family vpnv4
[PE1-bgp-af-vpnv4]peer 2.2.2.2 enable
#P
[P]bgp 100
[P-bgp]ipv4-family vpnv4
[P-bgp-af-vpnv4]undo policy vpn-target
[P-bgp-af-vpnv4]peer 1.1.1.1 enable
[P-bgp-af-vpnv4]peer 3.3.3.3 enable
[P-bgp-af-vpnv4]peer 1.1.1.1 reflect-client
[P-bgp-af-vpnv4]peer 3.3.3.3 reflect-client
#PE2
[PE2-bgp]ipv4-family vpn-instance ToDC
[PE2-bgp-ToDC]peer 20.1.3.2 as-number 300
[PE2-bgp]ipv4-family vpnv4
[PE2-bgp-af-vpnv4]peer 2.2.2.2 enable
[PE2-bgp-af-vpnv4]peer 2.2.2.2 next-hop-local
VPN静态路由
#PE1
[PE1]ip route-static vpn-instance ToDC 192.168.0.0 16 10.2.2.1
[PE1]ip route-static vpn-instance ToDC 192.168.0.0 16 10.3.2.1
[PE1]bgp 100
[PE1-bgp]ipv4-family vpn-instance ToDC
[PE1-bgp-ToDC]network 10.3.2.0 30
[PE1-bgp-ToDC]network 192.168.0.0 16验证:

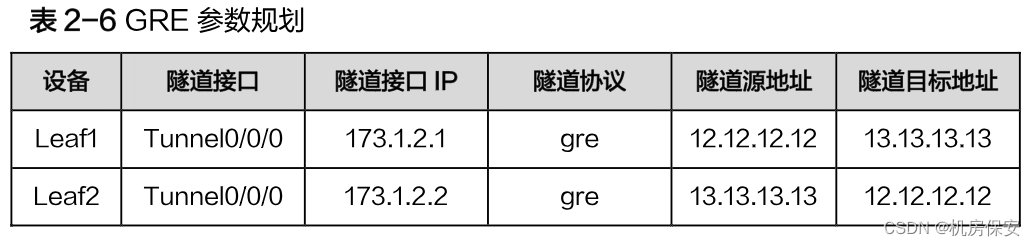
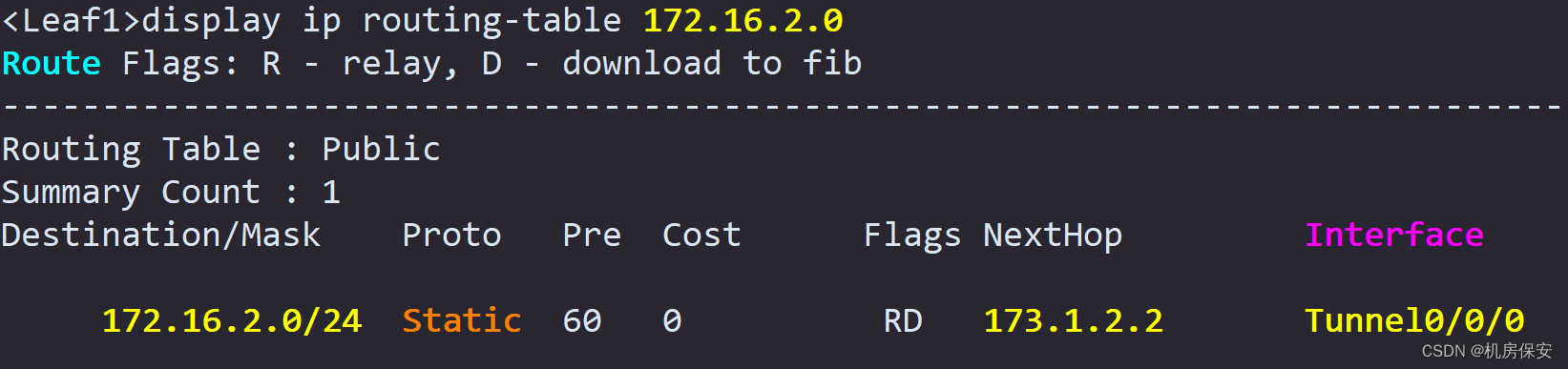
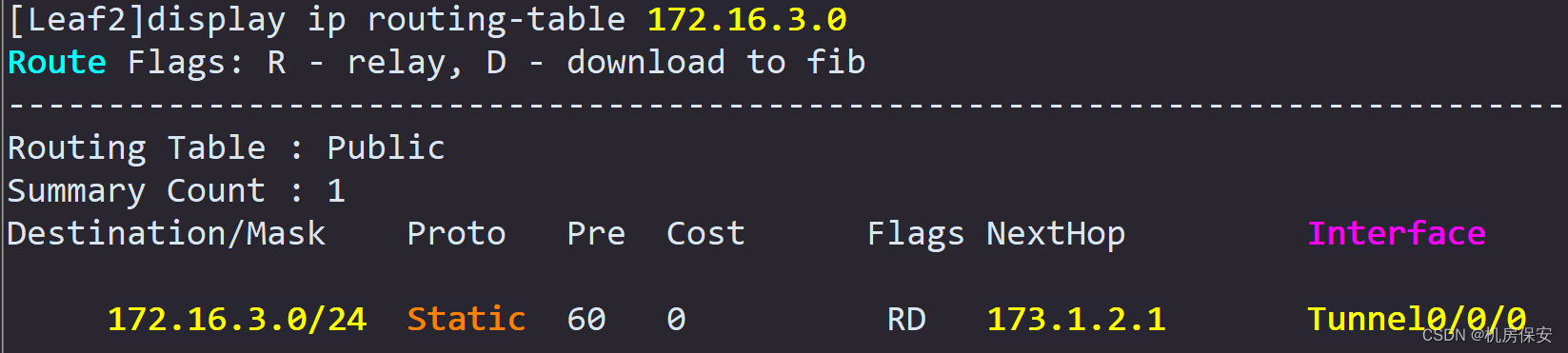
任务9:GRE
- 数据中心的租户会部署虚拟私有网络,该虚拟私有网络划分两个子网,VM1属于子网1(172.16.3.0/24),VM2属于子网2(172.16.2.0/24),为实现数据中心位于这两个不同子网的虚拟机互通,需要在VM1的网关Leaf和VM2的网关Leaf2之间部署GRE,根据表2-6参数规划完成GRE隧道配置。
配置过程:
任务9:GRE
#Leaf1
[Leaf1]interface Tunnel 0/0/0
[Leaf1-Tunnel0/0/0]tunnel-protocol gre
[Leaf1-Tunnel0/0/0]ip address 173.1.2.1 30
[Leaf1-Tunnel0/0/0]source 12.12.12.12
[Leaf1-Tunnel0/0/0]destination 13.13.13.13
[Leaf1]ip route-static 172.16.2.0 24 173.1.2.2
#Leaf2
[Leaf2]interface Tunnel 0/0/0
[Leaf2-Tunnel0/0/0]tunnel-protocol gre
[Leaf2-Tunnel0/0/0]ip address 173.1.2.2 30
[Leaf2-Tunnel0/0/0]source 13.13.13.13
[Leaf2-Tunnel0/0/0]destination 12.12.12.12
[Leaf2]ip route-static 172.16.3.0 24 173.1.2.1验证:
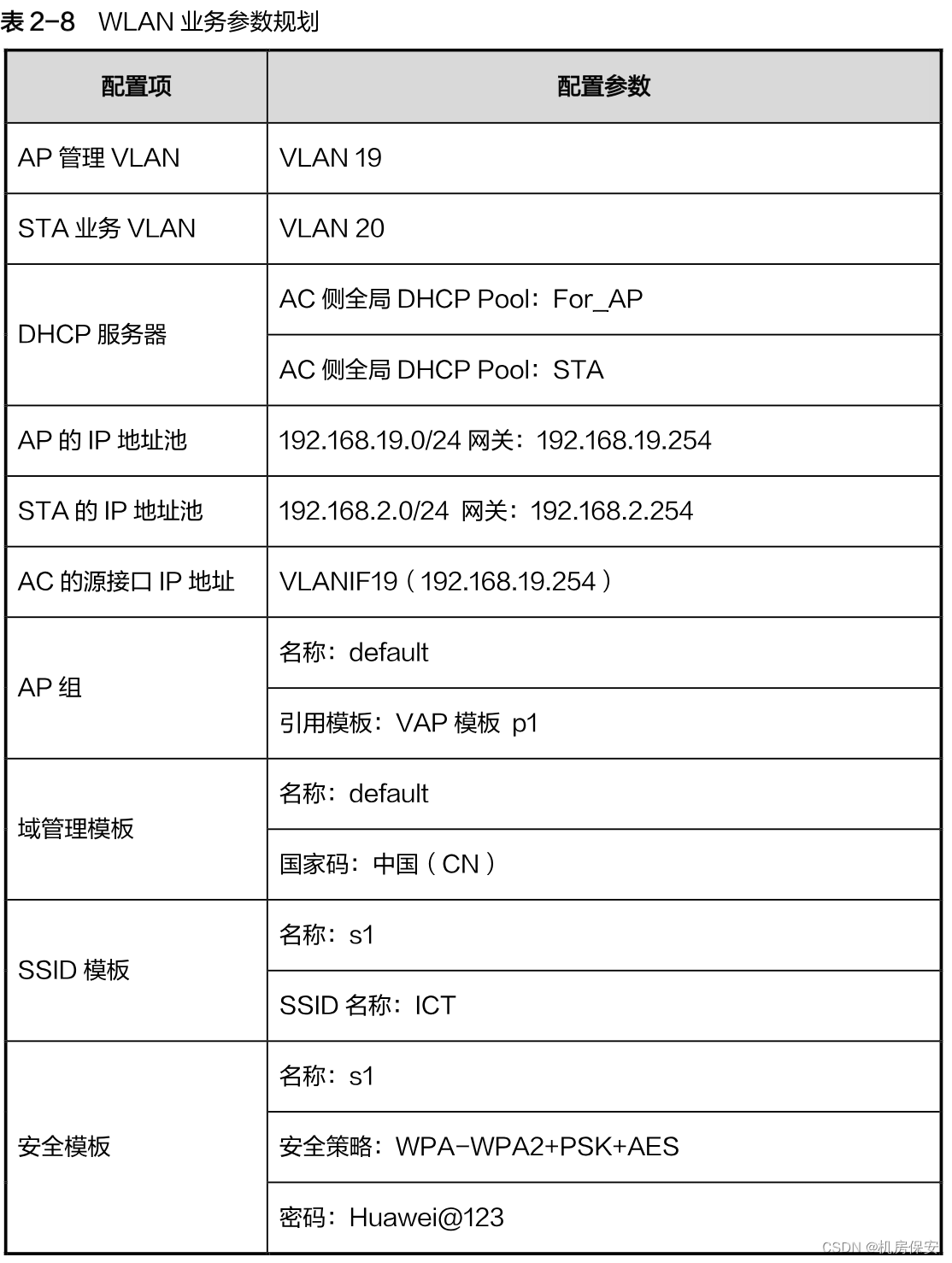
任务10:WLAN
Ⅰ.有线侧网络配置
- 完成企业内网的交换机侧配置,使得AP能够与AC进行通信,AP下的终端到WLAN网络后可以与网关(防火墙)进行通信。
- 完成AC侧底层网络配置,使得AC能够与AP进行通信,AC作为DHCP服务器分别为AP、Station分配IP地址。
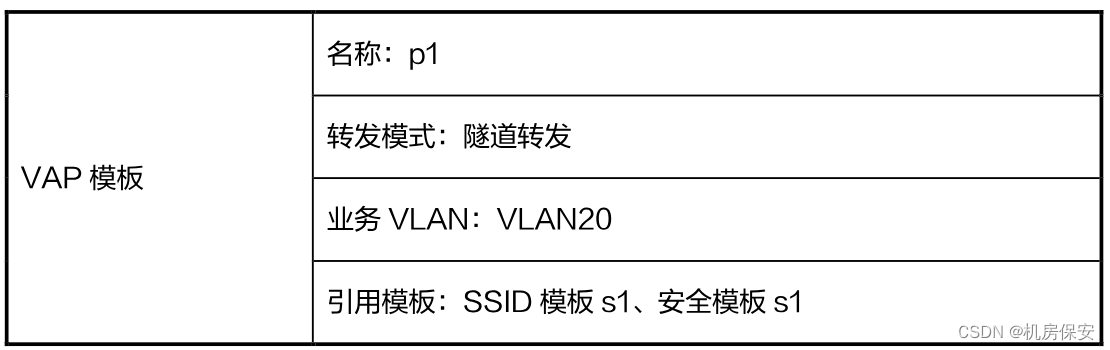
Ⅱ.WLAN业务配置
- WLAN侧业务要求如下:AP与AC处于同一网段,AP直接二层注册到AC,AP通过AC来转发station流量,AC作为AP以及station的DHCP Server。
- 无线侧业务配置按照表2-8规划完成:
配置过程:
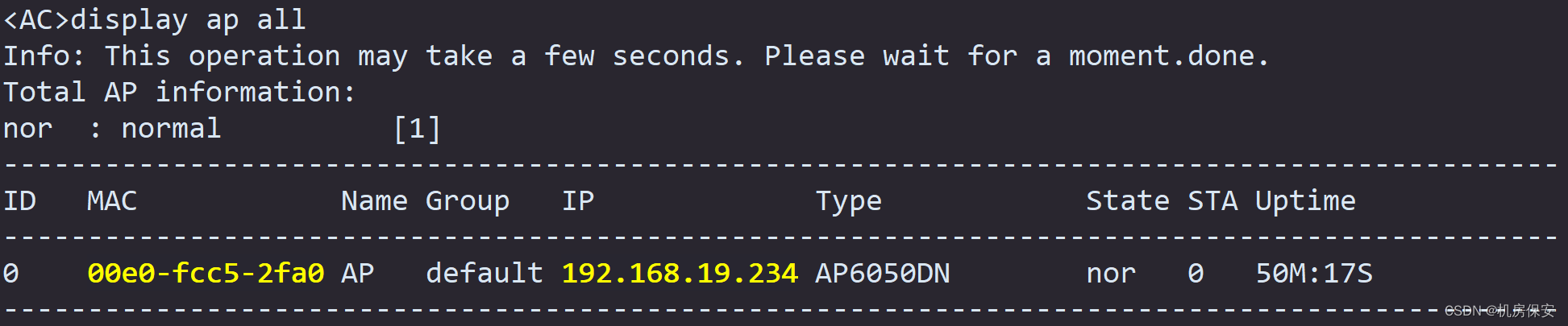
任务10:WLAN
DHCP
#AC1
[AC]interface Vlanif 19
[AC-Vlanif19]ip address 192.168.19.254 24
[AC]dhcp enable
[AC]ip pool For_AP
[AC-ip-pool-For_AP]network 192.168.19.0 mask 255.255.255.0
[AC-ip-pool-For_AP]gateway-list 192.168.19.254
[AC]ip pool STA
[AC-ip-pool-STA]network 192.168.2.0 mask 255.255.255.0
[AC-ip-pool-STA]gateway-list 192.168.2.254
[AC]interface Vlanif 19
[AC-Vlanif19]dhcp select global
[AC]interface Vlanif 20
[AC-Vlanif20]dhcp select global
[AC]interface Vlanif 19
[AC-Vlanif19]ip address 192.168.19.254 24
WLAN业务配置
[AC]capwap source interface Vlanif 19
[AC]wlan
[AC-wlan-view]ap auth-mode mac-auth
[AC-wlan-view]ap-id 0 ap-mac 00e0-fc52-0650
[AC-wlan-ap-0]ap-name AP
[AC-wlan-ap-0]ap-group default
[AC-wlan-view]ssid-profile name s1
[AC-wlan-ssid-prof-s1]ssid ICT
[AC-wlan-view]security-profile name s1
[AC-wlan-sec-prof-s1]security wpa-wpa2 psk pass-phrase Huawei@123 aes
[AC-wlan-view]vap-profile name p1
[AC-wlan-vap-prof-p1]forward-mode tunnel
[AC-wlan-vap-prof-p1]service-vlan vlan-id 20
[AC-wlan-vap-prof-p1]ssid-profile s1
[AC-wlan-vap-prof-p1]security-profile s1
[AC-wlan-view]ap-group name default
[AC-wlan-ap-group-default]regulatory-domain-profile default
[AC-wlan-ap-group-default]vap-profile p1 wlan 1 radio all 验证: