1.open-soure
这个直接给了源代码
#include <stdio.h>
#include <string.h>
int main(int argc, char *argv[]) {
if (argc != 4) {
printf("what?\n");
exit(1);
}
unsigned int first = atoi(argv[1]);
if (first != 0xcafe) {
printf("you are wrong, sorry.\n");
exit(2);
}
unsigned int second = atoi(argv[2]);
if (second % 5 == 3 || second % 17 != 8) {
printf("ha, you won't get it!\n");
exit(3);
}
if (strcmp("h4cky0u", argv[3])) {
printf("so close, dude!\n");
exit(4);
}
printf("Brr wrrr grr\n");
unsigned int hash = first * 31337 + (second % 17) * 11 + strlen(argv[3]) - 1615810207;
printf("Get your key: ");
printf("%x\n", hash);
return 0;
}
unsigned int hash = first * 31337 + (second % 17) * 11 + strlen(argv[3]) - 1615810207;
根据这行代码,得出要求出first、second、arvg[3]
if (first != 0xcafe) {
printf("you are wrong, sorry.\n");
exit(2);
}
上述代码得出,first=0xcafe,是个16进制的数
转化十进制=51966
if (second % 5 == 3 || second % 17 != 8) {
printf("ha, you won't get it!\n");
exit(3);
}
上述代码得出second=25
if (strcmp("h4cky0u", argv[3])) {
printf("so close, dude!\n");
exit(4);
}
上述代码得出argv[3]与h4cky0u相等,说明argv[3]=h4cky0u
#include <stdio.h>
#include <string.h>
int main(){
unsigned int hash = 51966* 31337 + (25% 17) * 11 + strlen("h4cky0u") - 1615810207;
printf("Get your key: ");
printf("%x\n", hash);
return 0;
}
写个代码运行一下得出
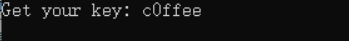
flag就是{c0ffee}
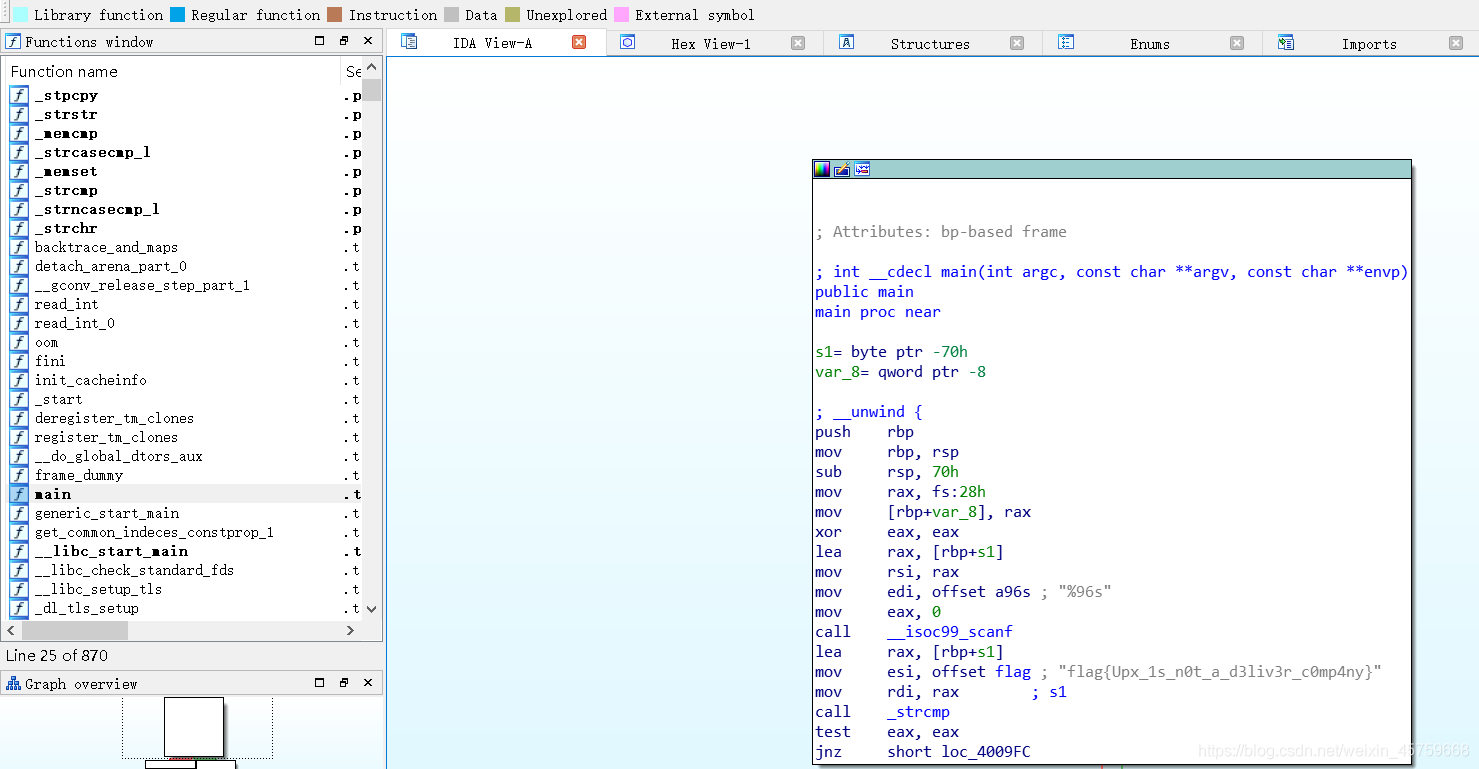
2.simple-unpack
这个是要脱壳,首先判断什么壳
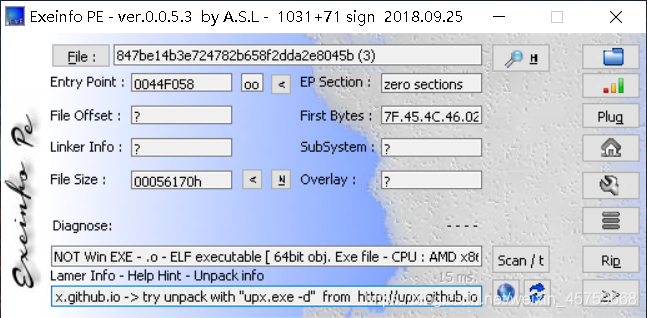
发现是upx壳
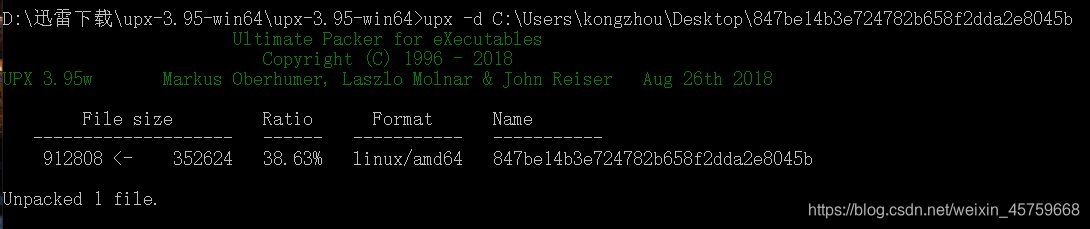
用upx脱壳成功,放进ida中查看,找的main函数,直接就出来了
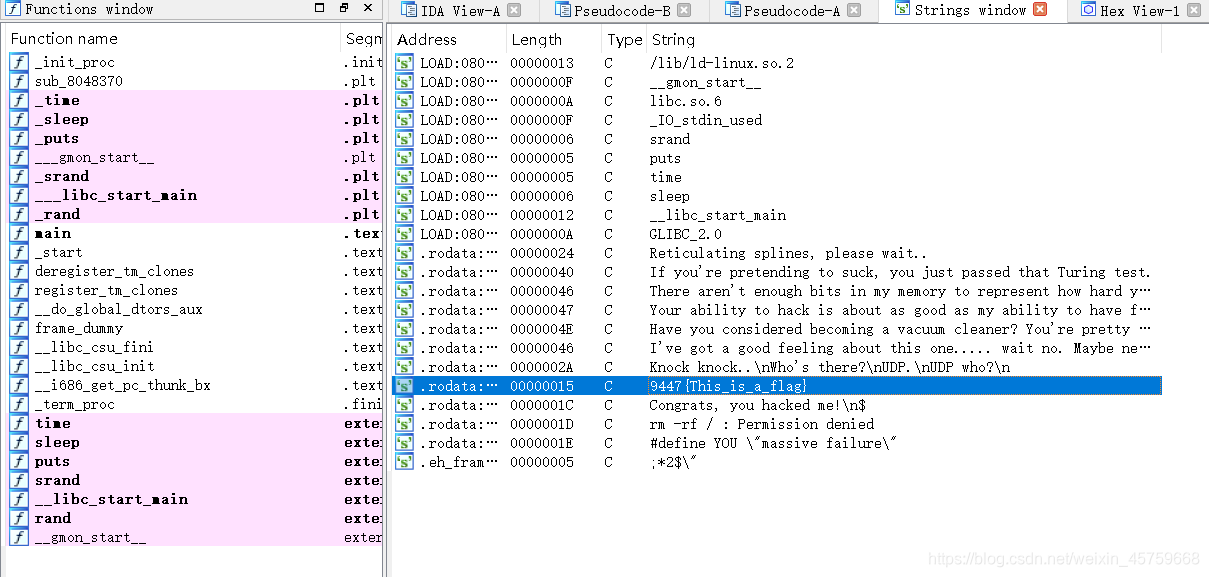
3.insanity
这个就是下载附件放入32位ida中
F5查看字符串