Reverse
jocker
前面是一个假的flag,直接跳过omg函数
下面这段代码把0x401500-0x4015ba都亦或了0x41(也就是说在运行时修改了text段的encrypt函数),从而得到真正的encrypt函数
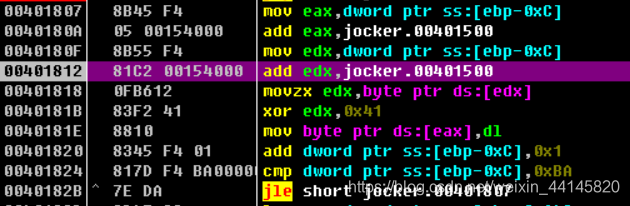
这段代码会把输入与字符串hahahaha_do_you_find_me?亦或,如果等于0x403040的那一串值,就通过
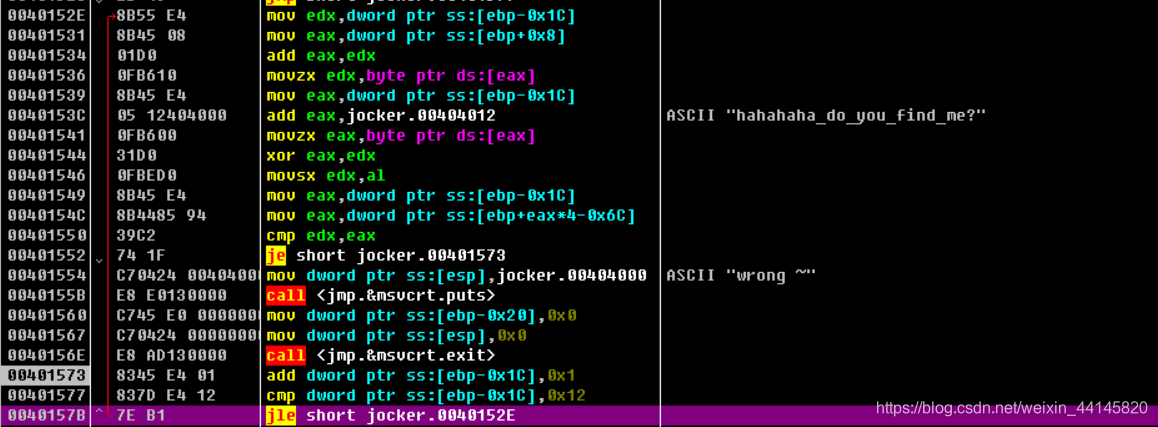
这串是0x403040:[0x0e, 0x0d, 9, 6, 0x13, 5, 0x58, 0x56, 0x3e, 6, 0x0c, 0x3c, 0x1f, 0x57, 0x14, 0x6b, 0x57, 0x59, 0x0d]
长度为19
我们求出前19个为flag{d07abccf8a410c
然后我们进入final函数,发现压进去5个byte,猜测为剩下的flag
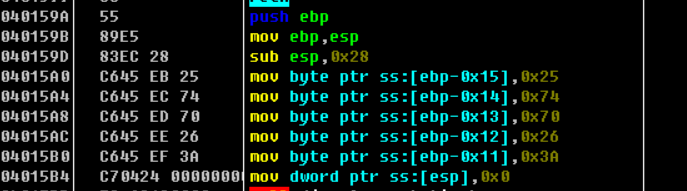
由于剩下的flag中最后一个一定是},我们用}(0x7d)和0x3a亦或,得到0x47
然后用0x47和剩下的4个亦或即可得到flag
最终Exp:
'''fake flag
s = [0x66, 0x6b, 0x63, 0x64, 0x7f, 0x61, 0x67, 0x64, 0x3b, 0x56, 0x6b, 0x61, 0x7b, 0x26, 0x3b, 0x50, 0x63, 0x5f, 0x4d, 0x5a, 0x71, 0x0c, 0x37, 0x66]
flag = ''
for i in range(24):
if i % 2 == 1:
s[i] += i
else:
s[i] ^= i
flag += chr(s[i])
print flag
'''
part1 = [0x0e, 0x0d, 9, 6, 0x13, 5, 0x58, 0x56, 0x3e, 6, 0x0c, 0x3c, 0x1f, 0x57, 0x14, 0x6b, 0x57, 0x59, 0x0d, 0x25, 0x74, 0x70, 0x26, 0x3a]
part1_s = 'hahahaha_do_you_find_me?'
flag = ''
for i in range(19):
flag += chr(part1[i]^ord(part1_s[i]))
guess = ord('}') ^ 0x3a
for i in range(19, 24):
flag += chr(part1[i]^guess)
print flag
signal
这题有点类似虚拟机吧,反正就是操作码+操作数,F5还是很清晰的
人肉翻译结果如下:
0A 00 00 00 read
04 00 00 00 v5 = 0x10^input[0]
10 00 00 00 pass
08 00 00 00 input[0] = v5
03 00 00 00 v5 = input[0] - 5
05 00 00 00 pass
01 00 00 00 check[0]=v5
04 00 00 00 v5 = 0x20^input[1]
20 00 00 00 pass
08 00 00 00 input[1]=v5
05 00 00 00 v5 = 3 * input[1]
03 00 00 00 pass
01 00 00 00 check[1]=v5
03 00 00 00 v5 = input[2] - 2
02 00 00 00 pass
08 00 00 00 input[2] = v5
0B 00 00 00 v5 = input[2] - 1
01 00 00 00 check[2] = v5
0C 00 00 00 v5 = input[3] + 1
08 00 00 00 input[3] = v5
04 00 00 00 v5 = 4 ^ input[3];
04 00 00 00
01 00 00 00 check[3] = v5
05 00 00 00 v5 = 3 * input[4]
03 00 00 00
08 00 00 00 input[4] = v5
03 00 00 00 v5 = input[4] - 0x21
21 00 00 00
01 00 00 00 check[4] = v5
0B 00 00 00 v5 = input[5] - 1
08 00 00 00 input[5] = v5
0B 00 00 00 v5 = input[5] - 1
01 00 00 00 check[5] = v5
04 00 00 00 v5 = 9 ^input[6]
09 00 00 00
08 00 00 00 input[6] = v5
03 00 00 00 v5 = input[6] - 0x20
20 00 00 00
01 00 00 00 check[6] = input[6]
02 00 00 00 v5 = 0x51 + input[7]
51 00 00 00
08 00 00 00 input[7] = v5
04 00 00 00 input[7] ^= 0x24
24 00 00 00
01 00 00 00 check[7] = input[7]
0C 00 00 00 v5 = input[8] + 1
08 00 00 00
0B 00 00 00
01 00 00 00 same
05 00 00 00 v5 = input[9] * 2
02 00 00 00
08 00 00 00
02 00 00 00 input[9] + 0x25
25 00 00 00
01 00 00 00
02 00 00 00 input[10] + 0x36
36 00 00 00
08 00 00 00
04 00 00 00 input[10] ^ 0x41
41 00 00 00
01 00 00 00
02 00 00 00 v5 = input[11] + 0x20
20 00 00 00
08 00 00 00
05 00 00 00 input[11] * 1
01 00 00 00
01 00 00 00
05 00 00 00 v5 = input[12] * 3
03 00 00 00
08 00 00 00
02 00 00 00 input[12] + 0x25
25 00 00 00
01 00 00 00
04 00 00 00 v5 = input[13] ^ 9
09 00 00 00
08 00 00 00
03 00 00 00 input[13] - 0x20
20 00 00 00
01 00 00 00
02 00 00 00 v5 = input[14] + 0x41
41 00 00 00
08 00 00 00
0C 00 00 00 input[14] + 1
01 00 00 00
操作完之后,操作码7就是check了,根据check的值和上面翻译的操作来逆向,exp如下:
res = [0x22,0x3f,0x34,0x32,0x72,0x33,0x18,0xFFFFFFA7,0x31,0xFFFFFFF1,0x28,0xFFFFFF84,0xFFFFFFC1,0x1e,0x7a]
flag = 'flag{'
flag += chr((res[0]+5)^0x10)
flag += chr((res[1]/3)^0x20)
flag += chr(res[2]+3)
flag += chr((res[3]^4)-1)
flag += chr((res[4]+0x21)/3)
flag += chr(res[5]+2)
flag += chr((res[6]+0x20)^9)
flag += chr(((res[7]&0xff)^0x24)-0x51)
flag += chr((res[8]))
flag += chr(((res[9]&0xff)-0x25)/2)
flag += chr((res[10]^0x41)-0x36)
flag += chr(((res[11]&0xff)-0x20))
flag += chr(((res[12]&0xff)-0x25)/3)
flag += chr((res[13]+0x20)^9)
flag += chr((res[14]-0x42))
flag += '}'
print flag
至于提取操作码和操作数,这里给一个IDA python脚本供大家参考
addr = 0x403040
offset = 0x403208-addr
ans = []
for i in range(offset/4):
print(hex(get_wide_dword(addr+i*4)))
bang
使用APK-Scan查壳,发现为梆梆加固
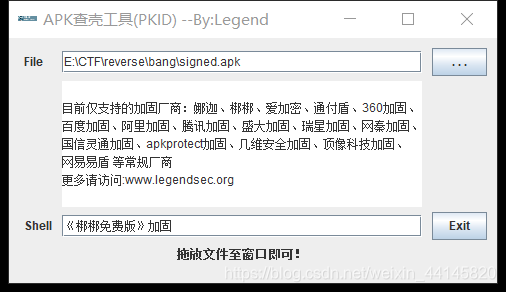
战队的大佬介绍了frida-dexdump的一个脱壳工具,非常方便使用,接下来我们就使用这个工具进行脱壳
首先我们打开模拟器(我这里用的是雷电)
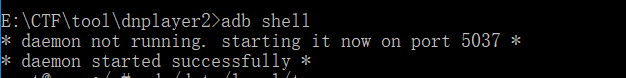
adb shell连接上去
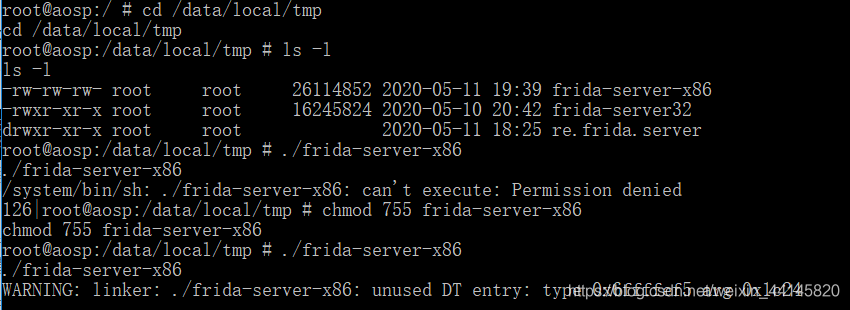
使用adb push 把frida-server文件放到/data/local/tmp目录下,server下载地址
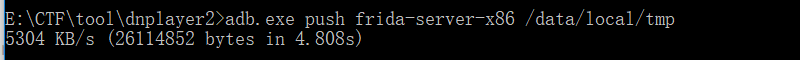
这里有个值得注意的地方,server一定要和你的模拟器或者手机架构一致,电脑上的模拟器(雷电什么的)一般是x86架构,而手机一般是arm的
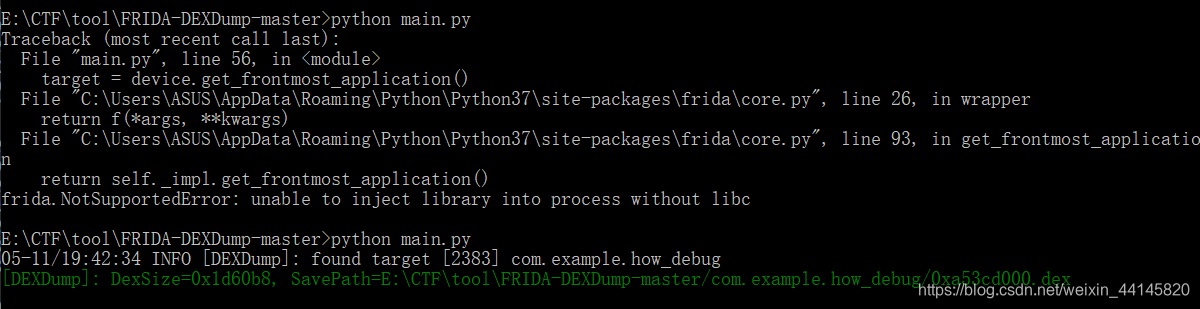
如果server不对可能会出现:
frida.NotSupportedError: unable to inject library into process without libc
chmod 755,然后启动server
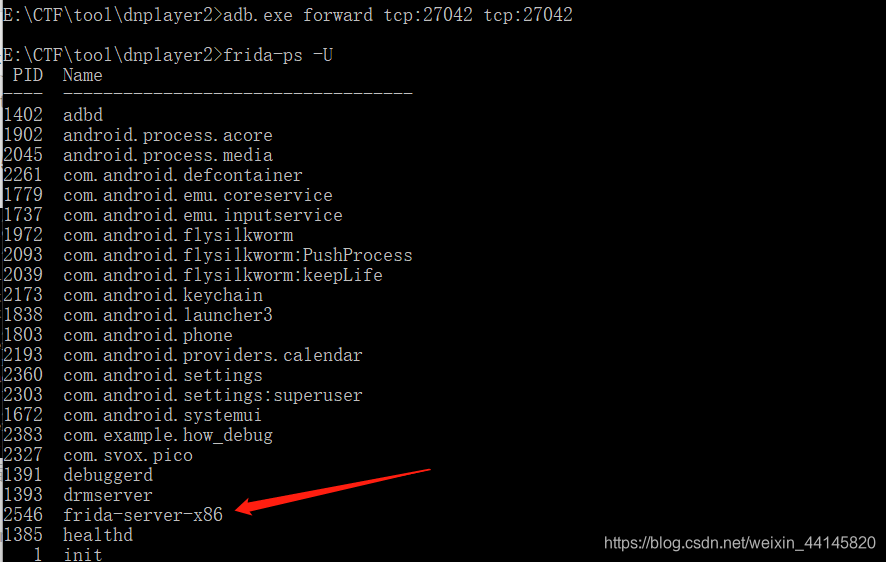
adb forwad 设置转发,然后frida-ps查看启动的进程
frida安装步骤
pip3 install frida
pip3 install frida-tools
用adb install signed.apk安装,运行app
然后使用工具把真正的dex文件导出,地址:https://github.com/hluwa/FRIDA-DEXDump
然后就是dex2jar转为jar文件

最后使用jd-gui打开,发现flag
