0 环境准备
1、导入依赖
<parent>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-parent</artifactId>
<version>2.2.4.RELEASE</version>
<relativePath/> <!-- lookup parent from repository -->
</parent>
<dependencies>
<dependency>
<groupId>org.mybatis.spring.boot</groupId>
<artifactId>mybatis-spring-boot-starter</artifactId>
<version>1.1.1</version>
</dependency>
<!-- mysql 依赖 -->
<dependency>
<groupId>mysql</groupId>
<artifactId>mysql-connector-java</artifactId>
</dependency>
<!-- SpringBoot 对lombok 支持 -->
<dependency>
<groupId>org.projectlombok</groupId>
<artifactId>lombok</artifactId>
</dependency>
<!-- SpringBoot web 核心组件 -->
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-web</artifactId>
</dependency>
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-tomcat</artifactId>
</dependency>
<!-- SpringBoot 外部tomcat支持 -->
<dependency>
<groupId>org.apache.tomcat.embed</groupId>
<artifactId>tomcat-embed-jasper</artifactId>
</dependency>
<!-- springboot-log4j -->
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-log4j</artifactId>
<version>1.3.8.RELEASE</version>
</dependency>
<!-- springboot-aop 技术 -->
<dependency>
<groupId>org.springframework.boot</groupId>
<artifactId>spring-boot-starter-aop</artifactId>
</dependency>
<!-- https://mvnrepository.com/artifact/commons-lang/commons-lang -->
<dependency>
<groupId>commons-lang</groupId>
<artifactId>commons-lang</artifactId>
<version>2.6</version>
</dependency>
</dependencies>
2、配置文件
spring:
mvc:
view:
prefix: /WEB-INF/jsp/
suffix: .jsp
datasource:
url: jdbc:mysql://120.78.134.111:3306/test
driver-class-name: com.mysql.jdbc.Driver
username: root
password: 123456
3、启动项
package com.snow;
import org.mybatis.spring.annotation.MapperScan;
import org.springframework.boot.SpringApplication;
import org.springframework.boot.autoconfigure.SpringBootApplication;
import org.springframework.boot.web.servlet.ServletComponentScan;
@MapperScan(basePackages = { "com.snow.mapper" })
@SpringBootApplication
@ServletComponentScan
public class App {
public static void main(String[] args) {
SpringApplication.run(App.class, args);
}
}
4、控制层
package com.snow.controller;
import javax.servlet.http.HttpServletRequest;
import org.springframework.stereotype.Controller;
import org.springframework.web.bind.annotation.RequestMapping;
@Controller
public class IndexController {
@RequestMapping("/index")
public String index() {
return "index";
}
// 接受頁面 參數
@RequestMapping("/postIndex")
public String postIndex(HttpServletRequest request) {
request.setAttribute("name", request.getParameter("name"));
return "forward";
}
}
5、
index.jsp
<%@ page language="java" contentType="text/html; charset=UTF-8"
pageEncoding="UTF-8"%>
<!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd">
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8">
<title>Insert title here</title>
</head>
<body>
<img src="http://127.0.0.1:8080/imgs/1.png">
<form action="postIndex" method="post">
输入内容: <input type="text" name="name"> <br> <input
type="submit">
</form>
</body>
</html>
6、
forward.jsp
<%@ page language="java" contentType="text/html; charset=UTF-8"
pageEncoding="UTF-8"%>
<!DOCTYPE html PUBLIC "-//W3C//DTD HTML 4.01 Transitional//EN" "http://www.w3.org/TR/html4/loose.dtd">
<html>
<head>
<meta http-equiv="Content-Type" content="text/html; charset=UTF-8">
<title>Insert title here</title>
</head>
<body>${name}
</body>
</html>
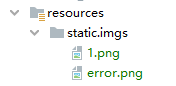
7、静态资源
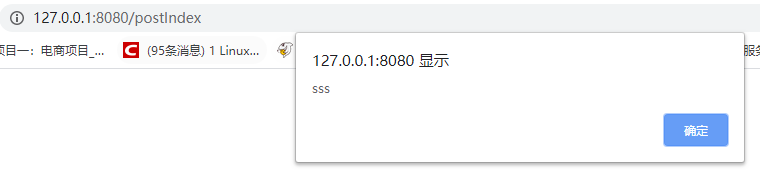
测试
浏览器访问:http://127.0.0.1:8080/index,在输入框中输入:
<script>alert('sss')</script>
点击提交:
输入:
<script>window.location.href='http://www.baidu.com';</script>
点击提交,跳转到百度首页。
1 什么是 XSS 攻击手段
XSS 攻击使用 Javascript 脚本注入进行攻击
例如:在提交表单后,展示到另一个页面,可能会受到 XSS 脚本注入,读取本地 cookie 远程发送给服务器端。
XSS攻击原理
使用 JS 脚本语言,因为浏览器默认支持脚本语言执行,如果在表单提交时,提交一些脚本参数,可能浏览器直接进行执行。
XSS攻击最常见的漏洞
- 论坛的评论:在评论里面填写 JS 脚本,如果不做 防御
XSS攻击,那么页面加载就会执行 JS 脚本
2 如何防御 XSS 攻击
将脚本特殊字符,转换成
html源代码进行展示。
例如:将一些特殊的字符,如 <、> 等进行转换,例如 < 写成 <
字符编码:http://www.mytju.com/classcode/tools/encode_gb2312.asp
测试:

显示:
2.1 程序中使用
步骤:编写过滤器拦截所有 getParameter 参数,重写 httpservletwrapp 方法,将参数特殊字符转换成 html 源代码保存。
1、定义一个过滤器
package com.snow.filter;
import com.snow.request.XssHttpServletRequestWrapper;
import javax.servlet.*;
import javax.servlet.annotation.WebFilter;
import javax.servlet.http.HttpServletRequest;
import java.io.IOException;
@WebFilter(filterName = "xssFilter", urlPatterns = "/*")
public class XssFilter implements Filter {
public void init(FilterConfig filterConfig) throws ServletException {
}
public void doFilter(ServletRequest request, ServletResponse response, FilterChain chain)
throws IOException, ServletException {
// 程序防止XSS攻击原理
// 1. 使用过滤器拦截所有参数
HttpServletRequest req = (HttpServletRequest) request;
// 2.重新getParameter方法
XssHttpServletRequestWrapper xssHttpServletRequestWrapper = new XssHttpServletRequestWrapper(req);
// 放行程序,继续往下执行
chain.doFilter(xssHttpServletRequestWrapper, response);
}
public void destroy() {
}
}
2、重写请求参数方法
package com.snow.request;
import org.apache.commons.lang.StringEscapeUtils;
import org.apache.commons.lang.StringUtils;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletRequestWrapper;
public class XssHttpServletRequestWrapper extends HttpServletRequestWrapper {
private HttpServletRequest request;
/**
* @param request
*/
public XssHttpServletRequestWrapper(HttpServletRequest request) {
super(request);
this.request = request;
}
@Override
public String getParameter(String name) {
// 获取之前的参数
String olValue = super.getParameter(name);
System.out.println("原来参数:" + olValue);
if (!StringUtils.isEmpty(olValue)) {
// 将特殊字符转换成html展示 // 3.使用(StringEscapeUtils.escapeHtml(name)转换特殊参数
olValue = StringEscapeUtils.escapeHtml(olValue);
System.out.println("转换后" + olValue);
}
System.out.println();
return olValue;
}
}
3、启动项加上注解
@ServletComponentScan
@ServletComponentScan
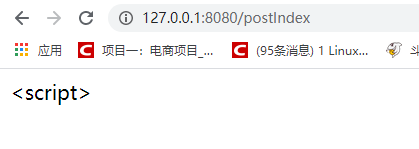
测试:
输入框输入:
<script>window.location.href='http://www.baidu.com';</script>

点击提交按钮:

控制台打印:
原来参数:<script>window.location.href='http://www.baidu.com';</script>
转换后<script>window.location.href='http://www.baidu.com';</script>
