Packet Tracer - Configure AAA Authentication on Cisco Routers
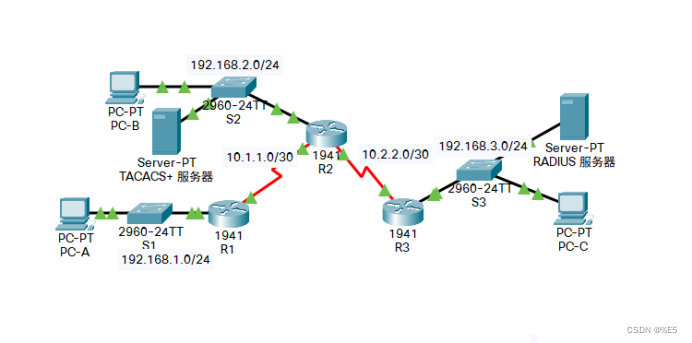
Topology
Address Allocation Table
| equipment |
interface |
IP address |
subnet mask |
default gateway |
switch port |
| R1 |
G0/1 |
192.168.1.1 |
255.255.255.0 |
not applicable |
S1 F0/1 |
| S0/0/0 (DCE) |
10.1.1.2 |
255.255.255.252 |
not applicable |
not applicable |
|
| R2 |
G0/0 |
192.168.2.1 |
255.255.255.0 |
not applicable |
S2 F0/2 |
| S0/0/0 |
10.1.1.1 |
255.255.255.252 |
not applicable |
not applicable |
|
| S0/0/1 (DCE) |
10.2.2.1 |
255.255.255.252 |
not applicable |
not applicable |
|
| R3 |
G0/1 |
192.168.3.1 |
255.255.255.0 |
not applicable |
S3 F0/5 |
| S0/0/1 |
10.2.2.2 |
255.255.255.252 |
not applicable |
not applicable |
|
| TACACS+ server |
NIC |
192.168.2.2 |
255.255.255.0 |
192.168.2.1 |
S2 F0/6 |
| RADIUS server |
NIC |
192.168.3.2 |
255.255.255.0 |
192.168.3.1 |
S3 F0/1 |
| PC-A |
NIC |
192.168.1.3 |
255.255.255.0 |
192.168.1.1 |
S1 F0/2 |
| PC-B |
NIC |
192.168.2.3 |
255.255.255.0 |
192.168.2.1 |
S2 F0/1 |
| PC-C |
NIC |
192.168.3.3 |
255.255.255.0 |
192.168.3.1 |
S3 F0/18 |
Target
• Configure local user accounts on R1 and configure authentication on the console and vty lines using local AAA.
• Verify the local AAA certificate from the R1 console and PC-A client.
• Configure server-based AAA authentication using TACACS+.
• Verify server-based AAA authentication from the PC-B client.
• Configure server-based AAA authentication using RADIUS.
• Verify server-based AAA authentication from a PC-C client.
background / scene
Routers R1, R2, and R3 are shown in the network topology. Currently, all administrative security is based on knowledge of the enabled encryption password. Your task is to configure and test local and server-based AAA solutions.
You will create a local user account and configure local AAA on router R1 to test console and vty logins.
oUser account: Admin1 , password: admin1pa55
You will then configure router R2 to support server-based authentication using the TACACS+ protocol. The TACACS+ server has been preconfigured with the following information:
oClient : R2 , use keyword tacacspa55
oUser account: Admin2 , password: admin2pa55
Finally, you will configure router R3 to support server-based authentication using the RADIUS protocol. The RADIUS server is preconfigured with the following information:
oClient : R3 , use the keyword radiuspa55
oUser account: Admin3 , password: admin3pa55
The router has been preconfigured with the following information:
oEnable encryption password: ciscoenpa55
oOSPF routing protocol using MD5 authentication, the password is: MD5pa55
Note : The console and vty lines are not preconfigured.
Note : IOS version 15.3 uses SCRYPT as the secure cryptographic hash algorithm; however, the currently supported IOS version in Packet Tracer uses MD5. Always use the safest option available on your device.
Part 1: Configure local AAA authentication for console access on R1
Step 1: Test the connection.
• Ping PC-B from PC -A .
• Ping PC-C from PC -A .
• Ping PC-C from PC -B .
Step 2: Configure the local username on R1.
Configure the user name Admin1 and use the encrypted password admin1pa55 .
R1(config)#username Admin1 secret admin1pa55
Step 3: Configure local AAA authentication for console access on R1.
Enable AAA on R1 and configure AAA authentication for console logins to use the local database.
R1(config)#aaa new-model
R1(config)#aaa authentication login default local
Step 4: Configure the line console to use the defined AAA authentication method.
Enable AAA on R1 and configure AAA authentication for console login to use the default method list.
R1(config)#line console 0
R1(config-line)#login authentication default
Step 5: Verify the AAA authentication method.
Authenticate user EXEC login using local database.
R1(config-line)#end
R1#
%SYS-5-CONFIG_I: Configured from console by console
R1#exit
R1 con0 is now available
Press RETURN to get started.
************ AUTHORIZED ACCESS ONLY *************
UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED.
************ AUTHORIZED ACCESS ONLY *************
UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED.
User Access Verification
Username: Admin1
Password: admin1pa55
R1>
Part 2: Configure local AAA authentication for vty lines on R1
Step 1: Configure a domain name and encryption key for SSH.
- Use ccnasecurity.com as the domain name on R1.
R1(config)#ip domain-name ccnasecurity.com
- Create an RSA encryption key using 1024 bits.
R1(config)#crypto key generate rsa
The name for the keys will be: R1.ccnasecurity.com
Choose the size of the key modulus in the range of 360 to 2048 for your
General Purpose Keys. Choosing a key modulus greater than 512 may take
a few minutes.
How many bits in the modulus [512]: 1024
% Generating 1024 bit RSA keys, keys will be non-exportable...[OK]
Step 2: Configure the named-list AAA authentication method for the vty line on R1.
Configure a named list called SSH-LOGIN to log in using local AAA authentication.
R1(config)#aaa authentication login SSH-LOGIN local
Step 3: Configure the vty line to use the defined AAA authentication method.
Configure the vty line to use the defined AAA authentication method and allow only SSH for remote access.
R1(config)#line vty 0 4
R1(config-line)#login authentication SSH-LOGIN
R1(config-line)#transport input ssh
R1(config-line)#end
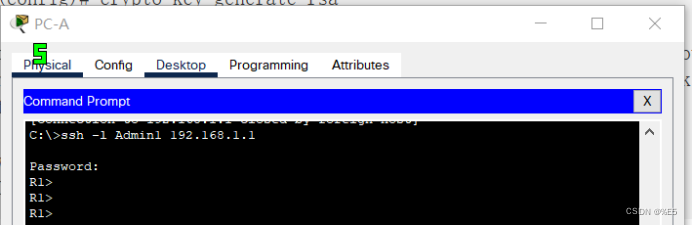
Step 4: Verify the AAA authentication method.
Verify R1 's SSH configuration from PC-A 's command prompt .
C:\>ssh -l Admin1 192.168.1.1
Password: admin1pa55
R1>
Part 3: Configuring Server-Based AAA Authentication Using TACACS+ on R2
Step 1: Configure a backup local database entry called Admin.
For backup purposes, configure a local username of Admin2 with an encrypted password of admin2pa55 .
R2(config)#username Admin2 secret admin2pa55
Step 2: Verify the TACACS+ server configuration.
Click on "TACACS+ Server". Click AAA on the Services tab . Note that the network configuration entries for R2 are shown, as well as the user settings entries for Admin2 .
Step 3: Configure the specific details of the TACACS+ server on R2.
Configure the AAA TACACS server IP address and key on R2 .
Note : The commands tacacs-server host and tacacs-server key are deprecated . Currently, Packet Tracer does not support the new command tacacs server .
R2(config)#tacacs-server host 192.168.2.2
R2(config)#tacacs-server key tacacspa55
Step 4: Configure AAA login authentication for console access on R2.
Enable AAA on R2 and configure all logins to use the AAA TACACS+ server for authentication. If not available, a local database is used.
R2(config)#username Admin2 secret admin2pa55
R2(config)#aaa authentication login default group tacacs+ local
Step 5: Configure the line console to use the defined AAA authentication method.
Configure AAA authentication for console login to use the default AAA authentication method.
R2(config)#line console 0
R2(config-line)#login authentication default
Step 6: Verify the AAA authentication method.
Authenticate user EXEC logins using an AAA TACACS+ server.
R2(config-line)#end
R2#
%SYS-5-CONFIG_I: Configured from console by console
R2#exit
R2 con0 is now available
Press RETURN to get started.
************ AUTHORIZED ACCESS ONLY *************
UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED.
User Access Verification
Username: Admin2
Password: admin2pa55
R2>
Part 4: Configuring Server-Based AAA Authentication Using TACACS+ on R3
Step 1: Configure a backup local database entry called Admin.
For backup purposes, configure a local username of Admin3 with an encrypted password of admin3pa55 .
R3(config)#username Admin3 secret admin3pa55
Step 2: Verify the configuration of the RADIUS server.
Click on RADIUS Server. Click AAA on the Services tab . Note that the network configuration entry for R3 is shown, as well as the user settings entry for Admin3 .
Step 3: Configure the specific details of the RADIUS server on R3.
Configure the AAA RADIUS server IP address and key on R3 .
Note : The commands radius-server host and radius-server key are deprecated . Currently, Packet Tracer does not support the new command radius server .
R3(config)#radius-server host 192.168.3.2
R3(config)#radius-server key radiuspa55
Step 4: Configure AAA login authentication for console access on R3.
Enable AAA on R3 and configure all logins to use the AAA RADIUS server for authentication. If not available, a local database is used.
R3(config)#aaa new-model
R3(config)#aaa authentication login default group radius local
Step 5: Configure the line console to use the defined AAA authentication method.
Configure AAA authentication for console login to use the default AAA authentication method.
R3(config)#line console 0
R3(config-line)#login authentication default
Step 6: Verify the AAA authentication method.
Use an AAA RADIUS server to authenticate user EXEC login.
R3(config-line)#end
R3#
%SYS-5-CONFIG_I: Configured from console by console
R3#exit
R3 con0 is now available
Press RETURN to get started.
************ AUTHORIZED ACCESS ONLY *************
UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED.
User Access Verification
Username: Admin3
Password: admin3pa55
R3>
Step 7: Check the result.
The percentage of completion should be 100%. Click Check Results to review feedback and verify required components are completed.
Experiment specific steps:
R1:
R1>en
Password: ciscoenpa55
R1#conf
Configuring from terminal, memory, or network [terminal]?
Enter configuration commands, one per line. End with CNTL/Z.
R1(config)#username Admin1 secret admin1pa55
R1(config)#aaa new-model
R1(config)#aaa authentication login default local
R1(config)#line console 0
R1(config-line)#login authentication default
R1(config-line)#end
R1#
%SYS-5-CONFIG_I: Configured from console by console
R1#exit
R1 con0 is now available
Press RETURN to get started.
*********** AUTHORIZED ACCESS ONLY *************
UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED.
************ AUTHORIZED ACCESS ONLY *************
UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED.
User Access Verification
Username: Admin1
Password: admin1pa55
R1>en
Password: ciscoenpa55
R1#
R1#conf
Configuring from terminal, memory, or network [terminal]?
Enter configuration commands, one per line. End with CNTL/Z.
R1(config)#ip domain-name ccnasecurity.com
R1(config)#crypto key generate rsa
The name for the keys will be: R1.ccnasecurity.com
Choose the size of the key modulus in the range of 360 to 2048 for your
General Purpose Keys. Choosing a key modulus greater than 512 may take
a few minutes.
How many bits in the modulus [512]: 1024
R1(config)#aaa authentication login SSH-LOGIN local
R1(config)#line vty 0 4
R1(config-line)#login authentication SSH-LOGIN
R1(config-line)#transport input ssh
R1(config-line)#end
R1#R2 configuration:
R2>en
Password: ciscoenpa55
R2#
R2#conf
Configuring from terminal, memory, or network [terminal]?
Enter configuration commands, one per line. End with CNTL/Z.
R2(config)#username Admin2 secret admin2pa55
R2(config)#tacacs-server host 192.168.2.2
R2(config)#tacacs-server key tacacspa55
R2(config)#username Admin2 secret admin2pa55
R2(config)#aaa authentication login default group tacacs+ local
R2(config)#line console 0
R2(config-line)#login authentication default
R2(config-line)#end
R2#
%SYS-5-CONFIG_I: Configured from console by console
R2#exit
R2 con0 is now available
Press RETURN to get started.
************ AUTHORIZED ACCESS ONLY *************
UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED.
User Access Verification
Username: Admin2
Password: admin2pa55
R2>R3 configuration:
R3>en
Password: ciscoenpa55
R3#conf
Configuring from terminal, memory, or network [terminal]?
Enter configuration commands, one per line. End with CNTL/Z.
R3(config)#username Admin3 secret admin3pa55
R3(config)#radius-server host 192.168.3.2
R3(config)#radius-server key radiuspa55
R3(config)#aaa new-model
R3(config)#aaa authentication login default group radius local
R3(config)#line console 0
R3(config-line)#login authentication default
R3(config-line)#end
R3#
%SYS-5-CONFIG_I: Configured from console by console
R3#exit
R3 con0 is now available
ess RETURN to get started.
************ AUTHORIZED ACCESS ONLY *************
UNAUTHORIZED ACCESS TO THIS DEVICE IS PROHIBITED.
User Access Verification
Username: Admin3
Password: admin3pa55
R3>Experiment link: https://pan.baidu.com/s/1F8suBBA48T6LcZUvFyBBoA?pwd=3612
Extraction code: 3612
--Sharing from Baidu Netdisk super member V2