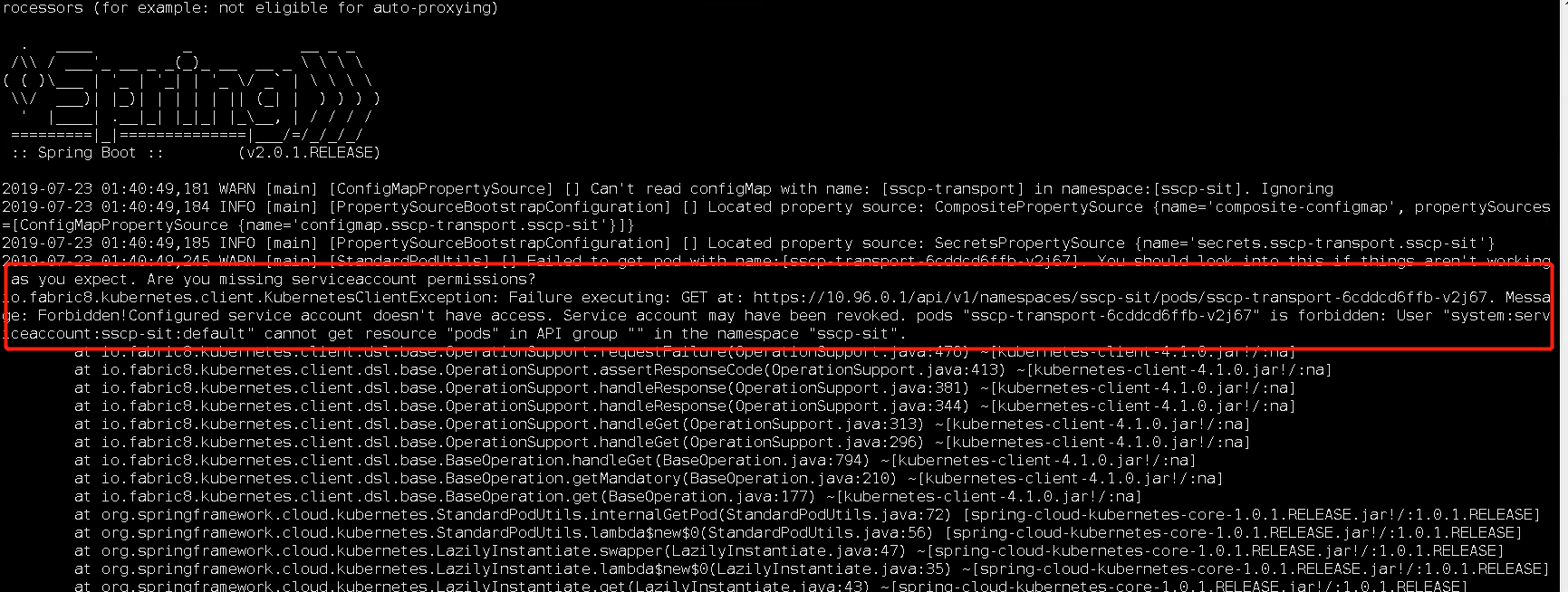
报错信息:
Message: Forbidden!Configured service account doesn't have access. Service account may have been revoked. User "system:serviceaccount:mycomp-services-process:default" cannot get resource “pods” in API group "" in the namespace "sscp-sit"
报错截图:
解决方法:
在第一个错误中,问题是默认命名空间中的serviceaccount default无法获取服务,因为它无法访问list / get服务。 因此,您需要做的是使用clusterrolebinding为该用户分配角色。
参考:https://www.e-learn.cn/content/wangluowenzhang/504150
遵循一组最低权限,您可以先创建一个可以访问列表服务的角色:
kind: Role apiVersion: rbac.authorization.k8s.io/v1 metadata: name: sscp-sit-minimal namespace: sscp-sit rules: - apiGroups: - "" - "extensions" resources: - nodes - services - endpoints - namespaces - ingresses - secrets - pods verbs: - get - list - watch - apiGroups: - "" - "extensions" resources: - configmaps - events - ingresses/status verbs: - get - list - watch - update - create - patch --- apiVersion: rbac.authorization.k8s.io/v1 kind: RoleBinding metadata: name: sscp-sit-minimal namespace: sscp-sit roleRef: apiGroup: rbac.authorization.k8s.io kind: Role name: sscp-sit-minimal subjects: - kind: ServiceAccount name: default namespace: sscp-sit