keepalived是一个类似于layer3, 4 & 5交换机制的软件,也就是我们平时说的第3层、第4层和第5层交换。Keepalived是自动完成,不需人工干涉。
使用keepalived主要两个功能:
1、keepalived实现主备机冗余功能
如果用nignx做负载均衡服务器,万一负载均衡服务器宕机了,也就挂了。
而keepalived通过VIP完美解决了这个问题,keepalived的主备机共用VIP,VIP对外提供访问,主机宕机了,备机会立即启动将VIP占用,接替主机的工作。
2、对后端的web服务器负载均衡(冗余)+健康监测
Keepalived的作用是检测服务器的状态,如果有一台web服务器宕机,或工作出现故障,Keepalived将检测到,并将有故障的服务器从系统中剔除,同时使用其他服务器代替该服务器的工作,当服务器工作正常后Keepalived自动将服务器加入到服务器群中,这些工作全部自动完成,不需要人工干涉,需要人工做的只是修复故障的服务器。
开始搭建
示例服务器
| 服务器 | IP | 端口 |
| VIP | 192.168.61.59 | |
| keepalived主机:NODE1 | 192.168.61.55 | |
| keepalived备机:NODE2 | 192.168.61.57 | |
| web服务器1:WEB1 | 192.168.61.56 | 10001 |
| web服务器2:WEB2 | 192.168.61.58 | 10001 |
1 安装keepalived(NODE1和NODE2)
最好先更新软件一下
yum update1.1 安装keepalived依赖 gcc和openssl-devel
yum -y install gcc openssl-devel1.2 安装keepalived
yum -y install keepalived2 修改keepalivd配置文件(NODE1和NODE2)
配置文件路径:/etc/keepalived/keepalived.conf。建议下载修改,修改完重新上传
NODE1配置文件如下
! Configuration File for keepalived
global_defs {
# notification_email {
# [email protected]
# [email protected]
# [email protected]
# }
# notification_email_from [email protected]
# smtp_server 192.168.200.1
# smtp_connect_timeout 30
router_id NODE1
# vrrp_skip_check_adv_addr
# vrrp_strict
vrrp_garp_interval 0
vrrp_gna_interval 0
}
vrrp_instance VI_1 {
state MASTER
interface ens192
virtual_router_id 101
priority 100
advert_int 1
authentication {
auth_type PASS
auth_pass 1111
}
virtual_ipaddress {
192.168.61.59
}
}
virtual_server 192.168.61.59 10001 {
delay_loop 3
lb_algo wrr
lb_kind DR
persistence_timeout 60
protocol TCP
real_server 192.168.61.56 10001 {
weight 2
HTTP_GET {
url {
path /cnic/
digest 63bad2e94270298fe051dc7ed342d71d
}
connect_timeout 2
nb_get_retry 3
delay_before_retry 2
}
}
real_server 192.168.61.58 10001 {
weight 1
HTTP_GET {
url {
path /cnic/
digest 63bad2e94270298fe051dc7ed342d71d
}
connect_timeout 2
nb_get_retry 3
delay_before_retry 2
}
}
}
NODE2配置文件如下
! Configuration File for keepalived
global_defs {
# notification_email {
# [email protected]
# [email protected]
# [email protected]
# }
# notification_email_from [email protected]
# smtp_server 192.168.200.1
# smtp_connect_timeout 30
router_id NODE2
# vrrp_skip_check_adv_addr
# vrrp_strict
vrrp_garp_interval 0
vrrp_gna_interval 0
}
vrrp_instance VI_1 {
state BACKUP
interface ens192
virtual_router_id 101
priority 10
advert_int 1
authentication {
auth_type PASS
auth_pass 1111
}
virtual_ipaddress {
192.168.61.59
}
}
virtual_server 192.168.61.59 10001 {
delay_loop 3
lb_algo wrr
lb_kind DR
persistence_timeout 60
protocol TCP
real_server 192.168.61.56 10001 {
weight 2
HTTP_GET {
url {
path /cnic/
digest 63bad2e94270298fe051dc7ed342d71d
}
connect_timeout 2
nb_get_retry 3
delay_before_retry 2
}
}
real_server 192.168.61.58 10001 {
weight 1
HTTP_GET {
url {
path /cnic/
digest 63bad2e94270298fe051dc7ed342d71d
}
connect_timeout 2
nb_get_retry 3
delay_before_retry 2
}
}
}
BCompare一下,主备机配置文件3处不同

配置文件中的digest(摘要)生成方法:
genhash语法:genhash -s [IP] -p [端口号] -u [url]
genhash是keepalived自带的,安装了keepalived就可以用了
本文以/cnic/为例
genhash -s 192.168.61.58 -p 10001 -u /cnic/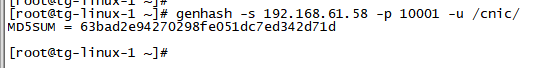
更多keepalived配置文件详解:
https://blog.csdn.net/lishuoboy/article/details/89919939
3 防火墙设置添加放行端口(NODE1、NODE2、WEB1、WEB2)
你可以简单粗暴点直接关闭防火墙,本文不推荐,略。
3.1 添加防火墙例外端口(centOS)
查看例外端口:firewall-cmd --list-all
添加10001端口:firewall-cmd --zone=public --add-port=10001/tcp --permanent
使生效(必须):firewall-cmd --reload添加完成后如下:

防火墙的命令参考https://blog.csdn.net/lishuoboy/article/details/88301273
4 防火墙设置放行回环ip(NODE1、NODE2、WEB1、WEB2)
firewall-cmd --direct --permanent --add-rule ipv4 filter INPUT 0 --in-interface ens192 --destination 224.0.0.18 --protocol vrrp -j ACCEPTens192是网卡,用ip a命令查看

224.0.0.18是keepalived的默认广播地址
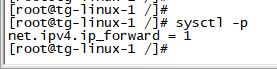
5 启用ip转发(NODE1、NODE2)
vim /etc/sysctl.conf加入 net.ipv4.ip_forward = 1

保存退出:按esc,然后输入:wq按回车
重载/etc/sysctl.conf使生效
sysctl -p6、将VIP添加的网络回环中(NODE1、NODE2、WEB1、WEB2)
编写一个将vip(192.168.61.59)添加到网络回环的脚本/bin/setvip.sh,内容如下
#!/bin/bash
#description: Config virtual IP address
VIP=192.168.61.59/32 #32是子网掩码,用32保证这一个网段只有一个ip,按需设置
case "$1" in
start)
ip addr add $VIP dev lo:1
echo "1" >/proc/sys/net/ipv4/conf/lo/arp_ignore
echo "2" >/proc/sys/net/ipv4/conf/lo/arp_announce
echo "1" >/proc/sys/net/ipv4/conf/all/arp_ignore
echo "2" >/proc/sys/net/ipv4/conf/all/arp_announce
sysctl -p >/dev/null 2>&1
echo "VIP has added"
;;
stop)
ip addr del $VIP dev lo:1
echo "0" >/proc/sys/net/ipv4/conf/lo/arp_ignore
echo "0" >/proc/sys/net/ipv4/conf/lo/arp_announce
echo "0" >/proc/sys/net/ipv4/conf/all/arp_ignore
echo "0" >/proc/sys/net/ipv4/conf/all/arp_announce
echo "VIP has deleted."
;;
*)
echo "Usage: $0 {start|stop}"
exit 1
esac
exit 0
添加执行权限
chmod +x /bin/setvip.sh添加VIP到网络回环
setvip.sh startstart之前(lo:网络回环loopback)↓
start之后↓(lo:网络回环loopback)
stop之后↓(lo:网络回环loopback)
7、调整SELinux安全策略
SELinux知识参考:https://blog.51cto.com/13570193/2093299
7.2 将SELinux策略改为警告
7.2.1 先临时改了
setenforce 0
ps:setenforce 0|1 分别代表permissive(放纵的)、enforcing(强制)
查看SELinux状态
getenforce![]()
7.2.2 设置SELinux永久为permissive(放纵的)
为防止服务器重启后SELinux模式恢复默认,设置SELINUX=permissive永久生效。
vim /etc/selinux/config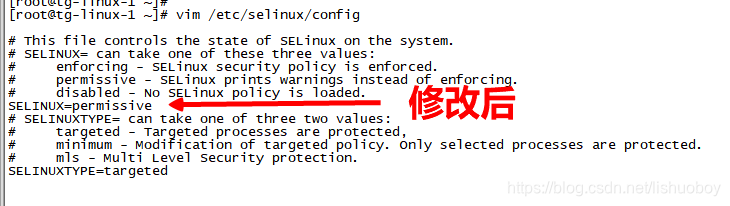
重启后验证一下
rebootgetenforce![]()