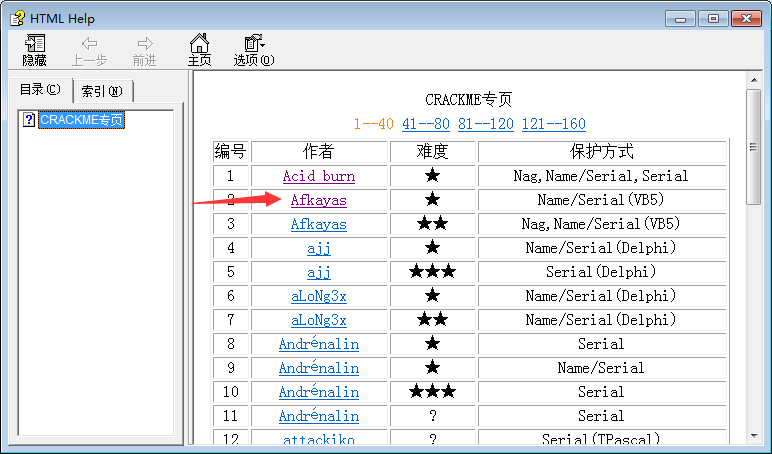
首先在 http://it0365.com/thread-29-1-1.html 下载实战样本,选择第2个程序
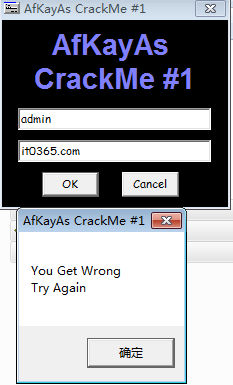
本次给大家讲4种方法,让你快速入门破解。
方法如下:
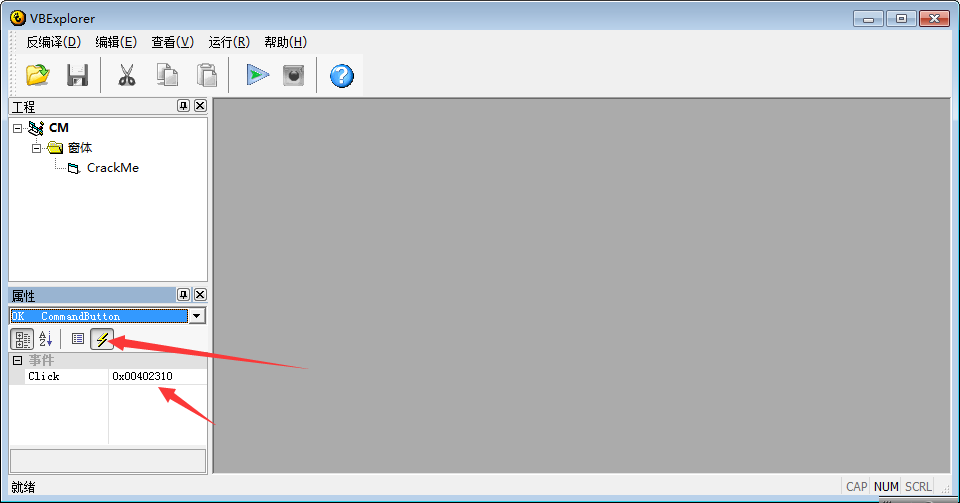
1、使用工具反编译出按钮事件位置
使用工具(VBExplorer资源编辑)加载要破解的程序,找到按钮事件位置:00402310
找到地址后,使用OD打开破解的程序,来到00402310位置下断点,F9运行程序即可来到关键位置
0040257C . 8945 94 mov dword ptr ss:[ebp-0x6C],eax
0040257F . 894D AC mov dword ptr ss:[ebp-0x54],ecx
00402582 . 8945 A4 mov dword ptr ss:[ebp-0x5C],eax
00402585 . 894D BC mov dword ptr ss:[ebp-0x44],ecx
00402588 . 8945 B4 mov dword ptr ss:[ebp-0x4C],eax
0040258B 74 58 je XAfkayas_.004025E5 这里直接NOP掉就完美爆破
0040258D . 68 801B4000 push Afkayas_.00401B80 ; You Get It
00402592 . 68 9C1B4000 push Afkayas_.00401B9C ; \r\n
00402597 . FFD7 call edi
00402599 . 8BD0 mov edx,eax
0040259B . 8D4D E8 lea ecx,dword ptr ss:[ebp-0x18]
0040259E . FFD3 call ebx
004025A0 . 50 push eax
004025A1 . 68 A81B4000 push Afkayas_.00401BA8 ; KeyGen It Now
004025A6 . FFD7 call edi
004025A8 . 8D4D 94 lea ecx,dword ptr ss:[ebp-0x6C]
004025AB . 8945 CC mov dword ptr ss:[ebp-0x34],eax
004025AE . 8D55 A4 lea edx,dword ptr ss:[ebp-0x5C]
004025B1 . 51 push ecx
004025B2 . 8D45 B4 lea eax,dword ptr ss:[ebp-0x4C]
004025B5 . 52 push edx
004025B6 . 50 push eax
004025B7 . 8D4D C4 lea ecx,dword ptr ss:[ebp-0x3C]
004025BA . 6A 00 push 0x0
004025BC . 51 push ecx
004025BD . C745 C4 08000>mov dword ptr ss:[ebp-0x3C],0x8
004025C4 . FF15 10414000 call dword ptr ds:[<&MSVBVM50.#595>] ; MSVBVM50.rtcMsgBox
004025CA . 8D4D E8 lea ecx,dword ptr ss:[ebp-0x18]
004025CD . FF15 80414000 call dword ptr ds:[<&MSVBVM50.__vbaFreeS>; MSVBVM50.__vbaFreeStr
004025D3 . 8D55 94 lea edx,dword ptr ss:[ebp-0x6C]
004025D6 . 8D45 A4 lea eax,dword ptr ss:[ebp-0x5C]
004025D9 . 52 push edx
004025DA . 8D4D B4 lea ecx,dword ptr ss:[ebp-0x4C]
004025DD . 50 push eax
004025DE . 8D55 C4 lea edx,dword ptr ss:[ebp-0x3C]
004025E1 . 51 push ecx
004025E2 . 52 push edx
004025E3 . EB 56 jmp XAfkayas_.0040263B
004025E5 > 68 C81B4000 push Afkayas_.00401BC8 ; You Get Wrong
004025EA . 68 9C1B4000 push Afkayas_.00401B9C ; \r\n
004025EF . FFD7 call edi
004025F1 . 8BD0 mov edx,eax
004025F3 . 8D4D E8 lea ecx,dword ptr ss:[ebp-0x18]
004025F6 . FFD3 call ebx
004025F8 . 50 push eax
004025F9 . 68 E81B4000 push Afkayas_.00401BE8 ; Try Again
004025FE . FFD7 call edi
00402600 . 8945 CC mov dword ptr ss:[ebp-0x34],eax
00402603 . 8D45 94 lea eax,dword ptr ss:[ebp-0x6C]
00402606 . 8D4D A4 lea ecx,dword ptr ss:[ebp-0x5C]
00402609 . 50 push eax
0040260A . 8D55 B4 lea edx,dword ptr ss:[ebp-0x4C]
0040260D . 51 push ecx
0040260E . 52 push edx
0040260F . 8D45 C4 lea eax,dword ptr ss:[ebp-0x3C]
00402612 . 6A 00 push 0x0
00402614 . 50 push eax
00402615 . C745 C4 08000>mov dword ptr ss:[ebp-0x3C],0x8
0040261C . FF15 10414000 call dword ptr ds:[<&MSVBVM50.#595>] ; MSVBVM50.rtcMsgBox
2、暂停法找关键位置
OD载入要破解的程序后,F9运行起来,点击按钮出现错误提示框,F12暂停后,ALT+K显示调用,找到程序段地址的调用,双击进入也可来到关键位置

3、对消息函数下断
(MSVBVM50.rtcMsgBox) 方法和F12法一样
4、查找字符串

找到报错的字符,双击进入也可来到破解的关键位置。
学会以上4种方法,你就算学破解入门了,快速来到关键破解位置进行分析了。
详细操作请观看高清视频教程:
https://pan.baidu.com/s/130Urp1S71WqmWRa_seJ6rA
新手学破解入门实例2
http://www.it0365.com/thread-35-1-1.html
(出处: IT资源社区)