AR1 和 AR2代表两个公司的出口,R2模拟互联,两个公司通信,通过ipsec vpn 加密隧道进行业务通信
切记:ipsec 路由器一定用AR系列,千万别用R,否则会给你惊喜
R2只有接口配ip,无任何配置(略)
[Huawei]sys R1
路由器接口配置
[R1]inte g0/0/0
[R1-GigabitEthernet0/0/0]ip ad 192.168.1.254 24
[R1-GigabitEthernet0/0/0]inte g0/0/1
[R1-GigabitEthernet0/0/1]ip ad 100.1.1.1 24
[R1-GigabitEthernet0/0/1]
[R1-GigabitEthernet0/0/1]q
路由配置
[R1]ip route-static 0.0.0.0 0 100.1.1.2
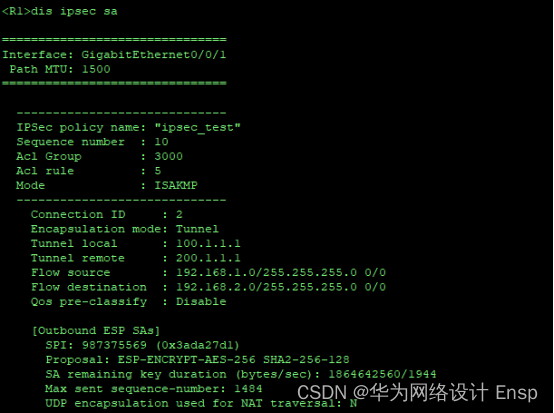
配置ipsec的感兴趣流
[R1]acl number 3000
[R1-acl-adv-3000] rule 5 permit ip source 192.168.1.0 0.0.0.255 destination 192.
168.2.0 0.0.0.255
[R1-acl-adv-3000]q
配置ipsec提议
[R1]ipsec proposal ipsec_test \\ 配置IPsec安全提议名称
[R1-ipsec-proposal-ipsec_test] esp authentication-algorithm sha2-256 \\ 设置ESP(封装安全有效载荷)的认证算法为SHA2-256
[R1-ipsec-proposal-ipsec_test] esp encryption-algorithm aes-256 \\ 设置ESP的加密算法为AES-256
[R1-ipsec-proposal-ipsec_test]
配置ike提议
[R1-ipsec-proposal-ipsec_test]ike proposal 10 \\ 配置ike安全提议名称
[R1-ike-proposal-10] encryption-algorithm aes-cbc-256 \\ 设置加密算法 AES-CBC-256
[R1-ike-proposal-10] dh group2 \\dh组2
[R1-ike-proposal-10]
配置ike对等体
[R1-ike-proposal-10]ike peer SH v1 设置IKE对等体 SH v1
[R1-ike-peer-SH] pre-shared-key simple test@123 \\ 设置预共享密钥 简单 test@123
[R1-ike-peer-SH] ike-proposal 10 \\ 绑定IKE提议 10
[R1-ike-peer-SH] local-address 100.1.1.1 \\ 设置本地地址 100.1.1.1
[R1-ike-peer-SH] remote-address 200.1.1.1 \\ 设置远程地址 200.1.1.1
[R1-ike-peer-SH]
配置ipsec策略
[R1-ike-peer-SH]ipsec policy ipsec_test 10 isakmp \\设置IPsec策略 ipsec_test 10 ISAKMP
[R1-ipsec-policy-isakmp-ipsec_test-10] security acl 3000 \\绑定感兴趣流
[R1-ipsec-policy-isakmp-ipsec_test-10] ike-peer SH \\绑定ike对等体
[R1-ipsec-policy-isakmp-ipsec_test-10] proposal ipsec_test \\绑定安全提议
[R1-ipsec-policy-isakmp-ipsec_test-10]q
接口调用ipsec策略
[R1]inte g0/0/1
[R1-GigabitEthernet0/0/1]ipsec policy ipsec_test
R3 同理
[Huawei]un in en
Info: Information center is disabled.
[Huawei]sys R3
[R3]inte g0/0/1
[R3-GigabitEthernet0/0/1]ip ad 192.168.2.254 24
[R3-GigabitEthernet0/0/1]inte g0/0/0
[R3-GigabitEthernet0/0/0]ip ad 200.1.1.1 24
[R3-GigabitEthernet0/0/0]
[R3-GigabitEthernet0/0/0]q
[R3]ip route-static 0.0.0.0 0 200.1.1.2
[R3]acl number 3000
[R3-acl-adv-3000] rule 5 permit ip source 192.168.2.0 0.0.0.255 destination 192.
168.1.0 0.0.0.255
[R3-acl-adv-3000]q
[R3]ipsec proposal ipsec_test2
[R3-ipsec-proposal-ipsec_test2] esp authentication-algorithm sha2-256
[R3-ipsec-proposal-ipsec_test2] esp encryption-algorithm aes-256
[R3-ipsec-proposal-ipsec_test2]
[R3-ipsec-proposal-ipsec_test2]ike proposal 10
[R3-ike-proposal-10] encryption-algorithm aes-cbc-256
[R3-ike-proposal-10] dh group2
[R3-ike-proposal-10]
[R3-ike-proposal-10]ike peer DH v1
[R3-ike-peer-DH] pre-shared-key simple test@123
[R3-ike-peer-DH] ike-proposal 10
[R3-ike-peer-DH] local-address 200.1.1.1
[R3-ike-peer-DH] remote-address 100.1.1.1
[R3-ike-peer-DH]
[R3-ike-peer-DH]ipsec policy ipsec_test2 20 isakmp
[R3-ipsec-policy-isakmp-ipsec_test2-20] security acl 3000
[R3-ipsec-policy-isakmp-ipsec_test2-20] ike-peer DH
[R3-ipsec-policy-isakmp-ipsec_test2-20] proposal ipsec_test2
[R3-ipsec-policy-isakmp-ipsec_test2-20]q
[R3]inte g0/0/0
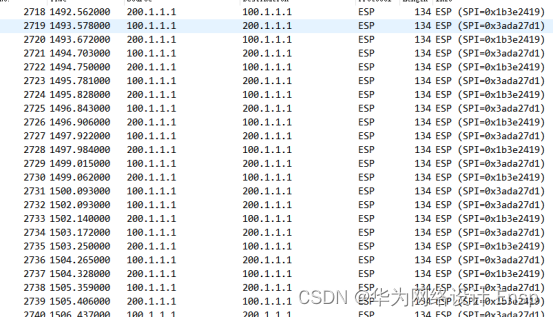
[R3-GigabitEthernet0/0/0] ipsec policy ipsec_test2验证测试