Preface
There are three main methods for ssh remote login password authentication Password: , Keyboard Interactiveand . The first two methods are password authentication, and their meanings are the same. The third method is the most secure login method and is also the default method used by our commonly used cloud servers.Public Key
Public KeyThis article demonstrates how to configure and use to log in.
Server configuration steps
Log in to the target Linux server as the root user and enter ssh-keygen -t rsathe command to generate the public and private keys, as follows:
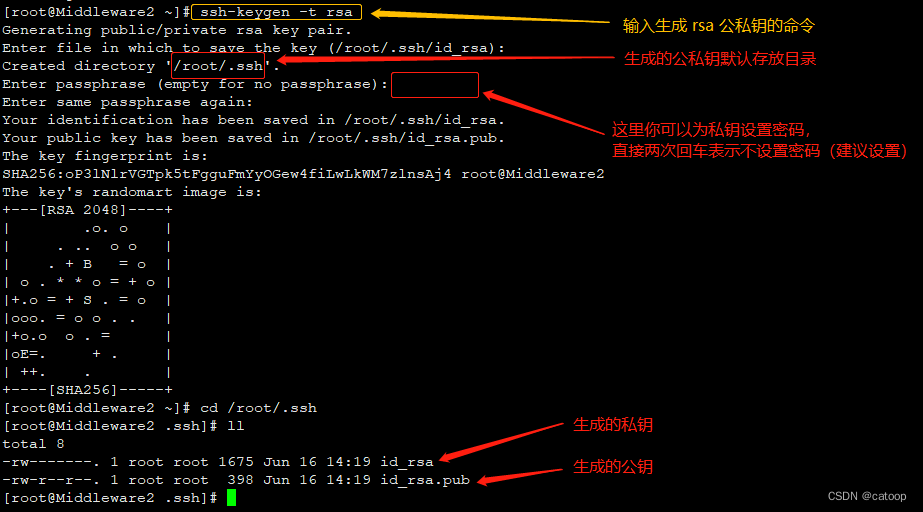
Note: Linux commands are used here to generate public and private keys, which do not necessarily have to be generated on the server. You can use external tools to directly generate public and private keys, and then upload the public keys to the server for the same use. Tools such as XShell provide operations for generating public and private keys.
File permission settings:
chmod 700 /root/.ssh/
chmod 600 ~/.ssh/id_rsa
chmod 644 ~/.ssh/id_rsa.pub
Add the public key to ~/.ssh/authorized_keysthe file:
cat ~/.ssh/id_rsa.pub >> ~/.ssh/authorized_keys
Modify the configuration file of the sshd service /etc/ssh/sshd_config:
# 开启 Pubkey 认证
PubkeyAuthentication yes
# 开启并检查授权文件位置是否正确
AuthorizedKeysFile .ssh/authorized_keys
When I tested and verified locally, I could use it without restarting the sshd service. If your sshd configuration does not take effect, you may need to try restarting the sshd service.
Finally, download the private key file ~/.ssh/id_rsato the local computer, which needs to be used on client connection tools such as XShell.
Take XShell as an example to use
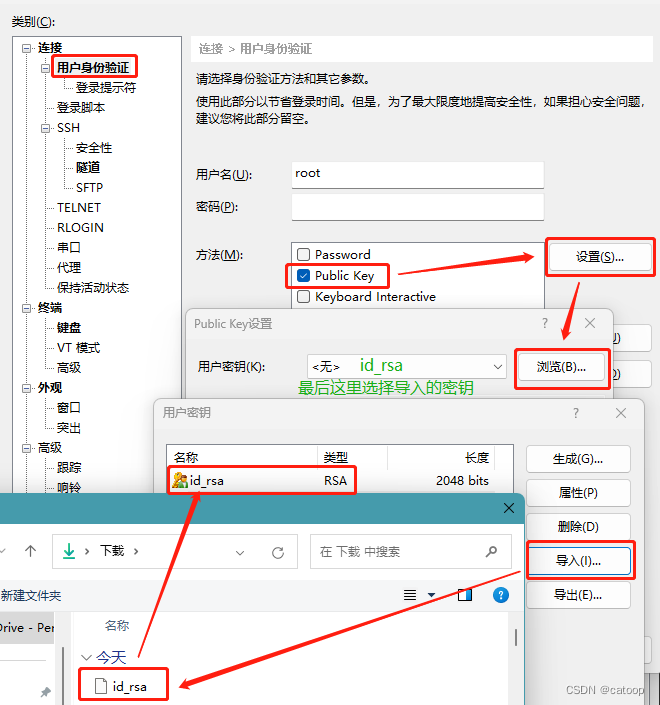
Import and configure the Public Key login method as shown in the figure to connect directly to the Linux ssh console without a password.
(END)