参考:
https://jenkins.io/security/advisory/2020-03-09/
关注几个标为High的漏洞:
OS command injection in CryptoMove Plugin
SECURITY-1635 / CVE-2020-2159
所需权限:Job/Configure
目前未修复
看一下官方给的安装量:
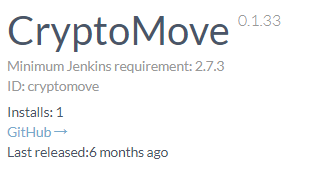
醉了,只有1个!
没有人用,忽略了。
RCE vulnerability in Literate Plugin
SECURITY-1750 / CVE-2020-2158
所需权限应该也是:Job/Configure?
目前未修复
这个安装量也是非常小了:
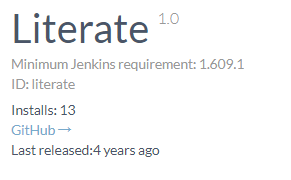
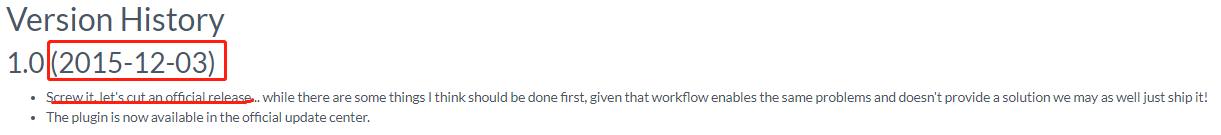
Literate插件没有在插件仓库里找到:
http://updates.jenkins-ci.org/download/plugins/
因为这是一个实验性插件()
参考这里:
https://jenkins.io/doc/developer/publishing/releasing-experimental-updates/
应该是要到Jenkins的pluginmanager里找到Advanced选项卡:
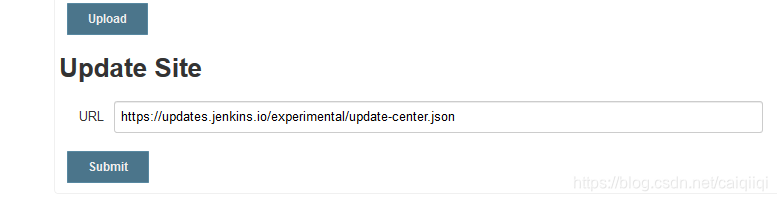
填入这个url:
https://updates.jenkins.io/experimental/update-center.json
然后Submit, 然后Check Now
然后这些实验性插件就会出现在Plugin Manager.
的Available and Updates选项卡里了。
然而,还是没有,不如就按github上说的,自己本地编译然后发布吧:
mvn clean verify
mvn release:prepare release:perform -B
然而编译失败了,
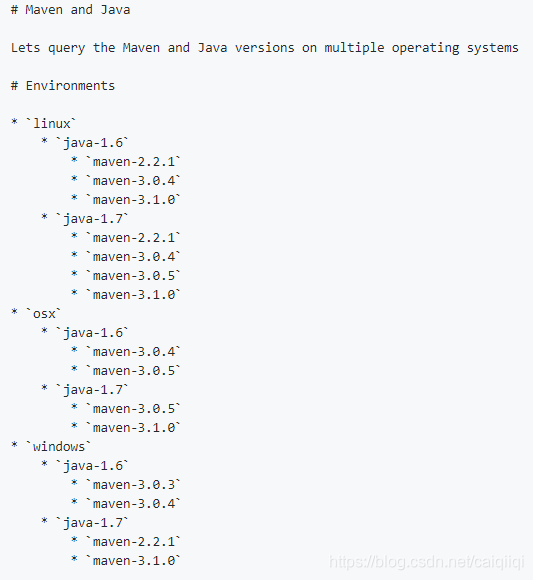
发现这个插件编译对环境版本要求有点老,
Sandbox bypass vulnerability in Script Security Plugin
SECURITY-1754 / CVE-2020-2134 (constructors), CVE-2020-2135 (GroovyInterceptable)
这种周期性频发的利用权限高的漏洞就不关注了。
还有两个XXE:
XXE vulnerability in Cobertura Plugin
SECURITY-1700 / CVE-2020-2138
影响范围:Cobertura Plugin <= 1.15
Cobertura Plugin 1.15 and earlier does not configure its XML parser to prevent XML external entity (XXE) attacks.
This allows a user able to control the input files for the ‘Publish Cobertura Coverage Report’ post-build step to have Jenkins parse a crafted file that uses external entities for extraction of secrets from the Jenkins master or server-side request forgery.
Cobertura Plugin 1.16 disables external entity resolution for its XML parser.
这个插件安装量有点大。

https://plugins.jenkins.io/cobertura/
而且还有一个任意文件写入的漏洞:
Arbitrary file write vulnerability in Cobertura Plugin
SECURITY-1668 / CVE-2020-2139
影响范围:Cobertura Plugin <= 1.15
Cobertura Plugin 1.15 and earlier does not validate file paths from the XML file it parses.
This allows attackers able to control the coverage report content to overwrite any file on the Jenkins master file system.
Cobertura Plugin 1.16 sanitizes the file paths to prevent escape from the base directory.
漏洞复现
学习一下这个插件怎么用
新建一个Job,选择maven风格的,
由于是第一次构建maven风格的,还没有配置mavan的路径,
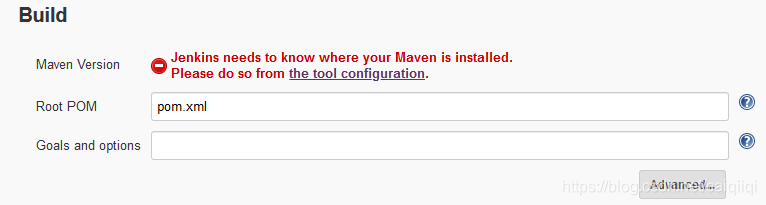
需要到这里设置本地maven的安装路径:
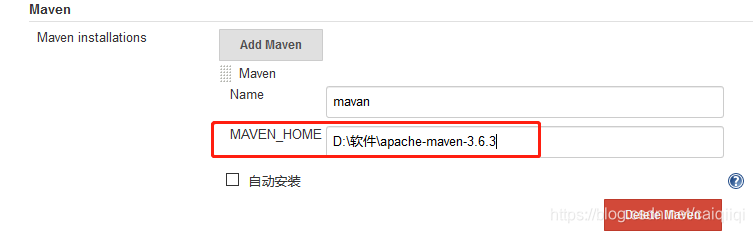
配置之后,再回到之前的Job配置页面刷新一下,就不会有红色的错误了:
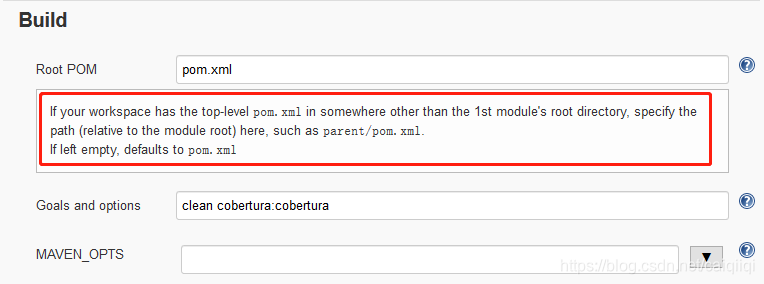
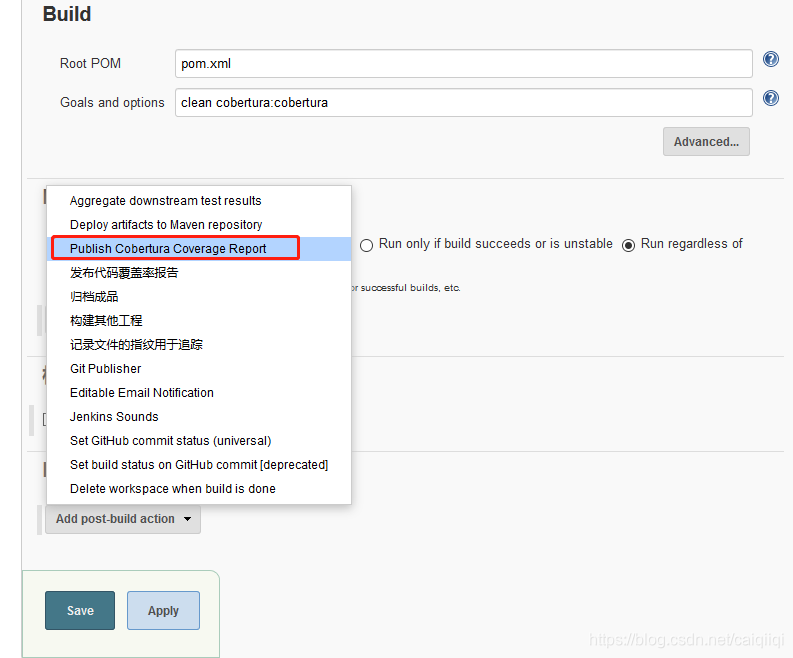
然后设置Goals and options为:
clean cobertura:cobertura
根据这个帮助信息知道应该是在这里指定了任意路径的pom.xml文件:
根据任意文件写入的修复commit中修改代码的地方:
https://github.com/jenkinsci/cobertura-plugin/commit/ea41b3f86a24ab398a588bde6a4eada869bed391
断点下在:
hudson/plugins/cobertura/renderers/SourceCodePainter#paintSourceCode, invoke、
hudson/plugins/cobertura/targets/CoverageResult#getSourceFile, isSourceFileAvailable, getSourceFileContent
漏洞描述中的’Publish Cobertura Coverage Report’ post-build step应该是这里:
XXE漏洞的修复commit应该在:
https://github.com/jenkinsci/cobertura-plugin/commit/fdee535fe4782181d822b875c96df8306f245d48
在hudson/plugins/cobertura/CoberturaCoverageParser.java
和hudson/plugins/cobertura/CoberturaPublisher.java

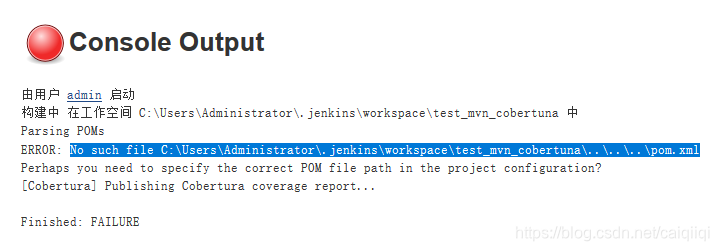
../../cobertura/coverage.xml
填入路径穿越的payload,然后build失败了,查看console日志发现未能找到这个文件:
本来就需要Job/Configure权限才能新建job,而这个漏洞描述还需要能控制coverage report content,就更加困难了吧。
不继续跟了。
杂
Jenkins提交请求之后一般可以在这里下断点:
hudson/model/Job#doConfigSubmit
