文章目录
ShiroUserMapper
ShiroUser queryByName(@Param("userName") String userName);
Set<String> getRolesByUserId(@Param("userid") Integer userId);
Set<String> getPersByUserId(@Param("userid") Integer userId);
ShiroUserMapper.xml
<select id="queryByName" resultType="com.wxm.model.ShiroUser" parameterType="java.lang.String">
select
<include refid="Base_Column_List" />
from t_shiro_user
where username =#{userName}
</select>
<!-- 这是根据用户id获取到所拥有的角色集合-->
<select id="getRolesByUserId" resultType="java.lang.String" parameterType="java.lang.Integer">
select r.roleid from t_shiro_user u,t_shiro_user_role ur,t_shiro_role r
where u.userid = ur.userid and ur.roleid = r.roleid
and u.userid = #{userid}
</select>
<!-- 这是根据用户id获取到所拥有的权限集合-->
<select id="getPersByUserId" resultType="java.lang.String" parameterType="java.lang.Integer">
select p.permission from t_shiro_user u,t_shiro_user_role ur,t_shiro_role_permission rp,t_shiro_permission p
where u.userid = ur.userid and ur.roleid = rp.roleid and rp.perid = p.perid
and u.userid = #{userid}
</select>
MyRealm
package com.wxm.util;
import com.wxm.model.ShiroUser;
import com.wxm.service.ShiroUserService;
import org.apache.shiro.authc.*;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.authz.SimpleAuthorizationInfo;
import org.apache.shiro.realm.AuthorizingRealm;
import org.apache.shiro.subject.PrincipalCollection;
import org.apache.shiro.util.ByteSource;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.stereotype.Component;
import java.util.Set;
/**
* 充当了ini文件,也就是数据源
* 认证的过程
* 1、数据源 (ini->>数据库)
* 2、doGetAuthenticationInfo将数据库的用户信息给subject主体做shiro认证的
* 2.1、需要在当前的realm中调用service来验证,当前用户是否在数据库中存在
* 2.2、盐加密
* @author wxm
* @site www.wxm.com
* @company xxx公司
* @create 2019-12-01 16:18
*/
@Component
public class MyRealm extends AuthorizingRealm {
private ShiroUserService shiroUserService;
public ShiroUserService getShiroUserService() {
return shiroUserService;
}
public void setShiroUserService(ShiroUserService shiroUserService) {
this.shiroUserService = shiroUserService;
}
/**
* 授权
*
* @param principalCollection
* @return
*/
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principalCollection) {
System.out.println("用户据授权");
//获取到的用户名
String username=principalCollection.getPrimaryPrincipal().toString();
//根据用户名获取当前用户
ShiroUser user=shiroUserService.queryByName(username);
//获取用户的角色列表
Set<String> roles=shiroUserService.getRolesByUserId(user.getUserid());
//获取当前用户的权限列表
Set<String> pers=shiroUserService.getPersByUserId(user.getUserid());
SimpleAuthorizationInfo info = new SimpleAuthorizationInfo();
//将用户的授权信息保持到info对象中
info.setRoles(roles);
info.setStringPermissions(pers);
return info;
}
/**
* 认证
*
* @param token 从jsp传递过来的用户名,密码组合成的一个token对象
* @return
* @throws AuthenticationException token是controller层传递过来的,也就是说一做登录操作,就会访问这个方法
*/
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken token) throws AuthenticationException {
//jsp用户名和密码
String userName = token.getPrincipal().toString();
//匹配
ShiroUser shiroUser = this.shiroUserService.queryByName(userName);
//认证
AuthenticationInfo info = new SimpleAuthenticationInfo(
shiroUser.getUsername(),
shiroUser.getPassword(),
ByteSource.Util.bytes(shiroUser.getSalt()),
this.getName()
);
return info;
}
}
springmvc-servlet.xml
<?xml version="1.0" encoding="UTF-8"?>
<beans xmlns="http://www.springframework.org/schema/beans"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xmlns:context="http://www.springframework.org/schema/context"
xmlns:mvc="http://www.springframework.org/schema/mvc" xmlns:aop="http://www.springframework.org/schema/aop"
xsi:schemaLocation="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans.xsd
http://www.springframework.org/schema/context http://www.springframework.org/schema/context/spring-context-4.3.xsd http://www.springframework.org/schema/mvc http://www.springframework.org/schema/mvc/spring-mvc.xsd http://www.springframework.org/schema/aop http://www.springframework.org/schema/aop/spring-aop.xsd">
<!-- 通过context:component-scan元素扫描指定包下的控制器-->
<!--1) 扫描com.javaxl.zf及子子孙孙包下的控制器(扫描范围过大,耗时)-->
<aop:aspectj-autoproxy/>
<context:component-scan base-package="com.wxm"/>
<!--2) 此标签默认注册DefaultAnnotationHandlerMapping和AnnotationMethodHandlerAdapter -->
<!--两个bean,这两个bean是spring MVC为@Controllers分发请求所必须的。并提供了数据绑定支持,-->
<!--@NumberFormatannotation支持,@DateTimeFormat支持,@Valid支持,读写XML的支持(JAXB),读写JSON的支持(Jackson)-->
<mvc:annotation-driven></mvc:annotation-driven>
<!--3) ViewResolver -->
<bean class="org.springframework.web.servlet.view.InternalResourceViewResolver">
<!-- viewClass需要在pom中引入两个包:standard.jar and jstl.jar -->
<property name="viewClass"
value="org.springframework.web.servlet.view.JstlView"></property>
<property name="prefix" value="/"/>
<property name="suffix" value=".jsp"/>
</bean>
<bean id="multipartResolver" class="org.springframework.web.multipart.commons.CommonsMultipartResolver">
<!-- 必须和用户JSP 的pageEncoding属性一致,以便正确解析表单的内容 -->
<property name="defaultEncoding" value="UTF-8"></property>
<!-- 文件最大大小(字节) 1024*1024*50=50M-->
<property name="maxUploadSize" value="52428800"></property>
<!--resolveLazily属性启用是为了推迟文件解析,以便捕获文件大小异常-->
<property name="resolveLazily" value="true"/>
</bean>
<!--4) 单独处理图片、样式、js等资源 -->
<!--<mvc:resources location="/css/" mapping="/css/**"/>-->
<!--<mvc:resources location="/images/" mapping="/images/**"/>-->
<!--<mvc:resources location="/js/" mapping="/js/**"/>-->
<bean class="org.springframework.aop.framework.autoproxy.DefaultAdvisorAutoProxyCreator"
depends-on="lifecycleBeanPostProcessor">
<property name="proxyTargetClass" value="true"></property>
</bean>
<bean class="org.apache.shiro.spring.security.interceptor.AuthorizationAttributeSourceAdvisor">
<property name="securityManager" ref="securityManager"/>
</bean>
<bean id="exceptionResolver" class="org.springframework.web.servlet.handler.SimpleMappingExceptionResolver">
<property name="exceptionMappings">
<props>
<prop key="org.apache.shiro.authz.UnauthorizedException">
unauthorized
</prop>
</props>
</property>
<property name="defaultErrorView" value="unauthorized"/>
</bean>
</beans>
ShirouUserController
package com.wxm.controller;
import com.sun.org.apache.bcel.internal.generic.RETURN;
import com.wxm.model.ShiroUser;
import com.wxm.service.ShiroUserService;
import com.wxm.util.PasswordHelper;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.authc.UsernamePasswordToken;
import org.apache.shiro.authz.annotation.Logical;
import org.apache.shiro.authz.annotation.RequiresPermissions;
import org.apache.shiro.authz.annotation.RequiresRoles;
import org.apache.shiro.authz.annotation.RequiresUser;
import org.apache.shiro.session.Session;
import org.apache.shiro.subject.Subject;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.stereotype.Controller;
import org.springframework.web.bind.annotation.RequestMapping;
import org.springframework.web.bind.annotation.ResponseBody;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
/**
* @author wxm
* @site www.wxm.com
* @company xxx公司
* @create 2019-12-01 16:30
*/
@Controller
public class ShiroUserCotroller {
@Autowired
private ShiroUserService shiroUserService;
/**
* 登入
*
* @param req
* @return
*/
@RequestMapping("/login")
public String login(HttpServletRequest req) {
String uname = req.getParameter("username");
String pwd = req.getParameter("password");
//生成令牌
UsernamePasswordToken token = new UsernamePasswordToken(uname, pwd);
Subject subject = SecurityUtils.getSubject();//登录主体
try {
subject.login(token);
req.getSession().setAttribute("username", uname);
return "hello";
} catch (Exception e) {
req.setAttribute("message", "用户名或密码错误");
return "login";
}
}
/**
* 登出
*
* @param req
* @return
*/
@RequestMapping("/logout")
public String logout(HttpServletRequest req) {
Subject subject = SecurityUtils.getSubject();//拿到登入主体
subject.logout();
return "redirect:/login.jsp";
}
/**
* 注册
*
* @param shiroUser
* @param req
* @param resp
* @return
*/
@RequestMapping("/add")
public String add(ShiroUser shiroUser, HttpServletRequest req, HttpServletResponse resp) {
//获取jsp传过来的用户名和密码
String uname = req.getParameter("username1");
String pwd = req.getParameter("password1");
shiroUser.setUsername(uname);
//使用工具类生成盐
String salt = PasswordHelper.createSalt();
shiroUser.setSalt(salt);
//盐加密后得到的密码
String credentials = PasswordHelper.createCredentials(pwd, salt);
shiroUser.setPassword(credentials);
//新增
int insert = this.shiroUserService.insert(shiroUser);
if (insert > 0) {
req.setAttribute("message", "新增成功!!!");
return "login";
} else {
req.setAttribute("message", "新增失败。。。。");
return "login";
}
}
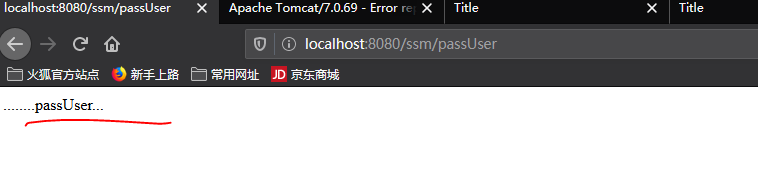
@RequiresUser
@ResponseBody
@RequestMapping("/passUser")
public String passUser() {
return "........passUser...";
}
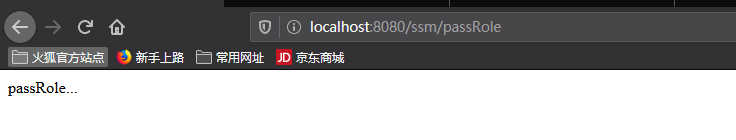
@RequiresRoles(value = {"2", "4"}, logical = Logical.AND)
@ResponseBody
@RequestMapping("/passRole")
public String passRole() {
return "passRole...";
}
@RequiresPermissions(value = {"user:update","user:view"},logical = Logical.OR) @ResponseBody
@RequestMapping("/passPer")
public String passPer() {
return "passPer...";
}
}

这个相当于前面的myraim的规则
验证一:测试用户是否登录
用户数据库表

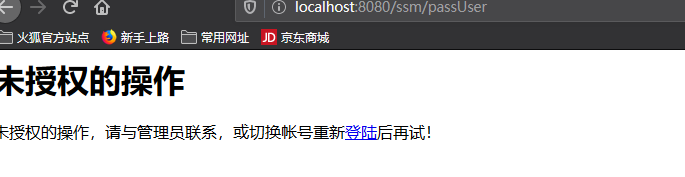
未登录状态访问passUser
admin/zs登录:(需要盐加密)
验证二:测试角色授权是否成功
OR 取并集,AND取交集

1,4分别是zs和zdm

只有zdm登录能访问passRole
zs登录
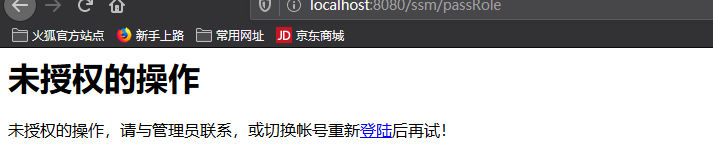
把Controller层的OR改成And

用用户角色中间表举例:
预测结果
用户4 -zdm-才能访问passRole
用户1--zs-不能访问passRole

验证三:角色权限

涉及的数据库表



预测
拥有角色为2,3,4的用户都能访问passPer

但是这里需要shiro盐加密所以是

zs,zdm都能访问但是admin不能登录
