1.虚拟专用网可以通过IPSec 虚拟专用网原理与配置理解虚拟专用网
2.IPsec 虚拟专用网故障排查
(show crypto isakmp)通过它可以了解管理连接所处的状态
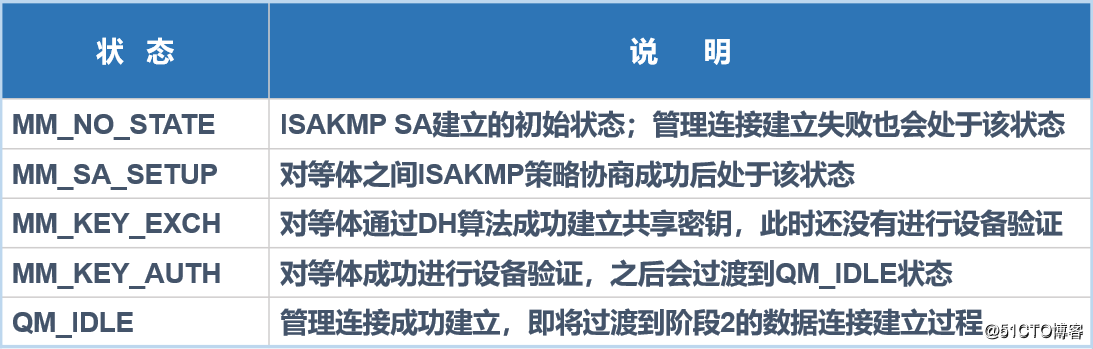
(debug crypto isakmp ) 通过该命令是实际工作中最常用于诊断和排查管理连接出现问题的命令
3.防火墙与路由器的区别
-
IKE协商默认是否开启
默认情况下,IKE协商在路由器中是开启的,而在ASA防火墙中是关闭的 -
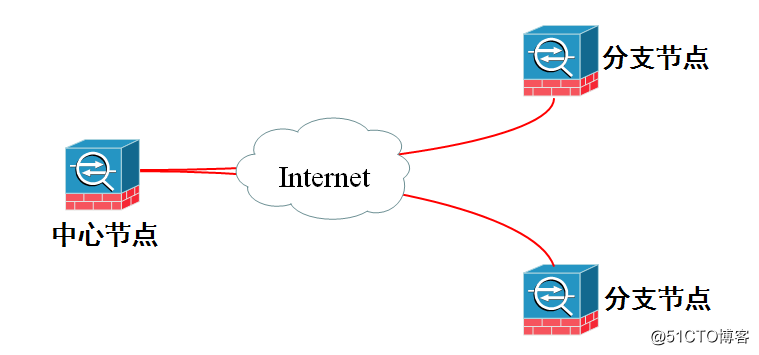
隧道组特性引入
- 接口安全级别对于IPSec流量的影响
ASA(config)#same-security-traffic permit intra-interface
intra-interface 参数允许流量进入和离开都是同一个接口,多于L2L会话中的中心设备
4.配置案例如下:
要求:全网互通,并且pc机能够访问互联网(R1)

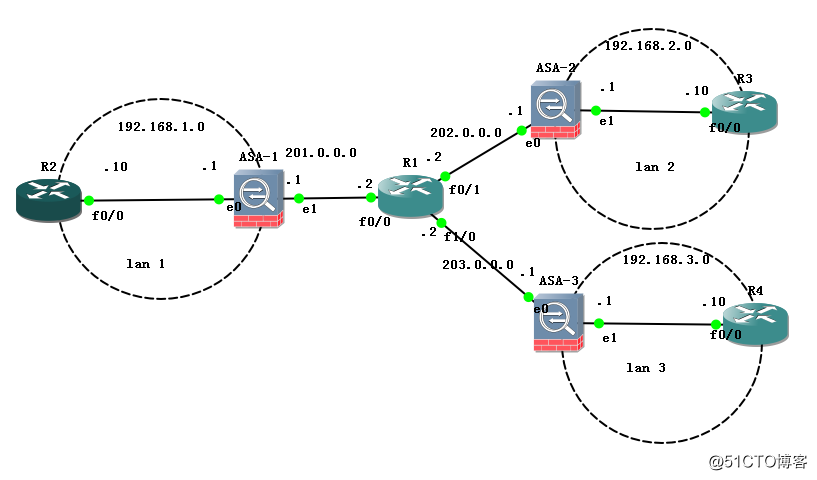
实际上简化图为:
(1)配置IP地址
R2,R3,R4和ASA-1,ASA-2,ASA-3都走一条默认 (R1就配IP)
如R2:
R2(config)#ip route 0.0.0.0 0.0.0.0 192.168.1.1
其它俩个路由器也做如上
防火墙配置如ASA-1:
ciscoasa(config)# int e0/1
ciscoasa(config-if)# nameif outside
ciscoasa(config-if)# security-level 0
ciscoasa(config)# int e0/0
ciscoasa(config-if)# nameif inside
ciscoasa(config-if)# security-level 100
ciscoasa(config)# route outside 0 0 201.0.0.2 //默认路由 其它俩个防火墙配置如这个,IP地址不同,注意不要配错
(2)ASA1的配置:(lan1_lan2)
配置管理连接
ciscoasa(config)# crypto isakmp enable outside
ciscoasa(config)# crypto isakmp policy 1
ciscoasa(config-isakmp-policy)# authentication pre-share
ciscoasa(config-isakmp-policy)# encryption aes
ciscoasa(config-isakmp-policy)# hash md5
ciscoasa(config-isakmp-policy)# group 2
ciscoasa(config-isakmp-policy)# lifetime 10000设置共享密钥:
ciscoasa(config-isakmp-policy)# crypto isakmp key 2008.cn address 202.0.0.1也可
以使用另一种方法
tunnel-group 202.0.0.1 type ipsec-l2l
tunnel-group 202.0.0.1 ipsec-attributes
pre-shared-key 2008.cn配置数据连接
ciscoasa(config)# access-list lan1_lan2 permit ip 192.168.1.0 255.255.255.0 192.168.2.0 255.255.255.0
crypto ipsec transform-set test-set esp-aes esp-md5-hmac
ciscoasa(config)# crypto map test-map 1 match address lan1_lan2
ciscoasa(config)# crypto map test-map 1 set peer 202.0.0.1 //对端的IP
ciscoasa(config)# crypto map test-map 1 set transform-set test-set
ciscoasa(config)# crypto map test-map interface outside //应用到外接口上 在ASA-2上配置如下:
ciscoasa(config)# crypto isakmp enable outside
ciscoasa(config)# crypto isakmp policy 1
ciscoasa(config-isakmp-policy)# authentication pre-share
ciscoasa(config-isakmp-policy)# encryption aes
ciscoasa(config-isakmp-policy)# hash md5
ciscoasa(config-isakmp-policy)# group 2
ciscoasa(config-isakmp-policy)# lifetime 10000
ciscoasa(config-isakmp-policy)# crypto isakmp key 2008.cn address 201.0.0.1配置数据连接
ciscoasa(config)# access-list lan2_lan1 permit ip 192.168.2.0 255.255.255.0 192.168.1.0 255.255.255.0
ciscoasa(config)# crypto ipsec transform-set test-set esp-aes esp-md5-hmac
ciscoasa(config)# crypto map test-map 1 match address lan2_lan1
ciscoasa(config)# crypto map test-map 1 set peer 201.0.0.1
ciscoasa(config)# crypto map test-map 1 set transform-set test-set
ciscoasa(config)# crypto map test-map interface outside //应用到外接口这时lan1与lan2可以互通了
R2#ping 192.168.2.10
Type escape sequence to abort.
Sending 5, 100-byte ICMP Echos to 192.168.2.10, timeout is 2 seconds:
..!!!
Success rate is 60 percent (3/5), round-trip min/avg/max = 72/156/296 ms开始做lan1与lan3互通
ASA-1配置如下:(稍微修改一下就可以)
ciscoasa(config)# tunnel-group 203.0.0.1 type ipsec-l2l
ciscoasa(config)# tunnel-group 203.0.0.1 ipsec-attributes
ciscoasa(config-tunnel-ipsec)# pre-shared-key 2008.cn配置ACL
ciscoasa(config)# access-list lan1_lan3 permit ip 192.168.1.0 255.255.255.0 192.168.3.0 255.255.255.0
ciscoasa(config)# crypto map test-map 2 match address lan1_lan3
ciscoasa(config)# crypto map test-map 2 set peer 203.0.0.1
ciscoasa(config)# crypto map test-map 2 set transform-set test-setASA-3配置如下:
ciscoasa(config)#crypto isakmp enable outside //开启IKE协商功能
ciscoasa(config)# crypto isakmp policy 1
ciscoasa(config-isakmp-policy)# authentication pre-share
ciscoasa(config-isakmp-policy)# encryption aes
ciscoasa(config-isakmp-policy)# hash md5
ciscoasa(config-isakmp-policy)# lifetime 10000
ciscoasa(config-isakmp-policy)# crypto isakmp key 2008.cn address 203.0.0.2ciscoasa(config)# access-list lan3_lan1 permit ip 192.168.3.0 255.255.255.0 192.168.1.0 255.255.255.0
ciscoasa(config)# crypto ipsec transform-set test-set esp-aes esp-md5-hmac
ciscoasa(config)# crypto map test-map 1 match address lan3_lan1
ciscoasa(config)# crypto map test-map 1 set peer 201.0.0.1
ciscoasa(config)# crypto map test-map 1 set transform-set test-set
ciscoasa(config)# crypto map test-mao interface outside 实现lan2_lan3 虚拟专用网通信,中间经过lan1转发
ASA1上需添加的配置:
ciscoasa(config)# same-security-traffic permit intra-interface //允许流量进入和离开同一个接口
iscoasa(config)#access-list lan1_lan2 permit ip 192.168.3.0 255.255.255.0 192.168.2.0 255.255.255.0
iscoasa(config)#access-list lan1_lan3 permit ip 192.168.2.0 255.255.255.0 192.168.3.0 255.255.255.0 ASA2上配置:
添加ACL
ciscoasa(config)# access-list lan2_lan1 permit ip 192.168.2.0 255.255.255.0 192.168.3.0 255.255.255.0ASA3上配置:
添加ACL
ciscoasa(config)#access-list lan3_lan1 permit ip 192.168.3.0 255.255.255.0 192.168.2.0 255.255.255.0
如果需要让公司的其他网段能访问互联网,需要在ASA上做PAT,并启用nat控制,豁免虚拟专用网的流量
启用
nat-control
ciscoasa(config)#nat (inside) 1 0 0
ciscoasa(config)#global (outside) 1 interface
ciscoasa(config)#access-list asd permit ip 192.168.1.0 255.255.255.0 192.168.2.0 255.255.255.0
ciscoasa(config)#access-list asd permit ip 192.168.1.0 255.255.255.0 192.168.3.0 255.255.255.0
ciscoasa(config)#nat (inside) 0 access-list asdASA2上配置:
ciscoasa(config)#nat (inside) 1 0 0
ciscoasa(config)#global (outside) 1 interface
ciscoasa(config)#nat (inside) 0 access-list lan2_lan1ASA3上配置:
ciscoasa(config)#nat (inside) 1 0 0
ciscoasa(config)#global (outside) 1 interface
ciscoasa(config)#nat (inside) 0 access-list lan3_lan1
全网互通