版权声明:本文为博主原创文章,遵循 CC 4.0 BY-SA 版权协议,转载请附上原文出处链接和本声明。
本章目标:
1、shiro认证
2、盐加密
请先参考我的另一篇博客 Shiro 入门使用 ,能更好的理解本章内容,Shiro 入门使用:https://blog.csdn.net/qq_44641053/article/details/102527260
Shiro认证
1、Pom依赖:
<dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-core</artifactId>
<version>1.3.2</version>
</dependency>
<dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-web</artifactId>
<version>1.3.2</version>
</dependency>
<dependency>
<groupId>org.apache.shiro</groupId>
<artifactId>shiro-spring</artifactId>
<version>1.3.2</version>
</dependency>
2、web.xml配置:
<!-- shiro过滤器定义 -->
<filter>
<filter-name>shiroFilter</filter-name>
<filter-class>org.springframework.web.filter.DelegatingFilterProxy</filter-class>
<init-param>
<!-- 该值缺省为false,表示生命周期由SpringApplicationContext管理,设置为true则表示由ServletContainer管理 -->
<param-name>targetFilterLifecycle</param-name>
<param-value>true</param-value>
</init-param>
</filter>
<filter-mapping>
<filter-name>shiroFilter</filter-name>
<url-pattern>/*</url-pattern>
</filter-mapping>
通过 逆向工程 将五张表生成对应的 model、mapper(ShiroUser,ShiroUserMapper,ShiroUserMapper.xml)
3、自定义 Realm
MyRealm.java
package com.dj.ssm.shiro;
import com.dj.ssm.model.ShiroUser;
import com.dj.ssm.model.User;
import com.dj.ssm.service.ShiroUserService;
import com.dj.ssm.service.UserService;
import org.apache.shiro.authc.AuthenticationException;
import org.apache.shiro.authc.AuthenticationInfo;
import org.apache.shiro.authc.AuthenticationToken;
import org.apache.shiro.authc.SimpleAuthenticationInfo;
import org.apache.shiro.authz.AuthorizationInfo;
import org.apache.shiro.realm.AuthorizingRealm;
import org.apache.shiro.subject.PrincipalCollection;
import org.apache.shiro.util.ByteSource;
import org.springframework.stereotype.Service;
public class MyRealm extends AuthorizingRealm {
private ShiroUserService shiroUserService;
public ShiroUserService getShiroUserService() {
return shiroUserService;
}
public void setShiroUserService(ShiroUserService shiroUserService) {
this.shiroUserService = shiroUserService;
}
/**
* 授权
* @param principalCollection
* @return
*/
@Override
protected AuthorizationInfo doGetAuthorizationInfo(PrincipalCollection principals) {
return null;
}
/**
* 认证
* @param token 从jsp传递过来的用户名密码组合成的一个token对象
* @return
* @throws AuthenticationException
*
* 认证过程:
* 1.数据源(ini--》数据库)
* 2.AuthenticationInfo将数据库的用户信息给subject主题做shiro认证的
* 2.1.需要在当前的realm中调用service来验证,当前用户是否在数据库中存在
* 2.2.盐加密
*/
@Override
protected AuthenticationInfo doGetAuthenticationInfo(AuthenticationToken token) throws AuthenticationException {
System.out.println("身份认证...");
String username = token.getPrincipal().toString();
String password = token.getCredentials().toString();
ShiroUser user = shiroUserService.queryByName(username);
// 拿到数据库中的用户信息,放入token凭证中,用于controler进行对比
AuthenticationInfo info = new SimpleAuthenticationInfo(
user.getUsername(),
user.getPassword(),
ByteSource.Util.bytes(user.getSalt()),
this.getName()
);
return info;
}
}
ShiroUserMapper和ShiroUserMapper.xml中加入:
ShiroUser queryByName(String uname);
Mapper 中新增
<select id="queryByName" resultType="com.dj.ssm.model.ShiroUser" parameterType="java.lang.String">
select
<include refid="Base_Column_List" />
from t_shiro_user
where userName = #{userName}
</select>
Service层
ShiroUserService.java
package com.dj.ssm.service;
import com.dj.ssm.model.ShiroUser;
import java.util.Set;
public interface ShiroUserService {
public Set<String> getRolesByUserId(Integer userId);
public Set<String> getPersByUserId(Integer userId);
public ShiroUser queryByName(String userName);
public int insert(ShiroUser shiroUser);
}
ShiroUserServiceImpl.java
package com.dj.ssm.service.impl;
import com.dj.ssm.mapper.ShiroUserMapper;
import com.dj.ssm.model.ShiroUser;
import com.dj.ssm.service.ShiroUserService;
import org.springframework.beans.factory.annotation.Autowired;
import org.springframework.stereotype.Service;
import java.util.Set;
@Service("shiroUserService")
public class ShiroUserServiceImpl implements ShiroUserService {
@Autowired
private ShiroUserMapper shiroUserMapper;
@Override
public Set<String> getRolesByUserId(Integer userId) {
return shiroUserMapper.getRolesByUserId(userId);
}
@Override
public Set<String> getPersByUserId(Integer userId) {
return shiroUserMapper.getPersByUserId(userId);
}
@Override
public ShiroUser queryByName(String userName) {
return shiroUserMapper.queryByName(userName);
}
@Override
public int insert(ShiroUser shiroUser) {
return shiroUserMapper.insert(shiroUser);
}
}
4、application-shiro配置
applicationContext-shiro.xml
<?xml version="1.0" encoding="UTF-8"?>
<beans xmlns="http://www.springframework.org/schema/beans"
xmlns:xsi="http://www.w3.org/2001/XMLSchema-instance"
xsi:schemaLocation="http://www.springframework.org/schema/beans http://www.springframework.org/schema/beans/spring-beans.xsd">
<!--配置自定义的Realm-->
<bean id="shiroRealm" class="com.dj.ssm.shiro.MyRealm">
<property name="shiroUserService" ref="shiroUserService" />
<!--注意:重要的事情说三次~~~~~~此处加密方式要与用户注册时的算法一致 -->
<!--注意:重要的事情说三次~~~~~~此处加密方式要与用户注册时的算法一致 -->
<!--注意:重要的事情说三次~~~~~~此处加密方式要与用户注册时的算法一致 -->
<!--以下三个配置告诉shiro将如何对用户传来的明文密码进行加密-->
<property name="credentialsMatcher">
<bean id="credentialsMatcher" class="org.apache.shiro.authc.credential.HashedCredentialsMatcher">
<!--指定hash算法为MD5-->
<property name="hashAlgorithmName" value="md5"/>
<!--指定散列次数为1024次-->
<property name="hashIterations" value="1024"/>
<!--true指定Hash散列值使用Hex加密存. false表明hash散列值用用Base64-encoded存储-->
<property name="storedCredentialsHexEncoded" value="true"/>
</bean>
</property>
</bean>
<!--注册安全管理器-->
<bean id="securityManager" class="org.apache.shiro.web.mgt.DefaultWebSecurityManager">
<property name="realm" ref="shiroRealm" />
</bean>
<!--Shiro核心过滤器-->
<bean id="shiroFilter" class="org.apache.shiro.spring.web.ShiroFilterFactoryBean">
<!-- Shiro的核心安全接口,这个属性是必须的 -->
<property name="securityManager" ref="securityManager" />
<!-- 身份验证失败,跳转到登录页面 -->
<property name="loginUrl" value="/login"/>
<!-- 身份验证成功,跳转到指定页面 -->
<!--<property name="successUrl" value="/index.jsp"/>-->
<!-- 权限验证失败,跳转到指定页面 -->
<property name="unauthorizedUrl" value="/unauthorized.jsp"/>
<!-- Shiro连接约束配置,即过滤链的定义 -->
<property name="filterChainDefinitions">
<value>
<!--
注:anon,authcBasic,auchc,user是认证过滤器
perms,roles,ssl,rest,port是授权过滤器
-->
<!--anon 表示匿名访问,不需要认证以及授权-->
<!--authc表示需要认证 没有进行身份认证是不能进行访问的-->
<!--roles[admin]表示角色认证,必须是拥有admin角色的用户才行-->
/user/login=anon
/user/updatePwd.jsp=authc
/admin/*.jsp=roles[admin]
/user/teacher.jsp=perms["user:update"]
<!-- /css/** = anon
/images/** = anon
/js/** = anon
/ = anon
/user/logout = logout
/user/** = anon
/userInfo/** = authc
/dict/** = authc
/console/** = roles[admin]
/** = anon-->
</value>
</property>
</bean>
<!-- Shiro生命周期,保证实现了Shiro内部lifecycle函数的bean执行 -->
<bean id="lifecycleBeanPostProcessor" class="org.apache.shiro.spring.LifecycleBeanPostProcessor"/>
</beans>
ShiroUserController.java
package com.dj.ssm.controller;
import org.apache.shiro.SecurityUtils;
import org.apache.shiro.authc.UsernamePasswordToken;
import org.apache.shiro.subject.Subject;
import org.springframework.stereotype.Controller;
import org.springframework.web.bind.annotation.RequestMapping;
import dj.servlet.ServletException;
import dj.servlet.http.HttpServletRequest;
import dj.servlet.http.HttpServletResponse;
import java.io.IOException;
@Controller
public class ShiroUserController {
@Autowired
private ShiroUserService shiroUserService;
@RequestMapping("/login")
public String login(HttpServletRequest req, HttpServletResponse resp) {
Subject subject = SecurityUtils.getSubject();
String uname = req.getParameter("username");
String pwd = req.getParameter("password");
UsernamePasswordToken token = new UsernamePasswordToken(uname, pwd);
try {
subject.login(token);
return "main";
} catch (Exception e) {
req.setAttribute("message", "用户名或者密码错误");
return "login";
}
}
@RequestMapping("/logout")
public String logout(HttpServletRequest req, HttpServletResponse resp) {
Subject subject = SecurityUtils.getSubject();
subject.logout();
return "login";
}
@RequestMapping("/register")
public String register(HttpServletRequest req, HttpServletResponse resp) {
String uname = req.getParameter("username");
String pwd = req.getParameter("password");
String salt = PasswordHelper.createSalt();
String credentials = PasswordHelper.createCredentials(pwd, salt);
ShiroUser shiroUser = new ShiroUser();
shiroUser.setUsername(uname);
shiroUser.setPassword(credentials);
shiroUser.setSalt(salt);
int insert = shiroUserService.insert(shiroUser);
if (insert > 0) {
req.setAttribute("message", "注册成功");
return "login";
} else {
req.setAttribute("message", "注册失败");
return "login";
}
}
}
jsp界面,请参见上一篇博客哦,♪(∇*)
盐加密
盐加密工具类,在做新增用户的时候使用,将加密后的密码、及加密时候的盐放入数据库;
本篇博客中的表数据是现成的,暂时用不上这个工具类去生成数据;
PasswordHelper.java
package com.dj.ssm.util;
import org.apache.shiro.crypto.RandomNumberGenerator;
import org.apache.shiro.crypto.SecureRandomNumberGenerator;
import org.apache.shiro.crypto.hash.SimpleHash;
public class PasswordHelper {
/**
* 随机数生成器
*/
private static RandomNumberGenerator randomNumberGenerator = new SecureRandomNumberGenerator();
/**
* 指定hash算法为MD5
*/
private static final String hashAlgorithmName = "md5";
/**
* 指定散列次数为1024次,即加密1024次
*/
private static final int hashIterations = 1024;
/**
* true指定Hash散列值使用Hex加密存. false表明hash散列值用用Base64-encoded存储
*/
private static final boolean storedCredentialsHexEncoded = true;
/**
* 获得加密用的盐
*
* @return
*/
public static String createSalt() {
return randomNumberGenerator.nextBytes().toHex();
}
/**
* 获得加密后的凭证
*
* @param credentials 凭证(即密码)
* @param salt 盐
* @return
*/
public static String createCredentials(String credentials, String salt) {
SimpleHash simpleHash = new SimpleHash(hashAlgorithmName, credentials,
salt, hashIterations);
return storedCredentialsHexEncoded ? simpleHash.toHex() : simpleHash.toBase64();
}
/**
* 进行密码验证
*
* @param credentials 未加密的密码
* @param salt 盐
* @param encryptCredentials 加密后的密码
* @return
*/
public static boolean checkCredentials(String credentials, String salt, String encryptCredentials) {
return encryptCredentials.equals(createCredentials(credentials, salt));
}
public static void main(String[] args) {
//盐
String salt = createSalt();
System.out.println(salt);
System.out.println(salt.length());
//凭证+盐加密后得到的密码
String credentials = createCredentials("123", salt);
System.out.println(credentials);
System.out.println(credentials.length());
boolean b = checkCredentials("123", salt, credentials);
System.out.println(b);
}
}
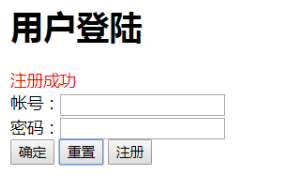
具体jsp界面:
login.jsp
<%@ page contentType="text/html;charset=UTF-8" language="java" %>
<html>
<head>
<title>Title</title>
</head>
<body>
<h1>用户登陆</h1>
<div style="color: red">${message}</div>
<form action="${pageContext.request.contextPath}/login" method="post">
帐号:<input type="text" name="username"><br>
密码:<input type="password" name="password"><br>
<input type="submit" value="确定">
<input type="reset" value="重置">
<input type="button" onclick="location.href='${pageContext.request.contextPath}/insert.jsp'" value="注册">
</form>
</body>
</html>
insert.jsp
<%--
Created by IntelliJ IDEA.
User: Administrator
Date: 2019/10/13 0013
Time: 19:01
To change this template use File | Settings | File Templates.
--%>
<%@ page contentType="text/html;charset=UTF-8" language="java" %>
<html>
<head>
<title>Title</title>
</head>
<body>
<h1>用户注册</h1>
<form action="${pageContext.request.contextPath}/register" method="post">
帐号:<input type="text" name="username"><br>
密码:<input type="password" name="password"><br>
<input type="submit" value="注册">
<input type="button" onclick="location.href='${pageContext.request.contextPath}/login.jsp'" value="返回">
</form>
</body>
</html>
5、运行效果:
在不登陆的情况下只能访问 login.jsp
zs用户登录只能看到个人密码修改界面
ls用户登录,比zs多看到老师简介界面
6、数据库脚本
/*
SQLyog v10.2
MySQL - 5.5.36 : Database - mybatis_ssm
*********************************************************************
*/
/*!40101 SET NAMES utf8 */;
/*!40101 SET SQL_MODE=''*/;
/*!40014 SET @OLD_UNIQUE_CHECKS=@@UNIQUE_CHECKS, UNIQUE_CHECKS=0 */;
/*!40014 SET @OLD_FOREIGN_KEY_CHECKS=@@FOREIGN_KEY_CHECKS, FOREIGN_KEY_CHECKS=0 */;
/*!40101 SET @OLD_SQL_MODE=@@SQL_MODE, SQL_MODE='NO_AUTO_VALUE_ON_ZERO' */;
/*!40111 SET @OLD_SQL_NOTES=@@SQL_NOTES, SQL_NOTES=0 */;
CREATE DATABASE /*!32312 IF NOT EXISTS*/`mybatis_ssm` /*!40100 DEFAULT CHARACTER SET utf8 */;
USE `mybatis_ssm`;
/*Table structure for table `t_shiro_permission` */
DROP TABLE IF EXISTS `t_shiro_permission`;
CREATE TABLE `t_shiro_permission` (
`perid` int(11) NOT NULL AUTO_INCREMENT COMMENT 'ID,主键',
`pername` varchar(100) NOT NULL COMMENT '权限名称',
`pid` int(11) DEFAULT NULL COMMENT '父编号',
`permission` varchar(100) NOT NULL COMMENT '权限字符串:例如:system:user:create:1',
PRIMARY KEY (`perid`)
) ENGINE=InnoDB AUTO_INCREMENT=7 DEFAULT CHARSET=utf8;
/*Data for the table `t_shiro_permission` */
insert into `t_shiro_permission`(`perid`,`pername`,`pid`,`permission`) values (1,'书籍新增',-1,'user:create'),(2,'书籍修改',-1,'user:update'),(3,'书籍删除',-1,'user:delete'),(4,'书籍列表',-1,'user:view'),(5,'书籍详情',-1,'user:load'),(6,'书籍信息导出',-1,'user:export');
/*Table structure for table `t_shiro_role` */
DROP TABLE IF EXISTS `t_shiro_role`;
CREATE TABLE `t_shiro_role` (
`roleid` int(11) NOT NULL AUTO_INCREMENT COMMENT '角色ID,主键',
`rolename` varchar(100) NOT NULL COMMENT '角色名称',
`description` varchar(100) DEFAULT NULL COMMENT '角色描述',
PRIMARY KEY (`roleid`),
UNIQUE KEY `rolename` (`rolename`)
) ENGINE=InnoDB AUTO_INCREMENT=5 DEFAULT CHARSET=utf8;
/*Data for the table `t_shiro_role` */
insert into `t_shiro_role`(`roleid`,`rolename`,`description`) values (1,'普通用户',NULL),(2,'高级用户',NULL),(3,'特权用户',NULL),(4,'管理员',NULL);
/*Table structure for table `t_shiro_role_permission` */
DROP TABLE IF EXISTS `t_shiro_role_permission`;
CREATE TABLE `t_shiro_role_permission` (
`roleid` int(11) NOT NULL COMMENT '角色ID',
`perid` int(11) NOT NULL COMMENT '权限ID',
PRIMARY KEY (`roleid`,`perid`)
) ENGINE=InnoDB DEFAULT CHARSET=utf8;
/*Data for the table `t_shiro_role_permission` */
insert into `t_shiro_role_permission`(`roleid`,`perid`) values (1,1),(2,1),(2,2),(3,1),(3,2),(3,3),(3,4),(3,5),(4,1),(4,2),(4,3),(4,4),(4,5),(4,6);
/*Table structure for table `t_shiro_user` */
DROP TABLE IF EXISTS `t_shiro_user`;
CREATE TABLE `t_shiro_user` (
`userid` int(11) NOT NULL AUTO_INCREMENT COMMENT '用户ID,主键',
`username` varchar(10) NOT NULL COMMENT '用户账号',
`PASSWORD` varchar(32) NOT NULL COMMENT '用户密码=MD5+盐加密',
`salt` varchar(32) NOT NULL COMMENT '盐',
`createdate` timestamp NULL DEFAULT CURRENT_TIMESTAMP COMMENT '创建日期',
PRIMARY KEY (`userid`),
UNIQUE KEY `username` (`username`)
) ENGINE=InnoDB AUTO_INCREMENT=5 DEFAULT CHARSET=utf8;
/*Data for the table `t_shiro_user` */
insert into `t_shiro_user`(`userid`,`username`,`PASSWORD`,`salt`,`createdate`) values (1,'zs','797b9916091af1463c03bd3d0c433ea7','a88e860b1f70960af7575145247c55ec','2018-12-27 11:47:11'),(2,'ls','60dffbf999e1c613a3ce15a10fdf2d75','7b4bdcce6329281584322e77861c5248','2018-12-27 11:47:11'),(3,'ww','60dffbf999e1c613a3ce15a10fdf2d75','7b4bdcce6329281584322e77861c5248','2018-12-27 11:47:11'),(4,'zdm','60dffbf999e1c613a3ce15a10fdf2d75','7b4bdcce6329281584322e77861c5248','2018-12-27 19:30:36');
/*Table structure for table `t_shiro_user_role` */
DROP TABLE IF EXISTS `t_shiro_user_role`;
CREATE TABLE `t_shiro_user_role` (
`userid` int(11) NOT NULL COMMENT '用户ID',
`roleid` int(11) NOT NULL COMMENT '角色ID',
PRIMARY KEY (`userid`,`roleid`)
) ENGINE=InnoDB DEFAULT CHARSET=utf8;
/*Data for the table `t_shiro_user_role` */
insert into `t_shiro_user_role`(`userid`,`roleid`) values (1,1),(2,2),(3,3),(4,1),(4,4);
/*!40101 SET SQL_MODE=@OLD_SQL_MODE */;
/*!40014 SET FOREIGN_KEY_CHECKS=@OLD_FOREIGN_KEY_CHECKS */;
/*!40014 SET UNIQUE_CHECKS=@OLD_UNIQUE_CHECKS */;
/*!40111 SET SQL_NOTES=@OLD_SQL_NOTES */;
7、盐加密工具类
PasswordHelper.java
package com.dj.ssm.util;
import org.apache.shiro.crypto.RandomNumberGenerator;
import org.apache.shiro.crypto.SecureRandomNumberGenerator;
import org.apache.shiro.crypto.hash.SimpleHash;
/**
* 用于shiro权限认证的密码工具类
*/
public class PasswordHelper {
/**
* 随机数生成器
*/
private static RandomNumberGenerator randomNumberGenerator = new SecureRandomNumberGenerator();
/**
* 指定hash算法为MD5
*/
private static final String hashAlgorithmName = "md5";
/**
* 指定散列次数为1024次,即加密1024次
*/
private static final int hashIterations = 1024;
/**
* true指定Hash散列值使用Hex加密存. false表明hash散列值用用Base64-encoded存储
*/
private static final boolean storedCredentialsHexEncoded = true;
/**
* 获得加密用的盐
*
* @return
*/
public static String createSalt() {
return randomNumberGenerator.nextBytes().toHex();
}
/**
* 获得加密后的凭证
*
* @param credentials 凭证(即密码)
* @param salt 盐
* @return
*/
public static String createCredentials(String credentials, String salt) {
SimpleHash simpleHash = new SimpleHash(hashAlgorithmName, credentials,
salt, hashIterations);
return storedCredentialsHexEncoded ? simpleHash.toHex() : simpleHash.toBase64();
}
/**
* 进行密码验证
*
* @param credentials 未加密的密码
* @param salt 盐
* @param encryptCredentials 加密后的密码
* @return
*/
public static boolean checkCredentials(String credentials, String salt, String encryptCredentials) {
return encryptCredentials.equals(createCredentials(credentials, salt));
}
public static void main(String[] args) {
//盐
String salt = createSalt();
System.out.println(salt);
System.out.println(salt.length());
//凭证+盐加密后得到的密码
String credentials = createCredentials("123", salt);
System.out.println(credentials);
System.out.println(credentials.length());
boolean b = checkCredentials("123", salt, credentials);
System.out.println(b);
}
}