环境版本
[root@test ~]# lsb_release -a
LSB Version: :core-4.1-amd64:core-4.1-noarch
Distributor ID: CentOS
Description: CentOS Linux release 7.4.1708 (Core)
Release: 7.4.1708
Codename: Core
openvpn-2.4.5-1.el7.x86_64
easy-rsa-3.0.3-1.el7.noarch安装
yum install -y openssl openssl-devel lzo lzo-devel pam pam-devel automake pkgconfig makecache
yum install -y openvpn
yum install -y easy-rsa
groupadd openvpn
useradd -g openvpn -M -s /sbin/nologin openvpn
mkdir /etc/openvpn/
cp -R /usr/share/easy-rsa/ /etc/openvpn/
cp /usr/share/doc/openvpn-2.4.5/sample/sample-config-files/server.conf /etc/openvpn/
cp -r /usr/share/doc/easy-rsa-3.0.3/vars.example /etc/openvpn/easy-rsa/3.0/vars配置文件
/etc/openvpn/server.conf
port 1194
proto udp
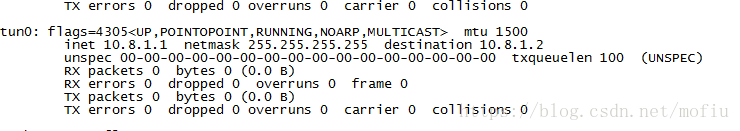
dev tun
ca /etc/openvpn/easy-rsa/3.0/pki/ca.crt
cert /etc/openvpn/easy-rsa/3.0/pki/issued/wwwserver.crt
key /etc/openvpn/easy-rsa/3.0/pki/private/wwwserver.key
dh /etc/openvpn/easy-rsa/3.0/pki/dh.pem
tls-auth /etc/openvpn/ta.key 0
server 10.8.1.0 255.255.255.0
ifconfig-pool-persist ipp.txt
push "redirect-gateway def1 bypass-dhcp"
push "dhcp-option DNS 223.5.5.5"
push "dhcp-option DNS 114.114.114.114"
keepalive 10 120
cipher AES-256-CBC
comp-lzo
max-clients 50
user openvpn
group openvpn
persist-key
persist-tun
status openvpn-status.log
log-append openvpn.log
verb 3
mute 20/etc/openvpn/easy-rsa/3.0/vars
去掉一下参数前面的#号
set_var EASYRSA "$PWD"
set_var EASYRSA_PKI "$EASYRSA/pki"
set_var EASYRSA_DN "cn_only"
set_var EASYRSA_REQ_COUNTRY "CN"
set_var EASYRSA_REQ_PROVINCE "BEIJING"
set_var EASYRSA_REQ_CITY "BEIJING"
set_var EASYRSA_REQ_ORG "OpenVPN CERTIFICATE AUTHORITY"
set_var EASYRSA_REQ_EMAIL "[email protected]"
set_var EASYRSA_REQ_OU "OpenVPN EASY CA"
set_var EASYRSA_KEY_SIZE 2048
set_var EASYRSA_ALGO rsa
set_var EASYRSA_CA_EXPIRE 7000
set_var EASYRSA_CERT_EXPIRE 3650
set_var EASYRSA_NS_SUPPORT "no"
set_var EASYRSA_NS_COMMENT "OpenVPN CERTIFICATE AUTHORITY"
set_var EASYRSA_EXT_DIR "$EASYRSA/x509-types"
set_var EASYRSA_SSL_CONF "$EASYRSA/openssl-1.0.cnf"
set_var EASYRSA_DIGEST "sha256"证书的创建
cd /etc/openvpn/easy-rsa/3.0
./easyrsa init-pki
初始化,会在当前目录创建PKI目录,用于存储一些中间变量及最终生成的证书
./easyrsa build-ca
创建根证书,首先会提示设置密码,用于ca对之后生成的server和client证书签名时使用,然后会提示设置Country Name,State or Province Name,Locality Name,Organization Name,Organizational Unit Name,Common Name,Email Address,可以键入回车使用默认的,也可以手动更改
设置ca密码(输入两次):ca.com./easyrsa gen-dh
openvpn --genkey --secret ta.key
cp -r ta.key /etc/openvpn/创建服务端证书,生成请求,使用gen-req来生成req,创建server端证书和private key,可以使用nopass表示不加密private key,然后会提示设置Country Name,State or Province Name,Locality Name,Organization Name,Organizational Unit Name,Common Name,Email Address,可以键入回车使用默认的,也可以手动更改
./easyrsa gen-req wwwserver
设置server密码(输入两次):openserver.com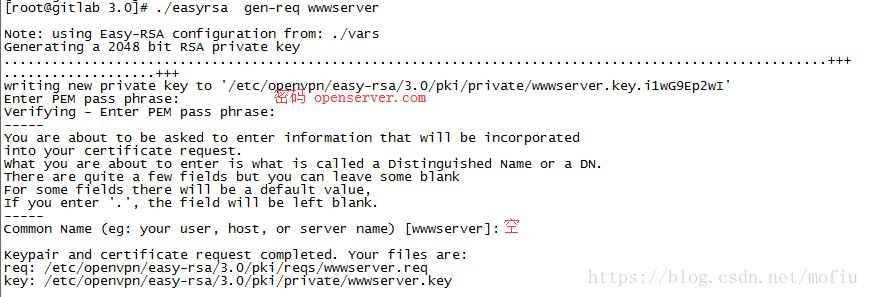
创建服务端证书、密码openserver.com
签发证书,签约服务端证书,给server端证书做签名,首先是对一些信息的确认,可以输入yes,然后输入build-ca时设置的那个密码
./easyrsa sign-req server wwwserver
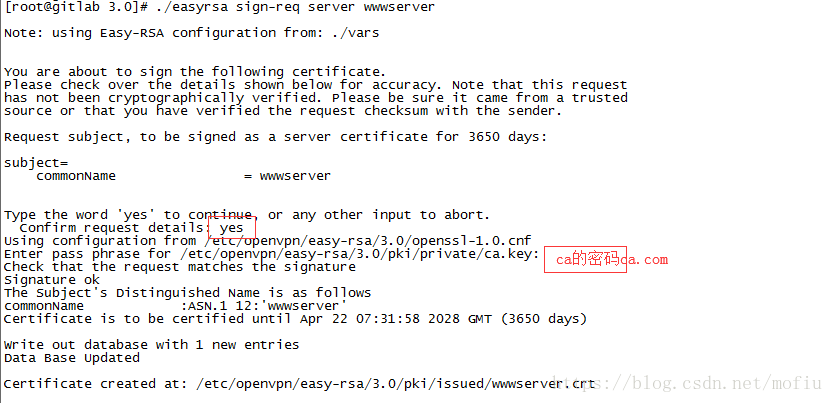
输入yes签发证书,输入ca密码:ca.com
生成windows客户端用户:
./easyrsa build-client-full testname
#注意:生成客户端用户的时候会提示设置密码
#可以直按回车密码为空、也可以设置输入密码(如设置密码,客户端连接时需输入密码)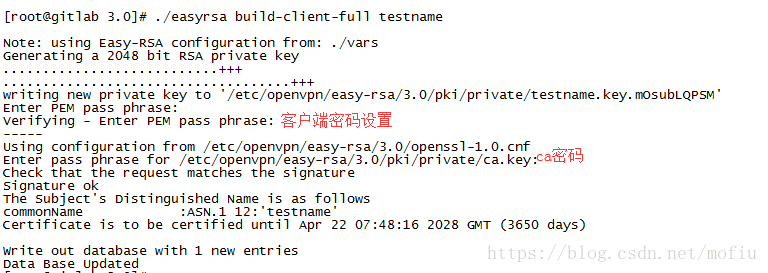
生成客户端证书,并设置密码(客户端连接时用)
[root@gitlab ~]# ll /etc/openvpn/easy-rsa/3.0/pki/private/testname.key
-rw------- 1 root root 1834 Apr 25 15:48 /etc/openvpn/easy-rsa/3.0/pki/private/testname.key
[root@gitlab ~]# ll /etc/openvpn/easy-rsa/3.0/pki/issued/testname.crt
-rw------- 1 root root 4438 Apr 25 15:48 /etc/openvpn/easy-rsa/3.0/pki/issued/testname.crt操作系统设置
vim /etc/sysctl.conf
末尾加入
net.ipv4.ip_forward = 1
保存后执行:sysctl -p
systemctl start firewalld.service
firewall-cmd --state
firewall-cmd --zone=public --list-all
firewall-cmd --add-service=openvpn --permanent
firewall-cmd --add-port=1194/tcp --permanent
firewall-cmd --add-port=1194/udp --permanent
firewall-cmd --add-port=22/tcp --permanent
firewall-cmd --add-source=10.8.0.0 --permanent
firewall-cmd --query-source=10.8.0.0 --permanent
firewall-cmd --add-masquerade --permanent
firewall-cmd --query-masquerade --permanent
firewall-cmd --reload
可以根据自己的需求开放端口启动openvpn
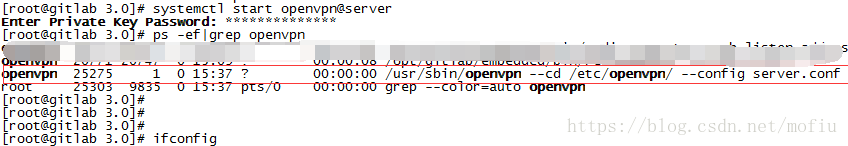
systemctl start openvpn@server
启动时输入服务端证书密码:openserver.com
第一次启动的时候可能会提示,重新执行systemctl start openvpn@server输入密码即可
客户端配置
客户端openvpn版本2.4.5
链接:https://pan.baidu.com/s/13ngQs9WSpQ0ZER5Q9lR-kg 密码:kisi

客户端需要的证书:testname.crt、testname.key、ca.crt、ta.key
get /etc/openvpn/easy-rsa/3.0/pki/private/testname.key
get /etc/openvpn/easy-rsa/3.0/pki/issued/testname.crt
get /etc/openvpn/easy-rsa/3.0/pki/ca.crt
get /etc/openvpn/ta.key
客户端配置文件testname.ovpn(ip换为openvpn服务器外网ip)
client
dev tun
proto udp
resolv-retry infinite
nobind
remote 47.175.155.184 1194
ns-cert-type server
comp-lzo
ca ca.crt
cert testname.crt
key testname.key
tls-auth ta.key 1
keepalive 10 120
persist-key
persist-tun
verb 5
redirect-gateway
route-method exe
route-delay 2
status testname-status.log
log-append testname.log安装OpenVPN 2.4.5 x86_64后,清空config文件夹,将testname.crt、testname.key、ca.crt、ta.key、testname.ovpn放入config目录中,
配置完成后启动,如果有设置密码的话输入密码即可。
备注
1、如果需要创建其他用户的话,按照上面的方式创建客户端证书即可
2、客户端证书生成失败,删除文件即可
rm -rf /etc/openvpn/easy-rsa/3.0/pki/reqs/username.req
rm -rf /etc/openvpn/easy-rsa/3.0/pki/private/username.key
3、删除用户证书
cd /etc/openvpn/easy-rsa/3.0
./easyrsa revoke username
生成CRL文件(撤销证书的列表)
./easyrsa gen-crl
4、服务启停
systemctl stop openvpn@server
systemctl start openvpn@server
参考资料:https://www.jianshu.com/p/5ae8a5fddc1b 。再次感谢文章作者。