PEM文件有以下格式
1.PEM私钥文件格式
-----BEGIN RSA PRIVATE KEY-----
-----END RSA PRIVATE KEY-----生成该密钥的Linux命令 : OpenSSL> genrsa -out privateKey.pem 1024
读取该密钥的Linux Openssl API函数文件读取:
RSA *PEM_read_RSAPrivateKey(FILE *fp, RSA **rsa, pem_password_cb *cb, void *u)
读取该密钥的Linux Openssl API函数内存读取:
RSA *PEM_read_bio_RSAPrivateKey(BIO *bio, RSA **rsa, pem_password_cb *cb, void *u)
2.PEM私钥文件格式(经过口令加密)
-----BEGIN RSA PRIVATE KEY-----
Proc-Type: 4,ENCRYPTED
DEK-Info: DES-EDE3-CBC,FCD22C6C17CF034C
-----END RSA PRIVATE KEY-----3.PEM公钥文件格式
-----BEGIN PUBLIC KEY-----
-----END PUBLIC KEY-----生成该密钥的Linux命令: OpenSSL>rsa -in privateKey.pem -pubout -out publicKey.pem
读取该密钥的Linux Openssl API函数文件读取:
RSA *PEM_read_RSA_PUBKey(FILE *fp, RSA **rsa, pem_password_cb *cb, void *u)
读取该密钥的Linux Openssl API函数内存读取:
RSA *PEM_read_bio_PublicKey(BIO *bio, RSA **rsa, pem_password_cb *cb, void *u)
4.PEM RSAPublicKey公钥文件格式
-----BEGIN RSA PUBLIC KEY-----
-----END RSA PUBLIC KEY-----
生成该密钥的Linux命令: OpenSSL>rsa -in privateKey.pem -RSAPublicKey_out -out publicKey.pem
读取该密钥的Linux Openssl API函数文件读取:
RSA *PEM_read_RSAPublicKey(FILE *fp, RSA **rsa, pem_password_cb *cb, void *u)
读取该密钥的Linux Openssl API函数内存读取:
RSA *PEM_read_bio_RSAPublicKey(BIO *bio, RSA **rsa, pem_password_cb *cb, void *u)
5.RSA加密API
int RSA_public_encrypt(int flen, unsigned char *from, unsigned char *to, RSA *rsa, int padding)
参数说明:
flen: 填充方式加密长度
from: 要加密信息
to: 加密后的信息
padding: 填充方式(RSA_PKCS1_PADDING, RSA_PKCS1_OAEP_PADDING, RSA_SSLV23_PADDING, RSA_NO_PADDING)
注:flen会根据不同的填充方式大小会有变化参考
6.RSA解密API
int RSA_private_decrypt(int flen, unsigned char *from, unsigned char *to, RSA *rsa, int padding)
flen: 解密密钥长度
from: 要解密信息
to: 解密后的信息
padding: 填充方式(RSA_PKCS1_PADDING, RSA_PKCS1_OAEP_PADDING, RSA_SSLV23_PADDING, RSA_NO_PADDING)
注: flen填写的是密钥长度可用RSA_size(rsa)函数得到的
7.RSA编程示例(PEM文件方式)
#include <openssl/rsa.h>
#include <openssl/pem.h>
#define PUBLICKEY "publicKey.pem"
#define PRIVATEKEY "privateKey.pem"
#define PASS "8888" //口令
int main(int argc, char *argv[])
{
FILE *fp = NULL;
RSA *publicRsa = NULL;
RSA *privateRsa = NULL;
if ((fp = fopen(PUBLICKEY, "r")) == NULL) {
printf("public key path error\n");
return -1;
}
if ((publicRsa = PEM_read_RSA_PUBKEY(fp, NULL, NULL, NULL)) == NULL) {
printf("PEM_read_RSA_PUBKEY error \n");
return -1;
}
fclose(fp);
if ((fp = fopen(PRIVATEKEY, "r")) == NULL) {
printf("private key path error\n");
return -1;
}
OpenSSL_add_all_algorithms(); //密钥有经过口令加密需要这个函数
if ((privateRsa = PEM_read_RSAPrivateKey(fp, NULL, NULL, (char *)PASS)) == NULL) {
printf("PEM_read_RSAPrivateKey error\n");
return NULL;
}
fclose(fp);
unsigned char *source = (unsigned char *)"123456789";
int rsa_len = RSA_size(publicRsa);
unsigned char *encryptMsg = (unsigned char *)malloc(rsa_len);
memset(encryptMsg, 0, rsa_len);
int len = rsa_len - 11;
if (RSA_public_encrypt(len, source, encryptMsg, publicRsa, RSA_PKCS1_PADDING) < 0)
printf("RSA_public_encrypt error\n");
else {
rsa_len = RSA_size(privateRsa);
unsigned char *decryptMsg = (unsigned char *)malloc(rsa_len);
memset(decryptMsg, 0, rsa_len);
int mun = RSA_private_decrypt(rsa_len, encryptMsg, decryptMsg, privateRsa, RSA_PKCS1_PADDING);
if (mun < 0)
printf("RSA_private_decrypt error\n");
else
printf("RSA_private_decrypt %s\n", decryptMsg);
}
RSA_free(publicRsa);
RSA_free(privateRsa);
return 0;
}8.RSA编程示例(PEM内存方式)
#include <cstdio>
#include <cstring>
#include <openssl/rsa.h>
#include <openssl/pem.h>
const char *publicKey = "-----BEGIN PUBLIC KEY-----\n\
MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQDnal1HozHfmZ3B1TITmbjCNKOs\n\
49S+urgJ2P0/T36qN5w+r1jGhZKr54QDI5oXEk+9arlKxDW8kufwGjaTV3i3hyGS\n\
jYv4wNXhPeZAyAQ1vlloLMT6oA0PKe9/l8+mAr1QPEW9fMixAc/0UzPVospjkpfr\n\
YULcrKcH2Oaou5DZ0QIDAQAB\n\
-----END PUBLIC KEY-----";
const char *privateKey = "-----BEGIN RSA PRIVATE KEY-----\n\
Proc-Type: 4,ENCRYPTED\n\
DEK-Info: DES-EDE3-CBC,DF3BD9835CA1186D\n\
\n\
pomWi9/hjscwDDzH5CEpcj8nCumOQpl/2Gk2YynA47qfhxt12glNjgWl5Eaevk2L\n\
bG1t85sPqEvYxAe+ZxZdP6fot+sAg4SUUwSvBMwa7s3XjVhHjf/+hOIjb0skHvp/\n\
p0eOoUgytX7FrNNYEpUFI+eiPob79fgQMq/rypGJ//G6GXLMYixWw2+PyPa1x2PQ\n\
WdBaTpZK3gmDqmu6jR3ieKOahVVO4fEGB5etvB5i1aAh0mT4Wu+ejv2LgIRr2xor\n\
r8LkQZvI/TryZ0sNLe7LlC1bz/Hw8hLBDPprhWaUcSEk6MMgh3LKA2y/pGpFdIYN\n\
Ncj/c+YqEsO+I0KOtPQ1fXlXd1hH1H1rkJxuaNanF0UInUuupV3fP+7cvmfyHM4m\n\
aix8ROt1/Ghau41JDZGYmwk2qgKjUw4zz3eYOMQKl6row3pzhDxbvoMp0Qvfje1J\n\
RYpKMy8skG9pY1l4i1CC98aESC2a7FzjUNcY3f5Jt+QznO15xXxxuJZ8+xNqtIh2\n\
U348rlrQ8OxS1YBJCr+wjesdBdQAiY6X1YB9tljPs7AhlTLo78pHtQac521xOA8j\n\
IcbfkuTIrMIwYBOtM6SJHkB1TgPdPWx+haEy79Ct2yDnvpPqOiFz8i8TG8AQY53l\n\
5xKxxJ9CmPqw+Ua3DAWPaxAMaJFteRbl5Lv/2MvxV9Mu3T0W4B3ij+Gg5aw81v5Y\n\
KTH2KxruYAF5Q70QG8CAR8Vkvdczw940y8nb9pvcixmqYcaaeM9DLaTbycn/AeCt\n\
3UM0R0vvu039Ix5uhXUtVMjhTeUnvNObwEcKM8Grv1oPV3zmTJ5hJg==\n\
-----END RSA PRIVATE KEY-----";
---------------------
#define PASS "8888" //口令
int main(int argc, char *argv[])
{
BIO *bio = NULL;
RSA *publicRsa = NULL;
RSA *privateRsa = NULL;
if ((bio = BIO_new_mem_buf((void *)publicKey, -1)) == NULL) {
printf("BIO_new_mem_buf publicKey error\n");
return -1;
}
if ((publicRsa = PEM_read_bio_RSA_PUBKEY(bio, NULL, NULL, NULL)) == NULL) {
printf("PEM_read_bio_RSA_PUBKEY error\n");
return -1;
}
BIO_free_all(bio);
if ((bio = BIO_new_mem_buf((void *)privateKey, -1)) == NULL) {
printf("BIO_new_mem_buf privateKey error\n");
return -1;
}
OpenSSL_add_all_algorithms();//密钥有经过口令加密需要这个函数
if ((privateRsa = PEM_read_bio_RSAPrivateKey(bio, NULL, NULL, (char *)PASS)) == NULL) {
printf("PEM_read_RSAPrivateKey error\n");
return NULL;
}
BIO_free_all(bio);
unsigned char *source = (unsigned char *)"123456789";
int rsa_len = RSA_size(publicRsa);
unsigned char *encryptMsg = (unsigned char *)malloc(rsa_len);
memset(encryptMsg, 0, rsa_len);
int len = rsa_len - 11;
if (RSA_public_encrypt(len, source, encryptMsg, publicRsa, RSA_PKCS1_PADDING) < 0)
printf("RSA_public_encrypt error\n");
else {
rsa_len = RSA_size(privateRsa);
unsigned char *decryptMsg = (unsigned char *)malloc(rsa_len);
memset(decryptMsg, 0, rsa_len);
int mun = RSA_private_decrypt(rsa_len, encryptMsg, decryptMsg, privateRsa, RSA_PKCS1_PADDING);
if (mun < 0)
printf("RSA_private_decrypt error\n");
else
printf("RSA_private_decrypt %s\n", decryptMsg);
}
RSA_free(publicRsa);
RSA_free(privateRsa);
return 0;
}
9.RSA编程示例(PEM文件方式多线程测试样例)
#include <cstdio>
#include <cstring>
#include <pthread.h>
#include <openssl/rsa.h>
#include <openssl/pem.h>
#include <openssl/err.h>
#define PRIKEY "prikey.pem"
#define PUBKEY "pubkey.pem"
RSA *publicRsa = NULL;
RSA *privateRsa = NULL;
void* rsaThreadOne(void* param)
{
unsigned char *source = (unsigned char *)param;
int rsa_len = RSA_size(publicRsa);
unsigned char *encryptMsg = (unsigned char *)malloc(rsa_len);
memset(encryptMsg, 0, rsa_len);
int len = rsa_len - 11;
if (RSA_public_encrypt(len, source, encryptMsg, publicRsa, RSA_PKCS1_PADDING) < 0)
{
printf("rsaThreadOne RSA_public_encrypt error\n");
return 0;
}
rsa_len = RSA_size(privateRsa);
unsigned char *decryptMsg = (unsigned char *)malloc(rsa_len);
memset(decryptMsg, 0, rsa_len);
int mun = RSA_private_decrypt(rsa_len, encryptMsg, decryptMsg, privateRsa, RSA_PKCS1_PADDING);
if ( mun < 0)
{
printf("rsaThreadOne RSA_private_decrypt error\n");
return 0;
}
else
{
printf("rsaThreadOne %s\n", decryptMsg);
}
return 0;
}
void* rsaThreadTwo(void* param)
{
unsigned char *source = (unsigned char *)param;
int rsa_len = RSA_size(publicRsa);
unsigned char *encryptMsg = (unsigned char *)malloc(rsa_len);
memset(encryptMsg, 0, rsa_len);
int len = rsa_len - 11;
if (RSA_public_encrypt(len, source, encryptMsg, publicRsa, RSA_PKCS1_PADDING) < 0)
{
printf("rsaThreadTwo RSA_public_encrypt error\n");
return 0;
}
rsa_len = RSA_size(privateRsa);
unsigned char *decryptMsg = (unsigned char *)malloc(rsa_len);
memset(decryptMsg, 0, rsa_len);
int mun = RSA_private_decrypt(rsa_len, encryptMsg, decryptMsg, privateRsa, RSA_PKCS1_PADDING);
if ( mun < 0)
{
printf("rsaThreadTwo RSA_private_decrypt error\n");
return 0;
}
else
{
printf("rsaThreadTwo %s\n", decryptMsg);
}
return 0;
}
int main(int argc, char *argv[])
{
FILE *fp = NULL;
if ((fp = fopen(PUBKEY, "r")) == NULL)
{
printf("pubkey_path error\n");
return -1;
}
if ((publicRsa = PEM_read_RSA_PUBKEY(fp, NULL, NULL, NULL)) == NULL)
{
printf("PEM_read_RSA_PUBKEY error\n");
return -1;
}
fclose(fp);
if ((fp = fopen(PRIKEY, "r")) == NULL)
{
printf("prikey_path error\n");
return -1;
}
OpenSSL_add_all_algorithms();//密钥有经过口令加密需要这个函数
if ((privateRsa = PEM_read_RSAPrivateKey(fp, NULL, NULL, (char *)"8888")) == NULL)
{
printf("PEM_read_RSAPrivateKey error\n");
return NULL;
}
fclose(fp);
pthread_t tid1 ;
pthread_t tid2 ;
pthread_create(&tid1, NULL, rsaThreadOne, (void *)"123456789");
pthread_create(&tid2, NULL, rsaThreadTwo, (void *)"987654321");
pthread_join(tid1,NULL);
pthread_join(tid2,NULL);
return 0;
}
10.相应参考文章、文档
嗨!大佟!博客
wjlkoorey的博客
需要翻墙才能访问的openssl github
转载地址:https://blog.csdn.net/aqlick12/article/details/78480505
在实际的编译过程中,出现了如下的错误:
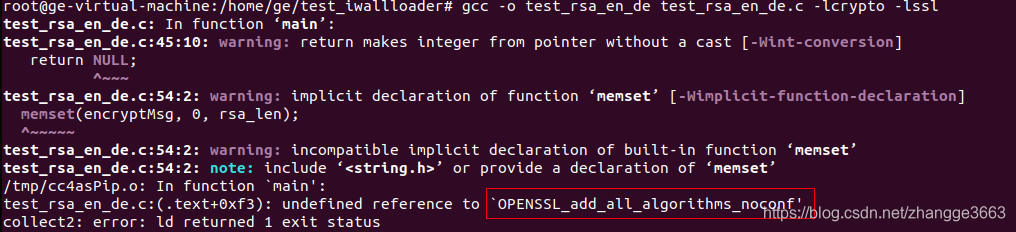
参考了https://bugs.php.net/bug.php?id=15780链接中的第一条回复,发现我的系统中有两个openssl版本,所以需要确保include的东西和link的东西版本保持一致。故加了-I/usr/local/openssl/include之后,问题消失,如下:
