版权声明:本文为博主原创文章,未经博主允许不得转载。 https://blog.csdn.net/Hannah_zh/article/details/84104324
一、Docker证书
1、创建certs证书,生成服务器私钥
[root@foundation51 docker]# cd /tmp/docker/
[root@foundation51 docker]# mkdir certs
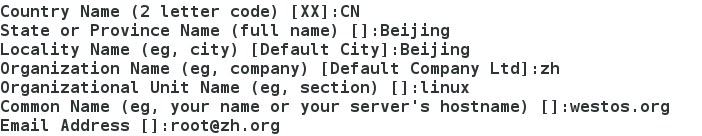
[root@foundation51 docker]# openssl req -newkey rsa:4096 -nodes -sha256 -keyout certs/westos.org.key -x509 -days 365 -out certs/westos.org.crt
- 填写证书信息
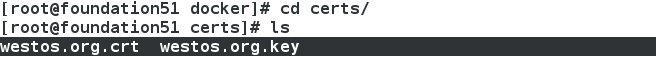
- 查看证书、私钥
2、启动仓库
[root@foundation51 docker]# docker run -d \
> --restart=always \
> --name registry \
> -v `pwd`/certs:/certs \
> -e REGISTRY_HTTP_ADDR=0.0.0.0:443 \
> -e REGISTRY_HTTP_TLS_CERTIFICATE=/certs/westos.org.crt \
> -e REGISTRY_HTTP_TLS_KEY=/certs/westos.org.key \
> -p 443:443 \
> registry:2.3.1
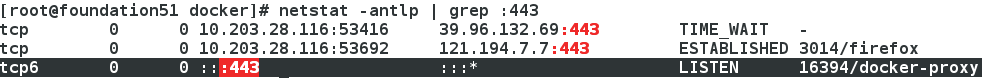
- 查看443端口(https)
3、上传westos.org/rhel7
[root@foundation51 docker]# docker tag rhel7 westos.org/rhel7
[root@foundation51 ~]# cd /etc/docker/
[root@foundation51 docker]# mkdir certs.d
[root@foundation51 docker]# cd certs.d/
[root@foundation51 certs.d]# mkdir westos.org
[root@foundation51 certs.d]# cd westos.org/
[root@foundation51 westos.org]# cp /tmp/docker/certs/westos.org.crt ./ca.crt
[root@foundation51 westos.org]# docker push westos.org/rhel7
4、更新CA证书
[root@foundation51 ~]# cd /etc/pki/ca-trust/source/anchors/
[root@foundation51 anchors]# cp /tmp/docker/certs/westos.org.crt .
[root@foundation51 anchors]# ls
westos.org.crt
[root@foundation51 anchors]# update-ca-trust
5、域名解析
[root@foundation51 ~]# vim /etc/hosts
172.25.51.250 westos.org
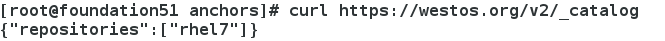
6、测试:访问 https
[root@foundation51 anchors]# curl https://westos.org/v2/_catalog
二、Docker生产环境安全性——证书验证仓库客户端
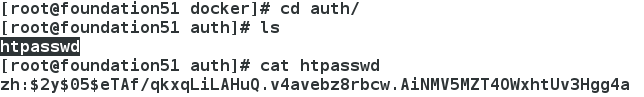
1、生成鉴权密码文件
[root@foundation51 ~]# cd /tmp/docker/
[root@foundation51 docker]# mkdir auth
[root@foundation51 docker]# docker run --entrypoint htpasswd registry:2.3.1 -Bbn zh westos > auth/htpasswd ##用户zh,密码westos
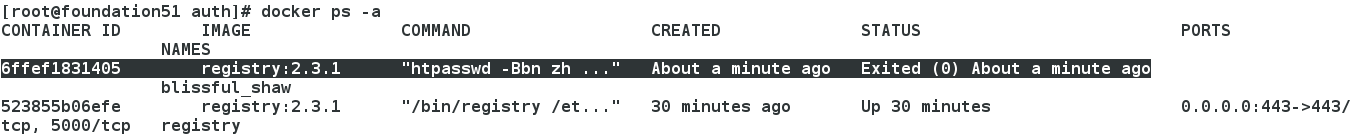
2、关闭之前的仓库,防止冲突
[root@foundation51 docker]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
523855b06efe registry:2.3.1 "/bin/registry /et..." 34 minutes ago Up 34 minutes 0.0.0.0:443->443/tcp, 5000/tcp registry
[root@foundation51 docker]# docker rm -f registry
registry
3、启动Registry
[root@foundation51 docker]# docker run -d --restart=always --name registry -v `pwd`/auth:/auth -e "REGISTRY_AUTH=htpasswd" -e "REGISTRY_AUTH_HTPASSWD_REALM=Registry Realm" -e REGISTRY_AUTH_HTPASSWD_PATH=/auth/htpasswd -v `pwd`/certs:/certs -e REGISTRY_HTTP_ADDR=0.0.0.0:443 -e REGISTRY_HTTP_TLS_CERTIFICATE=/certs/westos.org.crt -e REGISTRY_HTTP_TLS_KEY=/certs/westos.org.key -p 443:443 registry:2.3.1
登陆验证,curl无法看到
[root@foundation51 docker]# curl https://westos.org/v2/_catalog

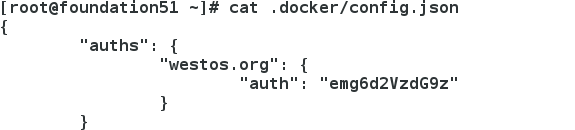
4、用户登录
登录认证成功后,才可进行push等操作
[root@foundation51 docker]# docker login westos.org
Username (zh): zh
Password:
Login Succeeded
5、上传成功
完成registry服务器的搭建,可以尝试pull image到registry:
[root@foundation51 docker]# docker tag nginx westos.org/nginx
[root@foundation51 docker]# docker push westos.org/nginx
认证成功后,认证信息保存在当前文件下
三、docker安全
1、一般情况,容器中操作权限受限
[root@foundation51 ~]# docker run -it --name vm1 ubuntu bash
root@1afd45516ffe:/# ip addr add 172.17.0.120/24 dev eth0
2、授予所有权限
[root@foundation51 ~]# docker run -it --name vm2 --privileged=true ubuntu bash
root@1db0e5a2cf8a:/# ip addr add 172.17.0.120/24 dev eth0
3、授予指定权限
[root@foundation51 ~]# docker run -it --name vm3 --cap-add=NET_ADMIN ubuntu bash
root@f45481c6757b:/# ip link set down eth0
root@f45481c6757b:/# ip link set up eth0
4、查看相应权限
[root@foundation51 ~]# docker inspect -f {{.HostConfig.Privileged}} vm1
false
[root@foundation51 ~]# docker inspect -f {{.HostConfig.Privileged}} vm2
true
[root@foundation51 ~]# docker inspect -f {{.HostConfig.CapAdd}} vm3
[NET_ADMIN]
[root@foundation51 ~]# docker inspect -f {{.HostConfig.CapAdd}} vm2
[]