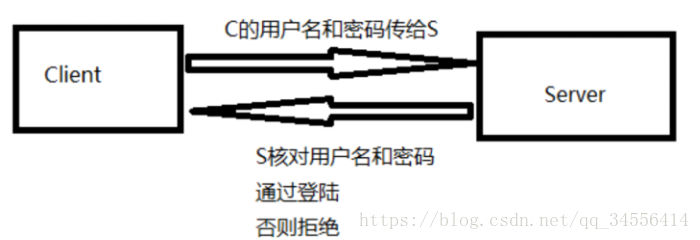
密码登入:
非对称:A --B
假设B有数据要发给A
首先B需要获取A的公钥
B使用获取到的A的公钥对数据进行加密
B将加密的信息,传递给A,在网络传输过程中是安全的
只能使用A的私钥进行解密
下面是对ssh原理进行的实验得出密匙登入的原理:
密钥登录client: 虚拟机1(root) test用户
server:虚拟机2上有root用户,不需要使用密码,密钥---基于用户来验证
[root@localhost ~]# useradd test
[root@localhost ~]# passwd test
Changing password for user test.
New password:
BAD PASSWORD: The password is shorter than 8 characters
Retype new password:
passwd: all authentication tokens updated successfully.
[root@localhost ~]# su - test
1.在客户端生成密钥对
[test@localhost ~]$ ssh-keygen
Generating public/private rsa key pair.
Enter file in which to save the key (/home/test/.ssh/id_rsa):
Created directory '/home/test/.ssh'.
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /home/test/.ssh/id_rsa.
Your public key has been saved in /home/test/.ssh/id_rsa.pub.
The key fingerprint is:
17:3a:6c:50:bd:36:eb:00:ce:2f:67:2b:b2:96:f4:c9 [email protected]
The key's randomart image is:
+--[ RSA 2048]----+
| .. |
| . . |
| . .. |
| .o .+. |
| o .S..o |
| . o..o. |
| . + o o |
| + E + . |
| ..o =.. |
+-----------------+
[test@localhost ~]$ ls .ssh/
id_rsa id_rsa.pub --id_rsa公钥,id_rsa.pub私钥
[test@localhost ~]$ cat .ssh/id_rsa.pub --查看公钥里面的内容
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDOwVswfEANULfO+AeDI8wxQC9kp11XkjDDl3/1NYUhJ+UUXFcCL0iPXszY8Ofrw3u12xxUoTuczj6IcN6SCtIbjEASVfpB8WE2QhCTgtO++SbWd38l1qLIaOJ5kduUc9S4u1tVjplQ6ob98/m2JXQEnWomSVBXYp8F9BdfhKWkylVQZQ7TFmiKx21LH6MHVcSmihXRlv7suoucszpCVqZnYPktkx5CcxnVwfQiRjSzGTSZzdt0ZbMzTDipPL5ro5X+wAlFGbw6w1iEawCI8Vt+CMRSt6EKgpKGH9ulOM5Q4JBgXOC9b0RXtomx4kHRpcrWsDWaMg6G0Am6yPF22DBF [email protected]
[test@localhost ~]$ cat .ssh/id_rsa --查看私钥里面的内容
-----BEGIN RSA PRIVATE KEY-----
MIIEowIBAAKCAQEAzsFbMHxADVC3zvgHgyPMMUAvZKddV5Iww5d/9TWFISflFFxX
Ai9Ij17M2PDn68N7tdscVKE7nM4+iHDekgrSG4xAElX6QfFhNkIQk4LTvvkm1nd/
JdaiyGjieZHblHPUuLtbVY6ZUOqG/fP5tiV0BJ1qJklQV2KfBfQXX4SlpMpVUGUO
0xZoisdtSx+jB1XEpooV0Zb+7LqLnLM6QlamZ2D5LZMeQnMZ1cH0IkY0sxk0mc3b
dGWzM0w4qTy+a6OV/sAJRRm8OsNYhGsAiPFbfgjEUrehCoKShh/bpTjOUOCQYFzg
vW9EV7aJseJB0aXK1rA1mjIOhtAJusjxdtgwRQIDAQABAoIBADkFBjsW6StC6Y5A
xQGbq8KhavCdX5a5EI3AiF99xRthv0GgPbayh5ZSlLf3qF5S6Rk8NlH4rVIPZxuF
1Tv9k/hY84qa/4uUIDUwfxXPbMosOFPJXN14ligjFOJmIWKNl0rjEMtFqm6wX05G
LMXZCmgDabTpXyjaX/TqXk/Pa0dIrqyw6tWalvpEHljzIWbISmoajZuQ8x+xqh8V
x9OoDOBLQ43cy0rz12s8mWpE64fqV3h6GyyUwRg9Y+JDK4brvJRYSZeo4Iscxi6D
HwFE6+AZp2XF/wO61s+8LJ+484NpH8l4a9WANIVcJ4XFMXdSvmvuHnXSrd9KrrSE
VrPrREECgYEA8vFW0K+WzNxkRjFPfGd6XLUBh7BqqbR2aNVQFDVMq4KFnsnzIfzM
RrsPhFY0rNELNn//FBXU0arT/SHGCh4QAFbC8TdVEQ0Zxmoy/rgSWyb4vw8SdEQc
3EViCi5aDQJ5B6m74b9qG1hbIqK6pEl0WpCMnwlK941BwEIvD2Yei60CgYEA2d4c
yB3tDymKt966clisVhddq7PKem8DUvRCnX1cdq6xFwJeus9IAW8AN1PBOUoTqrhP
DYcwdQXXqvKy0bwJqaeUbEYMnm5RBwWpm/FkhfLfh7kEQsLqQDr6GFeooZLkeMje
gYdailauwmPCowx0GRImRhZIdRSvqEvT/qxGSfkCgYBSyZU5Bi0QYKY3GUSp8yVK
hFAiKice76VOMirYyBT5eUAJjW4yDdCa5dHy2eGXZqE4kEOfV5UvYdRdtW2kMvxm
8Sn7Q0zUw68d40C/doCi2VP436z9O9zN30L6jzMWrdoKl3e0BSOmb+SWl/ecVn+1
AP86jtMiKtvWJXed+sG7/QKBgDwUtYk2P36T7S5BnNcVvwjKzskf/rF+1cLVm11F
Ce+swydePvNzYB8NFlkrnriGxh+pThuj8WgEIXKCFXAjU+LWVOb69lXmhC/Uju5z
Rk5uKNiL3DHxAJqP6RI3ckiEcr8gXcQIqJ5Hw0/WJQHD2GxlheqEEJ1BBCP8LU0p
AwU5AoGBAOhb0wJYeuOYSQzsDDGXySIYavjh0G+Pa40kyML/nS8CEmMcqSnffbfp
P60FFCu+pNiDHAX17GnCUIgMil0WGJvg+9u+/SKPXOFhax0zNgVdYtvseZtqRTb1
ZxGUBQJIvTWKxuqWXPfPMB7ZFXlA6cTBxDJQwq6Xp9029G8u/m+b
-----END RSA PRIVATE KEY-----
2.将客户端的公钥发送给服务器
[test@localhost ~]$ ssh-copy-id -i ~/.ssh/id_rsa.pub root@desktop0
The authenticity of host 'desktop0 (172.25.0.10)' can't be established.
ECDSA key fingerprint is eb:24:0e:07:96:26:b1:04:c2:37:0c:78:2d:bc:b0:08.
Are you sure you want to continue connecting (yes/no)? yes
/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed
/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys
root@desktop0's password:
Number of key(s) added: 1
Now try logging into the machine, with: "ssh 'root@desktop0'"
and check to make sure that only the key(s) you wanted were added.
[test@localhost ~]$ ls .ssh/
id_rsa id_rsa.pub known_hosts
[test@localhost ~]$ cat .ssh/known_hosts
desktop0,172.25.0.10 ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBHX+o9KAnlfw2dE7CsmM4hqfv1udM79a5NWC2BuWlmfKSwfYLptPQMJF8bnqaz0EjDlxCxRu/aito+GphPLzp/k=
3.在服务端查看产生的authorized_keys的内容
[test@localhost ~]$ ssh root@desktop0
Last login: Mon Apr 23 21:36:44 2018 from 172.25.0.250
[root@desktop0 ~]# ls .ssh/
authorized_keys
[root@desktop0 ~]# cat .ssh/authorized_keys
ssh-rsa AAAAB3NzaC1yc2EAAAADAQABAAABAQDOwVswfEANULfO+AeDI8wxQC9kp11XkjDDl3/1NYUhJ+UUXFcCL0iPXszY8Ofrw3u12xxUoTuczj6IcN6SCtIbjEASVfpB8WE2QhCTgtO++SbWd38l1qLIaOJ5kduUc9S4u1tVjplQ6ob98/m2JXQEnWomSVBXYp8F9BdfhKWkylVQZQ7TFmiKx21LH6MHVcSmihXRlv7suoucszpCVqZnYPktkx5CcxnVwfQiRjSzGTSZzdt0ZbMzTDipPL5ro5X+wAlFGbw6w1iEawCI8Vt+CMRSt6EKgpKGH9ulOM5Q4JBgXOC9b0RXtomx4kHRpcrWsDWaMg6G0Am6yPF22DBF [email protected]
可以看到id_rsa.pub 和 authorized_keys文件内容一致
总结如下:
1.在虚拟机1上test上生成密钥对,A-G,A-S2.
2.虚拟机1会把A-G公钥发给 虚拟机2
3.第一次虚拟机1公钥传递给虚拟机2的时候,需要输入密码
4.以后登录就不要
①虚拟机1会把A-G发给服务器
②服务器收到之后 A-G,会和之前收到的公钥信息进行
①公钥不一致,直接拒绝
②公钥一致,不能直接进行登录
①服务器会生成随机的字符串,使用保存在本地的公钥对字符串进行加密
②虚拟机使用自己的私钥进行解密
①解密失败,直接不能登录
②解密成功,将解密的信息发给服务器(字符串)
③将收到的字符串的信息 和原先自己生成的字符串进行对比
①比对失败,拒绝
②比对成功,允许登录