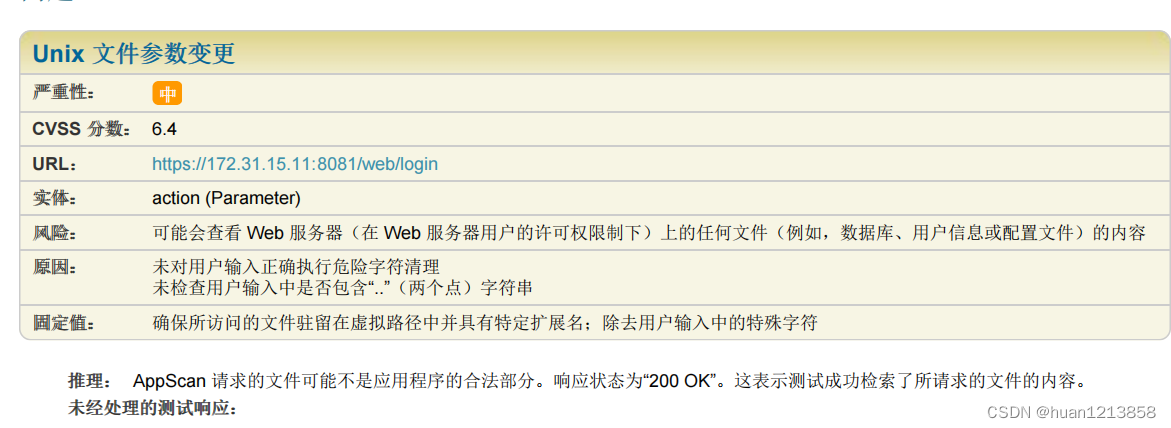
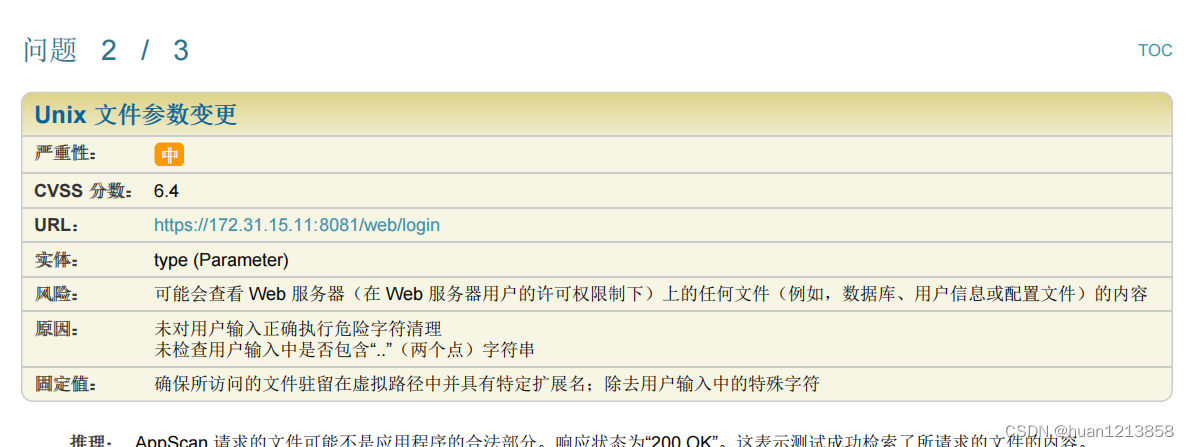
原因:未对用户输入正确执行危险字符清理
未检查用户输入中是否包含“…”(两个点)字符串,比如 url 为 /login?action=…/webapps/RTJEKSWTN26635&type=randomCode
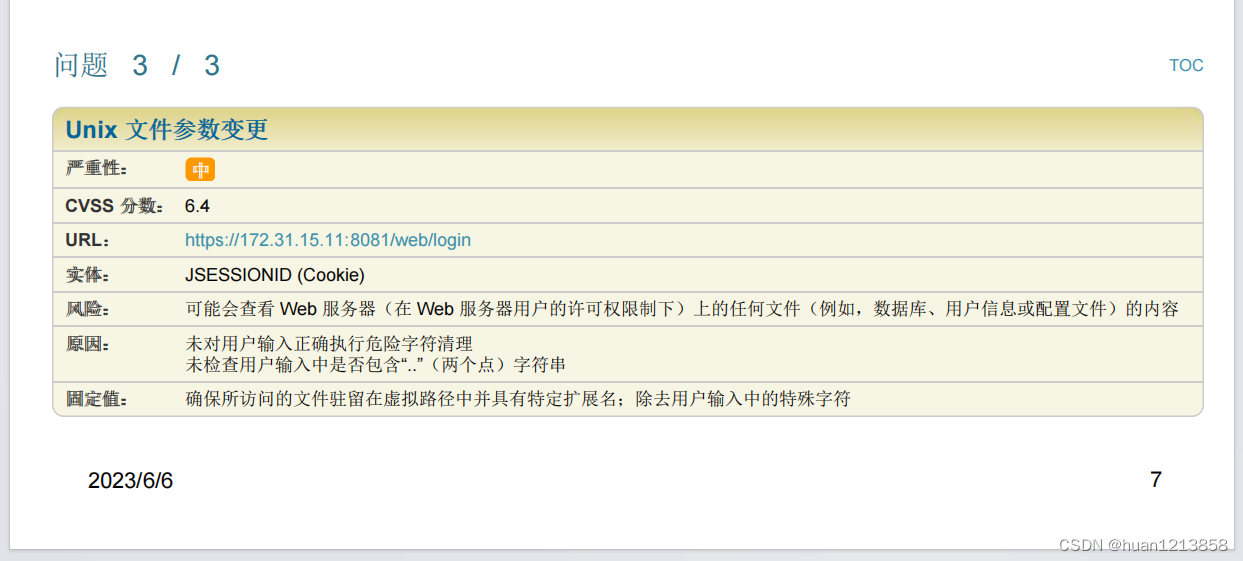
cookie为Cookie: JSESSIONID=…/webapps/RTJEKSWTN26241;
测试返回为200
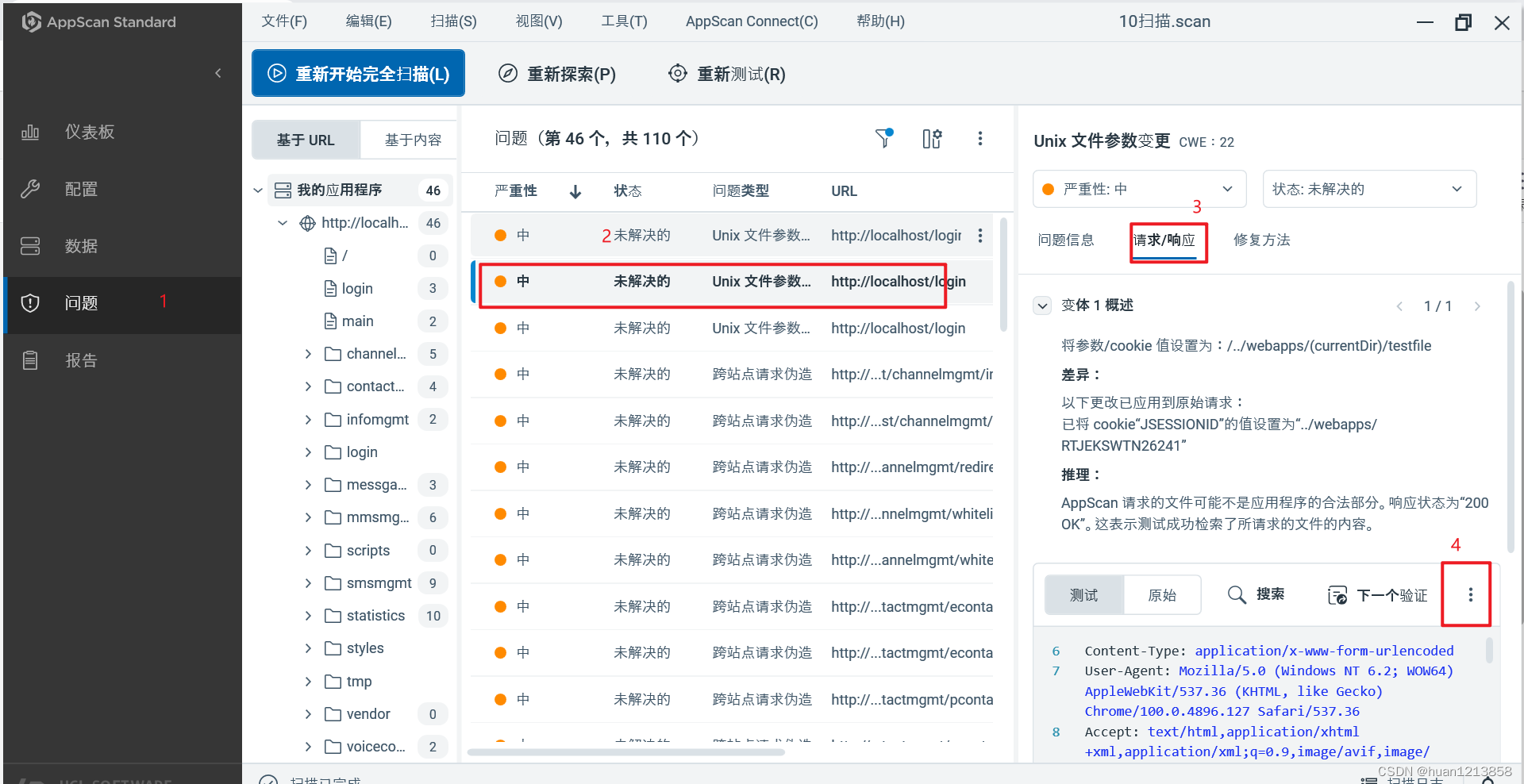
使用AppScan扫描之后可以通过这样的方式进行指定问题手动测试
解决办法:使用过滤器过滤参数以及cookie中的…/
package com.xuanwu.web.frontkit.filter;
import com.alibaba.fastjson.JSON;
import org.slf4j.Logger;
import org.slf4j.LoggerFactory;
import org.springframework.http.HttpStatus;
import javax.servlet.*;
import javax.servlet.http.HttpServletRequest;
import javax.servlet.http.HttpServletResponse;
import java.io.IOException;
import java.io.PrintWriter;
import java.util.Enumeration;
import java.util.HashMap;
import java.util.Map;
import java.util.regex.Matcher;
import java.util.regex.Pattern;
public class InjectFilter implements Filter {
private static Logger log = LoggerFactory.getLogger(InjectFilter.class);
private static final String REG_EXP = "\\.\\./";
@Override
public void init(FilterConfig filterConfig) throws ServletException {
}
public void doFilter(ServletRequest request, ServletResponse response,
FilterChain filterchain) throws IOException, ServletException {
//判断是否有注入攻击字符
HttpServletRequest req = (HttpServletRequest) request;
boolean flag = injectInput(req, response);
if (!flag) {
return;
} else {
filterchain.doFilter(request, response);
}
}
@Override
public void destroy() {
}
/**
* 判断request中是否含有注入攻击字符
*
* @param request
* @return
*/
public boolean injectInput(ServletRequest request, ServletResponse response) throws IOException {
Enumeration e = request.getParameterNames();
String attributeName;
String attributeValues[];
HttpServletRequest req = (HttpServletRequest) request;
String cookie = req.getHeader("Cookie");
if (!isSpecialChar(cookie, response)){
return false;
}
while (e.hasMoreElements()) {
attributeName = (String) e.nextElement();
//不对密码信息进行过滤,一般密码中可以包含特殊字符
if (attributeName.equals("username") || attributeName.equals("password")) {
continue;
}
attributeValues = request.getParameterValues(attributeName);
for (int i = 0; i < attributeValues.length; i++) {
if (attributeValues[i] == null || attributeValues[i].equals(""))
continue;
boolean flag = isSpecialChar(attributeValues[i], response);
if (!flag){
return flag;
}
}
}
return true;
}
/**
* 判断字符串中是否含有注入攻击字符
*/
private boolean isSpecialChar(String value, ServletResponse servletResponse) throws IOException {
Pattern pattern = Pattern.compile(REG_EXP);
if (value == null) {
return true;
}
Matcher matcher = pattern.matcher(value);
if (matcher.find()) {
log.info("入参中有非法字符: " + value);
HttpServletResponse response = (HttpServletResponse) servletResponse;
Map<String, Object> responseMap = new HashMap<>();
// 匹配到非法字符,立即返回
responseMap.put("code", 500);
responseMap.put("msg", "入参中有非法字符");
response.setContentType("application/json;charset=UTF-8");
response.setStatus(HttpStatus.INTERNAL_SERVER_ERROR.value());
PrintWriter writer = response.getWriter();
writer.write(JSON.toJSONString(responseMap));
writer.flush();
writer.close();
return false;
}
return true;
}
}