iptables是什么?
1,IPTABLES 是与最新的3.5版本Linux内核集成的IP信息包过滤系统。如果
Linux系统连接到因特网或LAN服务器或连接LAN和因特网的代理服务器,
则该系统有利于在Linux系统上更好地控制IP信息包过滤和防火墙配置。
2,防火墙在做信息包过滤决定时,有一套遵循和组成的规则,这些规则存储
在专用的信息包过滤表中,而这些表集成在 Linux 内核中。在信息包过
滤表中,规则被分组放在我们所谓的链(chain)中。而netfilter/iptables
IP信息包过滤系统是一款功能强大的工具,可用于添加、编辑和移除规则。
3,虽然 netfilter/iptables IP 信息包过滤系统被称为单个实体,
但它实际上由两个组件netfilter和iptables组成。netfilter 组件
也称为内核空间(kernelspace),是内核的一部分,由一些信息包过
滤表组成,这些表包含内核用来控制信息包过滤处理的规则集。
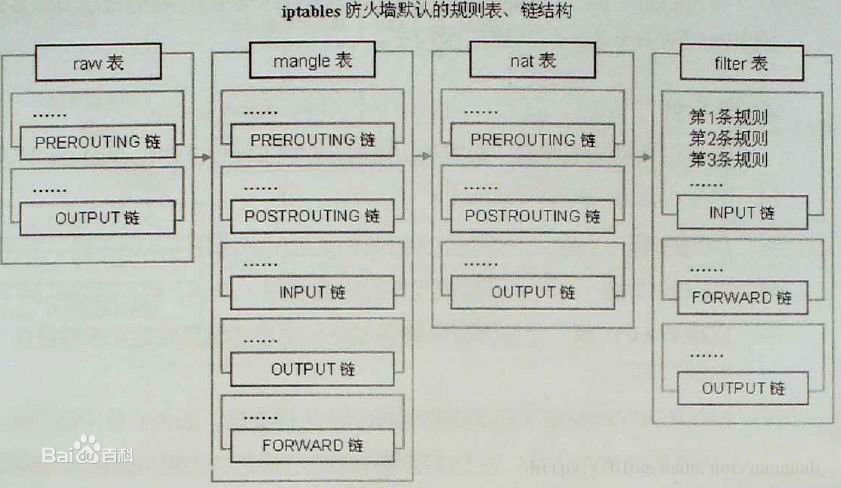
iptables 组件是一种工具,也称为用户空间(userspace),它使插入、修改和除去信息包过滤表中的规则变得容易。iptables默认的防火墙,链结构:
iptables的表名,链结构:
表名包括:
raw:高级功能,如:网址过滤。
mangle:数据包修改(QOS),用于实现服务质量。
net:地址转换,用于网关路由器。
filter:包过滤,用于防火墙规则。
规则链名包括:
INPUT链:处理输入数据包。
OUTPUT链:处理输出数据包。
PORWARD链:处理转发数据包。
PREROUTING链:用于目标地址转换(DNAT)。
POSTOUTING链:用于源地址转换(SNAT)。
动作包括:
accept:接收数据包。
DROP:丢弃数据包。
REDIRECT:重定向、映射、透明代理。
SNAT:源地址转换。
DNAT:目标地址转换。
MASQUERADE:IP伪装(NAT),用于ADSL。
LOG:日志记录。iptables的参数配置:
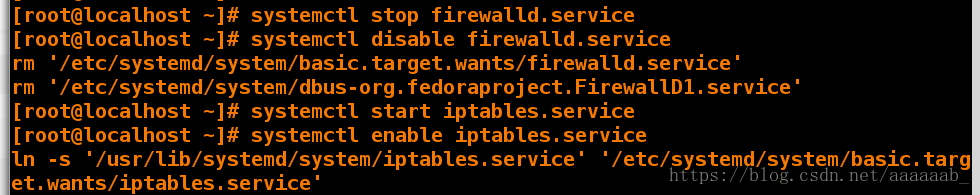
[root@desktop Desktop]# systemctl stop firewalld 关闭防火墙
[root@desktop Desktop]# systemctl disable firewalld 开机自动关闭防火墙
rm '/etc/systemd/system/basic.target.wants/firewalld.service'
rm '/etc/systemd/system/dbus-org.fedoraproject.FirewallD1.service'
[root@desktop Desktop]# systemctl start iptables.service 开启iptables服务
[root@desktop Desktop]# systemctl enable iptables.service 开机自动启动iptables服务
ln -s '/usr/lib/systemd/system/iptables.service' '/etc/systemd/system/basic.target.wants/iptables.service'[root@desktop Desktop]# iptables -nL 查看iptables策略信息
Chain INPUT (policy ACCEPT)
target prot opt source destination
ACCEPT all -- 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED
ACCEPT icmp -- 0.0.0.0/0 0.0.0.0/0
ACCEPT all -- 0.0.0.0/0 0.0.0.0/0
ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:22
REJECT all -- 0.0.0.0/0 0.0.0.0/0 reject-with icmp-host-prohibited
Chain FORWARD (policy ACCEPT)
target prot opt source destination
REJECT all -- 0.0.0.0/0 0.0.0.0/0 reject-with icmp-host-prohibited
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
[root@desktop Desktop]# iptables -F 刷新iptables
[root@desktop Desktop]# iptables -nL 查看iptables策略信息
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination [root@desktop Desktop]# service iptables save 保存
iptables: Saving firewall rules to /etc/sysconfig/iptables:[ OK ]
[root@desktop Desktop]# vim /etc/sysconfig/iptables 查看保存的策略文件
[root@desktop Desktop]# cd
iptables读取策略从上到下依次读取满足就执行,保证速度快
-t指定表
-I指定添加策略的位置
-n不做解析,显示IP
-L显示所有的策略信息
-I插入
-A添加
-R修改策略信息
-F刷新
[root@desktop Desktop]# systemctl start httpd 首先打开阿帕其服务才可以进行网页测试[root@desktop Desktop]# iptables -nL 查看所有策略均允许,在真机和server虚拟机测试可以看到阿帕其测试界面
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination 真机测试:
虚拟机测试:
[root@desktop Desktop]# iptables -t filter -nL 查看filter表策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
[root@desktop Desktop]# iptables -t nat -nL 查看nat表策略
Chain PREROUTING (policy ACCEPT)
target prot opt source destination
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
Chain POSTROUTING (policy ACCEPT)
target prot opt source destination
[root@desktop Desktop]# iptables -t mangle -nL 查看mangle表策略
Chain PREROUTING (policy ACCEPT)
target prot opt source destination
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
Chain POSTROUTING (policy ACCEPT)
target prot opt source destination [root@desktop Desktop]# iptables -P INPUT DROP 设置为丢弃状态
[root@desktop Desktop]# iptables -nL
Chain INPUT (policy DROP)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination 用真机和虚拟机测试一直转圈,因为丢弃状态不返回值 真机测试:
虚拟机测试:
[root@desktop Desktop]# iptables -P INPUT ACCEPT 重新改到接受
[root@desktop Desktop]# iptables -nL 查看策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
[root@desktop Desktop]# iptables -A INPUT -p tcp --dport 80 -j REJECT 将80端口设置为拒绝
[root@desktop Desktop]# iptables -nL 查看策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
REJECT tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:80 reject-with icmp-port-unreachable
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
[root@desktop Desktop]# iptables -D INPUT 1 删除策略 [root@desktop Desktop]# iptables -A INPUT -s 172.25.254.84 -p tcp --dport 80 -j ACCEPT 设置84主机可以访问,用真机和虚拟机测试发现均可以连接,80端口为http的端口
[root@desktop Desktop]# iptables -nL 查看策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
ACCEPT tcp -- 172.25.254.84 0.0.0.0/0 tcp dpt:80
Chain FORWARD (policy ACCEPT
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination 真机测试:
虚拟机测试:
[root@desktop Desktop]# iptables -A INPUT -p tcp --dport 80 -j REJECT 拒绝其他用户访问,iptables从上到下读取,不拒绝的话其他用户还可以访问
[root@desktop Desktop]# iptables -nL 查看策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
ACCEPT tcp -- 172.25.254.84 0.0.0.0/0 tcp dpt:80
REJECT tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:80 reject-with icmp-port-unreachable
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination 真机测试:
虚拟机测试不可以访问:
[root@desktop Desktop]# iptables -D INPUT 2 删除策略
[root@desktop Desktop]# iptables -R INPUT 1 -s 172.25.254.21 -p tcp --dport 22 -j ACCEPT 允许21连接ssh服务
[root@desktop Desktop]# iptables -A INPUT -p tcp --dport 22 -j REJECT 拒绝其他主机连接
[root@desktop Desktop]# iptables -nL 用真机可以连接,其他主机无法连接
[root@desktop Desktop]# iptables -F 刷新
[root@desktop Desktop]# iptables -nL 查看策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination 真机测试可以使用ssh连接:
虚拟机测试不可以使用ssh连接:
iptables的常规配置:
在desktop(双网卡):
[root@desktop Desktop]# iptables -F 刷新
[root@desktop Desktop]# iptables -nL 查看策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination [root@desktop Desktop]# iptables -N westos 添加一行
[root@desktop Desktop]# iptables -nL 查看策略多出来一行
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
Chain westos (0 references)
target prot opt source destination [root@desktop Desktop]# iptables -E westos WESTOS 更改名字为大写
[root@desktop Desktop]# iptables -nL 查看策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
Chain WESTOS (0 references)
target prot opt source destination [root@desktop Desktop]# iptables -X WESTOS 删除WESTOS表
[root@desktop Desktop]# iptables -nL 查看策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination [root@desktop Desktop]# iptables -A INPUT -p tcp --dport 22 -j ACCEPT 允许访问22端口
[root@desktop Desktop]# iptables -A INPUT -p tcp --dport 53 -j ACCEPT 允许访问53端口
[root@desktop Desktop]# iptables -A INPUT -p tcp --dport 80 -j ACCEPT 允许访问80端口
[root@desktop Desktop]# iptables -A INPUT -p tcp --dport 3260 -j ACCEPT 允许访问3260端口
[root@desktop Desktop]# iptables -A INPUT -i lo -j ACCEPT 允许访问回环端口
[root@desktop Desktop]# iptables -nL 查看策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:22
ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:53
ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:80
ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 tcp dpt:3260
ACCEPT all -- 0.0.0.0/0 0.0.0.0/0
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination [root@desktop Desktop]# iptables -F 刷新策略
[root@desktop Desktop]# iptables -nL 查看策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
[root@desktop Desktop]# iptables -A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT 将已经建立的和正在进行的设置允许访问
[root@desktop Desktop]# iptables -nL 查看策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
ACCEPT all -- 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination [root@desktop Desktop]# iptables -A INPUT -m state --state NEW -p tcp --dport 22 -j ACCEPT 允许22端口
[root@desktop Desktop]# iptables -A INPUT -m state --state NEW -p tcp --dport 53 -j ACCEPT 允许3端口
[root@desktop Desktop]# iptables -A INPUT -m state --state NEW -p tcp --dport 80 -j ACCEPT 允许80端口
[root@desktop Desktop]# iptables -A INPUT -m state --state NEW -p tcp --dport 443 -j ACCEPT 允许443端口
[root@desktop Desktop]# iptables -A INPUT -m state --state NEW -p tcp --dport 3260 -j ACCEPT 允许3260端口
[root@desktop Desktop]# iptables -A INPUT -m state --state NEW -i lo -j ACCEPT 允许回环接口[root@localhost ~]# iptables -A INPUT -j REJECT 拒绝其他
[root@localhost ~]# iptables -nL 查看策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
ACCEPT all -- 0.0.0.0/0 0.0.0.0/0 state RELATED,ESTABLISHED
ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:22
ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:53
ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:80
ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:443
ACCEPT tcp -- 0.0.0.0/0 0.0.0.0/0 state NEW tcp dpt:3260
ACCEPT all -- 0.0.0.0/0 0.0.0.0/0 state NEW
REJECT all -- 0.0.0.0/0 0.0.0.0/0 reject-with icmp-port-unreachable
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination [root@localhost ~]# service iptables save 保存策略
iptables: Saving firewall rules to /etc/sysconfig/iptables:[ OK ]
[root@localhost ~]# cat /etc/sysconfig/iptables 查看策略文件
-A INPUT -m state --state RELATED,ESTABLISHED -j ACCEPT
-A INPUT -p tcp -m state --state NEW -m tcp --dport 22 -j ACCEPT
-A INPUT -p tcp -m state --state NEW -m tcp --dport 53 -j ACCEPT
-A INPUT -p tcp -m state --state NEW -m tcp --dport 80 -j ACCEPT
-A INPUT -p tcp -m state --state NEW -m tcp --dport 443 -j ACCEPT
-A INPUT -p tcp -m state --state NEW -m tcp --dport 3260 -j ACCEPT
-A INPUT -i lo -m state --state NEW -j ACCEPT
-A INPUT -j REJECT --reject-with icmp-port-unreachable
COMMIT
[root@desktop Desktop]# iptables -F 刷新
[root@desktop Desktop]# iptables -nL 查看策略
Chain INPUT (policy ACCEPT)
target prot opt source destination
Chain FORWARD (policy ACCEPT)
target prot opt source destination
Chain OUTPUT (policy ACCEPT)
target prot opt source destination
[root@desktop Desktop]# rpm -e httpd 卸载阿帕其iptables的地址伪装:
在desktop虚拟机:(双网卡)
在server虚拟机: