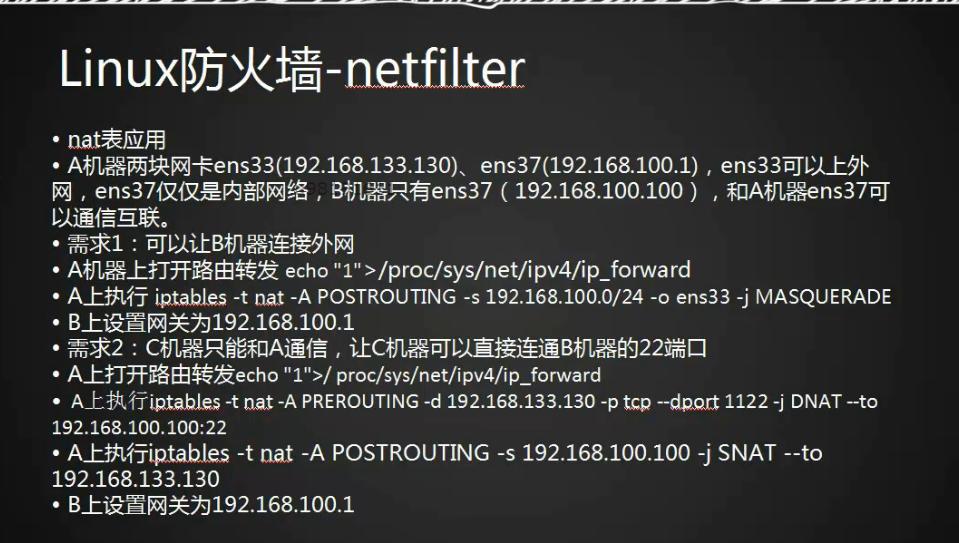
10.16 iptables nat表应用
1、打开端口转发模式
查询(将 /proc/sys/net/ipv4/ip_forward设置为1为转发,默认为0);
[root@shu-test ~]# cat /proc/sys/net/ipv4/ip_forward
0
[root@shu-test ~]#打开端口转发
echo "1" > /proc/sys/net/ipv4/ip_forward
[root@shu-test ~]# echo "1" > /proc/sys/net/ipv4/ip_forward
[root@shu-test ~]# cat /proc/sys/net/ipv4/ip_forward
1
[root@shu-test ~]#2、在机器A上增加规则
(记住B机器的网关必须指向机器A的ens37也就是192.168.100.1)
iptables -t nat -A POSTROUTING -s 192.168.100.0/24 -o ens33 -j MASQUERADE在机器A上增加nat 将源地址192.168.100.0/24的所有路由(数据包)指向ens33出去
[root@shu-test ~]# iptables -F
[root@shu-test ~]# iptables -t nat -nvL
Chain PREROUTING (policy ACCEPT 659 packets, 67162 bytes)
pkts bytes target prot opt in out source destination
Chain INPUT (policy ACCEPT 18 packets, 1935 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 50 packets, 3782 bytes)
pkts bytes target prot opt in out source destination
Chain POSTROUTING (policy ACCEPT 50 packets, 3782 bytes)
pkts bytes target prot opt in out source destination
42 3201 MASQUERADE all -- * ens33 192.168.100.0/24 0.0.0.0/0
[root@shu-test ~]#3、测试:
如果能ping通机器A的ens33网卡,而ping不通外网,可以清空下iptables -F配置的规则;
机器B上ping www.hao123.com
[root@localhost ~]# ping 192.168.188.1
PING 192.168.188.1 (192.168.188.1) 56(84) bytes of data.
64 bytes from 192.168.188.1: icmp_seq=1 ttl=127 time=1.58 ms
64 bytes from 192.168.188.1: icmp_seq=2 ttl=127 time=0.814 ms
^C
--- 192.168.188.1 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1002ms
rtt min/avg/max/mdev = 0.814/1.199/1.585/0.387 ms
[root@localhost ~]# ping www.hao123.com
PING hao123.n.shifen.com (112.34.111.167) 56(84) bytes of data.
64 bytes from 112.34.111.167 (112.34.111.167): icmp_seq=1 ttl=127 time=31.1 ms
64 bytes from 112.34.111.167 (112.34.111.167): icmp_seq=2 ttl=127 time=31.5 ms
64 bytes from 112.34.111.167 (112.34.111.167): icmp_seq=3 ttl=127 time=31.2 ms
^C
--- hao123.n.shifen.com ping statistics ---
3 packets transmitted, 3 received, 0% packet loss, time 2002ms
rtt min/avg/max/mdev = 31.116/31.291/31.502/0.159 ms
[root@localhost ~]#端口映射
需求2:C机器只能和A通信,让C机器可以直接通过B机器22端口;(端口映射)
1、打开A机器的端口转发功能;
echo "1" > /proc/sys/net/ipv4/ip_forward
[root@localhost ~]# echo "1" > /proc/sys/net/ipv4/ip_forward
[root@localhost ~]# cat /proc/sys/net/ipv4/ip_forward
1
[root@localhost ~]#2、清空和删除所有配置
使用iptables -F与 -D 命令,详情见前文章
3、在A机器上添加规则
iptables -t nat -A PREROUTING -d 192.168.188.2 -p tcp --dport 1122 -j DNAT --to 192.168.100.101:22
将192.168.100.101的22端口 映射到A机器的ens33的1122端口上,
使外网通过访问192.168.188.2:1122来达到访问机器C(ip:192.168.100.101)的22端口;
[root@shu-test ~]# iptables -t nat -A PREROUTING -d 192.168.188.2 -p tcp --dport 1122 -j DNAT --to 192.168.100.101:22
[root@shu-test ~]#
[root@shu-test ~]# iptables -t nat -nvL
Chain PREROUTING (policy ACCEPT 13 packets, 1072 bytes)
pkts bytes target prot opt in out source destination
5 260 DNAT tcp -- * * 0.0.0.0/0 192.168.188.2 tcp dpt:1122 to:192.168.100.101:22
Chain INPUT (policy ACCEPT 6 packets, 549 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 2 packets, 152 bytes)
pkts bytes target prot opt in out source destination
Chain POSTROUTING (policy ACCEPT 7 packets, 412 bytes)
pkts bytes target prot opt in out source destination
113 8561 MASQUERADE all -- * ens33 192.168.100.0/24 0.0.0.0/0
[root@shu-test ~]#4、在A机器上添加回包规则
iptables -t nat -A POSTROUTING -s 192.168.100.101 -j SNAT --to 192.168.188.2
将从192.168.100.101的过来的包,返回给192.168.188.2;
有来有回
[root@shu-test ~]# iptables -t nat -A POSTROUTING -s 192.168.100.101 -j SNAT --to 192.168.188.2
[root@shu-test ~]# iptables -t nat -nvL
Chain PREROUTING (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
5 260 DNAT tcp -- * * 0.0.0.0/0 192.168.188.2 tcp dpt:1122 to:192.168.100.101:22
Chain INPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain OUTPUT (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
Chain POSTROUTING (policy ACCEPT 0 packets, 0 bytes)
pkts bytes target prot opt in out source destination
122 9236 MASQUERADE all -- * ens33 192.168.100.0/24 0.0.0.0/0
0 0 SNAT all -- * * 192.168.100.101 0.0.0.0/0 to:192.168.188.2
[root@shu-test ~]#5、测试
在Windows上直接ssh 192.168.188.2:1122
Connecting to 192.168.188.2:1122...
Connection established.
To escape to local shell, press 'Ctrl+Alt+]'.
Last login: Thu Jan 25 22:22:33 2018 from 192.168.188.1
[root@shu002 ~]# w
23:02:45 up 43 min, 2 users, load average: 0.00, 0.01, 0.05
USER TTY FROM LOGIN@ IDLE JCPU PCPU WHAT
root tty1 22:20 11:09 0.29s 0.29s -bash
root pts/0 192.168.188.1 23:02 5.00s 0.07s 0.04s w
[root@shu002 ~]#
[root@shu002 ~]# ifconfig
ens33: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
ether 00:0c:29:20:41:c3 txqueuelen 1000 (Ethernet)
RX packets 636 bytes 67857 (66.2 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 333 bytes 45907 (44.8 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
ens37: flags=4163<UP,BROADCAST,RUNNING,MULTICAST> mtu 1500
inet 192.168.100.101 netmask 255.255.255.0 broadcast 192.168.100.255
inet6 fe80::d347:6274:ae3f:7255 prefixlen 64 scopeid 0x20<link>
inet6 fe80::f39c:81b9:efac:5b41 prefixlen 64 scopeid 0x20<link>
ether 00:0c:29:20:41:cd txqueuelen 1000 (Ethernet)
RX packets 289 bytes 27155 (26.5 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 341 bytes 34283 (33.4 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
lo: flags=73<UP,LOOPBACK,RUNNING> mtu 65536
inet 127.0.0.1 netmask 255.0.0.0
inet6 ::1 prefixlen 128 scopeid 0x10<host>
loop txqueuelen 1 (Local Loopback)
RX packets 72 bytes 5712 (5.5 KiB)
RX errors 0 dropped 0 overruns 0 frame 0
TX packets 72 bytes 5712 (5.5 KiB)
TX errors 0 dropped 0 overruns 0 carrier 0 collisions 0
[root@shu002 ~]#10.19 iptables规则备份和恢复
service iptables save ,会把规则保存到 iptables 的配置文件中 /etc/sysconfig/iptables
iptables -save > /tmp/ipt.txt 将规则保存到ipt.txt
iptabls - restore </tmp/ipt.txt 恢复规则